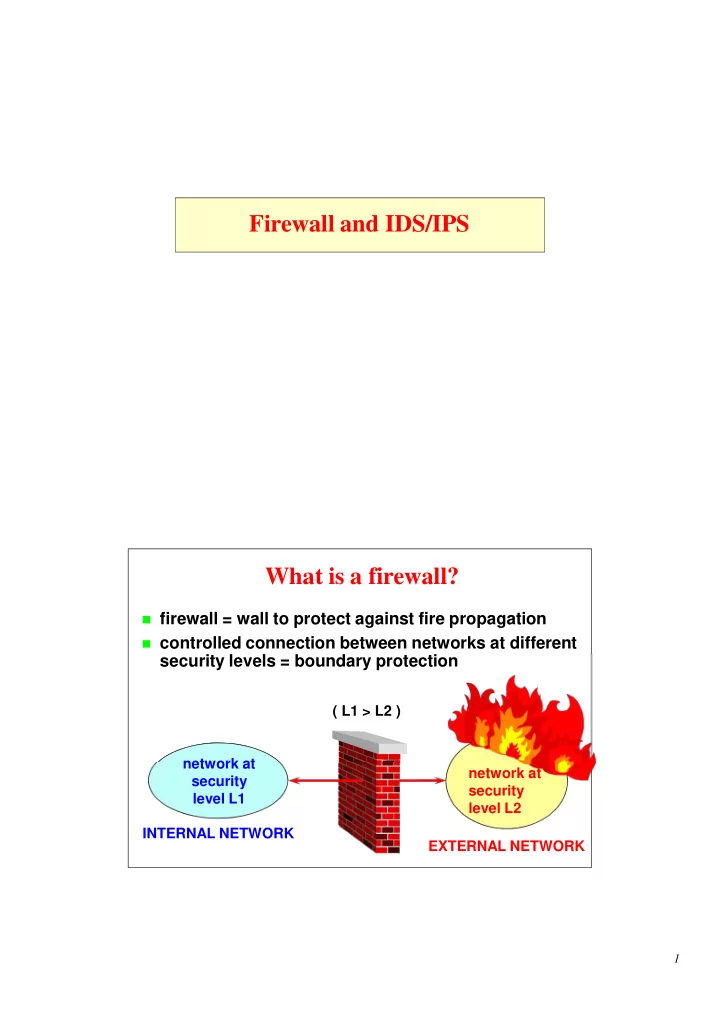
Firewall and IDS/IPS What is a firewall?
firewall = wall to protect against fire propagation controlled connection between networks at different
security levels = boundary protection
( L1 > L2 ) network at security level L2
1
Firewall and IDS/IPS What is a firewall? firewall = wall to protect - - PDF document
Firewall and IDS/IPS What is a firewall? firewall = wall to protect against fire propagation controlled connection between networks at different security levels = boundary protection ( L1 > L2 ) network at network at security
1
2
3
4
5
6
GW
7
GW
8
GW 9
GW
10
11
12
13
14
15
internal network FTP server FTP client pasv port(1040)
16
17
control connection control connection application space FTP proxy server FTP client FTP firewall OS kernel space data connection data connection 18
19
20
21
22
23
(image from wikipedia)
24
net card net card
prerouting conntrack mangle NA T (dst) (qdisc) routing decision forward filter mangle postrouting conntrack mangle NA T (src) (qdisc) deny / reject local process input filter conntrack mangle
filter conntrack mangle NA T (dst) routing decision deny / reject deny / reject
25
26
27
28
29
IDS director DMZ (host) (host) sensor(s) external network internal network
(net) sensor sensor(s) (net) sensor(s)
30
security policy
31
32
33
E-mail security
34
E-mail security
35
E-mail security
36
E-mail security
37
E-mail security
38
E-mail security
39
E-mail security
40
E-mail security
41
E-mail security
42
E-mail security
43
E-mail security
44
E-mail security
45
E-mail security
46
E-mail security
47
E-mail security
48
E-mail security
49
E-mail security
50
E-mail security
51
E-mail security
E F M
A B C D G I L
N completely trusted partially trusted untrusted unknown X Y signs X Y H
52
E-mail security
53
E-mail security
Version: 2.6.1 hIwDpHi4wHwVW/0BA/9oop5thKhbkVXxf1nILrk5X1sUD/L7WsfCBuQQqCLAufgW Cidy90kGO/zGKvrcPCK+CHQQqxxCbJDscFsmuQVArewaNIyxAvqVvNqOiVkhtc5Q NjL5VN/J9PosNcwKBah3u7vtamse1EMLtVVZxAr+rc7NJcvdG8XTbRQ1ihCpuaYA AADLVcTPRT1fpHVhO0zZn4kTpwjAty2sSpGh5hR8X8PTmWZvqjhS9joMHHTz5Esh SJQXn1HHZn8NdtHPJ4BGgVJ0FoTKpbe9zFrburR7gVBNiaAu2s1q05VXmeKgE7NW Lc74S0PHfSavpAbpHg+0dZDL6Pk9w0kVNlTbovWbjr6zuSb4Ga8Q27w9w3hF0bLX 0B0EpCy6vbOihr8OxVtO3KpRseshaCUs6LMd7kAaO5mjT+7JaqwH7U3GeKCAAa+z I0bpLA/muWBOEtEUh9g= =7T85
54
E-mail security
Text of the message
Version: 2.6.1 iQCVAwUBLuAyudzgsuo2HSCtAQESeAQAkUReUyhlAsRFktzjgIOtCogCFl6/elbM +20a71qpZWBoRviELK9sF7BQoQ3Moa35T18EeZtIHskj89mvDAAeuW3wzUcid5Hz ZiQ7vjKWqWb2lWgZ9oNbMyNMoDA+jMSCr8H0p9NguQPnNK4Lo+Gn251dBhsh4ISy vCzBoK7FLVM= =7RAd
55
E-mail security
56
E-mail security
57
E-mail security
58
E-mail security
59
E-mail security
60
E-mail security
61
E-mail security
62
E-mail security
63
E-mail security
64
E-mail security
65
E-mail security
66
E-mail security
67