SLIDE 1
Diffie-Hellman Key Exchange
Source: Wikipedia
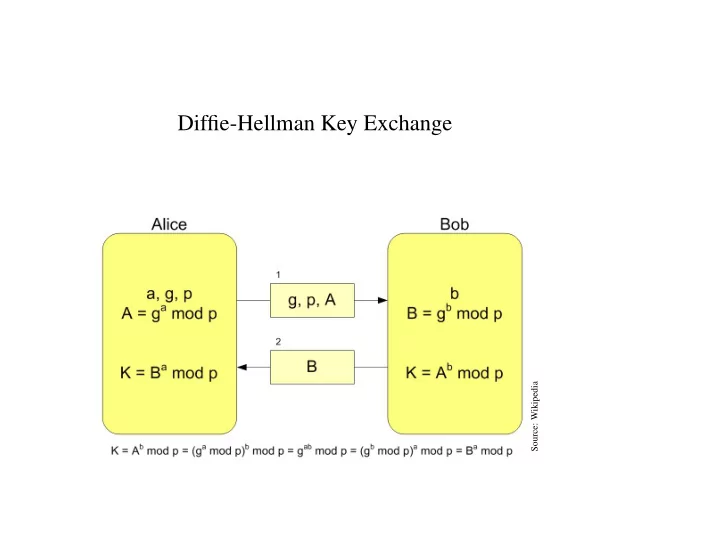
Diffie-Hellman Key Exchange Source: Wikipedia ElGamal Key - - PowerPoint PPT Presentation
Diffie-Hellman Key Exchange Source: Wikipedia ElGamal Key Generator Generate primes p and q as well as an element g Z p that generates the subgroup G q . Choose a random x from { 0 , . . . , q 1 } . Compute h = g x .
Source: Wikipedia