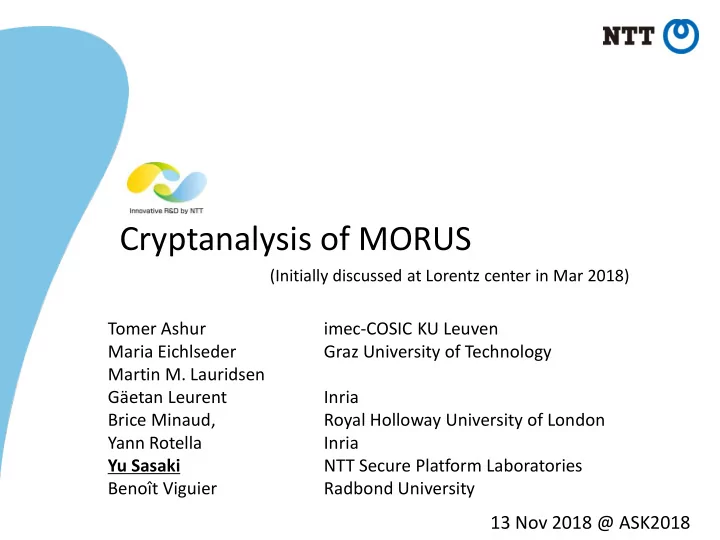
Cryptanalysis of MORUS
Tomer Ashur imec-COSIC KU Leuven Maria Eichlseder Graz University of Technology Martin M. Lauridsen Gӓetan Leurent Inria Brice Minaud, Royal Holloway University of London Yann Rotella Inria Yu Sasaki NTT Secure Platform Laboratories Benoît Viguier Radbond University
13 Nov 2018 @ ASK2018
(Initially discussed at Lorentz center in Mar 2018)