Applied Cryptography Week 1 Basic Tools and Protocols
Frank Beatrous
Applied Cryptography Week 1Basic Tools and Protocols – p.1/53
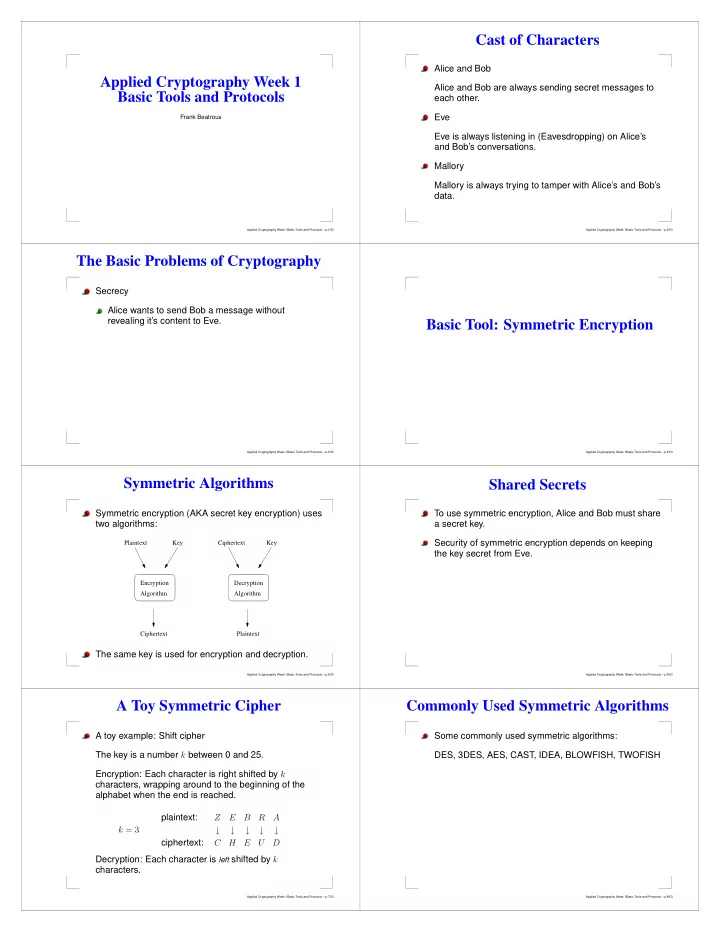
Cast of Characters
Alice and Bob Alice and Bob are always sending secret messages to each other. Eve Eve is always listening in (Eavesdropping) on Alice’s and Bob’s conversations. Mallory Mallory is always trying to tamper with Alice’s and Bob’s data.
Applied Cryptography Week 1Basic Tools and Protocols – p.2/53
The Basic Problems of Cryptography
Secrecy Alice wants to send Bob a message without revealing it’s content to Eve.
Applied Cryptography Week 1Basic Tools and Protocols – p.3/53
Basic Tool: Symmetric Encryption
Applied Cryptography Week 1Basic Tools and Protocols – p.4/53
Symmetric Algorithms
Symmetric encryption (AKA secret key encryption) uses two algorithms:
Plaintext Key Ciphertext Encryption Algorithm Decryption Algorithm Key Ciphertext Plaintext
The same key is used for encryption and decryption.
Applied Cryptography Week 1Basic Tools and Protocols – p.5/53
Shared Secrets
To use symmetric encryption, Alice and Bob must share a secret key. Security of symmetric encryption depends on keeping the key secret from Eve.
Applied Cryptography Week 1Basic Tools and Protocols – p.6/53
A Toy Symmetric Cipher
A toy example: Shift cipher The key is a number k between 0 and 25. Encryption: Each character is right shifted by k characters, wrapping around to the beginning of the alphabet when the end is reached. k = 3 plaintext: Z E B R A ↓ ↓ ↓ ↓ ↓ ciphertext: C H E U D Decryption: Each character is left shifted by k characters.
Applied Cryptography Week 1Basic Tools and Protocols – p.7/53
Commonly Used Symmetric Algorithms
Some commonly used symmetric algorithms: DES, 3DES, AES, CAST, IDEA, BLOWFISH, TWOFISH
Applied Cryptography Week 1Basic Tools and Protocols – p.8/53