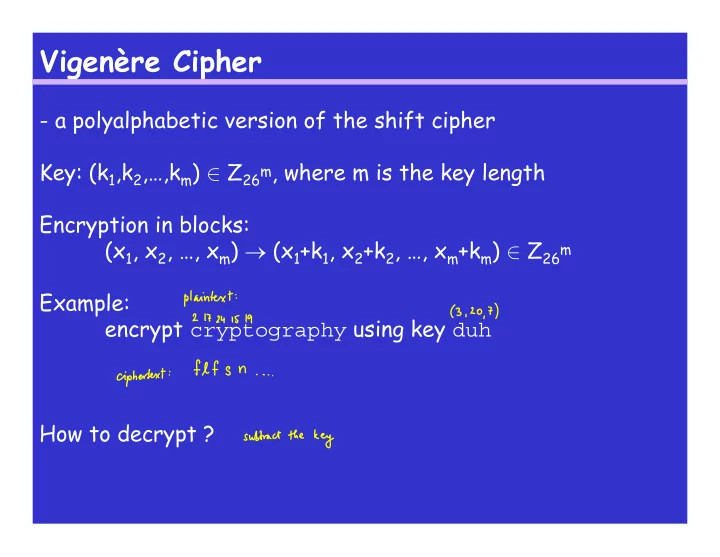
SLIDE 1 Vigenère Cipher
- a polyalphabetic version of the shift cipher
Key: (k1,k2,…,km) ∈ Z26m, where m is the key length Encryption in blocks: (x1, x2, …, xm) → (x1+k1, x2+k2, …, xm+km) ∈ Z26m Example: encrypt cryptography using key duh How to decrypt ?

SLIDE 2 Cryptanalysis of the Vigenère Cipher
- if m small:
- exhaustive search might be ok
- how many keys ?
- known plaintext attack: easy / hard ?
- ciphertext-only attack
- long thought safe against this attack
- what do we know now ?
- first find the key length m: counting coincidences
(see Section 2.3.1), Kasiski test, index of coincidence

SLIDE 3 Kasiski test
- two identical segments of ciphertext of length ≥ 3 likely
correspond to the same segments of plaintext
- if two such segments are δ positions apart, what is the likely
relationship between m and δ ? Example (Stinson, Exercise 1.21 1(b) using Vigenère):
KCCPKBGUFDPHQTYAVINRRTMVGRKDNBVFDETDGILTXRGUD DKOTFMBPVGEGLTGCKQRACQCWDNAWCRXIZAKFTLEWRPTYC QKYVXCHKFTPONCQQRHJVAJUWETMCMSPKQDYHJVDAHCTRL SVSKCGCZQQDZXGSFRLSWCWSJTBHAFSIASPRJAHKJRJUMV GKMITZHFPDISPZLVLGWTFPLKKEBDPGCEBSHCTJRWXBAFS PEZQNRWXCVYCGAONWDDKACKAWBBIKFTIOVKCGGHJVLNHI FFSQESVYCLACNVRWBBIREPBBVFEXOSCDYGZWPFDTKFQIY CWHJVLNHIQIBTKHJVNPIST
Trigram HJV: positions 108, 126, 264, 318, and 330. Conclusions ?

SLIDE 4
Index of Coincidence
Reasoning: Let y = y1y2…yn be the ciphertext. For a given m, we define these substrings of y: y1 = y1ym+1y2m+1… y2 = y2ym+2y2m+2… : : : : ym = ymy2my3m… If m is divisible by the key length, what property do we expect from these strings ? If m not divisible by the key length, then what ?

SLIDE 5
Index of Coincidence
Example: For m=6 and the text from slide 3: y1 = KGQNGVGGTGCQWAWQHNJEPJTKQFWAP… y2 = CUTRRFIUFEKCCKRKKCVTKVRCDRSFR… y3 = CFYRKDLDMGQWRFPYFQAMQDLGZLJSJ… y4 = PDATDETDBLRDXTTVTQJCDASCXSTIA… Y5 = KPVMNTXKPTANILYXPRUMYHVZGWBAH… Y6 = BHIVBDROVGCAZECCOHWSHCSQSCHSK…

SLIDE 6 Index of Coincidence
Def: Suppose that x = x1x2…xn is a string of n alphabetic
- characters. The index of coincidence of x, denoted Ic(x), is
defined to be the probability that two random elements of x are identical. Thus, Ic(x) = where fi, i∈ Z26 is the number of occurrences of the symbol i in the string x.

SLIDE 7
Index of Coincidence
For English text, the index of coincidence is approximately ∑i=025 pi2 = 0.066 where pi is the probability of occurrence of symbol i (see Table 2.1). What is the index of coincidence of shift ciphertext, if plaintext is English ? For a completely random text, the index of coincidence is approximately Idea: find m so that the index of coincidence close to 0.066

SLIDE 8
Index of Coincidence
Example from slide 3: m = 1: 0.041 m = 2: 0.038, 0.047 m = 3: 0.056, 0.048, 0.048 m = 4: 0.037, 0.042, 0.037, 0.050 m = 5: 0.043, 0.043, 0.031, 0.035, 0.043 m = 6: 0.063, 0.084, 0.049, 0.065, 0.042, 0.071 m = 7: 0.031, 0.044, 0.043, 0.038, 0.044, 0.044, 0.041 What m do we choose ?

SLIDE 9 Computing the Key
- need to find (k1,k2,…,km)
- let fi be the number of occurrences of symbol i, i∈ Z26 in yi;
let n’ be the length of yi Idea 1: use frequencies to determine ki Idea 2:
- more precise but needs more computation
- for a shift g, we expect the normalized frequencies (divide
by n’) fg/n’, fg+1/n’, fg+2/n’, …, fg+25/n’ to be “close to” p0,p1,…,p25 iff g = ki

SLIDE 10 Computing the Key
Idea 2, continued:
Mg = ∑i=025 pifg+i/n’
- if g=ki, what do we expect Mg to be ?
- if g≠ ki, what do we expect Mg to be ?
- algorithm to determine the key ?