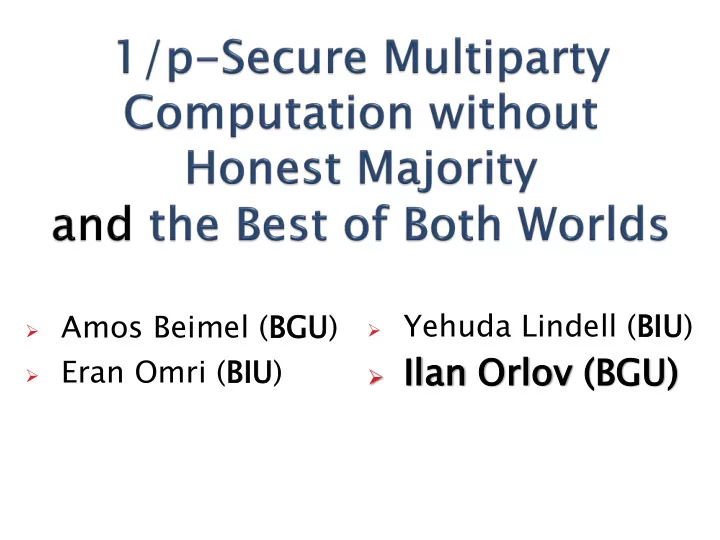
- Yehuda Lindell (BIU)
- Il
Ilan Orlov
- v (BGU
GU) )
- Amos Beimel (BGU
BGU)
- Eran Omri (BIU)
Il Ilan Orlov ov (BGU GU) ) Eran Omri (BIU) We explore - - PowerPoint PPT Presentation
Yehuda Lindell (BIU) Amos Beimel (BGU BGU) Il Ilan Orlov ov (BGU GU) ) Eran Omri (BIU) We explore 1/p-secure multiparty protocols wi without out an honest majority Positive result: 1/p-secure protocols for cons
We explore 1/p-secure multiparty protocols
wi without
Positive result:
nstant tant number of parties for computing any function with polynomial-sized range tolerating any number of corrupt parties
Impossibility result:
constant ant number of parties
Best of both worlds:
Honest majority Full security No honest majority 1/p
/p-security
2
Background Our results The ideas of our protocol Summary and Open Problems
3
4
5
m parties r-round protocol
poly(security parameter)
Adversary:
In each round:
Sees all messages of honest parties Chooses and sends messages on behalf of malicious parties
Can depend on the messages of honest parties
Broadcast channel
6
The security definitions involve a comparison
between two worlds:
7
There is a trusted party that helps with the computation
The protocol
Guarantees many nice properties:
Privacy, correctness, and Fai airne ness (fairness = corrupt parties get the output the honest parties get the output)
8
x1 x2 x3 x4 xm y = =f(x1,x ,x2,x ,x3,z4…,zm) y y y y y zm z4
Trusted party Adversary
9
[GoldreichMicaliWigderson87]: Any polynomial-time F
[Cleave86]: Any r-round m-party coin-tossing
Conclusio
10
11
[GMW87]: Security-with-abort
The adversary can learn the output, while the honest parties learn noting
Can we g get reasonabl
airne ness ss without hout honest est majori
ty?
Compare the previous two worlds: Full security – REAL fully emulates IDEAL 1/p-security – REAL emulates IDEAL within
12
Ideal World Real World
For every function F, where the size of
Impossibility: Domain or range have
13
Background Our results The ideas of our protocol Summary and Open Problems
14
F is polynomial
2.
F is constant 3.
O(log log log log n) n)
15
16
Special
Impos
[GMW 87]: Any polynomial-time F can be computed by a
protocol with full security with an honest majority
If there is no honest majority, the above protocol does
not guarantee any security
Goal: Single protocol that achieves
Honest majority Full security No honest majority Some weaker notion of security
(fallback security)
[IshaiKatzKushilevitzLindellPetrank]: Defined the problem and
suggested protocols achieving several models of fallback security
Do not achieve the above goal (for some good reasons)
17
For every function F for m parties, if
2.
then, there exists a (single) protocol
Honest majority Full security No honest majority 1/p
/p-security
This is best of both worlds! Secure-with-abort is not possibl
sible e as a fallback [IKKLP]
Strong motivation for 1/p-security
18
Background Our Results The Ideas of Our Protocol Summary and Open Problems
19
The protocol has 2 steps:
Prepressing: The parties execute a secure-with-abort
protocol:
round protocol
Rounds of Interaction: There are r rounds, in each round:
20
21
There is a special round, called i*
i*
i*, each subset of parties receives a value that depends only on its inputs
To cause “computational distance”, the adversary
must guess i*
The value of i* is concealed This structure was used in previous constructions:
[IKLP06, Katz06, GK06, GHKL06, MNS09, GK10, BOO10, …]
22
How to conceal the value of i*
How to deal with any possible abort of any
Some of the solutions:
sharing
protocol
This protocol has to conceal i* i*
Background Our Results The Ideas of Our Protocol Summary and Open Problems
23
We explore 1/p
/p-secure multiparty protocols without
an honest majority
Positive result:
/p-secure protocols for cons nstant tant number of parties*
Impossibility result:
/p-secure protocol for non-const constant ant number of parties*
Best of both worlds
Honest majority Full security No honest majority 1/p
/p-security
24
* Some restriction might apply
25
26
Is there a 1/p-secure protocol for F
F with non- constant number of parties and polynomial- sized range and domain?
Are there more efficient 1/p
/p-secure protocols?
Can we guarantee full-privacy and partial
fairness in secure multiparty computation without an honest majority?
/p security: With prob. 1/p /p privacy can be totally lost
27