1
CS 465 Fall 2001 1
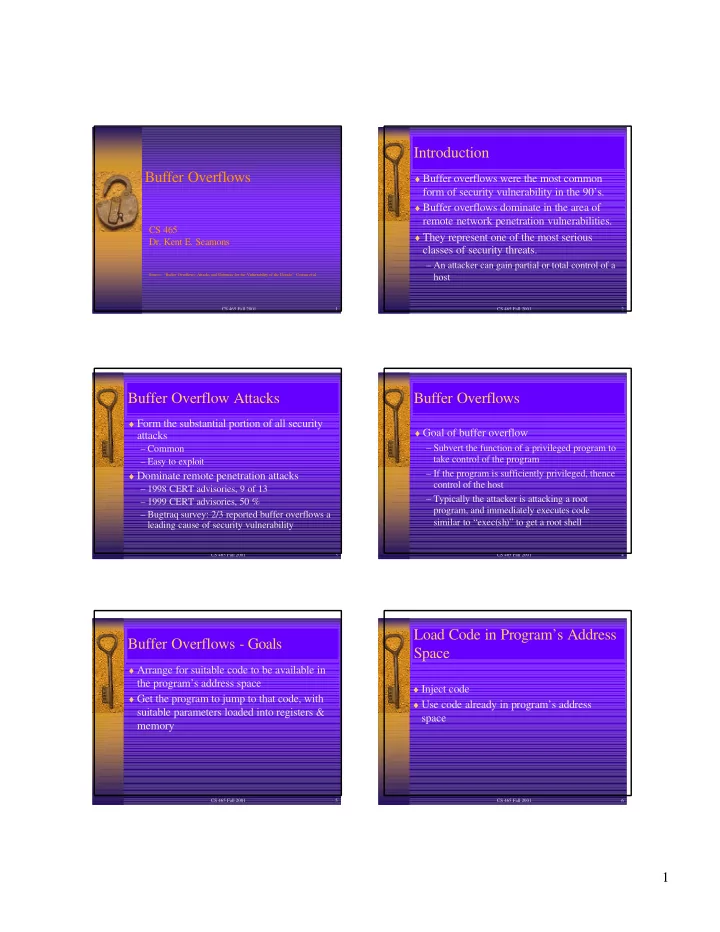
Buffer Overflows
CS 465
- Dr. Kent E. Seamons
Source: “Buffer Overflows: Attacks and Defenses for the Vulnerability of the Decade” Cowan et al.
CS 465 Fall 2001 2
Introduction
♦ Buffer overflows were the most common
form of security vulnerability in the 90’s.
♦ Buffer overflows dominate in the area of
remote network penetration vulnerabilities.
♦ They represent one of the most serious
classes of security threats.
– An attacker can gain partial or total control of a host
CS 465 Fall 2001 3
Buffer Overflow Attacks
♦ Form the substantial portion of all security
attacks
– Common – Easy to exploit ♦ Dominate remote penetration attacks – 1998 CERT advisories, 9 of 13 – 1999 CERT advisories, 50 % – Bugtraq survey: 2/3 reported buffer overflows a leading cause of security vulnerability
CS 465 Fall 2001 4
Buffer Overflows
♦ Goal of buffer overflow – Subvert the function of a privileged program to take control of the program – If the program is sufficiently privileged, thence control of the host – Typically the attacker is attacking a root program, and immediately executes code similar to “exec(sh)” to get a root shell
CS 465 Fall 2001 5
Buffer Overflows - Goals
♦ Arrange for suitable code to be available in
the program’s address space
♦ Get the program to jump to that code, with
suitable parameters loaded into registers & memory
CS 465 Fall 2001 6