1
load
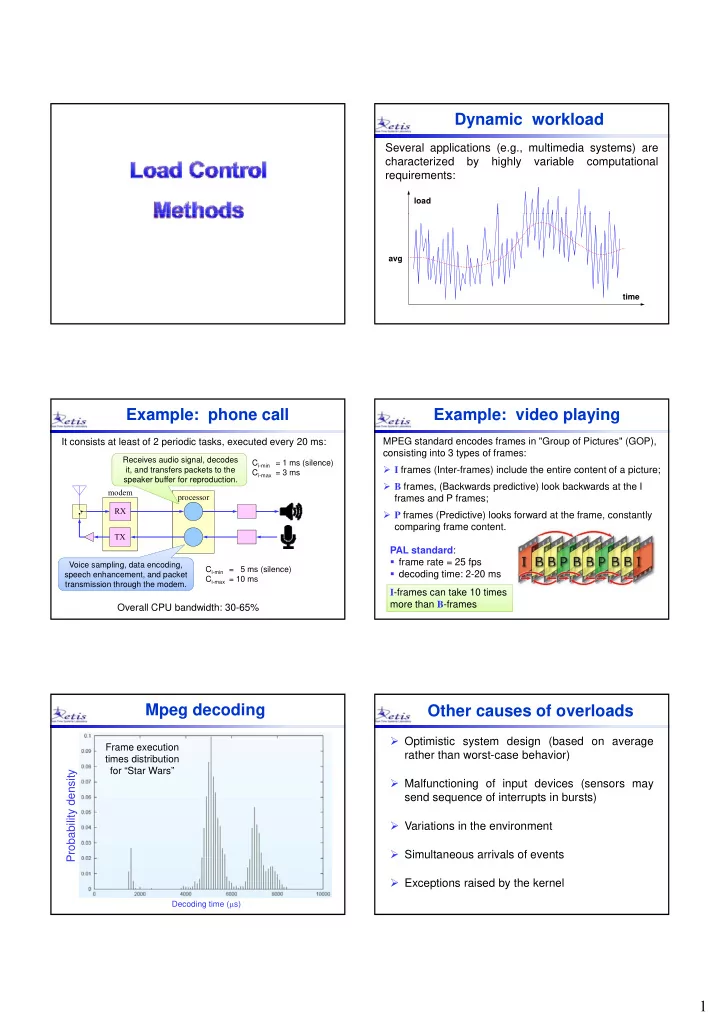
Dynamic workload
Several applications (e.g., multimedia systems) are characterized by highly variable computational requirements:
time avg
Example: phone call
It consists at least of 2 periodic tasks, executed every 20 ms:
RX modem processor Ci-min = 1 ms (silence) Ci-max = 3 ms Receives audio signal, decodes it, and transfers packets to the speaker buffer for reproduction. RX TX
Overall CPU bandwidth: 30-65%
Voice sampling, data encoding, speech enhancement, and packet transmission through the modem. Ci-min = 5 ms (silence) Ci-max = 10 ms
Example: video playing
MPEG standard encodes frames in "Group of Pictures" (GOP), consisting into 3 types of frames:
- I frames (Inter-frames) include the entire content of a picture;
- B frames, (Backwards predictive) look backwards at the I
frames and P frames;
- P frames (Predictive) looks forward at the frame, constantly
comparing frame content. PAL standard:
- frame rate = 25 fps
- decoding time: 2-20 ms
I-frames can take 10 times more than B-frames
Mpeg decoding
density
Frame execution times distribution for “Star Wars”
Decoding time (s)
Probability d
Other causes of overloads
- Optimistic system design (based on average
rather than worst-case behavior)
- Malfunctioning of input devices (sensors may
send sequence of interrupts in bursts)
- Variations in the environment
- Simultaneous arrivals of events
- Exceptions raised by the kernel