Reusable Non-Interactive Secure Computation Melissa Chase (MSR - - PowerPoint PPT Presentation
Reusable Non-Interactive Secure Computation Melissa Chase (MSR - - PowerPoint PPT Presentation
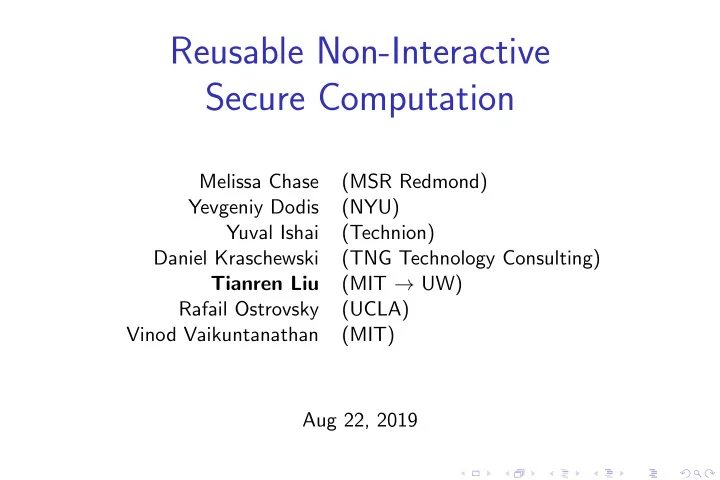
Reusable Non-Interactive Secure Computation Melissa Chase (MSR Redmond) Yevgeniy Dodis (NYU) Yuval Ishai (Technion) Daniel Kraschewski (TNG Technology Consulting) Tianren Liu (MIT UW) Rafail Ostrovsky (UCLA) Vinod Vaikuntanathan
Non-Interactive Secure Computation (NISC)
R
x
S
y Goal: receiver gets f (x,y) for a public function f .
Non-Interactive Secure Computation (NISC)
R
x
S
y Goal: receiver gets f (x,y) for a public function f .
Non-Interactive Secure Computation (NISC)
R
x
S
y Goal: receiver gets f (x,y) for a public function f .
Non-Interactive Secure Computation (NISC)
R
x
S
y f (x,y) Goal: receiver gets f (x,y) for a public function f .
Non-Interactive Secure Computation (NISC)
E.g. FHE = ⇒ Semi-honest NISC
R
x
S
y f (x,y) Goal: receiver gets f (x,y) for a public function f .
Non-Interactive Secure Computation (NISC)
E.g. FHE = ⇒ Semi-honest NISC
R
x
S
y Enc( x ) f (x,y) Goal: receiver gets f (x,y) for a public function f .
Non-Interactive Secure Computation (NISC)
E.g. FHE = ⇒ Semi-honest NISC
R
x
S
y Enc( x ) Enc( f (x,y) ) f (x,y) Goal: receiver gets f (x,y) for a public function f .
Garbled Circuit + OT = ⇒ Semi-honest NISC [Kilian’88]
R
x
S
y
Garbled Circuit + OT = ⇒ Semi-honest NISC [Kilian’88]
R
x
S
y ˜ C and tags w1,0 w1,1 w2,0 w2,1 w3,0 w3,1 w4,0 w4,1 . . . wn,0 wn,1
Garbled Circuit + OT = ⇒ Semi-honest NISC [Kilian’88]
R
x
S
y ˜ C and tags w1,0 w1,1 w2,0 w2,1 w3,0 w3,1 w4,0 w4,1 . . . wn,0 wn,1 x = 1 1 . . . 1
Garbled Circuit + OT = ⇒ Semi-honest NISC [Kilian’88]
R
x
S
y ˜ C and tags w1,0 w1,1 w2,0 w2,1 w3,0 w3,1 w4,0 w4,1 . . . wn,0 wn,1 x = 1 1 . . . 1
Garbled Circuit + OT = ⇒ Semi-honest NISC [Kilian’88]
R
x
S
y ˜ C and tags w1,0 w1,1 w2,0 w2,1 w3,0 w3,1 w4,0 w4,1 . . . wn,0 wn,1 x = 1 1 . . . 1 ˜ C and (wi,xi)n
i=1 reveals f (x,y)
and nothing else computationally.
Garbled Circuit + OT = ⇒ Semi-honest NISC [Kilian’88]
R
x
S
y ˜ C and tags w1,0 w1,1 w2,0 w2,1 w3,0 w3,1 w4,0 w4,1 . . . wn,0 wn,1 x = 1 1 . . . 1 ˜ C and (wi,xi)n
i=1 reveals f (x,y)
and nothing else computationally. ˜ C
Garbled Circuit + OT = ⇒ Semi-honest NISC [Kilian’88]
R
x
S
y ˜ C and tags w1,0 w1,1 w2,0 w2,1 w3,0 w3,1 w4,0 w4,1 . . . wn,0 wn,1 x = 1 1 . . . 1 ˜ C and (wi,xi)n
i=1 reveals f (x,y)
and nothing else computationally. ˜ C OT wi,0,wi,1 xi wi,xi
NISC in OT-hybrid model
Advantages
◮ OT realization from various models/assumptions ◮ Efficiency ◮ Malicious Security [Ishai-Kushilevitz-Ostrovsky-Prabhakaran-Sahai’88]
◮ Information-theoretical NISC for NC0 in OT-hybrid. ◮ NISC in OT-hybrid using black-box PRG.
Disadvantages
◮ NOT reusable secure.
NISC in OT-hybrid model
Advantages
◮ OT realization from various models/assumptions ◮ Efficiency ◮ Malicious Security [Ishai-Kushilevitz-Ostrovsky-Prabhakaran-Sahai’88]
◮ Information-theoretical NISC for NC0 in OT-hybrid. ◮ NISC in OT-hybrid using black-box PRG.
Disadvantages
◮ NOT reusable secure.
NISC in OT-hybrid model
Advantages
◮ OT realization from various models/assumptions ◮ Efficiency ◮ Malicious Security [Ishai-Kushilevitz-Ostrovsky-Prabhakaran-Sahai’88]
◮ Information-theoretical NISC for NC0 in OT-hybrid. ◮ NISC in OT-hybrid using black-box PRG.
Disadvantages
◮ NOT reusable secure.
Reusable NISC
R
x
S
y
Reusable NISC
R
x
S
y “encryption” of my data Cx
Reusable NISC
R
x
S
y “encryption” of my data Cx msg
Reusable NISC
R
x
S
y “encryption” of my data Cx msg f (x,y)
Reusable NISC
R
x
S
y “encryption” of my data Cx msg f (x,y) Reusability: Safe for receiver to reuse first msg and randomness
Reusable NISC
R
x
S
y “encryption” of my data Cx msg f (x,y) Reusability: Safe for receiver to reuse first msg and randomness
S′
y′,y′′
Reusable NISC
R
x
S
y “encryption” of my data Cx msg f (x,y) Reusability: Safe for receiver to reuse first msg and randomness
S′
y′,y′′ msg′, msg′′
Reusable NISC
R
x
S
y “encryption” of my data Cx msg f (x,y) Reusability: Safe for receiver to reuse first msg and randomness
S′
y′,y′′ msg′, msg′′ f (x,y′) f (x,y′′)
Reusable NISC
R
x
S
y “encryption” of my data Cx msg f (x,y) Reusability: Safe for receiver to reuse first msg and randomness
S′
y′,y′′ msg′, msg′′ f (x,y′) f (x,y′′)
NISC in OT-hybrid model
R
x
S
y ˜ C and tags w1,0 w1,1 w2,0 w2,1 w3,0 w3,1 w4,0 w4,1 . . . wn,0 wn,1 x = 1 1 . . . 1 ˜ C
reusable
OT wi,0,wi,1 xi wi,xi
NISC in OT-hybrid model
R
x
S
y ˜ C and tags w1,0 mess w2,0 w2,1 w3,0 w3,1 w4,0 w4,1 . . . wn,0 wn,1 x = 1 1 . . . 1 ˜ C
reusable
OT wi,0,wi,1 xi wi,xi
NISC in OT-hybrid model
R
x
S
y ˜ C and tags w1,0 mess w2,0 w2,1 w3,0 w3,1 w4,0 w4,1 . . . wn,0 wn,1 x = 1 1 . . . 1 Replacing w1,1 changes ’s behaviour = ⇒ x[1] = 1 thus NO security against malicious sender. ˜ C
reusable
OT wi,0,wi,1 xi wi,xi
NISC in OT-hybrid model
R
x
S
y ˜ C and tags w1,0 mess w2,0 w2,1 w3,0 w3,1 w4,0 w4,1 . . . wn,0 wn,1 x = 1 1 . . . 1 ˜ C
reusable
OT wi,0,wi,1 xi wi,xi
NISC in OT-hybrid model + one-shot UC-security [IKOPS’11]
R
x
S
y ˜ C and tags w1,0 mess w2,0 w2,1 w3,0 w3,1 w4,0 w4,1 . . . wn,0 wn,1 let OT input be encoding ˜ x = 1 1 . . . 1 ˜ C
reusable
OT wi,0,wi,1 ˜ xi wi,˜
xi
NISC in OT-hybrid model + one-shot UC-security [IKOPS’11]
R
x
S
y ˜ C and tags w1,0 mess w2,0 w2,1 w3,0 w3,1 w4,0 w4,1 . . . wn,0 wn,1 let OT input be encoding ˜ x = 1 1 . . . 1 A few bits of ˜ x leaks no information about x. ˜ C
reusable
OT wi,0,wi,1 ˜ xi wi,˜
xi
NISC in OT-hybrid model + one-shot UC-security [IKOPS’11]
R
x
S
y ˜ C and tags w1,0 mess w2,0 w2,1 w3,0 w3,1 w4,0 w4,1 . . . wn,0 wn,1 let OT input be encoding ˜ x = 1 1 . . . 1 Repeat the attack to learn the whole encoding ˜ x thus NO reusable security against malicious sender. ˜ C
reusable
OT wi,0,wi,1 ˜ xi wi,˜
xi
Our Results
Impossible to patch the protocol against malicious adversaries in reusable settings, as we show...
Theorem 1
There is no information-theoretic reusable NISC in rOT-hybrid model.
Our Results
Impossible to patch the protocol against malicious adversaries in reusable settings, as we show...
Theorem 1
There is no information-theoretic reusable NISC in rOT-hybrid model. There is no reusable NISC for certain functionalities in rOT-hybrid model with black-box simulation, assuming OWF.
Our Results
Impossible to patch the protocol against malicious adversaries in reusable settings, as we show...
Theorem 1
There is no information-theoretic reusable NISC in rOT-hybrid model. There is no reusable NISC for certain functionalities in rOT-hybrid model with black-box simulation, assuming OWF. Expansive alternative: Semi-honest NISC + reusable NIZK = ⇒ reusable NISC.
Our Results (continue)
NEW primitive: Oblivious linear function evaluation (OLE) S R
x ∈ F a,b ∈ F
Our Results (continue)
NEW primitive: Oblivious linear function evaluation (OLE) S R
x ∈ F a,b ∈ F get ax +b ∈ F
Our Results (continue)
NEW primitive: Oblivious linear function evaluation (OLE) S R
x ∈ F a,b ∈ F get ax +b ∈ F
Theorem 2
An information-theoretical UC-secure reusable NISC protocol in rOLE-hybrid model.
Our Results (continue)
NEW primitive: Oblivious linear function evaluation (OLE) S R
x ∈ F a,b ∈ F get ax +b ∈ F
Theorem 2
An information-theoretical UC-secure reusable NISC protocol in rOLE-hybrid model.
Theorem 3
An UC-secure 2-msg reusable OLE protocol in the CRS setting, under Paillier assumption.
Our Results (continue)
NEW primitive: Oblivious linear function evaluation (OLE) S R
x ∈ F a,b ∈ F get ax +b ∈ F Degenerate into OT if |F| = 2.
Theorem 2
An information-theoretical UC-secure reusable NISC protocol in rOLE-hybrid model.
Theorem 3
An UC-secure 2-msg reusable OLE protocol in the CRS setting, under Paillier assumption.
Our Results (continue)
NEW primitive: Oblivious linear function evaluation (OLE) S R
x ∈ F a,b ∈ F get ax +b ∈ F Degenerate into OT if |F| = 2.
Theorem 2
An information-theoretical UC-secure reusable NISC protocol in rOLE-hybrid model.
Theorem 3
An UC-secure 2-msg reusable OLE protocol in the CRS setting, under Paillier assumption. Security loss ≈ 1
|F|
How to Lift One-shot Security to Reusability
R
x
S
y rOLE ai,bi ˜ xi ai ˜ xi +bi f (x,y)
How to Lift One-shot Security to Reusability
R
x
S
y rOLE ai,bi ˜ xi ai ˜ xi +bi f (x,y)
How to Lift One-shot Security to Reusability
R
x
S
/// y / rOLE ai,bi ˜ xi ai ˜ xi +bi f (x,y)
How to Lift One-shot Security to Reusability
R
x
S
/// y / rOLE ai,bi ˜ xi ai ˜ xi +bi f (x,y∗) ◮ UC-security: ∃ an efficient simulator S S (a1,b1,a2,b2,...) → y∗
How to Lift One-shot Security to Reusability
R
x
S
/// y / rOLE ai,bi ˜ xi ai ˜ xi +bi f (x,y∗) ◮ UC-security: ∃ an efficient simulator S S (a1,b1,a2,b2,...) → y∗ ◮ No Abort (optional): When abnormal behavior was detected,
- utput f (x,0)
How to Lift One-shot Security to Reusability
R
x
S
/// y / rOLE ai,bi ˜ xi ai ˜ xi +bi f (x,y∗) ◮ UC-security: ∃ an efficient simulator S S (a1,b1,a2,b2,...) → y∗ ◮ No Abort (optional): When abnormal behavior was detected,
- utput f (x,0)
◮ Difficulty: distribution y∗ = ⇒ f (x,y∗) has entropy in ideal world = ⇒ leak information of receiver’s randomness in real world
How to Lift One-shot Security to Reusability
R
x
S
/// y / rOLE ai,bi ˜ xi ai ˜ xi +bi f (x,y∗) ◮ UC-security: ∃ an efficient simulator S S (a1,b1,a2,b2,...) → y∗ ◮ No Abort (optional): When abnormal behavior was detected,
- utput f (x,0)
◮ Difficulty: distribution y∗ = ⇒ f (x,y∗) has entropy in ideal world = ⇒ leak information of receiver’s randomness in real world
How to Lift One-shot Security to Reusability
R
x
S
/// y / rOLE ai,bi ˜ xi ai ˜ xi +bi f (x,y∗) ◮ UC-security: ∃ an efficient simulator S S (a1,b1,a2,b2,...) → y∗ ◮ No Abort (optional): When abnormal behavior was detected,
- utput f (x,0)
◮ Difficulty: distribution y∗ = ⇒ f (x,y∗) has entropy in ideal world = ⇒ leak information of receiver’s randomness in real world
How to Lift One-shot Security to Reusability
R
x
S
/// y / rOLE ai,bi ˜ xi ai ˜ xi +bi f (x,y∗) ◮ UC-security: ∃ an efficient simulator S S (a1,b1,a2,b2,...) → y∗ ◮ No Abort (optional): When abnormal behavior was detected,
- utput f (x,0)
◮ Difficulty: distribution y∗ = ⇒ f (x,y∗) has entropy in ideal world = ⇒ leak information of receiver’s randomness in real world ◮ “Strong” UC-security = ⇒ Reusability The simulator is deterministic
Overview: rNISC in rOLE-hybrid model
R
x ∈ Fn
S
y ∈ Fn ◮ Assume f is an arithmetic NC1 circuit or an arithmetic branching program over F ◮ [IK’02,AIK’14] encode y → (A,b) s.t. Ax +b reveals f (x,y) and nothing else ◮ Against malicious sender: detect if (A,b) is honestly generated, i.e. satisfies some simple arithmetic constraints Certified rOLE →
- Ax +b,
if (A,b) satisfies constraints ⊥,
- therwise
Overview: rNISC in rOLE-hybrid model
R
x ∈ Fn
S
y ∈ Fn ◮ Assume f is an arithmetic NC1 circuit or an arithmetic branching program over F ◮ [IK’02,AIK’14] encode y → (A,b) s.t. Ax +b reveals f (x,y) and nothing else ◮ Against malicious sender: detect if (A,b) is honestly generated, i.e. satisfies some simple arithmetic constraints Certified rOLE →
- Ax +b,
if (A,b) satisfies constraints ⊥,
- therwise
Overview: rNISC in rOLE-hybrid model
R
x ∈ Fn
S
y ∈ Fn rOLE A,b x Ax +b ◮ Assume f is an arithmetic NC1 circuit or an arithmetic branching program over F ◮ [IK’02,AIK’14] encode y → (A,b) s.t. Ax +b reveals f (x,y) and nothing else ◮ Against malicious sender: detect if (A,b) is honestly generated, i.e. satisfies some simple arithmetic constraints Certified rOLE →
- Ax +b,
if (A,b) satisfies constraints ⊥,
- therwise
Overview: rNISC in rOLE-hybrid model
R
x ∈ Fn
S
y ∈ Fn rOLE A,b x Ax +b f (x,y) ◮ Assume f is an arithmetic NC1 circuit or an arithmetic branching program over F ◮ [IK’02,AIK’14] encode y → (A,b) s.t. Ax +b reveals f (x,y) and nothing else ◮ Against malicious sender: detect if (A,b) is honestly generated, i.e. satisfies some simple arithmetic constraints Certified rOLE →
- Ax +b,
if (A,b) satisfies constraints ⊥,
- therwise
Overview: rNISC in rOLE-hybrid model
R
x ∈ Fn
S
y ∈ Fn rOLE A,b x Ax +b f (x,y) ◮ Assume f is an arithmetic NC1 circuit or an arithmetic branching program over F ◮ [IK’02,AIK’14] encode y → (A,b) s.t. Ax +b reveals f (x,y) and nothing else ◮ Against malicious sender: detect if (A,b) is honestly generated, i.e. satisfies some simple arithmetic constraints Certified rOLE →
- Ax +b,
if (A,b) satisfies constraints ⊥,
- therwise
Overview: rNISC in rOLE-hybrid model
R
x ∈ Fn
S
y ∈ Fn
Certified
rOLE A,b x
- Ax +b
⊥ f (x,y) ◮ Assume f is an arithmetic NC1 circuit or an arithmetic branching program over F ◮ [IK’02,AIK’14] encode y → (A,b) s.t. Ax +b reveals f (x,y) and nothing else ◮ Against malicious sender: detect if (A,b) is honestly generated, i.e. satisfies some simple arithmetic constraints Certified rOLE →
- Ax +b,
if (A,b) satisfies constraints ⊥,
- therwise
Overview: rNISC in rOLE-hybrid model
R
x ∈ Fn
S
y ∈ Fn
Certified
rOLE A,b x
- Ax +b
⊥ f (x,y) ◮ Assume f is an arithmetic NC1 circuit or an arithmetic branching program over F ◮ [IK’02,AIK’14] encode y → (A,b) s.t. Ax +b reveals f (x,y) and nothing else ◮ Against malicious sender: detect if (A,b) is honestly generated, i.e. satisfies some simple arithmetic constraints Certified rOLE →
- Ax +b,
if (A,b) satisfies constraints ⊥,
- therwise
Certified rOLE
R S
Certified rOLE
R S
rOLE a1,b1 x1 a1x1 +b1 rOLE a2,b2 x2 a2x2 +b2 rOLE a3,b3 x3 a3x3 +b3 . . .
Certified rOLE
R S
rOLE a1,b1 x1 a1x1 +b1 rOLE a2,b2 x2 a2x2 +b2 rOLE a3,b3 x3 a3x3 +b3 . . . Certified rOLE
Certified rOLE
R S
rOLE a1,b1 x1 a1x1 +b1 rOLE a2,b2 x2 a2x2 +b2 rOLE a3,b3 x3 a3x3 +b3 . . . Certified rOLE ◮ Sender can prove (a1,b1,a2,b2,...) satisfies arithmetic constraints
Certified rOLE
R S
rOLE a1,b1 x1 a1x1 +b1 rOLE a2,b2 x2 a2x2 +b2 rOLE a3,b3 x3 a3x3 +b3 . . . Certified rOLE ◮ Sender can prove (a1,b1,a2,b2,...) satisfies arithmetic constraints ◮ Side product: reusable DV-NIZK in rOLE-hybrid model.
Certified rOLE
R S
rOLE a1,b1 x1 a1x1 +b1 rOLE a2,b2 x2 a2x2 +b2 rOLE a3,b3 x3 a3x3 +b3 . . . Certified rOLE ◮ Sender can prove (a1,b1,a2,b2,...) satisfies arithmetic constraints ◮ Side product: reusable DV-NIZK in rOLE-hybrid model.
Certified rOLE
R S
rOLE a1,b1 x1 a1x1 +b1 rOLE a2,b2 x2 a2x2 +b2 rOLE a3,b3 x3 a3x3 +b3 . . . Certified rOLE ◮ Sender can prove (a1,b1,a2,b2,...) satisfies arithmetic constraints ai = aj for some (i,j)
for general constraints → see eprint
◮ Side product: reusable DV-NIZK in rOLE-hybrid model.
Certified rOLE
R S
. . . Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + (aˆ ˆ xi +b +r′)
Certified rOLE
R
w ← F
S
rOLE w . . . Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + (aˆ ˆ xi +b +r′)
Certified rOLE
R
w ← F
S
r ← F rOLE w a,r aw +r . . . Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + (aˆ ˆ xi +b +r′)
Certified rOLE
R
w ← F
S
r ← F rOLE w a,r aw +r . . . Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + (aˆ ˆ xi +b +r′) Commitment(a)
Certified rOLE
R
w ← F
S
r ← F rOLE w a,r aw +r . . . Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + (aˆ ˆ xi +b +r′) Target Commitment(a)
Certified rOLE
R
w ← F ˆ xi ← F
S
r ← F rOLE w a,r aw +r rOLE ˆ xi rOLE ˆ ˆ xi = xi −w ˆ xi . . . Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + (aˆ ˆ xi +b +r′) Target Commitment(a)
Certified rOLE
R
w ← F ˆ xi ← F
S
r ← F r′ ← F rOLE w a,r aw +r rOLE ˆ xi r,r′ r ˆ xi +r′ rOLE ˆ ˆ xi = xi −w ˆ xi a,b +r′ aˆ ˆ xi +b +r′ . . . Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + (aˆ ˆ xi +b +r′) Target Commitment(a)
Certified rOLE
R
w ← F ˆ xi ← F
S
r ← F r′ ← F rOLE w a,r aw +r rOLE ˆ xi r,r′ r ˆ xi +r′ rOLE ˆ ˆ xi = xi −w ˆ xi a,b +r′ aˆ ˆ xi +b +r′ . . . Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + (aˆ ˆ xi +b +r′) Target Commitment(a) rOLE outputs
Certified rOLE
R
w ← F ˆ xi ← F
S
r ← F r′ ← F rOLE w a,r aw +r rOLE ˆ xi r,r′ r ˆ xi +r′ rOLE ˆ ˆ xi = xi −w ˆ xi a,b +r′ aˆ ˆ xi +b +r′ . . . Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + (aˆ ˆ xi +b +r′) Target Commitment(a) rOLE outputs
Certified rOLE
R
w, ˆ xi ← F
S
r,r′ ← F rOLE w a,r rOLE ˆ xi r,r′ rOLE ˆ ˆ xi = xi −w ˆ xi a,b +r′ Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + e(aˆ ˆ xi +b +r′) Target Commitment(a) rOLE outputs
Certified rOLE
R
w, ˆ xi ← F
S
r,r′ ← F rOLE w a,r rOLE ˆ xi r,r′ rOLE ˆ ˆ xi = xi −w ˆ xi a,b +r′ Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + e(aˆ ˆ xi +b +r′) Target Commitment(a) rOLE outputs ◮ Correctness: Above equation.
Certified rOLE
R
w, ˆ xi ← F
S
r,r′ ← F rOLE w a,r rOLE ˆ xi r,r′ rOLE ˆ ˆ xi = xi −w ˆ xi a,b +r′ Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + e(aˆ ˆ xi +b +r′) Target Commitment(a) rOLE outputs ◮ Correctness: Above equation. ◮ UC-secure against Receiver: xi := w ˆ xi + ˆ ˆ xi.
Certified rOLE
R
w, ˆ xi ← F
S
r,r′ ← F rOLE w a,r rOLE ˆ xi r,r′ rOLE ˆ ˆ xi = xi −w ˆ xi a,b +r′ Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + e(aˆ ˆ xi +b +r′) Target Commitment(a) rOLE outputs ◮ Correctness: Above equation. ◮ UC-secure against Receiver: xi := w ˆ xi + ˆ ˆ xi. ◮ “Strong” UC-secure against Sender:
Certified rOLE
R
w, ˆ xi ← F
S
r,r′ ← F rOLE w a,r rOLE ˆ xi r,r′ rOLE ˆ ˆ xi = xi −w ˆ xi a,b +r′ Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + e(aˆ ˆ xi +b +r′) Target Commitment(a) rOLE outputs ◮ Correctness: Above equation. ◮ UC-secure against Receiver: xi := w ˆ xi + ˆ ˆ xi. ◮ “Strong” UC-secure against Sender:
Certified rOLE
R
w, ˆ xi ← F
S
r,r′ ← F rOLE w a,r rOLE ˆ xi r,r′ rOLE ˆ ˆ xi = xi −w ˆ xi a,b +r′ Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + e(aˆ ˆ xi +b +r′) Target Commitment(a) rOLE outputs ◮ Correctness: Above equation. ◮ UC-secure against Receiver: xi := w ˆ xi + ˆ ˆ xi. ◮ “Strong” UC-secure against Sender: Deviate = ⇒ random output
Certified rOLE
R
w, ˆ xi ← F
S
r,r′ ← F rOLE w a,r rOLE ˆ xi r,r′ rOLE ˆ ˆ xi = xi −w ˆ xi a,b +r′ Certified rOLE axi +b = (aw +r)· ˆ xi − (r ˆ xi +r′) + e(aˆ ˆ xi +b +r′) Target Commitment(a) rOLE outputs ◮ Correctness: Above equation. ◮ UC-secure against Receiver: xi := w ˆ xi + ˆ ˆ xi. ◮ “Strong” not yet UC-secure against Sender: Deviate = ⇒ random output
Our Results
NEW primitive: Oblivious linear function evaluation (OLE) S R
x ∈ F a,b ∈ F get ax +b ∈ F
Theorem 2
An information-theoretical UC-secure reusable NISC protocol in rOLE-hybrid model.
Theorem 3
An UC-secure 2-msg reusable OLE protocol in the CRS setting, under Paillier assumption.
Our Results
NEW primitive: Oblivious linear function evaluation (OLE) S R
x ∈ F a,b ∈ F get ax +b ∈ F
Theorem 2
An information-theoretical UC-secure reusable NISC protocol in rOLE-hybrid model.
Theorem 3
An UC-secure 2-msg reusable OLE protocol in the CRS setting, under Paillier assumption.
rOLE from Paillier
Dual-mode (similar to OT from [PVW’08]) Mode I
S R
x a,b crs ← D1 Mode II
S R
x a,b crs ← D2
rOLE from Paillier
Dual-mode (similar to OT from [PVW’08]) Mode I
S R
x a,b crs ← D1 Enc( x ) Mode II
S R
x a,b crs ← D2
rOLE from Paillier
Dual-mode (similar to OT from [PVW’08]) Mode I
S R
x a,b crs ← D1 Enc( x ) Enc(a−r ) Enc( b +rx) Mode II
S R
x a,b crs ← D2
rOLE from Paillier
Dual-mode (similar to OT from [PVW’08]) Mode I
S R
x a,b crs ← D1 Enc( x ) Enc(a−r ) Enc( b +rx) Efficient simulator against unbounded malicious receiver Mode II
S R
x a,b crs ← D2
rOLE from Paillier
Dual-mode (similar to OT from [PVW’08]) Mode I
S R
x a,b crs ← D1 Enc( x ) Enc(a−r ) Enc( b +rx) Efficient simulator against unbounded malicious receiver Mode II
S R
x a,b crs ← D2 Enc( 0 )
rOLE from Paillier
Dual-mode (similar to OT from [PVW’08]) Mode I
S R
x a,b crs ← D1 Enc( x ) Enc(a−r ) Enc( b +rx) Efficient simulator against unbounded malicious receiver Mode II
S R
x a,b crs ← D2 Enc( 0 ) Enc( a ) Enc( b )
rOLE from Paillier
Dual-mode (similar to OT from [PVW’08]) Mode I
S R
x a,b crs ← D1 Enc( x ) Enc(a−r ) Enc( b +rx) Efficient simulator against unbounded malicious receiver Mode II
S R
x a,b crs ← D2 Enc( 0 ) Enc( a ) Enc( b ) Efficient simulator against unbounded malicious sender
rOLE from Paillier
Dual-mode (similar to OT from [PVW’08]) D1 is indistinguishable from D2 Mode I
S R
x a,b crs ← D1 Enc( x ) Enc(a−r ) Enc( b +rx) Efficient simulator against unbounded malicious receiver Mode II
S R
x a,b crs ← D2 Enc( 0 ) Enc( a ) Enc( b ) Efficient simulator against unbounded malicious sender
Paillier Encryption Scheme
KeyGen public key, trapdoor
Paillier Encryption Scheme
KeyGen public key, trapdoor x Encr( x ) x Encrypt Decrypt randomness r trapdoor
Paillier Encryption Scheme
KeyGen public key, trapdoor x Encr( x ) x Encrypt Decrypt randomness r trapdoor Enc0( x ) x Decrypt
Paillier Encryption Scheme
KeyGen public key, trapdoor x Encr( x ) x Encrypt Decrypt randomness r trapdoor Enc0( x ) x Decrypt Encr( x ) · Encs( y ) = Encr+s( x +y )
rOLE from Paillier
S R
x a,b
rOLE from Paillier
S R
x a,b CRS (Mode I) h = Enc0( 1 ) w = Encα( 0 ) W0 = Encβ( 1 )
rOLE from Paillier
S R
x a,b sample sk CRS (Mode I) h = Enc0( 1 ) w = Encα( 0 ) W0 = Encβ( 1 ) W1 = wskW x
0 = Encxβ+α·sk( x )
rOLE from Paillier
S R
x a,b sample sk sample r CRS (Mode I) h = Enc0( 1 ) w = Encα( 0 ) W0 = Encβ( 1 ) W1 = wskW x
0 = Encxβ+α·sk( x )
v = wr = Encrα( 0 ) V0 = haW −r = Enc−rβ( a−r ) V1 = hbW r
1 = Encrxβ+rα·sk( b +rx )
rOLE from Paillier
S R
x a,b sample sk sample r CRS (Mode I) h = Enc0( 1 ) w = Encα( 0 ) W0 = Encβ( 1 ) W1 = wskW x
0 = Encxβ+α·sk( x )
v = wr = Encrα( 0 ) V0 = haW −r = Enc−rβ( a−r ) V1 = hbW r
1 = Encrxβ+rα·sk( b +rx )
vskV x
0 V1 = Enc0( ax +b )
rOLE from Paillier
S R
x a,b sample sk sample r CRS (Mode II) h = Enc0( 1 ) w = Encα( 0 ) W0 = Encβ( 0 ) W1 = wskW x
0 = Encxβ+α·sk( x )
v = wr = Encrα( 0 ) V0 = haW −r = Enc−rβ( a−r ) V1 = hbW r
1 = Encrxβ+rα·sk( b +rx )
vskV x
0 V1 = Enc0( ax +b )
rOLE from Paillier
S R
x a,b sample sk sample r CRS (Mode II) h = Enc0( 1 ) w = Encα( 0 ) W0 = Encβ( 0 ) W1 = wskW x
0 = Encxβ+α·sk( 0 )
v = wr = Encrα( 0 ) V0 = haW −r = Enc−rβ( a−r ) V1 = hbW r
1 = Encrxβ+rα·sk( b +rx )
vskV x
0 V1 = Enc0( ax +b )
rOLE from Paillier
S R
x a,b sample sk sample r CRS (Mode II) h = Enc0( 1 ) w = Encα( 0 ) W0 = Encβ( 0 ) W1 = wskW x
0 = Encxβ+α·sk( 0 )
v = wr = Encrα( 0 ) V0 = haW −r = Enc−rβ( a ) V1 = hbW r
1 = Encrxβ+rα·sk(
b ) vskV x
0 V1 = Enc0( ax +b )
rOLE from Paillier
S R
x a,b sample sk sample r CRS (Mode II) h = Enc0( 1 ) w = Encα( 0 ) W0 = Encβ( 0 ) W1 = wskW x
0 = Encxβ+α·sk( 0 )
v = wr = Encrα( 0 ) V0 = haW −r = Enc−rβ( a ) V1 = hbW r
1 = Encrxβ+rα·sk(
b ) vskV x
0 V1 = Enc0( ax +b )
“Strong” UC-security requires a machenism to detect malicious sender
Our Results
◮ (!∃ IT rNISC/rOT) There is no information-theoretical reusable NISC protocol in rOT-hybrid model. ◮ (IT rNISC/rOLE for arithmetic NC1) Information-theoretical UC-secure reusable NISC protocol for any arithmetic NC1 circuit
- r arithmetic branching program in rOLE-hybrid model.