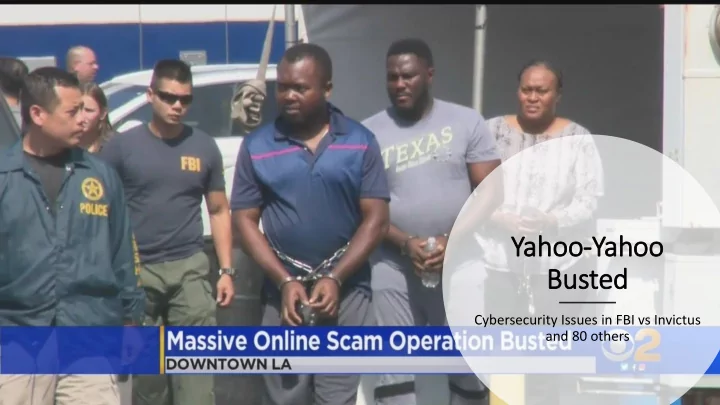
Yahoo-Yahoo Busted
Cybersecurity Issues in FBI vs Invictus and 80 others
Yahoo-Yahoo Busted Cybersecurity Issues in FBI vs Invictus and 80 - - PowerPoint PPT Presentation
Yahoo-Yahoo Busted Cybersecurity Issues in FBI vs Invictus and 80 others Courtesy: https://www.fbi.gov/ In Invictus Obi i (O (OBINWANNE OKEKE) A spear phishing on CFO of Unatrac Holding Limited, UK Unatrac email account was hosted
Cybersecurity Issues in FBI vs Invictus and 80 others
Courtesy: https://www.fbi.gov/
Limited, UK
Microsoft Office365
credentials to the fake logon page
account
from the email to the finance team
the conversation from the CFO
between April 11 and April 19, 2018
from the company
iconoclast1960@gmail.com
Twitter usemame of "@invictusobi.“
Type of Cyberattack on the CFO:
US Banks Involved 1. Bank of America 2. BBVA Compass Bancshares, Inc. 3. CalCom Federal Credit Union 4. Capital One Bank 5. Citibank N.A. 6. Citizens Financial Group 7. Comerica Bank 8. J.P. Morgan Chase N.A. 9. PNC Bank, Regions Financial Corporation
Business Email Compromise
when a hacker gains unauthorized access to a business email account,
to and/or from the email account,
email account
a separate fraudulent email account to communicate with personnel from a victim company,
an unauthorized wire transfer.
such as
to the email account of an escrow company or real estate agent,
unsuspecting buyer who is seeking to purchase property,
payment for purchase of property
legitimate bank account of an escrow company.
schemes where fraudsters hack escrow company email systems, impersonate employees and direct payments that funnel money back to themselves.
REDACTED EMAIL 5 also highlighted specific accounts which were engaged in large pending financial transactions. For example,
REDACTED EMAIL 5 to iconoclastl960@gmail.com advised of an upcoming real estate transaction valued at $585,000. In the email, REDACTED EMAIL 5 claimed the buyer had already paid 10%, with a remaining balance due of $526,000. REDACTED EMAIL 5 suggested to iconoclastl960@gmail.com that it would "make sense to tell them go transfer this balance this week prior to next week settlement."
partners or friendship
platforms.
fictitious or fake names, locations, images, and personas,
relationships with prospective romance scam victims.
behalf of the scammers.
captain stationed in Syria reached out to a Japanese woman on an international site for digital pen pals.
international romance with the man sending daily emails in English that she translated via Google. The man who called himself Terry Garcia asked for money
federal court documents. Over 10 months, she sent him a total of $200,000 that she borrowed from friends, her ex-husband and other relatives to make her love interest happy.
an international online scam ran by two Nigerian men in the Los Angeles area with the help of associates in their home country and other nations, federal officials say.
the 10 months that she had a relationship with Garcia. During that time, the fraudster(s) emailed her as many as 10 to 15 times each day, and Garcia was asking her to make the payments, so she kept paying to accounts in Turkey
FBI Investigators detailed an intricate scam traced to two key suspects who oversaw the fraudulent transfer of at least $6 million and the attempted theft of an additional $40 million. Once co-conspirators. who based in Nigeria, the United States and other countries persuaded victims to send money under false pretenses, the two Nigerian men who lived in Southern California coordinated the receipt of funds, the indictment says. The two men provided bank and money-service accounts that received funds
complaint alleges. The two men were arrested. All defendants will face charges of conspiracy to commit fraud, conspiracy to launder money, and aggravated identity theft. Some also will face fraud and money laundering charges.
mails with extensions that are similar to company e-mail. For example, legitimate e-mail
an e-mail rule to flag e-mail communications where the “reply” e-mail address is different from the “from” e-mail address shown.
employee/internal accounts are one color and e- mails from non-employee/external accounts are another.
adding additional two-factor authentication such as having secondary sign-off by company personnel.
to the encrypted database should require Multi Factor Authentication and several levels of human authentication (most especially from the paying party
banking authorities on setting up an end to end encrypted database for their business account details with which they regularly (or intending to) conduct business transactions. This database will be used in verification before transfer/transaction is authorized.
phone verification as part
a two-factor authentication; use previously known numbers, not the numbers provided in the e-mail request.
funds to determine if the requests are out of the
employees- CEO, CFO, etc)
engineering, phishing attacks, spoofing and other attacking mechanism in use.
prevent spammers from sending messages on behalf
authorized email servers
particular escrow website or service.
Be wary the moment a seller begins to stipulate the escrow site that must be used to complete a transaction
to you, that is a big red flag. An automated or generic message is also a strong indication of a scam. If the escrow website does not list any phone number or address, there is no need dealing with them in the first place.
and embed it on a fraudulent website. It is therefore essential to verify all endorsements and credentials on an
always ask you to wire money from your bank to theirs and will provide you an account number and a routing number.
escrow websites will often use a domain name that is close to the real one to trick their victims. Be sure that you have entered the correct URL and have landed on the right website.
“secure” are emphasized. When it
comes to choosing a domain name, there are lots of ways scammers shoot themselves in the foot. The first is that too much emphasis is placed on the words “safe” and “secure.” Some push their luck too far by having these words included in their domain name (something like secure- escrow.com). The use of a dash in the domain name of an escrow company is also a red flag
Establishing of bond quickly, ask a lot of personal questions, ask for financial help, etc
personal information like your full name, date of birth and home address with a stranger, you may not know what they’ll do with it.
request is coming from someone you think you know, check with them offline to ensure that it’s really them.
tend to want to take their criminal activity
you to interact with them via social media
website has no proof of them asking you for money
careful when using your webcam with a new online love interest, even if it’s someone whom you think you know. The footage could be used against you.
something is wrong, it may be. Be careful