1
1
CMPE 252A: SET 5:
Medium edium Acces ccess Cont
- ntrol
- l
Prot
- tocols
- cols
2
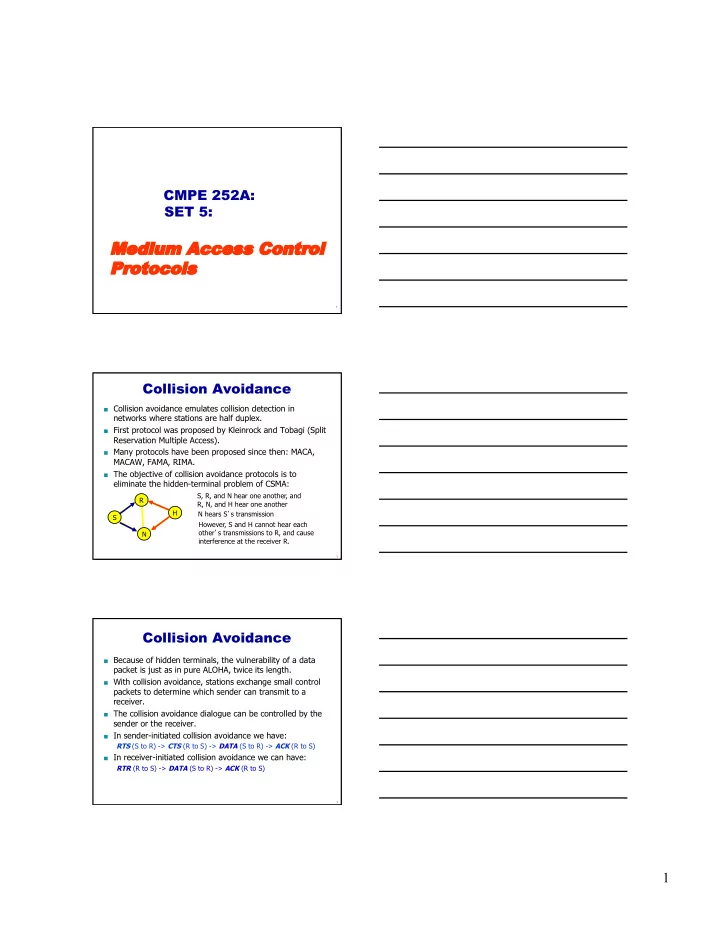
Collision Avoidance
Collision avoidance emulates collision detection in
networks where stations are half duplex.
First protocol was proposed by Kleinrock and Tobagi (Split
Reservation Multiple Access).
Many protocols have been proposed since then: MACA,
MACAW, FAMA, RIMA.
The objective of collision avoidance protocols is to
eliminate the hidden-terminal problem of CSMA:
S N R H S, R, and N hear one another, and R, N, and H hear one another N hears S’s transmission However, S and H cannot hear each
- ther’s transmissions to R, and cause
interference at the receiver R.
3
Collision Avoidance
Because of hidden terminals, the vulnerability of a data
packet is just as in pure ALOHA, twice its length.
With collision avoidance, stations exchange small control
packets to determine which sender can transmit to a receiver.
The collision avoidance dialogue can be controlled by the
sender or the receiver.
In sender-initiated collision avoidance we have:
RTS (S to R) -> CTS (R to S) -> DATA (S to R) -> ACK (R to S)
In receiver-initiated collision avoidance we can have:
RTR (R to S) -> DATA (S to R) -> ACK (R to S)