SLIDE 1
5/7/2009shankar
- authenticationslide1
- ComputerandNetworkSecurity
CMSC414
- STANDARDS
- UdayaShankar
shankar@cs.umd.edu
- 5/7/2009shankar
- authenticationslide2
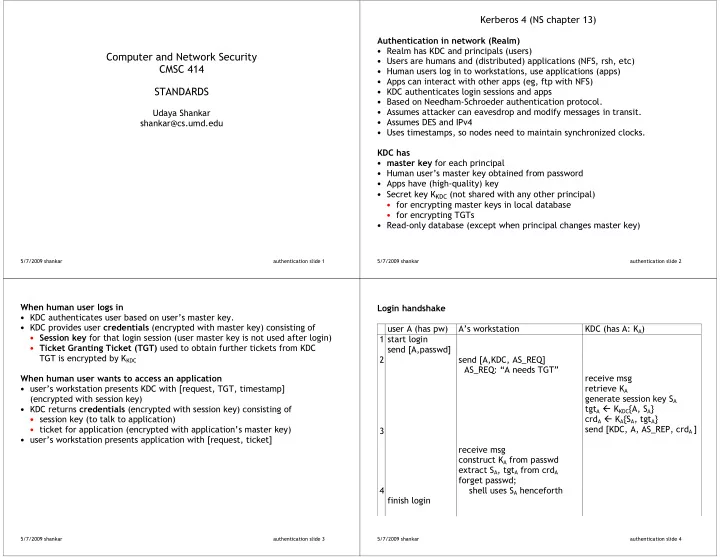
- Kerberos4(NSchapter13)
- RealmhasKDCandprincipals(users)
- Usersarehumansand(distributed)applications(NFS,rsh,etc)
- Humanuserslogintoworkstations,useapplications(apps)
- Appscaninteractwithotherapps(eg,ftpwithNFS)
- KDCauthenticatesloginsessionsandapps
- BasedonNeedham2Schroederauthenticationprotocol.
- Assumesattackercaneavesdropandmodifymessagesintransit.
- AssumesDESandIPv4
- Usestimestamps,sonodesneedtomaintainsynchronizedclocks.
- foreachprincipal
- Humanuser’smasterkeyobtainedfrompassword
- Appshave(high2quality)key
- SecretkeyKKDC(notsharedwithanyotherprincipal)
- forencryptingmasterkeysinlocaldatabase
- forencryptingTGTs
- Read2onlydatabase(exceptwhenprincipalchangesmasterkey)
5/7/2009shankar
- authenticationslide3
- KDCauthenticatesuserbasedonuser’smasterkey.
- KDCprovidesuser(encryptedwithmasterkey)consistingof
- forthatloginsession(usermasterkeyisnotusedafterlogin)
- usedtoobtainfurtherticketsfromKDC
TGTisencryptedbyKKDC
- user’sworkstationpresentsKDCwith[request,TGT,timestamp]
(encryptedwithsessionkey)
- KDCreturns(encryptedwithsessionkey)consistingof
- sessionkey(totalktoapplication)
- ticketforapplication(encryptedwithapplication’smasterkey)
- user’sworkstationpresentsapplicationwith[request,ticket]
5/7/2009shankar
- authenticationslide4
- userA(haspw)
A’sworkstation KDC(hasA:KA) 1startlogin send[A,passwd]
- 2
- 3
- send[A,KDC,AS_REQ]
AS_REQ:“AneedsTGT”
- receivemsg
retrieveKA generatesessionkeySA tgtAKKDC{A,SA} crdAKA{SA,tgtA} send[KDC,A,AS_REP,crdA]
- 4
- receivemsg
constructKAfrompasswd extractSA,tgtAfromcrdA forgetpasswd; shellusesSAhenceforth
- finishlogin