SLIDE 1
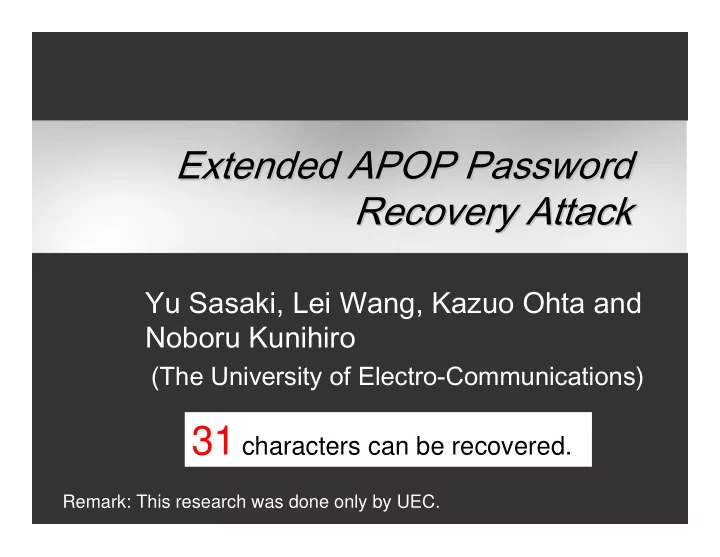
Yu Sasaki, Lei Wang, Kazuo Ohta and Noboru Kunihiro
(The University of Electro-Communications)
Extended APOP Password Extended APOP Password Recovery Attack Recovery Attack
Remark: This research was done only by UEC.
Again Guideline of IPA Again Guideline of IPA We respect the IPAs - - PowerPoint PPT Presentation
Extended APOP Password Extended APOP Password Recovery Attack Recovery Attack Yu Sasaki, Lei Wang, Kazuo Ohta and Noboru Kunihiro (The University of Electro-Communications) 31 characters can be recovered. Remark: This research was done only
Remark: This research was done only by UEC.
2
3
password C2 C1 password
password
password
password password
C1 C2
4
6