1 Last time
Internet overview what’s a protocol? network edge, core, access
network k t it hi
Home network Mobile network Global ISP Regional ISP
11/9-09 Datakommunikation - Jonny Pettersson, UmU
packet-switching versus
circuit-switching
Internet/ISP structure performance: loss, delay layering and service models history
Institutional network Regional ISP
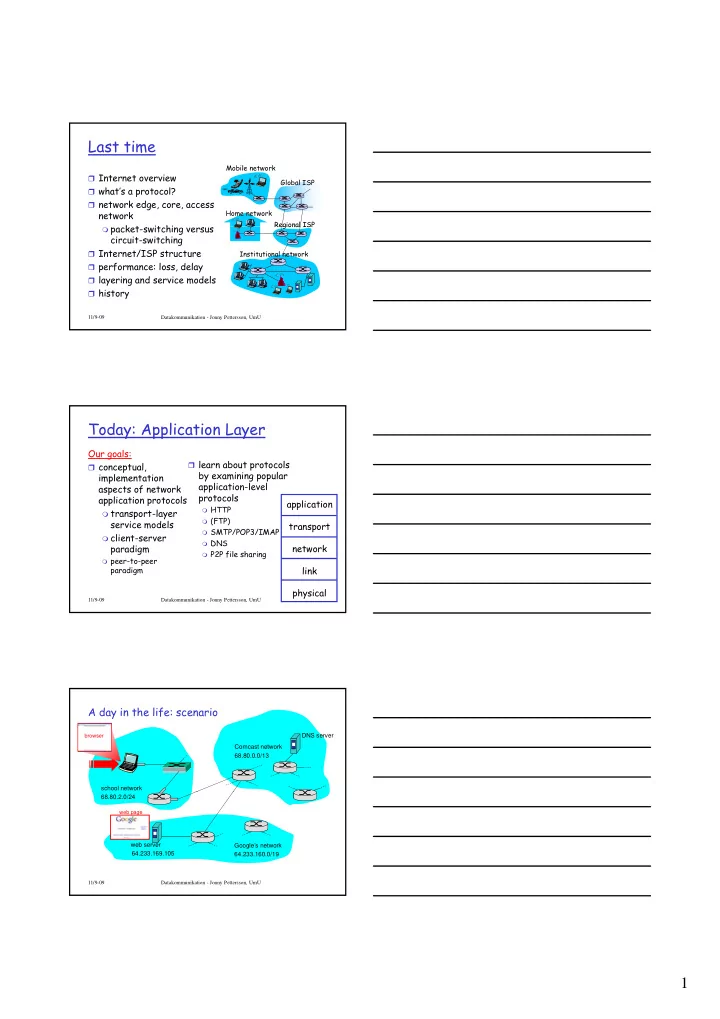
Today: Application Layer
Our goals:
conceptual,
implementation aspects of network application protocols
learn about protocols
by examining popular application-level protocols
HTTP
application
11/9-09 Datakommunikation - Jonny Pettersson, UmU
transport-layer
service models
client-server
paradigm
peer-to-peer
paradigm
HTTP (FTP) SMTP/POP3/IMAP DNS P2P file sharing
pp transport network link physical
A day in the life: scenario
Comcast network 68.80.0.0/13 DNS server school network
browser
Google’s network 64.233.160.0/19 64.233.169.105 web server 68.80.2.0/24
web page 11/9-09 Datakommunikation - Jonny Pettersson, UmU