Algorithmic Questions in Higher-Order Fourier Analysis Madhur - PowerPoint PPT Presentation
Algorithmic Questions in Higher-Order Fourier Analysis Madhur Tulsiani TTI Chicago 1 1 2 2 f Based on joint works with Arnab Bhattacharyya, Eli Ben-Sasson, Pooya Hatami, Noga Ron-Zewi and Julia Wolf Decomposition Theorems
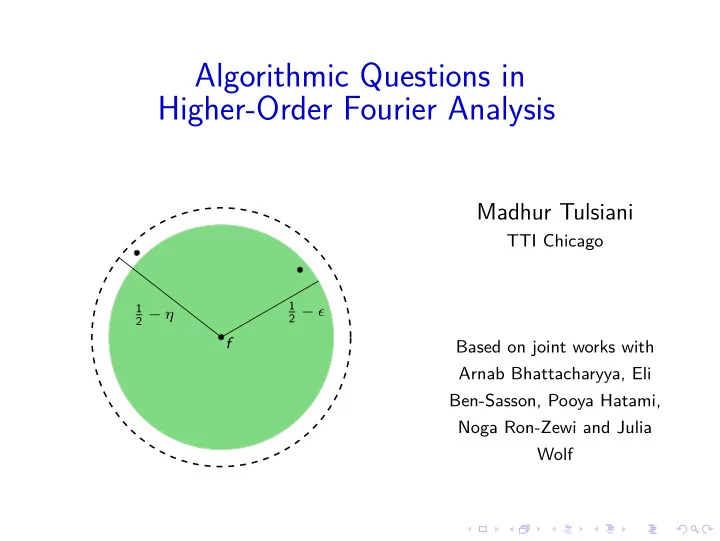
Algorithmic Questions in Higher-Order Fourier Analysis Madhur Tulsiani TTI Chicago 1 1 2 − ǫ 2 − η f Based on joint works with Arnab Bhattacharyya, Eli Ben-Sasson, Pooya Hatami, Noga Ron-Zewi and Julia Wolf
Decomposition Theorems
Decomposition Theorems Object of study Family of algorithms or functions
Decomposition Theorems = + Object of study Family of Structured No apparent algorithms or structure (Pseudorandom) functions
Decomposition Theorems = + Object of study Family of Structured No apparent algorithms or structure (Pseudorandom) functions - Decompose an object in to structured and pseudorandom parts.
Decomposition Theorems = + Object of study Family of Structured No apparent algorithms or structure (Pseudorandom) functions - Decompose an object in to structured and pseudorandom parts. - Can often ignore the pseudorandom part for many applications. Structured part easier to study.
A basic decomposition in Fourier analysis g : F n 2 → [ − 1 , 1 ]
A basic decomposition in Fourier analysis � χ α ( x ) = ( − 1 ) α · x = ( − 1 ) i α j x j g : F n 2 → [ − 1 , 1 ] α ∈ F n 2 � g = � g ( α ) χ α S
A basic decomposition in Fourier analysis � χ α ( x ) = ( − 1 ) α · x = ( − 1 ) i α j x j g : F n 2 → [ − 1 , 1 ] α ∈ F n 2 k � � � � g = � g ( α ) χ α = � g ( α ) χ α + � g ( α ) χ α = c i χ α i + f i = 1 S | � | � g ( α ) | >ǫ g ( α ) |≤ ǫ
A basic decomposition in Fourier analysis � χ α ( x ) = ( − 1 ) α · x = ( − 1 ) i α j x j g : F n 2 → [ − 1 , 1 ] α ∈ F n 2 k � � � � g = � g ( α ) χ α = � g ( α ) χ α + � g ( α ) χ α = c i χ α i + f i = 1 S | � | � g ( α ) | >ǫ g ( α ) |≤ ǫ - k ≤ 1 /ǫ 2 .
A basic decomposition in Fourier analysis � χ α ( x ) = ( − 1 ) α · x = ( − 1 ) i α j x j g : F n 2 → [ − 1 , 1 ] α ∈ F n 2 k � � � � g = � g ( α ) χ α = � g ( α ) χ α + � g ( α ) χ α = c i χ α i + f i = 1 S | � | � g ( α ) | >ǫ g ( α ) |≤ ǫ - k ≤ 1 /ǫ 2 . - f has small correlation with linear functions. For any α , |� f , χ α �| = | E x [ f ( x ) χ α ( x )] | ≤ ǫ
A basic decomposition in Fourier analysis � χ α ( x ) = ( − 1 ) α · x = ( − 1 ) i α j x j g : F n 2 → [ − 1 , 1 ] α ∈ F n 2 k � � � � g = � g ( α ) χ α = � g ( α ) χ α + � g ( α ) χ α = c i χ α i + f i = 1 S | � | � g ( α ) | >ǫ g ( α ) |≤ ǫ - k ≤ 1 /ǫ 2 . - f has small correlation with linear functions. For any α , |� f , χ α �| = | E x [ f ( x ) χ α ( x )] | ≤ ǫ - f is pseudorandom and can be ignored in many applications of Fourier analysis.
Quadratic Fourier Analysis [Gowers 98, Green 07] - “Fourier pseudorandomness” often insufficient for many applications (e.g. counting 4-term APs in a set).
Quadratic Fourier Analysis [Gowers 98, Green 07] - “Fourier pseudorandomness” often insufficient for many applications (e.g. counting 4-term APs in a set). - [Gowers 98]: Defined uniformity norms (Gowers norms). “Right” notion of pseudorandomness for many applications. � f(x) f(x+y) f(x+z) f(x+y+z) � � f � 8 U 3 = E x , y , z , w f(x+w) f(x+y+w) f(x+z+w) f(x+y+z+w)
Quadratic Fourier Analysis [Gowers 98, Green 07] - “Fourier pseudorandomness” often insufficient for many applications (e.g. counting 4-term APs in a set). - [Gowers 98]: Defined uniformity norms (Gowers norms). “Right” notion of pseudorandomness for many applications. � f(x) f(x+y) f(x+z) f(x+y+z) � � f � 8 U 3 = E x , y , z , w f(x+w) f(x+y+w) f(x+z+w) f(x+y+z+w) - � f � U 2 ≤ η ⇔ “Fourier pseudorandomness”. Measures correlation with Fourier characters (linear phase functions).
Quadratic Fourier Analysis [Gowers 98, Green 07] - “Fourier pseudorandomness” often insufficient for many applications (e.g. counting 4-term APs in a set). - [Gowers 98]: Defined uniformity norms (Gowers norms). “Right” notion of pseudorandomness for many applications. � f(x) f(x+y) f(x+z) f(x+y+z) � � f � 8 U 3 = E x , y , z , w f(x+w) f(x+y+w) f(x+z+w) f(x+y+z+w) - � f � U 2 ≤ η ⇔ “Fourier pseudorandomness”. Measures correlation with Fourier characters (linear phase functions). - [Green-Tao 05, Samorodnitsky 07]: Gowers U 3 norm approximately measures correlation with the set of quadratic phase functions. ( ( − 1 ) Q ( x ) for Q ( x ) = x T Ax + b T x + c ). For f : F n 2 → [ − 1 , 1 ] , � f , ( − 1 ) Q �� �� � ≤ ǫ . - � f � U 3 ≤ ǫ = ⇒ for all Q ,
Quadratic Fourier Analysis [Gowers 98, Green 07] - “Fourier pseudorandomness” often insufficient for many applications (e.g. counting 4-term APs in a set). - [Gowers 98]: Defined uniformity norms (Gowers norms). “Right” notion of pseudorandomness for many applications. � f(x) f(x+y) f(x+z) f(x+y+z) � � f � 8 U 3 = E x , y , z , w f(x+w) f(x+y+w) f(x+z+w) f(x+y+z+w) - � f � U 2 ≤ η ⇔ “Fourier pseudorandomness”. Measures correlation with Fourier characters (linear phase functions). - [Green-Tao 05, Samorodnitsky 07]: Gowers U 3 norm approximately measures correlation with the set of quadratic phase functions. ( ( − 1 ) Q ( x ) for Q ( x ) = x T Ax + b T x + c ). For f : F n 2 → [ − 1 , 1 ] , � f , ( − 1 ) Q �� �� � ≤ ǫ . - � f � U 3 ≤ ǫ = ⇒ for all Q , � f , ( − 1 ) Q �� �� � ≥ η ( ǫ ) . - � f � U 3 ≥ ǫ = ⇒ for some Q ,
Decompositions in Quadratic Fourier Analysis Theorem (Gowers-Wolf 09) Given ǫ > 0 , any g : F n 2 → [ − 1 , 1 ] can be decomposed as k � c i ( − 1 ) Q i + f + e g = i = 1 for quadratic functions Q 1 , . . . , Q k such that
Decompositions in Quadratic Fourier Analysis Theorem (Gowers-Wolf 09) Given ǫ > 0 , any g : F n 2 → [ − 1 , 1 ] can be decomposed as k � c i ( − 1 ) Q i + f + e g = i = 1 for quadratic functions Q 1 , . . . , Q k such that - � f � U 3 ≤ ǫ , � e � 1 ≤ ǫ
Decompositions in Quadratic Fourier Analysis Theorem (Gowers-Wolf 09) Given ǫ > 0 , any g : F n 2 → [ − 1 , 1 ] can be decomposed as k � c i ( − 1 ) Q i + f + e g = i = 1 for quadratic functions Q 1 , . . . , Q k such that - � f � U 3 ≤ ǫ , � e � 1 ≤ ǫ - � i | c i | ≤ M ( ǫ ) for M ( ǫ ) = exp ( 1 /ǫ C ) .
Decompositions in Quadratic Fourier Analysis Theorem (Gowers-Wolf 09) Given ǫ > 0 , any g : F n 2 → [ − 1 , 1 ] can be decomposed as k � c i ( − 1 ) Q i + f + e g = i = 1 for quadratic functions Q 1 , . . . , Q k such that - � f � U 3 ≤ ǫ , � e � 1 ≤ ǫ - � i | c i | ≤ M ( ǫ ) for M ( ǫ ) = exp ( 1 /ǫ C ) . Similar to basic Fourier decomposition, where we get k � g = c i χ α i ( x ) + f , i = 1 with |� f , χ α �| ≤ ǫ for all α and k ≤ 1 /ǫ 2 (also implies � i | c i | ≤ 1 /ǫ ).
Decompositions in Higher-Order Fourier Analysis Theorem (Gowers-Wolf 10) Given ǫ > 0 and p > d, there exists M ( ǫ, p ) such that any g : F n p → [ − 1 , 1 ] can be decomposed as � k c i · ω P i + f + e g = i = 1 for P 1 , . . . , P k ∈ P d (polynomials of degree at most d) such that - � f � U d + 1 ≤ ǫ , � e � 1 ≤ ǫ - � i | c i | ≤ M ( ǫ, p ) .
Decompositions in Higher-Order Fourier Analysis Theorem (Gowers-Wolf 10) Given ǫ > 0 and p > d, there exists M ( ǫ, p ) such that any g : F n p → [ − 1 , 1 ] can be decomposed as � k c i · ω P i + f + e g = i = 1 for P 1 , . . . , P k ∈ P d (polynomials of degree at most d) such that - � f � U d + 1 ≤ ǫ , � e � 1 ≤ ǫ - � i | c i | ≤ M ( ǫ, p ) . - Stronger decomposition theorems proved by [HL 11] and [BFL 12]. - Decomposition theorems for the case when p ≤ d require non-classical polynomials.
Q1: Can we compute these decompositions efficiently?
Algorithmic version of the basic Fourier decomposition Theorem (Goldreich-Levin 89) There is a randomized algorithm, which given ǫ, δ > 0 and oracle access � � n 2 log n · ( 1 /ǫ 2 ) · log ( 1 /δ ) to g : F n 2 → [ − 1 , 1 ] , runs in time O and outputs a decomposition � k g = c i · χ α i + f i = 1 such that
Algorithmic version of the basic Fourier decomposition Theorem (Goldreich-Levin 89) There is a randomized algorithm, which given ǫ, δ > 0 and oracle access � � n 2 log n · ( 1 /ǫ 2 ) · log ( 1 /δ ) to g : F n 2 → [ − 1 , 1 ] , runs in time O and outputs a decomposition � k g = c i · χ α i + f i = 1 such that - k = O ( 1 /ǫ 2 )
Algorithmic version of the basic Fourier decomposition Theorem (Goldreich-Levin 89) There is a randomized algorithm, which given ǫ, δ > 0 and oracle access � � n 2 log n · ( 1 /ǫ 2 ) · log ( 1 /δ ) to g : F n 2 → [ − 1 , 1 ] , runs in time O and outputs a decomposition � k g = c i · χ α i + f i = 1 such that - k = O ( 1 /ǫ 2 ) - P [ ∃ i such that | c i − � g ( α i ) | ≥ ǫ ] ≤ δ
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.