1 Gregory Neven IBM Zurich Research Laboratory
Identity-Based Encryption
gone WILD
2
PKI
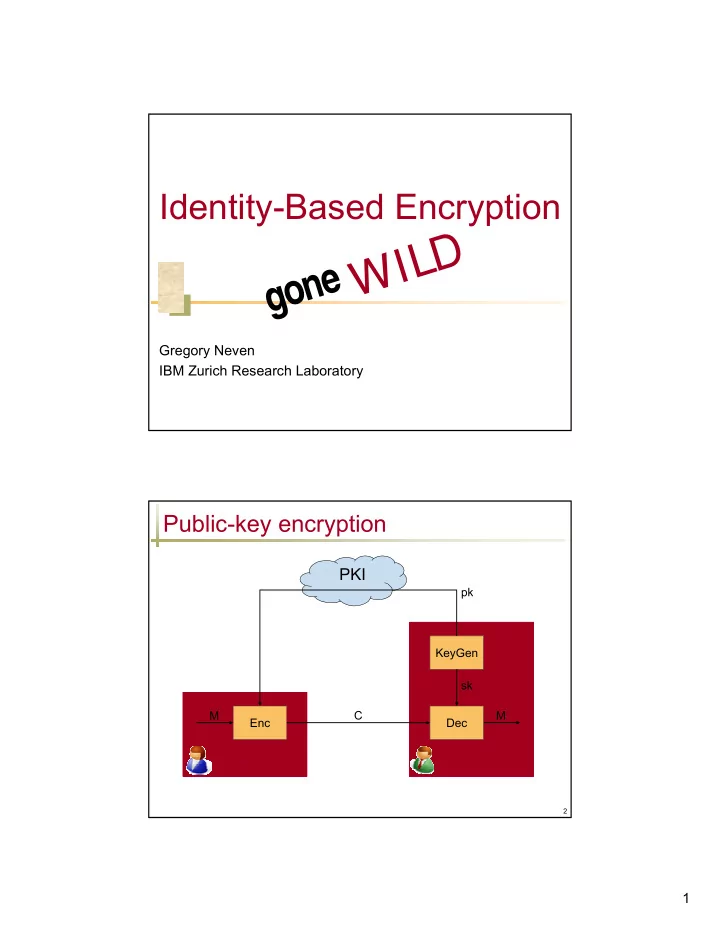
Public-key encryption
M C Sender (pk) Receiver (sk) KeyGen Dec sk Enc M pk
gone WILD Gregory Neven IBM Zurich Research Laboratory Public-key - - PDF document
Identity-Based Encryption gone WILD Gregory Neven IBM Zurich Research Laboratory Public-key encryption PKI pk KeyGen sk M C M Enc Dec Sender (pk) Receiver (sk) 2 1 Identity-based encryption (IBE) [S84] Goal: Allow to encrypt based
1 Gregory Neven IBM Zurich Research Laboratory
2
PKI
M C Sender (pk) Receiver (sk) KeyGen Dec sk Enc M pk
2
3
Goal: Allow to encrypt based solely on the receiver’s identity
msk ID skID mpk ID, M M Key distribution center (msk) C Sender (mpk) Receiver (skID) Enc Setup KeyDer Dec
4
Concept of IBE due to Shamir (1984) First efficient implementations [SK01, BF01] based on bilinear maps, aka pairings: Elliptic-curve groups G = (g), GT of prime order p Bilinear map e : G × G → GT so that e(ga,gb) = e(g,g)ab = e(gab,g) = e(g,gab) = e(ga,g)b = … → DDH problem in G is easy: Given (ga,gb,Z), decide Z = gab : e(ga,gb) = e(g,Z) → Bilinear DDH still assumed to be hard: Given (ga, gb, gc, Z), decide Z = e(g,g)abc
? ? ?
3
5
Encrypt email to ID = “bob@ibm.com” Temporary keys, key revocation: ID = “bob@ibm.com, 2007” User credentials: ID = “bob@ibm.com, role=Adminstrator” Credential is a decryption key → cryptographic policy enforcement Encrypting to the future: ID = “release-date” Trusted “clock” publishes skdate on date Searchable encryption
6
pk Sender (pk) Receiver (sk) KeyGen sk Enc W’
PKI
Trapd W Mail server Test C tW W’=W? high bandwidth low bandwidth
4
7
Generic construction of SE from IBE: SE.KeyGen = IBE.Setup SE.Trapd = IBE.KeyDer so tW = skID=W SE.Enc(W) = ( M , IBE.Enc(ID=W,M) ) for random M SE.Test(tW, (M,C)) = ( IBE.Dec(tW,C) = M ) Security relies on “anonymity” of IBE meaning ciphertext does not reveal ID
[BDOP04, ABC+05]
?
8
ID1 ID2 ID1 msk sk(ID1) ID2 sk(ID1,ID2) mpk, (ID1,ID2), M C M Receiver1 (skID1) Receiver2 (sk(ID1,ID2)) Sender (mpk) KeyDer Root (msk) KeyDer Dec … Enc
5
9
Email addresses as hierarchical identities bob@cs.univ.edu = (edu, univ, cs, bob) (edu, univ) can derive keys for @.univ.edu (edu, univ, cs) can derive keys for @cs.univ.edu
10
Restrict validity of trapdoor in time Trivial solution: encrypt to ID = “W || time” ; tW = (skW||1,…, skW||n) Logarithmic-size construction from HIBE: = tW valid for time periods 1,..,7 encrypt to ID = (W, …, i)
W’ W … 1 2 3 4 5 6 7 8
tW[1,7]
6
11
Searchable encryption revisited: consistency properties, relation to anonymous IBE, and extensions.
Crypto 2005, Journal of Cryptology 2008 Institutions involved: ENS, UCSD, DTU, U. Bristol, KUL, Gemalto
12
Allow “wildcards” in recipient identity E.g., send encrypted email to entire department: @cs.univ.edu entire university: @.univ.edu all computer scientists: @cs..edu all heads of department: head@.univ.edu the world: @..
7
13
Generic WIBE from any HIBE: Dedicated wildcard string “any” WIBE.sk(ID1,ID2) = ( HIBE.sk(ID1,ID2) , HIBE.sk(“any”,ID2) , HIBE.sk(ID1,“any”) , HIBE.sk(“any”, “any”) ) WIBE.Enc((ID1,), M) = HIBE.Enc((ID1,“any”), M) WIBE.Dec : select correct sk(.,.) and HIBE.Dec Disadvantage: |WIBE.sk| = O(2L) Direct constructions with |WIBE.sk| = O(L)
14
Identity-based encryption gone wild.
ICALP 2006 Efficient chosen-ciphertext secure identity-based encryption with wildcards.
ACISP 2007 Institutions involved: ENS, RHUL, U. Bristol, KUL
8
15
IBE with wildcard key derivation = WKD-IBE = “wicked” IBE ≈ dual of WIBE with wildcards in decryption keys e.g., derive keys for anyone: @.. entire university: @.univ.edu all system admininstrators: sysadmin@.univ.edu Applications to identity-based broadcast encryption Combination: wildcards in keys and ciphertext
16
Generalized key delegation for hierarchical identity-based encryption. Michel Abdalla, Eike Kiltz and Gregory Neven. ESORICS 2007 Institutions involved: ENS, CWI, KUL
9
17
Receiver ID3 (skID3) C Receiver ID2 (skID2) M Dec
msk List1,ID1 skID1 mpk List1, M Key distribution center (msk) C Sender (mpk) Enc KeyDer Setup Receiver ID1 (skID1) M Dec List1 List2 … C
18
Receiver ID3 (skID3) C Receiver ID2 (skID2) M Dec
msk List1,ID1 skID1 mpk List1, M Key distribution center (msk) C Sender (mpk) Enc KeyDer Setup Receiver ID1 (skID1) M Dec List1 List2 … C Trace ID2,ID3
10
19
Identity-based traitor tracing.
PKC 2007 Institutions involved: ENS, RHUL, U. Bristol, KUL, France Télécom
20
Several extensions to identity-based encryption searchable encryption wildcards traitor tracing Research retreats work top-level research international collaborations