1
.NET Passport Security Framework
CPSC 328 Spring 2009
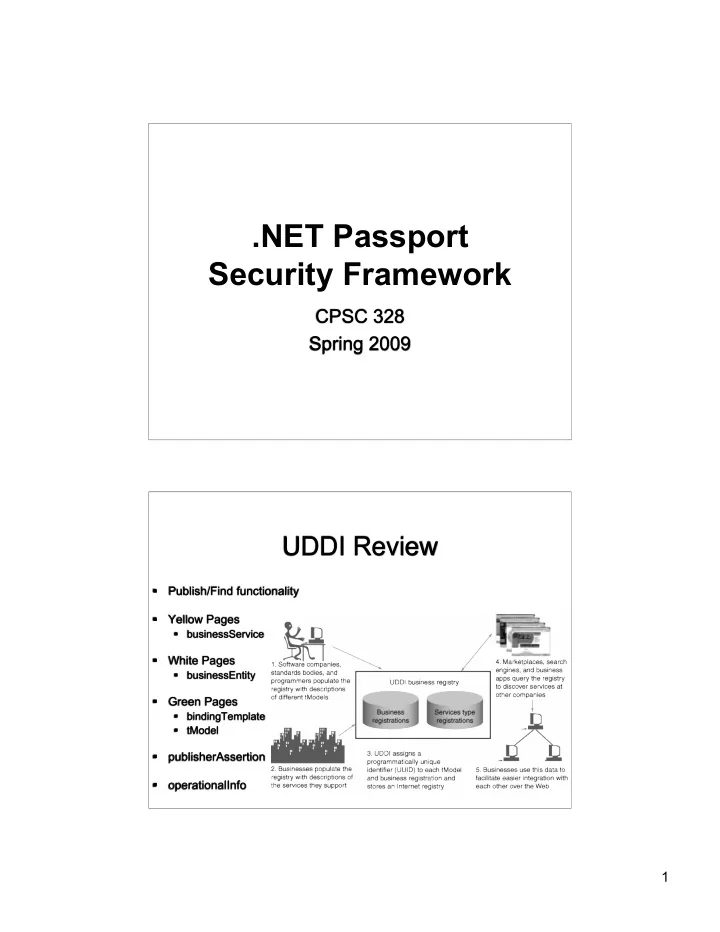
UDDI Review
- Publish/Find functionality
- Yellow Pages
- businessService
- White Pages
- businessEntity
- Green Pages
- bindingTemplate
- tModel
- publisherAssertion
- perationalInfo
.NET Passport Security Framework CPSC 328 Spring 2009 UDDI Review - - PDF document
.NET Passport Security Framework CPSC 328 Spring 2009 UDDI Review Publish/Find functionality Yellow Pages businessService White Pages businessEntity Green Pages bindingTemplate tModel
1
2
<html> <body> <img src=“http://foo.bar.com/logout.php”> </body> </html> <html> <body> <img src="http://www.example.com/transfer.do? frmAcct=document.form.frmAcct& toAcct=4345754&toSWIFTid=434343&amt=3434.43"> </body> </html>
3
<html> <body onload="document.getElementById('f').submit()"> <form id="f" action="http://foo.com/logout" method="post"> <input name="Log Me Out" value="Log Me Out" /> </form> </body> </html>
<form action="/transfer.do" method="post"> <input type="hidden" name="8438927730" value="43847384383"> </form>
4
Source: www.xml-dev.com/blog/
5
Source: microsoft.com
6
browser
sites
7
8
9