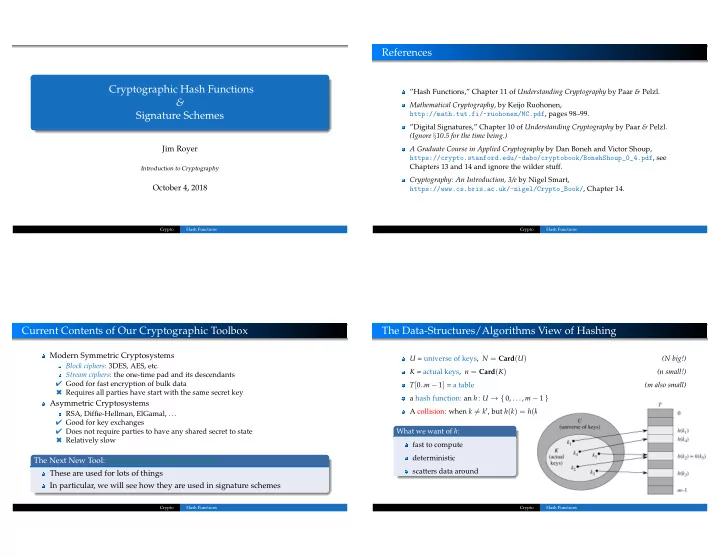
Cryptographic Hash Functions & Signature Schemes
Jim Royer
Introduction to Cryptography
October 4, 2018
Crypto Hash Functions
References
”Hash Functions,” Chapter 11 of Understanding Cryptography by Paar & Pelzl. Mathematical Cryptography, by Keijo Ruohonen, http://math.tut.fi/~ruohonen/MC.pdf, pages 98–99. ”Digital Signatures,” Chapter 10 of Understanding Cryptography by Paar & Pelzl. (Ignore §10.5 for the time being.) A Graduate Course in Applied Cryptography by Dan Boneh and Victor Shoup, https://crypto.stanford.edu/~dabo/cryptobook/BonehShoup_0_4.pdf, see Chapters 13 and 14 and ignore the wilder stuff. Cryptography: An Introduction, 3/e by Nigel Smart, https://www.cs.bris.ac.uk/~nigel/Crypto_Book/, Chapter 14.
Crypto Hash Functions
Current Contents of Our Cryptographic Toolbox
Modern Symmetric Cryptosystems
Block ciphers: 3DES, AES, etc. Stream ciphers: the one-time pad and its descendants ✔ Good for fast encryption of bulk data ✖ Requires all parties have start with the same secret key
Asymmetric Cryptosystems
RSA, Diffie-Hellman, ElGamal, ... ✔ Good for key exchanges ✔ Does not require parties to have any shared secret to state ✖ Relatively slow
The Next New Tool: Cryptographic Hash Functions These are used for lots of things In particular, we will see how they are used in signature schemes
Crypto Hash Functions
The Data-Structures/Algorithms View of Hashing
U = universe of keys, N = Card(U) (N big!) K = actual keys, n = Card(K) (n small!) T[0..m − 1] = a table (m also small) a hash function: an h: U → { 0, . . . , m − 1 } A collision: when k = k′, but h(k) = h(k′). What we want of h: fast to compute deterministic scatters data around
Crypto Hash Functions