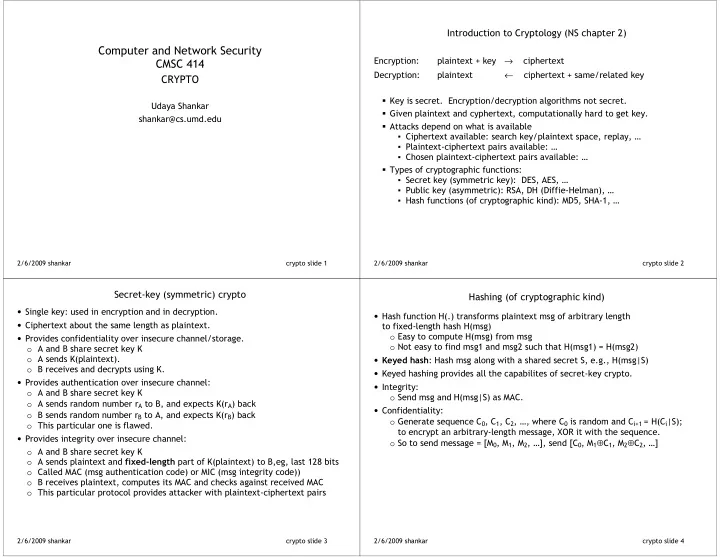
SLIDE 1
2/6/2009shankar
- cryptoslide1
- ComputerandNetworkSecurity
CMSC414
CRYPTO
- UdayaShankar
shankar@cs.umd.edu
2/6/2009shankar
- cryptoslide2
- IntroductiontoCryptology(NSchapter2)
- Encryption:
plaintext+key→ciphertext Decryption: plaintext←ciphertext+same/relatedkey
- Keyissecret.Encryption/decryptionalgorithmsnotsecret.
Givenplaintextandcyphertext,computationallyhardtogetkey. Attacksdependonwhatisavailable ▪ Ciphertextavailable:searchkey/plaintextspace,replay,… ▪ Plaintext7ciphertextpairsavailable:… ▪ Chosenplaintext7ciphertextpairsavailable:… Typesofcryptographicfunctions: ▪ Secretkey(symmetrickey):DES,AES,… ▪ Publickey(asymmetric):RSA,DH(Diffie7Helman),… ▪ Hashfunctions(ofcryptographickind):MD5,SHA71,…
2/6/2009shankar
- cryptoslide3
Secret7key(symmetric)crypto
- Singlekey:usedinencryptionandindecryption.
- Ciphertextaboutthesamelengthasplaintext.
- Providesconfidentialityoverinsecurechannel/storage.
- AandBsharesecretkeyK
- AsendsK(plaintext).
- BreceivesanddecryptsusingK.
- Providesauthenticationoverinsecurechannel:
- AandBsharesecretkeyK
- AsendsrandomnumberrAtoB,andexpectsK(rA)back
- BsendsrandomnumberrBtoA,andexpectsK(rB)back
- Thisparticularoneisflawed.
- Providesintegrityoverinsecurechannel:
- AandBsharesecretkeyK
- AsendsplaintextandpartofK(plaintext)toB,eg,last128bits
- CalledMAC(msgauthenticationcode)orMIC(msgintegritycode))
- Breceivesplaintext,computesitsMACandchecksagainstreceivedMAC
- Thisparticularprotocolprovidesattackerwithplaintext7ciphertextpairs
- 2/6/2009shankar
- cryptoslide4
Hashing(ofcryptographickind)
- HashfunctionH(.)transformsplaintextmsgofarbitrarylength
tofixed7lengthhashH(msg)
- EasytocomputeH(msg)frommsg
- Noteasytofindmsg1andmsg2suchthatH(msg1)=H(msg2)
- :HashmsgalongwithasharedsecretS,e.g.,H(msg|S)
- Keyedhashingprovidesallthecapabilitesofsecret7keycrypto.
- Integrity:
- SendmsgandH(msg|S)asMAC.
- Confidentiality:
- GeneratesequenceC0,C1,C2,…,whereC0israndomandCi+1=H(Ci|S);
toencryptanarbitrary7lengthmessage,XORitwiththesequence.
- Sotosendmessage=[M0,M1,M2,…],send[C0,M1⊕C1,M2⊕C2,…]