Information Bottleneck for an Oblivious Relay with Channel State Information: the Scalar Case
Giuseppe Caire⋆, Shlomo Shamai†, Antonia Tulino∗, Sergio Verdu‡, and Cagkan Yapar⋆⋆
⋆ USC, Los Angeles CA, † Technion Haifa, ∗ Universit´
a Federico II Napoli, ‡ Princeton, NJ, ⋆⋆ TU Berlin
Abstract—We consider an extension
- f
the information bottleneck problem where underlying Markov Chain is X–o–(Y, S)–o–Z, and where PX,S,Y = PXPSPY |X,S is the joint distribution of a source X, a channel state S independent of the source, and the channel output Y of a state-dependent channel. For the case Y = SX + N with X, S and N Gaussian circularly symmetric, we provide an upper bound and two achievable lower bounds on the information bottleneck rate. We relate this problem to the case of an oblivious relay with channel state
- information. Our results show that simple symbol-by-symbol
relay processing, possibly followed by “entropy coding” (data compression) yields a very effective method, virtually achieving the upper bound on a wide range of relevant system parameters. Index Terms—Gaussian Information Bottleneck, Channel State Information.
- I. INTRODUCTION AND PROBLEM DEFINITION
The Information Bottleneck (IB) problem considers the Markov Chain X–o–Y –o–Z, where PX,Y is an assigned joint probability distribution on X × Y (the alphabet of (X, Y )) and PZ|Y is to be found as the solution of the constrained maximization problem maximize I(X; Z) (1a) subject to I(Y ; Z) ≤ C, (1b) where C is the bottleneck constraint parameter. The alphabet
- f Z may or may not be specified a priori, depending on
the problem at hand [1]. This formulation was introduced by Tishby in [2], and it has been used to interpret the behavior
- f deep learning neural networks, where the evolution of the
learning process via some training scheme (e.g., stochastic gradient back propagation) can be visualized on the IB plane
- f I(X; Z) (relevant information on X) vs. C (representation
rate of the observation Y , referred to as complexity, [3]). From a more fundamental information theoretic viewpoint, the IB consists of a classical remote source coding problem [4], [5] under logarithmic distortion [6]. Another interesting scenario where the IB problem is rele- vant consists of the so-called oblivious relay (see [7]). Let X and Y be the input and the output of a communication channel, where a source node sends codewords from a given codebook, and the receiver is formed by a remote relay communicating to the actual decoder via an error-free link (digital pipe) of capacity C. The relay is oblivious in the sense that it cannot
This work has been supported by the US-Israel Binational Science Foun- dation (BSF).
X
<latexit sha1_base64="O1GCNFOLEfXrH+80JBkvTQl62o4=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEeqx6MVjC/YD2lA20m7drMJuxuhP4CLx4U8epP8ua/cdvmoK0vLDy8M8POvEiuDau+0UNja3tneKu6W9/YPDo/LxSVvHqWLYrGIVTegGgWX2DLcCOwmCmkUCOwEk7t5vfOESvNYPphpgn5ER5KHnFjrWZ3UK64VXchsg5eDhXI1RiUv/rDmKURSsME1brnuYnxM6oMZwJnpX6qMaFsQkfYsyhphNrPFovOyIV1hiSMlX3SkIX7eyKjkdbTKLCdETVjvVqbm/VeqkJb/yMyQ1KNnyozAVxMRkfjUZcoXMiKkFyhS3uxI2poyY7Mp2RC81ZPXoX1V9Sw3ryv12zyOIpzBOVyCBzWowz0oAUMEJ7hFd6cR+fFeXc+lq0FJ585hT9yPn8AtbuM3A=</latexit><latexit sha1_base64="O1GCNFOLEfXrH+80JBkvTQl62o4=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEeqx6MVjC/YD2lA20m7drMJuxuhP4CLx4U8epP8ua/cdvmoK0vLDy8M8POvEiuDau+0UNja3tneKu6W9/YPDo/LxSVvHqWLYrGIVTegGgWX2DLcCOwmCmkUCOwEk7t5vfOESvNYPphpgn5ER5KHnFjrWZ3UK64VXchsg5eDhXI1RiUv/rDmKURSsME1brnuYnxM6oMZwJnpX6qMaFsQkfYsyhphNrPFovOyIV1hiSMlX3SkIX7eyKjkdbTKLCdETVjvVqbm/VeqkJb/yMyQ1KNnyozAVxMRkfjUZcoXMiKkFyhS3uxI2poyY7Mp2RC81ZPXoX1V9Sw3ryv12zyOIpzBOVyCBzWowz0oAUMEJ7hFd6cR+fFeXc+lq0FJ585hT9yPn8AtbuM3A=</latexit><latexit sha1_base64="O1GCNFOLEfXrH+80JBkvTQl62o4=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEeqx6MVjC/YD2lA20m7drMJuxuhP4CLx4U8epP8ua/cdvmoK0vLDy8M8POvEiuDau+0UNja3tneKu6W9/YPDo/LxSVvHqWLYrGIVTegGgWX2DLcCOwmCmkUCOwEk7t5vfOESvNYPphpgn5ER5KHnFjrWZ3UK64VXchsg5eDhXI1RiUv/rDmKURSsME1brnuYnxM6oMZwJnpX6qMaFsQkfYsyhphNrPFovOyIV1hiSMlX3SkIX7eyKjkdbTKLCdETVjvVqbm/VeqkJb/yMyQ1KNnyozAVxMRkfjUZcoXMiKkFyhS3uxI2poyY7Mp2RC81ZPXoX1V9Sw3ryv12zyOIpzBOVyCBzWowz0oAUMEJ7hFd6cR+fFeXc+lq0FJ585hT9yPn8AtbuM3A=</latexit><latexit sha1_base64="O1GCNFOLEfXrH+80JBkvTQl62o4=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEeqx6MVjC/YD2lA20m7drMJuxuhP4CLx4U8epP8ua/cdvmoK0vLDy8M8POvEiuDau+0UNja3tneKu6W9/YPDo/LxSVvHqWLYrGIVTegGgWX2DLcCOwmCmkUCOwEk7t5vfOESvNYPphpgn5ER5KHnFjrWZ3UK64VXchsg5eDhXI1RiUv/rDmKURSsME1brnuYnxM6oMZwJnpX6qMaFsQkfYsyhphNrPFovOyIV1hiSMlX3SkIX7eyKjkdbTKLCdETVjvVqbm/VeqkJb/yMyQ1KNnyozAVxMRkfjUZcoXMiKkFyhS3uxI2poyY7Mp2RC81ZPXoX1V9Sw3ryv12zyOIpzBOVyCBzWowz0oAUMEJ7hFd6cR+fFeXc+lq0FJ585hT9yPn8AtbuM3A=</latexit>S
<latexit sha1_base64="C83UbuJfe6zLAdEUkfaiUdGRi4=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEfRY9OKxRfsBbSib7aRdu9mE3Y1Qn+BFw+KePUnefPfuG1z0NYXFh7emWFn3iARXBvX/XYKa+sbm1vF7dLO7t7+QfnwqKXjVDFsljEqhNQjYJLbBpuBHYShTQKBLaD8e2s3n5CpXksH8wkQT+iQ8lDzqixVuO+X64VXcusgpeDhXIVe+Xv3qDmKURSsME1bruYnxM6oMZwKnpV6qMaFsTIfYtShphNrP5otOyZl1BiSMlX3SkLn7eyKjkdaTKLCdETUjvVybmf/VuqkJr/2MyQ1KNniozAVxMRkdjUZcIXMiIkFyhS3uxI2oyY7Mp2RC85ZNXoXVR9Sw3Liu1mzyOIpzAKZyDB1dQgzuoQxMYIDzDK7w5j86L8+58LFoLTj5zDH/kfP4ArieM1w=</latexit><latexit sha1_base64="C83UbuJfe6zLAdEUkfaiUdGRi4=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEfRY9OKxRfsBbSib7aRdu9mE3Y1Qn+BFw+KePUnefPfuG1z0NYXFh7emWFn3iARXBvX/XYKa+sbm1vF7dLO7t7+QfnwqKXjVDFsljEqhNQjYJLbBpuBHYShTQKBLaD8e2s3n5CpXksH8wkQT+iQ8lDzqixVuO+X64VXcusgpeDhXIVe+Xv3qDmKURSsME1bruYnxM6oMZwKnpV6qMaFsTIfYtShphNrP5otOyZl1BiSMlX3SkLn7eyKjkdaTKLCdETUjvVybmf/VuqkJr/2MyQ1KNniozAVxMRkdjUZcIXMiIkFyhS3uxI2oyY7Mp2RC85ZNXoXVR9Sw3Liu1mzyOIpzAKZyDB1dQgzuoQxMYIDzDK7w5j86L8+58LFoLTj5zDH/kfP4ArieM1w=</latexit><latexit sha1_base64="C83UbuJfe6zLAdEUkfaiUdGRi4=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEfRY9OKxRfsBbSib7aRdu9mE3Y1Qn+BFw+KePUnefPfuG1z0NYXFh7emWFn3iARXBvX/XYKa+sbm1vF7dLO7t7+QfnwqKXjVDFsljEqhNQjYJLbBpuBHYShTQKBLaD8e2s3n5CpXksH8wkQT+iQ8lDzqixVuO+X64VXcusgpeDhXIVe+Xv3qDmKURSsME1bruYnxM6oMZwKnpV6qMaFsTIfYtShphNrP5otOyZl1BiSMlX3SkLn7eyKjkdaTKLCdETUjvVybmf/VuqkJr/2MyQ1KNniozAVxMRkdjUZcIXMiIkFyhS3uxI2oyY7Mp2RC85ZNXoXVR9Sw3Liu1mzyOIpzAKZyDB1dQgzuoQxMYIDzDK7w5j86L8+58LFoLTj5zDH/kfP4ArieM1w=</latexit><latexit sha1_base64="C83UbuJfe6zLAdEUkfaiUdGRi4=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEfRY9OKxRfsBbSib7aRdu9mE3Y1Qn+BFw+KePUnefPfuG1z0NYXFh7emWFn3iARXBvX/XYKa+sbm1vF7dLO7t7+QfnwqKXjVDFsljEqhNQjYJLbBpuBHYShTQKBLaD8e2s3n5CpXksH8wkQT+iQ8lDzqixVuO+X64VXcusgpeDhXIVe+Xv3qDmKURSsME1bruYnxM6oMZwKnpV6qMaFsTIfYtShphNrP5otOyZl1BiSMlX3SkLn7eyKjkdaTKLCdETUjvVybmf/VuqkJr/2MyQ1KNniozAVxMRkdjUZcIXMiIkFyhS3uxI2oyY7Mp2RC85ZNXoXVR9Sw3Liu1mzyOIpzAKZyDB1dQgzuoQxMYIDzDK7w5j86L8+58LFoLTj5zDH/kfP4ArieM1w=</latexit>Y
<latexit sha1_base64="45RxAjus7J8fHMzWOdPWZptgqnI=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEfRY9OKxBfshbSib7aRdu9mE3Y1Qn+BFw+KePUnefPfuG1z0NYXFh7emWFn3iARXBvX/XYKa+sbm1vF7dLO7t7+QfnwqKXjVDFsljEqhNQjYJLbBpuBHYShTQKBLaD8e2s3n5CpXks780kQT+iQ8lDzqixVuOhX64VXcusgpeDhXIVe+Xv3qDmKURSsME1bruYnxM6oMZwKnpV6qMaFsTIfYtShphNrP5otOyZl1BiSMlX3SkLn7eyKjkdaTKLCdETUjvVybmf/VuqkJr/2MyQ1KNniozAVxMRkdjUZcIXMiIkFyhS3uxI2oyY7Mp2RC85ZNXoXVR9Sw3Liu1mzyOIpzAKZyDB1dQgzuoQxMYIDzDK7w5j86L8+58LFoLTj5zDH/kfP4Atz+M3Q=</latexit><latexit sha1_base64="45RxAjus7J8fHMzWOdPWZptgqnI=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEfRY9OKxBfshbSib7aRdu9mE3Y1Qn+BFw+KePUnefPfuG1z0NYXFh7emWFn3iARXBvX/XYKa+sbm1vF7dLO7t7+QfnwqKXjVDFsljEqhNQjYJLbBpuBHYShTQKBLaD8e2s3n5CpXks780kQT+iQ8lDzqixVuOhX64VXcusgpeDhXIVe+Xv3qDmKURSsME1bruYnxM6oMZwKnpV6qMaFsTIfYtShphNrP5otOyZl1BiSMlX3SkLn7eyKjkdaTKLCdETUjvVybmf/VuqkJr/2MyQ1KNniozAVxMRkdjUZcIXMiIkFyhS3uxI2oyY7Mp2RC85ZNXoXVR9Sw3Liu1mzyOIpzAKZyDB1dQgzuoQxMYIDzDK7w5j86L8+58LFoLTj5zDH/kfP4Atz+M3Q=</latexit><latexit sha1_base64="45RxAjus7J8fHMzWOdPWZptgqnI=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEfRY9OKxBfshbSib7aRdu9mE3Y1Qn+BFw+KePUnefPfuG1z0NYXFh7emWFn3iARXBvX/XYKa+sbm1vF7dLO7t7+QfnwqKXjVDFsljEqhNQjYJLbBpuBHYShTQKBLaD8e2s3n5CpXks780kQT+iQ8lDzqixVuOhX64VXcusgpeDhXIVe+Xv3qDmKURSsME1bruYnxM6oMZwKnpV6qMaFsTIfYtShphNrP5otOyZl1BiSMlX3SkLn7eyKjkdaTKLCdETUjvVybmf/VuqkJr/2MyQ1KNniozAVxMRkdjUZcIXMiIkFyhS3uxI2oyY7Mp2RC85ZNXoXVR9Sw3Liu1mzyOIpzAKZyDB1dQgzuoQxMYIDzDK7w5j86L8+58LFoLTj5zDH/kfP4Atz+M3Q=</latexit><latexit sha1_base64="45RxAjus7J8fHMzWOdPWZptgqnI=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEfRY9OKxBfshbSib7aRdu9mE3Y1Qn+BFw+KePUnefPfuG1z0NYXFh7emWFn3iARXBvX/XYKa+sbm1vF7dLO7t7+QfnwqKXjVDFsljEqhNQjYJLbBpuBHYShTQKBLaD8e2s3n5CpXks780kQT+iQ8lDzqixVuOhX64VXcusgpeDhXIVe+Xv3qDmKURSsME1bruYnxM6oMZwKnpV6qMaFsTIfYtShphNrP5otOyZl1BiSMlX3SkLn7eyKjkdaTKLCdETUjvVybmf/VuqkJr/2MyQ1KNniozAVxMRkdjUZcIXMiIkFyhS3uxI2oyY7Mp2RC85ZNXoXVR9Sw3Liu1mzyOIpzAKZyDB1dQgzuoQxMYIDzDK7w5j86L8+58LFoLTj5zDH/kfP4Atz+M3Q=</latexit>PY |X,S
<latexit sha1_base64="h0wHAbBef1skmK2kP3BIp8kOKcQ=">AB8HicbZDLSgMxFIbP1Fut6pLN8EiuJAyI4Iui25cVrQ32qFk0kwbmSGJCOUcZ7CjQtF3Po47nwb03YW2vpD4OM/5Bz/iDmTBvX/XYK6tr6xvFzdLW9s7uXn/oKmjRBHaIBGPVDvAmnImacMw2k7VhSLgNWML6Z1luPVGkWyQcziakv8FCykBFsrNWp9POU/vsPuXK27VnQktg5dDBXLV+Wv3iAiaDSEI617npubPwUK8MIp1mpl2gaYzLGQ9q1KLGg2k9nC2foxDoDFEbKPmnQzP09kWKh9UQEtlNgM9KLtan5X62bmPDKT5mME0MlmX8UJhyZCE2vRwOmKDF8YgETxeyuiIywsTYjEo2BG/x5GVonlc9y3cXldp1HkcRjuAYTsGDS6jBLdShAQEPMrvDnKeXHenY95a8HJZw7hj5zPH280kCc=</latexit><latexit sha1_base64="h0wHAbBef1skmK2kP3BIp8kOKcQ=">AB8HicbZDLSgMxFIbP1Fut6pLN8EiuJAyI4Iui25cVrQ32qFk0kwbmSGJCOUcZ7CjQtF3Po47nwb03YW2vpD4OM/5Bz/iDmTBvX/XYK6tr6xvFzdLW9s7uXn/oKmjRBHaIBGPVDvAmnImacMw2k7VhSLgNWML6Z1luPVGkWyQcziakv8FCykBFsrNWp9POU/vsPuXK27VnQktg5dDBXLV+Wv3iAiaDSEI617npubPwUK8MIp1mpl2gaYzLGQ9q1KLGg2k9nC2foxDoDFEbKPmnQzP09kWKh9UQEtlNgM9KLtan5X62bmPDKT5mME0MlmX8UJhyZCE2vRwOmKDF8YgETxeyuiIywsTYjEo2BG/x5GVonlc9y3cXldp1HkcRjuAYTsGDS6jBLdShAQEPMrvDnKeXHenY95a8HJZw7hj5zPH280kCc=</latexit><latexit sha1_base64="h0wHAbBef1skmK2kP3BIp8kOKcQ=">AB8HicbZDLSgMxFIbP1Fut6pLN8EiuJAyI4Iui25cVrQ32qFk0kwbmSGJCOUcZ7CjQtF3Po47nwb03YW2vpD4OM/5Bz/iDmTBvX/XYK6tr6xvFzdLW9s7uXn/oKmjRBHaIBGPVDvAmnImacMw2k7VhSLgNWML6Z1luPVGkWyQcziakv8FCykBFsrNWp9POU/vsPuXK27VnQktg5dDBXLV+Wv3iAiaDSEI617npubPwUK8MIp1mpl2gaYzLGQ9q1KLGg2k9nC2foxDoDFEbKPmnQzP09kWKh9UQEtlNgM9KLtan5X62bmPDKT5mME0MlmX8UJhyZCE2vRwOmKDF8YgETxeyuiIywsTYjEo2BG/x5GVonlc9y3cXldp1HkcRjuAYTsGDS6jBLdShAQEPMrvDnKeXHenY95a8HJZw7hj5zPH280kCc=</latexit><latexit sha1_base64="h0wHAbBef1skmK2kP3BIp8kOKcQ=">AB8HicbZDLSgMxFIbP1Fut6pLN8EiuJAyI4Iui25cVrQ32qFk0kwbmSGJCOUcZ7CjQtF3Po47nwb03YW2vpD4OM/5Bz/iDmTBvX/XYK6tr6xvFzdLW9s7uXn/oKmjRBHaIBGPVDvAmnImacMw2k7VhSLgNWML6Z1luPVGkWyQcziakv8FCykBFsrNWp9POU/vsPuXK27VnQktg5dDBXLV+Wv3iAiaDSEI617npubPwUK8MIp1mpl2gaYzLGQ9q1KLGg2k9nC2foxDoDFEbKPmnQzP09kWKh9UQEtlNgM9KLtan5X62bmPDKT5mME0MlmX8UJhyZCE2vRwOmKDF8YgETxeyuiIywsTYjEo2BG/x5GVonlc9y3cXldp1HkcRjuAYTsGDS6jBLdShAQEPMrvDnKeXHenY95a8HJZw7hj5zPH280kCc=</latexit>Z
<latexit sha1_base64="kvZgzxK4Vbrow2WzP7hDgVZ/h8I=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEfRY9OKxBfuBbSib7aRdu9mE3Y1Qn+BFw+KePUnefPfuG1z0NYXFh7emWFn3iARXBvX/XYKa+sbm1vF7dLO7t7+QfnwqKXjVDFsljEqhNQjYJLbBpuBHYShTQKBLaD8e2s3n5CpXks780kQT+iQ8lDzqixVuOhX64VXcusgpeDhXIVe+Xv3qDmKURSsME1bruYnxM6oMZwKnpV6qMaFsTIfYtShphNrP5otOyZl1BiSMlX3SkLn7eyKjkdaTKLCdETUjvVybmf/VuqkJr/2MyQ1KNniozAVxMRkdjUZcIXMiIkFyhS3uxI2oyY7Mp2RC85ZNXoXVR9Sw3Liu1mzyOIpzAKZyDB1dQgzuoQxMYIDzDK7w5j86L8+58LFoLTj5zDH/kfP4AuMOM3g=</latexit><latexit sha1_base64="kvZgzxK4Vbrow2WzP7hDgVZ/h8I=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEfRY9OKxBfuBbSib7aRdu9mE3Y1Qn+BFw+KePUnefPfuG1z0NYXFh7emWFn3iARXBvX/XYKa+sbm1vF7dLO7t7+QfnwqKXjVDFsljEqhNQjYJLbBpuBHYShTQKBLaD8e2s3n5CpXks780kQT+iQ8lDzqixVuOhX64VXcusgpeDhXIVe+Xv3qDmKURSsME1bruYnxM6oMZwKnpV6qMaFsTIfYtShphNrP5otOyZl1BiSMlX3SkLn7eyKjkdaTKLCdETUjvVybmf/VuqkJr/2MyQ1KNniozAVxMRkdjUZcIXMiIkFyhS3uxI2oyY7Mp2RC85ZNXoXVR9Sw3Liu1mzyOIpzAKZyDB1dQgzuoQxMYIDzDK7w5j86L8+58LFoLTj5zDH/kfP4AuMOM3g=</latexit><latexit sha1_base64="kvZgzxK4Vbrow2WzP7hDgVZ/h8I=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEfRY9OKxBfuBbSib7aRdu9mE3Y1Qn+BFw+KePUnefPfuG1z0NYXFh7emWFn3iARXBvX/XYKa+sbm1vF7dLO7t7+QfnwqKXjVDFsljEqhNQjYJLbBpuBHYShTQKBLaD8e2s3n5CpXks780kQT+iQ8lDzqixVuOhX64VXcusgpeDhXIVe+Xv3qDmKURSsME1bruYnxM6oMZwKnpV6qMaFsTIfYtShphNrP5otOyZl1BiSMlX3SkLn7eyKjkdaTKLCdETUjvVybmf/VuqkJr/2MyQ1KNniozAVxMRkdjUZcIXMiIkFyhS3uxI2oyY7Mp2RC85ZNXoXVR9Sw3Liu1mzyOIpzAKZyDB1dQgzuoQxMYIDzDK7w5j86L8+58LFoLTj5zDH/kfP4AuMOM3g=</latexit><latexit sha1_base64="kvZgzxK4Vbrow2WzP7hDgVZ/h8I=">AB6HicbZBNS8NAEIYn9avWr6pHL4tF8FQSEfRY9OKxBfuBbSib7aRdu9mE3Y1Qn+BFw+KePUnefPfuG1z0NYXFh7emWFn3iARXBvX/XYKa+sbm1vF7dLO7t7+QfnwqKXjVDFsljEqhNQjYJLbBpuBHYShTQKBLaD8e2s3n5CpXks780kQT+iQ8lDzqixVuOhX64VXcusgpeDhXIVe+Xv3qDmKURSsME1bruYnxM6oMZwKnpV6qMaFsTIfYtShphNrP5otOyZl1BiSMlX3SkLn7eyKjkdaTKLCdETUjvVybmf/VuqkJr/2MyQ1KNniozAVxMRkdjUZcIXMiIkFyhS3uxI2oyY7Mp2RC85ZNXoXVR9Sw3Liu1mzyOIpzAKZyDB1dQgzuoQxMYIDzDK7w5j86L8+58LFoLTj5zDH/kfP4AuMOM3g=</latexit>source
<latexit sha1_base64="YS7Ry7dSJ2pZ4FxnUzCH1mMch+w=">AB9HicbZDLSgMxFIbP1Fut6pLN8EiuCozIthlwY3LCvYC7VAyaYNzWVMsUy9DncuFDErQ/jzrcxbWehrQcCH/9/TnLyRwlnxvr+t1fY2Nza3inulvb2Dw6PyscnLaNSTWiTK50J8KGciZp0zLaSfRFIuI03Y0vp37QnVhin5YKcJDQUeShYzgq2Twp6I1FO2vG3WL1f8qr8otA5BDhXIq9Evf/UGiqSCSks4NqYb+IkNM6wtI5zOSr3U0ASTMR7SrkOJBTVhtlh6hi6cMkCx0u5Iixbq74kMC2OmInKdAtuRWfXm4n9eN7VxLcyYTFJLJVk+FKcWYXmCaAB05RYPnWAiWZuV0RGWGNiXU4lF0Kw+uV1aF1VA8f315V6LY+jCGdwDpcQwA3U4Q4a0AQCj/AMr/DmTbwX7937WLYWvHzmFP6U9/kDiRiSjQ=</latexit><latexit sha1_base64="YS7Ry7dSJ2pZ4FxnUzCH1mMch+w=">AB9HicbZDLSgMxFIbP1Fut6pLN8EiuCozIthlwY3LCvYC7VAyaYNzWVMsUy9DncuFDErQ/jzrcxbWehrQcCH/9/TnLyRwlnxvr+t1fY2Nza3inulvb2Dw6PyscnLaNSTWiTK50J8KGciZp0zLaSfRFIuI03Y0vp37QnVhin5YKcJDQUeShYzgq2Twp6I1FO2vG3WL1f8qr8otA5BDhXIq9Evf/UGiqSCSks4NqYb+IkNM6wtI5zOSr3U0ASTMR7SrkOJBTVhtlh6hi6cMkCx0u5Iixbq74kMC2OmInKdAtuRWfXm4n9eN7VxLcyYTFJLJVk+FKcWYXmCaAB05RYPnWAiWZuV0RGWGNiXU4lF0Kw+uV1aF1VA8f315V6LY+jCGdwDpcQwA3U4Q4a0AQCj/AMr/DmTbwX7937WLYWvHzmFP6U9/kDiRiSjQ=</latexit><latexit sha1_base64="YS7Ry7dSJ2pZ4FxnUzCH1mMch+w=">AB9HicbZDLSgMxFIbP1Fut6pLN8EiuCozIthlwY3LCvYC7VAyaYNzWVMsUy9DncuFDErQ/jzrcxbWehrQcCH/9/TnLyRwlnxvr+t1fY2Nza3inulvb2Dw6PyscnLaNSTWiTK50J8KGciZp0zLaSfRFIuI03Y0vp37QnVhin5YKcJDQUeShYzgq2Twp6I1FO2vG3WL1f8qr8otA5BDhXIq9Evf/UGiqSCSks4NqYb+IkNM6wtI5zOSr3U0ASTMR7SrkOJBTVhtlh6hi6cMkCx0u5Iixbq74kMC2OmInKdAtuRWfXm4n9eN7VxLcyYTFJLJVk+FKcWYXmCaAB05RYPnWAiWZuV0RGWGNiXU4lF0Kw+uV1aF1VA8f315V6LY+jCGdwDpcQwA3U4Q4a0AQCj/AMr/DmTbwX7937WLYWvHzmFP6U9/kDiRiSjQ=</latexit><latexit sha1_base64="YS7Ry7dSJ2pZ4FxnUzCH1mMch+w=">AB9HicbZDLSgMxFIbP1Fut6pLN8EiuCozIthlwY3LCvYC7VAyaYNzWVMsUy9DncuFDErQ/jzrcxbWehrQcCH/9/TnLyRwlnxvr+t1fY2Nza3inulvb2Dw6PyscnLaNSTWiTK50J8KGciZp0zLaSfRFIuI03Y0vp37QnVhin5YKcJDQUeShYzgq2Twp6I1FO2vG3WL1f8qr8otA5BDhXIq9Evf/UGiqSCSks4NqYb+IkNM6wtI5zOSr3U0ASTMR7SrkOJBTVhtlh6hi6cMkCx0u5Iixbq74kMC2OmInKdAtuRWfXm4n9eN7VxLcyYTFJLJVk+FKcWYXmCaAB05RYPnWAiWZuV0RGWGNiXU4lF0Kw+uV1aF1VA8f315V6LY+jCGdwDpcQwA3U4Q4a0AQCj/AMr/DmTbwX7937WLYWvHzmFP6U9/kDiRiSjQ=</latexit>state
<latexit sha1_base64="jNa2HGLjfdXv39IdIu6u478F2Ds=">AB83icbZDLSgMxFIYz9VbrerSTbAIrsqMCHZcOygr1AZyiZNOG5jIkZ8Qy9DXcuFDErS/jzrcxbWehrT8EPv5zDufkj1PBLfj+t1fa2Nza3invVvb2Dw6PqscnHaszQ1mbaqFNLyaWCa5YGzgI1ksNIzIWrBtPbuf17iMzlmv1ANOURZKMFE84JeCsMJSxfsotEGCzQbXm1/2F8DoEBdRQodag+hUONc0kU0AFsbYf+ClEOTHAqWCzSphZlhI6ISPWd6iIZDbKFzfP8IVzhjRxj0FeOH+nsiJtHYqY9cpCYztam1u/lfrZ5A0opyrNAOm6HJRkgkMGs8DwENuGAUxdUCo4e5WTMfEAoupoLIVj98jp0ruqB4/vrWrNRxFGZ+gcXaIA3aAmukMt1EYUpegZvaI3L/NevHfvY9la8oqZU/RH3ucPtQ+SEw=</latexit><latexit sha1_base64="jNa2HGLjfdXv39IdIu6u478F2Ds=">AB83icbZDLSgMxFIYz9VbrerSTbAIrsqMCHZcOygr1AZyiZNOG5jIkZ8Qy9DXcuFDErS/jzrcxbWehrT8EPv5zDufkj1PBLfj+t1fa2Nza3invVvb2Dw6PqscnHaszQ1mbaqFNLyaWCa5YGzgI1ksNIzIWrBtPbuf17iMzlmv1ANOURZKMFE84JeCsMJSxfsotEGCzQbXm1/2F8DoEBdRQodag+hUONc0kU0AFsbYf+ClEOTHAqWCzSphZlhI6ISPWd6iIZDbKFzfP8IVzhjRxj0FeOH+nsiJtHYqY9cpCYztam1u/lfrZ5A0opyrNAOm6HJRkgkMGs8DwENuGAUxdUCo4e5WTMfEAoupoLIVj98jp0ruqB4/vrWrNRxFGZ+gcXaIA3aAmukMt1EYUpegZvaI3L/NevHfvY9la8oqZU/RH3ucPtQ+SEw=</latexit><latexit sha1_base64="jNa2HGLjfdXv39IdIu6u478F2Ds=">AB83icbZDLSgMxFIYz9VbrerSTbAIrsqMCHZcOygr1AZyiZNOG5jIkZ8Qy9DXcuFDErS/jzrcxbWehrT8EPv5zDufkj1PBLfj+t1fa2Nza3invVvb2Dw6PqscnHaszQ1mbaqFNLyaWCa5YGzgI1ksNIzIWrBtPbuf17iMzlmv1ANOURZKMFE84JeCsMJSxfsotEGCzQbXm1/2F8DoEBdRQodag+hUONc0kU0AFsbYf+ClEOTHAqWCzSphZlhI6ISPWd6iIZDbKFzfP8IVzhjRxj0FeOH+nsiJtHYqY9cpCYztam1u/lfrZ5A0opyrNAOm6HJRkgkMGs8DwENuGAUxdUCo4e5WTMfEAoupoLIVj98jp0ruqB4/vrWrNRxFGZ+gcXaIA3aAmukMt1EYUpegZvaI3L/NevHfvY9la8oqZU/RH3ucPtQ+SEw=</latexit><latexit sha1_base64="jNa2HGLjfdXv39IdIu6u478F2Ds=">AB83icbZDLSgMxFIYz9VbrerSTbAIrsqMCHZcOygr1AZyiZNOG5jIkZ8Qy9DXcuFDErS/jzrcxbWehrT8EPv5zDufkj1PBLfj+t1fa2Nza3invVvb2Dw6PqscnHaszQ1mbaqFNLyaWCa5YGzgI1ksNIzIWrBtPbuf17iMzlmv1ANOURZKMFE84JeCsMJSxfsotEGCzQbXm1/2F8DoEBdRQodag+hUONc0kU0AFsbYf+ClEOTHAqWCzSphZlhI6ISPWd6iIZDbKFzfP8IVzhjRxj0FeOH+nsiJtHYqY9cpCYztam1u/lfrZ5A0opyrNAOm6HJRkgkMGs8DwENuGAUxdUCo4e5WTMfEAoupoLIVj98jp0ruqB4/vrWrNRxFGZ+gcXaIA3aAmukMt1EYUpegZvaI3L/NevHfvY9la8oqZU/RH3ucPtQ+SEw=</latexit>relay
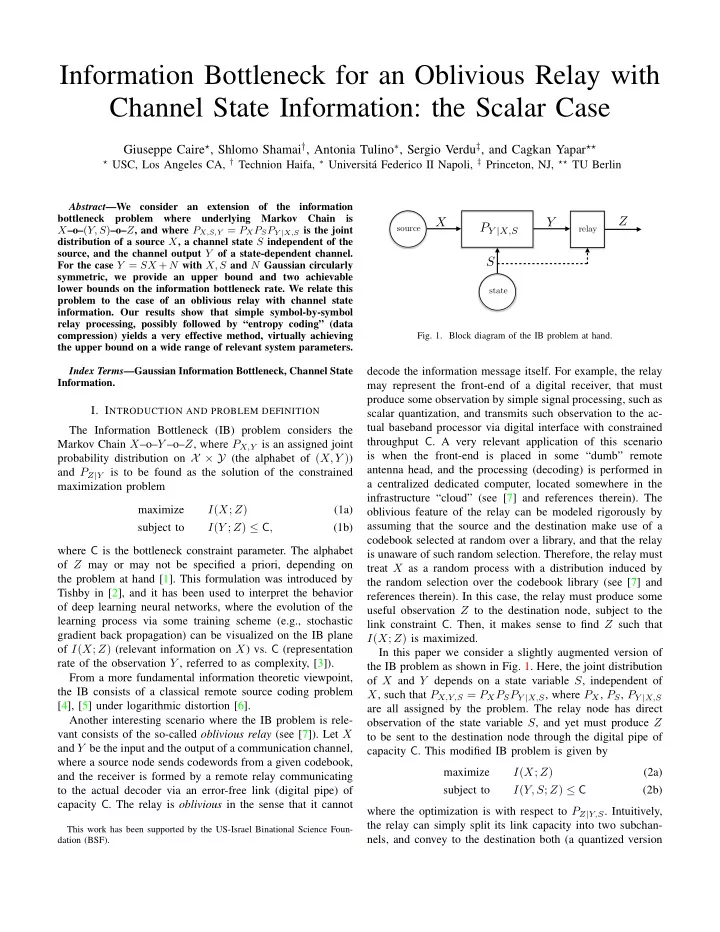
<latexit sha1_base64="kPz/N2Kcut6+LP3dh6ZWhBdBI=">AB83icbZDLSgMxFIbP1Fut6pLN8EiuCozIthlwY3LCvYC7VAyaYNzWVIMuIw9DXcuFDErS/jzrcxbWehrT8EPv5zDufkjxLOjPX9b6+0sbm1vVPereztHxweVY9POkalmtA2UVzpXoQN5UzStmW016iKRYRp91oejuvdx+pNkzJB5slNBR4LFnMCLbOGgxEpJ5yTnOZsNqza/7C6F1CAqoQaHWsPo1GCmSCiot4diYfuAnNsyxtoxwOqsMUkMTKZ4TPsOJRbUhPni5hm6cM4IxUq7Jy1auL8nciyMyUTkOgW2E7Nam5v/1fqpjRthzmSWirJclGcmQVmgeARkxTYnmABPN3K2ITLDGxLqYKi6EYPXL69C5qgeO769rzUYRxnO4BwuIYAbaMIdtKANBJ4hld481LvxXv3PpatJa+YOYU/8j5/AK7Nkg8=</latexit><latexit sha1_base64="kPz/N2Kcut6+LP3dh6ZWhBdBI=">AB83icbZDLSgMxFIbP1Fut6pLN8EiuCozIthlwY3LCvYC7VAyaYNzWVIMuIw9DXcuFDErS/jzrcxbWehrT8EPv5zDufkjxLOjPX9b6+0sbm1vVPereztHxweVY9POkalmtA2UVzpXoQN5UzStmW016iKRYRp91oejuvdx+pNkzJB5slNBR4LFnMCLbOGgxEpJ5yTnOZsNqza/7C6F1CAqoQaHWsPo1GCmSCiot4diYfuAnNsyxtoxwOqsMUkMTKZ4TPsOJRbUhPni5hm6cM4IxUq7Jy1auL8nciyMyUTkOgW2E7Nam5v/1fqpjRthzmSWirJclGcmQVmgeARkxTYnmABPN3K2ITLDGxLqYKi6EYPXL69C5qgeO769rzUYRxnO4BwuIYAbaMIdtKANBJ4hld481LvxXv3PpatJa+YOYU/8j5/AK7Nkg8=</latexit><latexit sha1_base64="kPz/N2Kcut6+LP3dh6ZWhBdBI=">AB83icbZDLSgMxFIbP1Fut6pLN8EiuCozIthlwY3LCvYC7VAyaYNzWVIMuIw9DXcuFDErS/jzrcxbWehrT8EPv5zDufkjxLOjPX9b6+0sbm1vVPereztHxweVY9POkalmtA2UVzpXoQN5UzStmW016iKRYRp91oejuvdx+pNkzJB5slNBR4LFnMCLbOGgxEpJ5yTnOZsNqza/7C6F1CAqoQaHWsPo1GCmSCiot4diYfuAnNsyxtoxwOqsMUkMTKZ4TPsOJRbUhPni5hm6cM4IxUq7Jy1auL8nciyMyUTkOgW2E7Nam5v/1fqpjRthzmSWirJclGcmQVmgeARkxTYnmABPN3K2ITLDGxLqYKi6EYPXL69C5qgeO769rzUYRxnO4BwuIYAbaMIdtKANBJ4hld481LvxXv3PpatJa+YOYU/8j5/AK7Nkg8=</latexit><latexit sha1_base64="kPz/N2Kcut6+LP3dh6ZWhBdBI=">AB83icbZDLSgMxFIbP1Fut6pLN8EiuCozIthlwY3LCvYC7VAyaYNzWVIMuIw9DXcuFDErS/jzrcxbWehrT8EPv5zDufkjxLOjPX9b6+0sbm1vVPereztHxweVY9POkalmtA2UVzpXoQN5UzStmW016iKRYRp91oejuvdx+pNkzJB5slNBR4LFnMCLbOGgxEpJ5yTnOZsNqza/7C6F1CAqoQaHWsPo1GCmSCiot4diYfuAnNsyxtoxwOqsMUkMTKZ4TPsOJRbUhPni5hm6cM4IxUq7Jy1auL8nciyMyUTkOgW2E7Nam5v/1fqpjRthzmSWirJclGcmQVmgeARkxTYnmABPN3K2ITLDGxLqYKi6EYPXL69C5qgeO769rzUYRxnO4BwuIYAbaMIdtKANBJ4hld481LvxXv3PpatJa+YOYU/8j5/AK7Nkg8=</latexit>- Fig. 1. Block diagram of the IB problem at hand.
decode the information message itself. For example, the relay may represent the front-end of a digital receiver, that must produce some observation by simple signal processing, such as scalar quantization, and transmits such observation to the ac- tual baseband processor via digital interface with constrained throughput C. A very relevant application of this scenario is when the front-end is placed in some “dumb” remote antenna head, and the processing (decoding) is performed in a centralized dedicated computer, located somewhere in the infrastructure “cloud” (see [7] and references therein). The
- blivious feature of the relay can be modeled rigorously by
assuming that the source and the destination make use of a codebook selected at random over a library, and that the relay is unaware of such random selection. Therefore, the relay must treat X as a random process with a distribution induced by the random selection over the codebook library (see [7] and references therein). In this case, the relay must produce some useful observation Z to the destination node, subject to the link constraint C. Then, it makes sense to find Z such that I(X; Z) is maximized. In this paper we consider a slightly augmented version of the IB problem as shown in Fig. 1. Here, the joint distribution
- f X and Y depends on a state variable S, independent of
X, such that PX,Y,S = PXPSPY |X,S, where PX, PS, PY |X,S are all assigned by the problem. The relay node has direct
- bservation of the state variable S, and yet must produce Z
to be sent to the destination node through the digital pipe of capacity C. This modified IB problem is given by maximize I(X; Z) (2a) subject to I(Y, S; Z) ≤ C (2b) where the optimization is with respect to PZ|Y,S. Intuitively, the relay can simply split its link capacity into two subchan- nels, and convey to the destination both (a quantized version