Human Factors in Coercion-Resistant Internet Voting
Oksana Kulyk
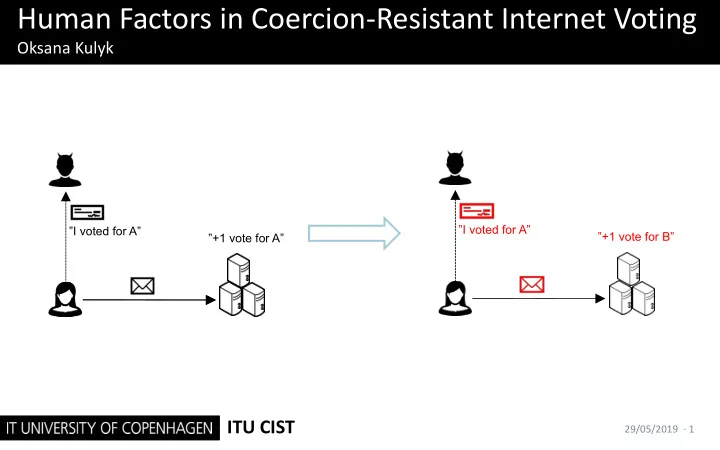
”+1 vote for A” ”I voted for A” ”+1 vote for B” ”I voted for A”
ITU CIST
29/05/2019 · 1
Human Factors in Coercion-Resistant Internet Voting Oksana Kulyk I - - PowerPoint PPT Presentation
Human Factors in Coercion-Resistant Internet Voting Oksana Kulyk I voted for A I voted for A +1 vote for B +1 vote for A ITU CIST 29/05/2019 1 Coercion in Internet Voting Internet voting is an unsupervised channel
”+1 vote for A” ”I voted for A” ”+1 vote for B” ”I voted for A”
29/05/2019 · 1
29/05/2019 · 2
voting procedure)
the-shoulder adversary)
”+1 vote for A” ”I voted for A”
29/05/2019 · 3
counter-strategy
the voter obeyed or not
”+1 vote for B” ”I voted for A”
29/05/2019 · 4
29/05/2019 · 5
”+1 invalid vote” ”I voted for A”
29/05/2019 · 6
mistakes
credential twice à further complication of the procedure
distribution
”+1 invalid vote” ”I voted for A”
29/05/2019 · 7
”+1 vote for A” ”-1 vote for A” ”+1 vote for B” ”I voted for A”
29/05/2019 · 8
updating [KTV15, BKV17]
coercion
”+1 vote for A” ”-1 vote for A” ”+1 vote for B” ”I voted for A”
29/05/2019 · 9
”8388 is the code for A” ”+1 vote for B”
A 1590 B 8388 C 5165 8388
29/05/2019 · 10
”8388 is the code for A” ”+1 vote for B”
A 1590 B 8388 C 5165
8388
29/05/2019 · 11
steps
stressful conditions?
”+1 vote for B” ”I voted for A”
29/05/2019 · 12
29/05/2019 · 13
29/05/2019 · 14
“vote for A” “vote for A” ≡ ?
29/05/2019 · 15
29/05/2019 · 16
29/05/2019 · 17
29/05/2019 · 18
29/05/2019 · 19
Thank you!
”+1 vote for B” ”I voted for A”
29/05/2019 · 20
strengthen e-Voting protocols. In Proceedings of the 12th ACM workshop on Workshop on privacy in the electronic society (pp. 237-242). ACM.
receipt-freeness and ballot privacy for the Helios voting scheme. In Proceedings of the 12th International Conference on Availability, Reliability and Security(p. 1). ACM.
coercion-resistance. In International Conference on Financial Cryptography and Data Security (pp. 47-61). Springer, Berlin, Heidelberg.
In Proceedings of the 2005 ACM workshop on Privacy in the electronic society (pp. 61-70). ACM
29/05/2019 · 21
Security’Research for Verifiability. E-Vote-ID 2018, 66.
everlasting privacy. In International Conference on Financial Cryptography and Data Security (pp. 161-175). Springer, Berlin, Heidelberg.
a practical point of view. In 2012 Seventh International Conference on Availability, Reliability and Security (pp. 180-185). IEEE.
Protocols (pp. 111-130). Springer, Berlin, Heidelberg.
29/05/2019 · 22
into smartphone security. In International Workshop on Security and Trust Management (pp. 265-273). Springer, Cham.