SQL Injection Attack
1
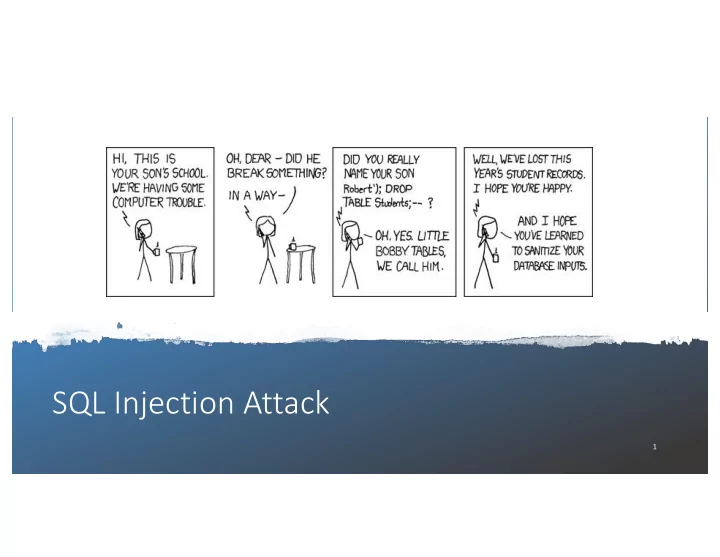
SQL Injection Attack 1 Brief Tutorial of SQL MySQL: an open-source - - PowerPoint PPT Presentation
SQL Injection Attack 1 Brief Tutorial of SQL MySQL: an open-source relational database management system Log in to MySQL Create a Database : SHOW DATABSES command: list existing databases. Create a new database called
1
2
3
4
Asks the database for all its records, including all the columns Asks the database
and Salary columns
5
6
7
8
9
10
database.
11
Once the submit button is clicked, send out an HTTP request with the data attached
12
request will be saved to an array $_GET or $_POST.
13
database using.
14
15
16
17
Is it possible for a user to change the meaning of the SQL statement?
18
19
20
INTO, we will have chance to change the database.
changing passwords. It asks users to fill in three pieces of information, EID, old password and new password.
HTTP POST request will be sent to the server-side script changepasswd.php, which uses an UPDATE statement to change the user’s password.
21
using the SQL injection vulnerability. How?
attribute for us, the salary attribute. The SQL statement will now look as follows.
EID (eid5001), not his password. How can she execute the attack?
22
statement.
delete the entire dbtest database, we can type the following in the EID box
appended a new SQL statement to the existing SQL statement string.
mysqli::query() API doesn’t allow multiple queries to run in the database server.
23
recommended]
24
Mixing data and code
system() function
25
interpreted as code.
the characters that have special meanings in SQL. The following code snippet shows how to use this API.
26
the database server knows not to retrieve any code from the data channel.
statement needs to be executed repeatedly.
unspecified
template and stores the result without executing it.
27
The vulnerable version: code and data are mixed together. Using prepared statements, we separate code and data. Send code Send data Start execution
28
29
30