1
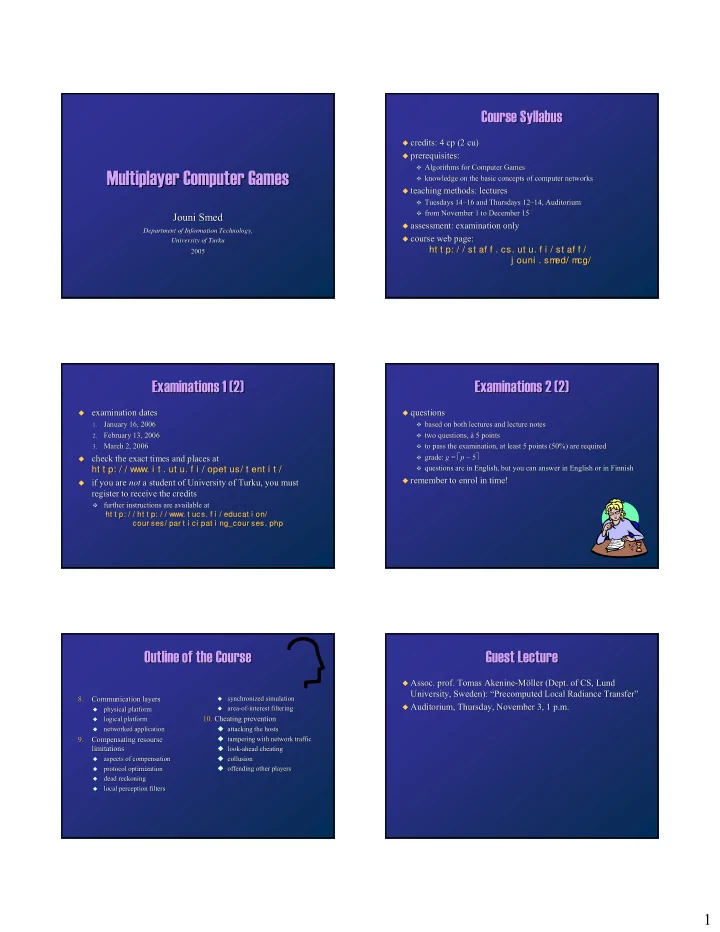
Multiplayer Computer Games Multiplayer Computer Games
Jouni Smed Jouni Smed
Department of Information Technology, Department of Information Technology, University of Turku University of Turku 2005 2005
Course Syllabus Course Syllabus
- credits: 4 cp (2 cu)
credits: 4 cp (2 cu)
- prerequisites:
prerequisites:
- Algorithms for Computer Games
Algorithms for Computer Games
- knowledge on the basic concepts of computer networks
knowledge on the basic concepts of computer networks
- teaching methods: lectures
teaching methods: lectures
- Tuesdays 14
Tuesdays 14– –16 and Thursdays 12 16 and Thursdays 12– –14, Auditorium 14, Auditorium
- from November 1 to December 15
from November 1 to December 15
- assessment: examination only
assessment: examination only
- course web page:
course web page: ht t p: / / st af f . ht t p: / / st af f . cs. ut u. f i / st a
- cs. ut u. f i / st af f /
f f / ht t p: / / st af f . ht t p: / / st af f . cs. ut u. f i / st a
- cs. ut u. f i / st af f /
f f / j ouni . sm ed/ m c j ouni . sm ed/ m cg/ g/ j ouni . sm ed/ m c j ouni . sm ed/ m cg/ g/
Examinations 1 (2) Examinations 1 (2)
- examination dates
examination dates
1. 1.
January 16, 2006 January 16, 2006
2. 2.
February 13, 2006 February 13, 2006
3. 3.
March 2, 2006 March 2, 2006
- check the exact times and places at
check the exact times and places at ht t p: / / www. i t ht t p: / / www. i t . ut u. f i / opet u . ut u. f i / opet us/ t ent i t / s/ t ent i t / ht t p: / / www. i t ht t p: / / www. i t . ut u. f i / opet u . ut u. f i / opet us/ t ent i t / s/ t ent i t /
- if you are
if you are not not a student of University of Turku, you must a student of University of Turku, you must register to receive the credits register to receive the credits
- further instructions are available at
further instructions are available at ht t ht t p: p: / / / / ht ht t p t p: / : / / w / www.
- ww. t u
t ucs
- cs. f
. f i / i / ed educ ucat i at i on
- n/
ht t ht t p: p: / / / / ht ht t p t p: / : / / w / www.
- ww. t u
t ucs
- cs. f
. f i / i / ed educ ucat i at i on
- n/
cou cour s r ses es/ p / par ar t i t i ci ci pat pat i n i ng_ g_co cour ur se ses.
- s. php
php cou cour s r ses es/ p / par ar t i t i ci ci pat pat i n i ng_ g_co cour ur se ses.
- s. php
php
Examinations 2 (2) Examinations 2 (2)
- questions
questions
- based on both lectures and lecture notes
based on both lectures and lecture notes
- two questions, à 5 points
two questions, à 5 points
- to pass the examination, at least 5 points (50%) are required
to pass the examination, at least 5 points (50%) are required
- grade:
grade: g g = = ⎡ ⎡p p − 5 − 5⎤ ⎤
- questions are in English, but you can answer in English or in Fi
questions are in English, but you can answer in English or in Finnish nnish
- remember to enrol in time!
remember to enrol in time!
Outline of the Course Outline of the Course
8. 8. Communication layers Communication layers
- physical platform
physical platform
- logical platform
logical platform
- networked application
networked application
9. 9. Compensating resourse Compensating resourse limitations limitations
- aspects of compensation
aspects of compensation
- protocol optimization
protocol optimization
- dead reckoning
dead reckoning
- local perception filters
local perception filters
- synchronized simulation
synchronized simulation
- area
area-
- of
- f-
- interest filtering
interest filtering
10.
- 10. Cheating prevention
Cheating prevention
- attacking the hosts
attacking the hosts
- tampering with network traffic
tampering with network traffic
- look
look-
- ahead cheating
ahead cheating
- collusion
collusion
- ffending other players
- ffending other players
Guest Lecture Guest Lecture
- Assoc. prof. Tomas Akenine
- Assoc. prof. Tomas Akenine-
- Möller (Dept. of CS, Lund
Möller (Dept. of CS, Lund University, Sweden): “Precomputed Local Radiance Transfer” University, Sweden): “Precomputed Local Radiance Transfer”
- Auditorium, Thursday, November 3, 1 p.m.
Auditorium, Thursday, November 3, 1 p.m.