SLIDE 1
Last updated 8/18/2016
Application for IRB Review for Unfunded Research Tulsa Community - - PDF document
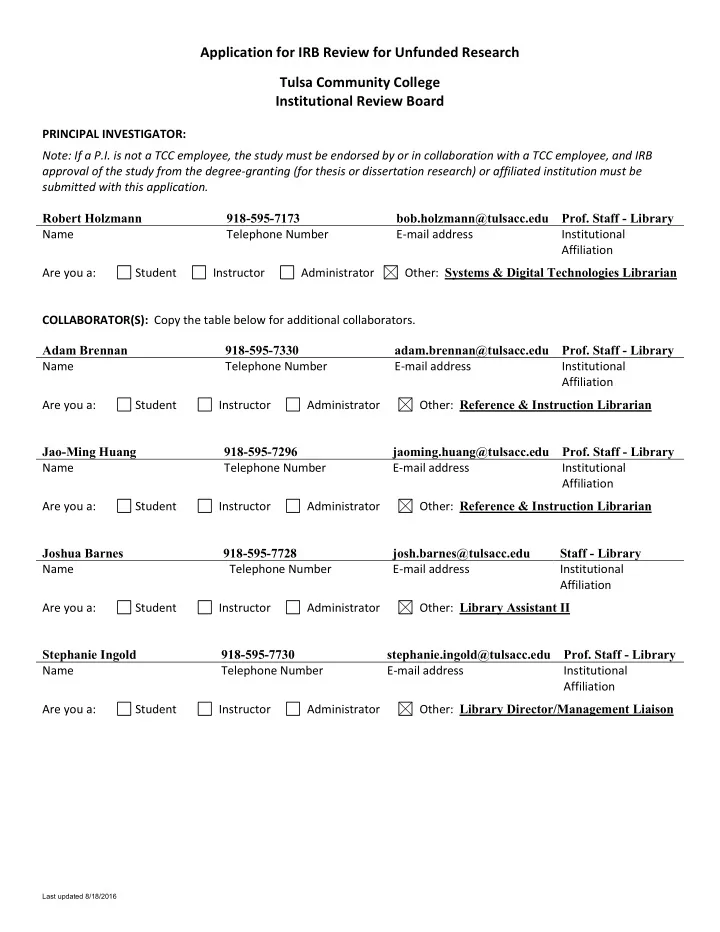
Application for IRB Review for Unfunded Research Tulsa Community College Institutional Review Board PRINCIPAL INVESTIGATOR: Note: If a P.I. is not a TCC employee, the study must be endorsed by or in collaboration with a TCC employee, and IRB
Last updated 8/18/2016
Last updated 8/18/2016
Last updated 8/18/2016
Last updated 8/18/2016
Last updated 8/18/2016
Last updated 8/18/2016
Last updated 8/18/2016
Last updated 8/18/2016
Last updated 8/18/2016