CPSC 410--Richard Furuta 1/21/991/21/99 1
CPSC 410-Richard Furuta 01/19/99 1
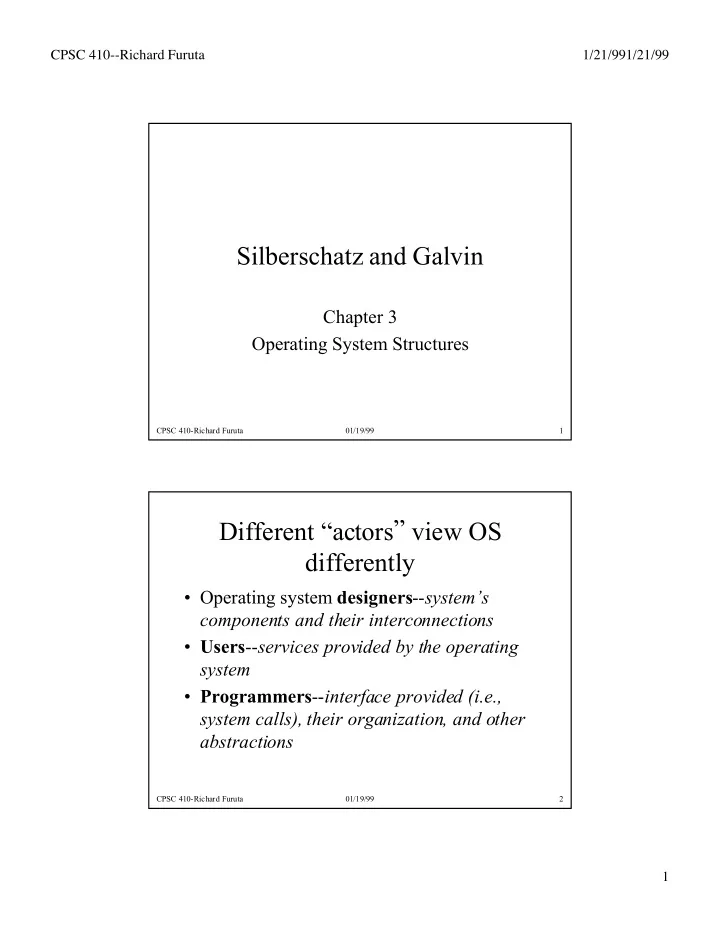
Silberschatz and Galvin
Chapter 3 Operating System Structures
CPSC 410-Richard Furuta 01/19/99 2
Silberschatz and Galvin Chapter 3 Operating System Structures CPSC - - PDF document
CPSC 410--Richard Furuta 1/21/991/21/99 Silberschatz and Galvin Chapter 3 Operating System Structures CPSC 410-Richard Furuta 01/19/99 1 Different actors view OS differently Operating system designers -- systems components and
CPSC 410-Richard Furuta 01/19/99 1
CPSC 410-Richard Furuta 01/19/99 2
CPSC 410-Richard Furuta 01/19/99 3
CPSC 410-Richard Furuta 01/19/99 4
CPSC 410-Richard Furuta 01/19/99 5
CPSC 410-Richard Furuta 01/19/99 6
CPSC 410-Richard Furuta 01/19/99 7
CPSC 410-Richard Furuta 01/19/99 8
CPSC 410-Richard Furuta 01/19/99 9
CPSC 410-Richard Furuta 01/19/99 10
CPSC 410-Richard Furuta 01/19/99 11
CPSC 410-Richard Furuta 01/19/99 12
CPSC 410-Richard Furuta 01/19/99 13
CPSC 410-Richard Furuta 01/19/99 14
CPSC 410-Richard Furuta 01/19/99 15
CPSC 410-Richard Furuta 01/19/99 16
CPSC 410-Richard Furuta 01/19/99 17
CPSC 410-Richard Furuta 01/19/99 18
CPSC 410-Richard Furuta 01/19/99 19
CPSC 410-Richard Furuta 01/19/99 20
CPSC 410-Richard Furuta 01/19/99 21
CPSC 410-Richard Furuta 01/19/99 22
CPSC 410-Richard Furuta 01/19/99 23
CPSC 410-Richard Furuta 01/19/99 24
CPSC 410-Richard Furuta 01/19/99 25
CPSC 410-Richard Furuta 01/19/99 26
CPSC 410-Richard Furuta 01/19/99 27
¥ Consists of everything below the system-call interface and above the physical hardware ¥ Provides the file system, CPU scheduling, memory management, and other operating-system functions; a large number of functions for one level.
CPSC 410-Richard Furuta 01/19/99 28
CPSC 410-Richard Furuta 01/19/99 29
CPSC 410-Richard Furuta 01/19/99 30
CPSC 410-Richard Furuta 01/19/99 31
CPSC 410-Richard Furuta 01/19/99 32
CPSC 410-Richard Furuta 01/19/99 33
CPSC 410-Richard Furuta 01/19/99 34
CPSC 410-Richard Furuta 01/19/99 35
CPSC 410-Richard Furuta 01/19/99 36
Ð CPU to be used Ð Amount of memory available Ð Available devices Ð Operating system options desired, e.g., what job mix is expected, etc.