1 Link Layer: setting the context two physically connected devices: - PDF document
Network Layer Overview: network layer services virtual circuit and datagram Goals: networks whats inside a router? understand principles behind network layer IP: Internet Protocol services: IPv4 datagram format
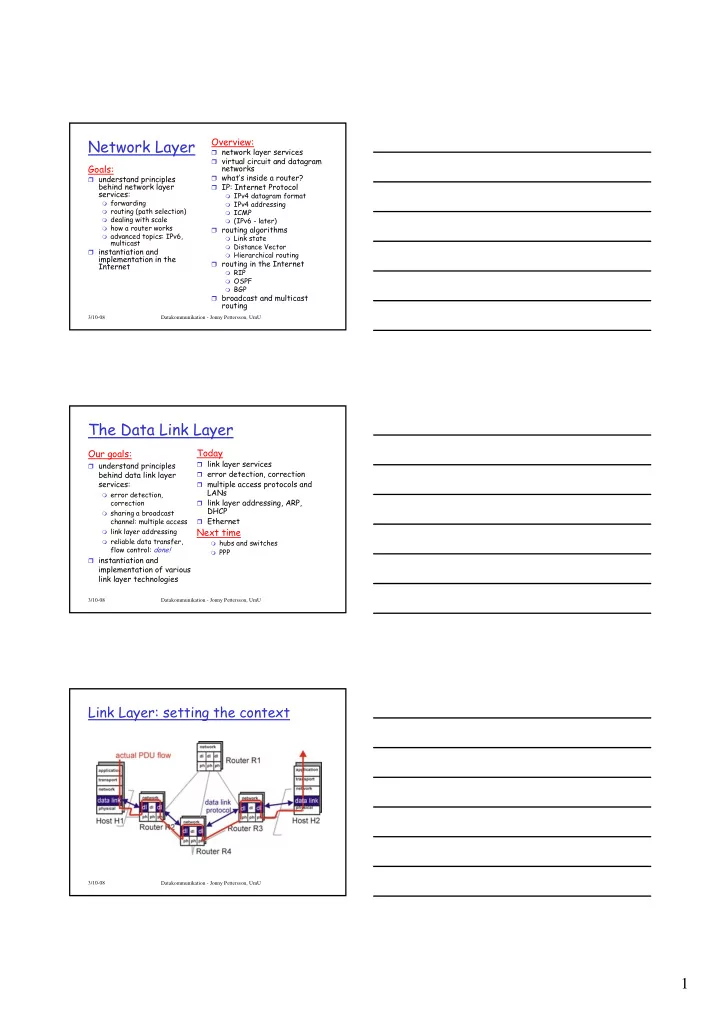
Network Layer Overview: � network layer services � virtual circuit and datagram Goals: networks � what’s inside a router? � understand principles behind network layer � IP: Internet Protocol services: � IPv4 datagram format � forwarding � IPv4 addressing � routing (path selection) � ICMP � dealing with scale � (IPv6 - later) � how a router works � routing algorithms � advanced topics: IPv6, � Link state multicast � Distance Vector � instantiation and � Hierarchical routing implementation in the � routing in the Internet Internet � RIP � OSPF � BGP � broadcast and multicast routing 3/10-08 Datakommunikation - Jonny Pettersson, UmU The Data Link Layer Today Our goals: � link layer services � understand principles behind data link layer � error detection, correction services: � multiple access protocols and LANs � error detection, � link layer addressing, ARP, correction DHCP � sharing a broadcast channel: multiple access � Ethernet � link layer addressing Next time � reliable data transfer, � hubs and switches flow control: done! � PPP � instantiation and implementation of various link layer technologies 3/10-08 Datakommunikation - Jonny Pettersson, UmU Link Layer: setting the context 3/10-08 Datakommunikation - Jonny Pettersson, UmU 1
Link Layer: setting the context � two physically connected devices: � host-router, router-router, host-host � unit of data: frame M application transport H t M network network H n H t M data link protocol link link H l H n H t M H n H t M H l physical physical frame phys. link adapter card 3/10-08 Datakommunikation - Jonny Pettersson, UmU Link Layer Services � Framing, link access: � encapsulate datagram into frame, adding header, trailer � channel access if shared medium � ‘physical addresses’ used in frame headers to identify source, dest • different from IP address! � Reliable delivery between two physically connected devices: � we learned how to do this already (chapter 3)! � seldom used on low bit error link (fiber, some twisted pair) � wireless links: high error rates • Q: why both link-level and end-end reliability? 3/10-08 Datakommunikation - Jonny Pettersson, UmU Link Layer Services (more) � Flow Control: � pacing between adjacent sending and receiving nodes � Error Detection : � errors caused by signal attenuation, noise � receiver detects presence of errors: • signals sender for retransmission or drops frame � Error Correction: � receiver identifies and corrects bit error(s) without resorting to retransmission � Half-duplex and full-duplex � with half duplex, nodes at both ends of link can transmit, but not at same time 3/10-08 Datakommunikation - Jonny Pettersson, UmU 2
Adaptors Communicating datagram rcving link layer protocol node sending node frame frame adapter adapter � link layer implemented in � sending side: “adaptor” (aka NIC) � encapsulates datagram in a frame � Ethernet card, PCMCIA card, 802.11 card � adds error checking bits, rdt, flow control, etc � typically includes: RAM, DSP (Digital Signal Processing) � receiving side chips, host bus interface, � looks for errors, rdt, flow and link interface control, etc � adapter is semi-autonomous � extracts datagram, passes to � link & physical layers rcving node 3/10-08 Datakommunikation - Jonny Pettersson, UmU Error Detection EDC= Error Detection and Correction bits (redundancy) D = Data protected by error checking, may include header fields • Error detection not 100% reliable! • protocol may miss some errors, but rarely • larger EDC field yields better detection and correction 3/10-08 Datakommunikation - Jonny Pettersson, UmU Multiple Access Links and Protocols Two types of “links”: � point-to-point � PPP for dial-up access � point-to-point link between Ethernet switch and host � broadcast (shared wire or medium) � old-fashioned Ethernet � upstream HFC � 802.11 wireless LAN humans at a shared wire (e.g., cocktail party shared RF shared RF cabled Ethernet) (shared air, acoustical) (e.g., 802.11 WiFi) (satellite) 3/10-08 Datakommunikation - Jonny Pettersson, UmU 3
Multiple Access protocols � single shared communication channel � two or more simultaneous transmissions by nodes: interference � collision if node receives two or more signals at the same time � multiple access protocol: � distributed algorithm that determines how nodes share channel, i.e., determine when node can transmit � communication about channel sharing must use channel itself! � what to look for in multiple access protocols: • synchronous or asynchronous • information needed about other nodes • robustness (e.g., to channel errors) • performance 3/10-08 Datakommunikation - Jonny Pettersson, UmU Ideal Mulitple Access Protocol Broadcast channel of rate R bps 1. When one node wants to transmit, it can send at rate R 2. When M nodes want to transmit, each can send at average rate R/M 3. Fully decentralized: � no special node to coordinate transmissions � no synchronization of clocks, slots 4. Simple 3/10-08 Datakommunikation - Jonny Pettersson, UmU MAC Protocols: a taxonomy (MAC – Media Access Control) Three broad classes: � Channel Partitioning � divide channel into smaller “pieces” (time slots, frequency, code) � allocate piece to node for exclusive use � Random Access � channel not divided, allow collisions � “recover” from collisions � “Taking turns” � tightly coordinate shared access to avoid collisions Goal: efficient, fair, simple, decentralized 3/10-08 Datakommunikation - Jonny Pettersson, UmU 4
Channel Partitioning MAC protocols: TDMA TDMA: time division multiple access � access to channel in "rounds" � each station gets fixed length slot (length = pkt trans time) in each round � unused slots go idle � example: 6-station LAN, 1,3,4 have pkt, slots 2,5,6 idle 3/10-08 Datakommunikation - Jonny Pettersson, UmU Channel Partitioning MAC protocols: FDMA FDMA: frequency division multiple access � channel spectrum divided into frequency bands � each station assigned fixed frequency band � unused transmission time in frequency bands go idle � example: 6-station LAN, 1,3,4 have pkt, frequency bands 2,5,6 idle t i m e frequency bands FDM cable 3/10-08 Datakommunikation - Jonny Pettersson, UmU Random Access protocols � When node has packet to send � transmit at full channel data rate R � no a priori coordination among nodes � two or more transmitting nodes -> “collision” � random access MAC protocol specifies: � how to detect collisions � how to recover from collisions (e.g., via delayed retransmissions) � Examples of random access MAC protocols: � slotted ALOHA � ALOHA � CSMA and CSMA/CD 3/10-08 Datakommunikation - Jonny Pettersson, UmU 5
Slotted ALOHA Assumptions Operation � all frames same size � when node obtains fresh frame, it transmits in next � time is divided into slot equal size slots = time to transmit 1 frame � no collision, node can send new frame in next slot � nodes start to transmit frames only at � if collision, node beginning of slots retransmits frame in each subsequent slot with prob. � nodes are synchronized p until success � if 2 or more nodes transmit in slot, all nodes detect collision 3/10-08 Datakommunikation - Jonny Pettersson, UmU Slotted ALOHA Cons Pros � collisions, wasting slots � single active node can � idle slots continuously transmit at full rate of channel � nodes may be able to detect collision in less � highly decentralized: than time to transmit only slots in nodes packet need to be in sync � clock synchronization � simple 3/10-08 Datakommunikation - Jonny Pettersson, UmU Slotted Aloha efficiency � For max efficiency Efficiency is the long-run with N nodes, find p* fraction of successful slots that maximizes when there are many nodes, Np(1-p) N-1 each with many frames to send � For many nodes, take � Suppose N nodes with limit of Np*(1-p*) N-1 many frames to send, as N goes to infinity, each transmits in slot gives 1/e = 0.37 with probability p � prob that node 1 has At best: channel success in a slot used for useful = p(1-p) N-1 transmissions 37% � prob that any node has of time! a success = Np(1-p) N-1 3/10-08 Datakommunikation - Jonny Pettersson, UmU 6
Pure (unslotted) ALOHA � unslotted Aloha: simpler, no synchronization � when frame first arrives � transmit immediately � collision probability increases: � frame sent at t 0 collides with other frames sent in [t 0 -1,t 0 +1] 3/10-08 Datakommunikation - Jonny Pettersson, UmU Pure Aloha efficiency P(success by given node) = P(node transmits) . P(no other node transmits in [p 0 -1,p 0 ] . P(no other node transmits in [p 0 -1,p 0 ] = p . (1-p) N-1 . (1-p) N-1 = p . (1-p) 2(N-1) … choosing optimum p and then letting n -> infty ... = 1/(2e) = 0.18 protocol constrains even worse than slotted Aloha! effective channel throughput! 3/10-08 Datakommunikation - Jonny Pettersson, UmU CSMA (Carrier Sense Multiple Access) CSMA : listen before transmit: If channel sensed idle: transmit entire frame � If channel sensed busy, defer transmission � Human analogy: don’t interrupt others! 3/10-08 Datakommunikation - Jonny Pettersson, UmU 7
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.