Mihir Bellare, UCSD
1
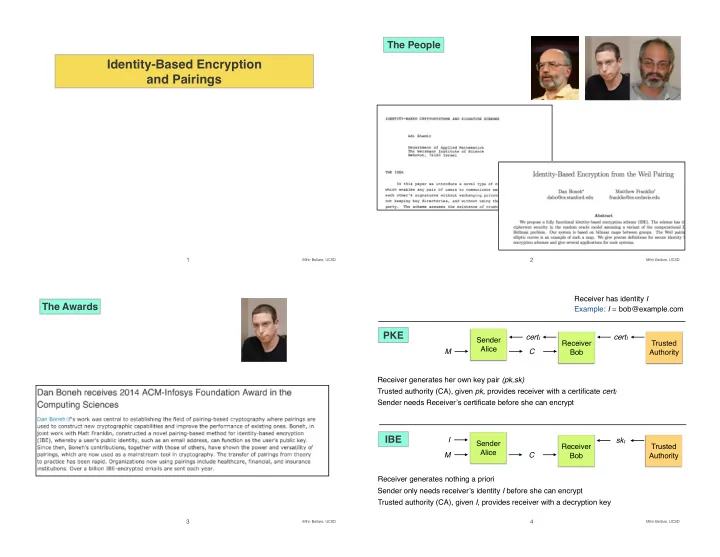
Identity-Based Encryption and Pairings
Mihir Bellare, UCSD
2
The People
Mihir Bellare, UCSD
3
The Awards
Mihir Bellare, UCSD
4
Identity-Based Encryption and Pairings 1 Mihir Bellare, UCSD 2 - - PowerPoint PPT Presentation
The People Identity-Based Encryption and Pairings 1 Mihir Bellare, UCSD 2 Mihir Bellare, UCSD Receiver has identity I The Awards Example: I = bob@example.com PKE cert I cert I Sender Receiver Trusted Alice M C Bob Authority Receiver
Mihir Bellare, UCSD
1
Mihir Bellare, UCSD
2
Mihir Bellare, UCSD
3
Mihir Bellare, UCSD
4
Mihir Bellare, UCSD
5
Mihir Bellare, UCSD
6
IBE = (P, K, E, D) is an IBE scheme.
Mihir Bellare, UCSD
7
IBE = (P, K, E, D) is an IBE scheme. Let A be an adversary. Advind-cpa
IBE
(A) = 2 Pr[IND-CPAA
IBE ⇒ true] − 1
b Challenge bit ExI Set of exposed identities ChI Set of challenge identities b0 A’s output, guess of b
Mihir Bellare, UCSD
8
IBE = (P, K, E, D) is an IBE scheme.
Mihir Bellare, UCSD
9
e,g (A) = Pr[BDHA e,g ⇒ true]
Mihir Bellare, UCSD
10
Mihir Bellare, UCSD
11
Mihir Bellare, UCSD
12
Mihir Bellare, UCSD
13