Analysing Security Protocols Using Automated Reasoning
Graham Steel
T H E U N I V E R S I T Y O F E D I N B U R G H
2
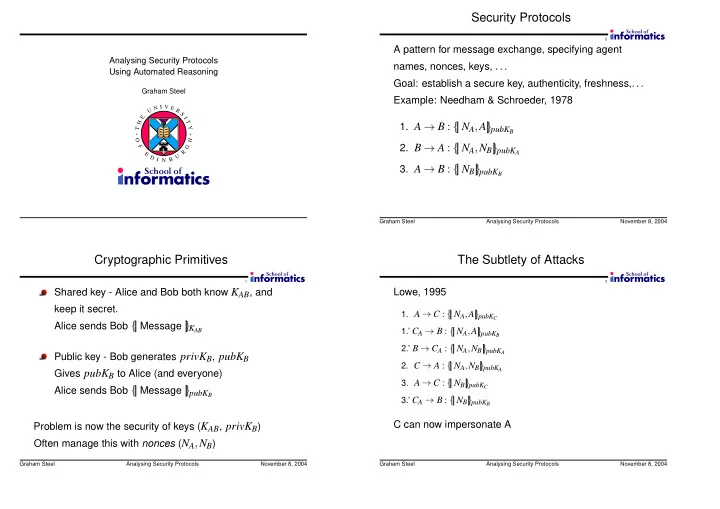
Security Protocols
A pattern for message exchange, specifying agent names, nonces, keys,
- Goal: establish a secure key, authenticity, freshness,
- Example: Needham & Schroeder, 1978
- 1. A
B :
✂✄NA
☎A
✆ ✄pubKB
- 2. B
A :
✂✄NA
☎NB
✆ ✄pubKA
- 3. A
B :
✂✄NB
✆ ✄pubKB
Graham Steel Analysing Security Protocols November 8, 2004
1
Cryptographic Primitives
Shared key - Alice and Bob both know KAB, and keep it secret. Alice sends Bob
✂✄Message
✆ ✄KAB
Public key - Bob generates privKB, pubKB Gives pubKB to Alice (and everyone) Alice sends Bob
✂✄Message
✆ ✄pubKB
Problem is now the security of keys (KAB, privKB) Often manage this with nonces (NA
☎NB)
Graham Steel Analysing Security Protocols November 8, 2004
3
The Subtlety of Attacks
Lowe, 1995
- 1. A
C :
✞✟NA
✠A
✡ ✟pubKC
1.’ CA
✝B :
✞✟NA
✠A
✡ ✟pubKB
2.’ B
✝CA :
✞✟NA
✠NB
✡ ✟pubKA
- 2. C
A :
✞✟NA
✠NB
✡ ✟pubKA
- 3. A
C :
✞✟NB
✡ ✟pubKC
3.’ CA
✝B :
✞✟NB
✡ ✟pubKB
C can now impersonate A
Graham Steel Analysing Security Protocols November 8, 2004