SLIDE 1
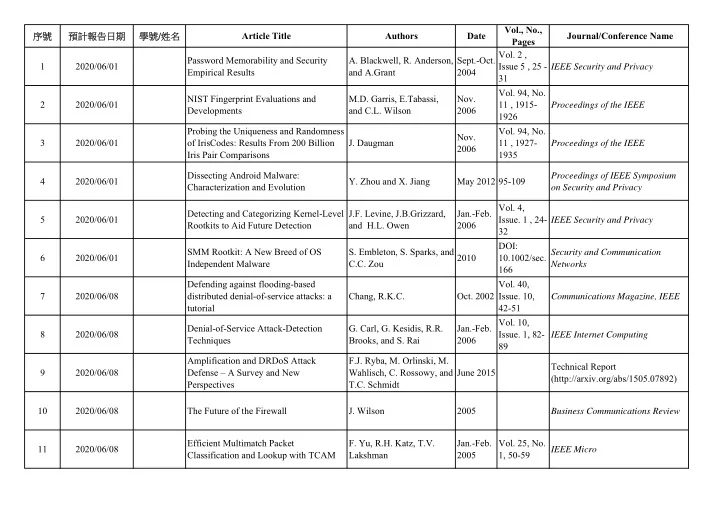
1 2020/06/01 Password Memorability and Security Empirical Results
- A. Blackwell, R. Anderson,
and A.Grant Sept.-Oct. 2004
- Vol. 2 ,
Issue 5 , 25 - 31 IEEE Security and Privacy 2 2020/06/01 NIST Fingerprint Evaluations and Developments M.D. Garris, E.Tabassi, and C.L. Wilson Nov. 2006
- Vol. 94, No.
11 , 1915- 1926 Proceedings of the IEEE 3 2020/06/01 Probing the Uniqueness and Randomness
- f IrisCodes: Results From 200 Billion
Iris Pair Comparisons
- J. Daugman
Nov. 2006
- Vol. 94, No.
11 , 1927- 1935 Proceedings of the IEEE 4 2020/06/01 Dissecting Android Malware: Characterization and Evolution
- Y. Zhou and X. Jiang
May 2012 95-109 Proceedings of IEEE Symposium
- n Security and Privacy
5 2020/06/01 Detecting and Categorizing Kernel-Level Rootkits to Aid Future Detection J.F. Levine, J.B.Grizzard, and H.L. Owen Jan.-Feb. 2006
- Vol. 4,
- Issue. 1 , 24-
32 IEEE Security and Privacy 6 2020/06/01 SMM Rootkit: A New Breed of OS Independent Malware
- S. Embleton, S. Sparks, and
C.C. Zou 2010 DOI: 10.1002/sec. 166 Security and Communication Networks 7 2020/06/08 Defending against flooding-based distributed denial-of-service attacks: a tutorial Chang, R.K.C.
- Oct. 2002
- Vol. 40,
- Issue. 10,
42-51 Communications Magazine, IEEE 8 2020/06/08 Denial-of-Service Attack-Detection Techniques
- G. Carl, G. Kesidis, R.R.
Brooks, and S. Rai Jan.-Feb. 2006
- Vol. 10,
- Issue. 1, 82-
89 IEEE Internet Computing 9 2020/06/08 Amplification and DRDoS Attack Defense – A Survey and New Perspectives F.J. Ryba, M. Orlinski, M. Wahlisch, C. Rossowy, and T.C. Schmidt June 2015 Technical Report (http://arxiv.org/abs/1505.07892) 10 2020/06/08 The Future of the Firewall
- J. Wilson
2005 Business Communications Review 11 2020/06/08 Efficient Multimatch Packet Classification and Lookup with TCAM
- F. Yu, R.H. Katz, T.V.
Lakshman Jan.-Feb. 2005
- Vol. 25, No.