1
Quantum Quantum Crypto ?? Crypto ?? Cani Cani
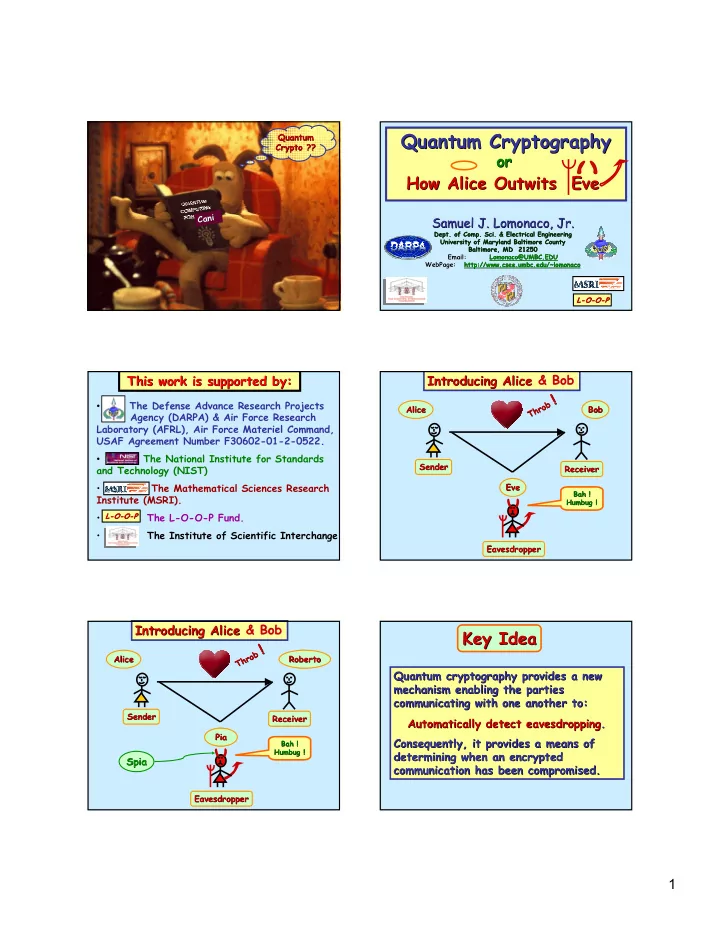
Quantum Cryptography Quantum Cryptography
Samuel J. Lomonaco, Jr. Samuel J. Lomonaco, Jr.
- Dept. of Comp.
- Dept. of Comp. Sci
- Sci. & Electrical Engineering
. & Electrical Engineering University of Maryland Baltimore County University of Maryland Baltimore County Baltimore, MD 21250 Baltimore, MD 21250 Email: Email: Lomonaco@UMBC.EDU Lomonaco@UMBC.EDU WebPage WebPage: : http:// http://www.csee.umbc.edu/~lomonaco www.csee.umbc.edu/~lomonaco
How Alice Outwits Eve How Alice Outwits Eve
- r
- r
L L-
- O
O-
- O
O-
- P
P
- The Defense Advance Research Projects
Agency (DARPA) & Air Force Research Laboratory (AFRL), Air Force Materiel Command, USAF Agreement Number F30602-01-2-0522.
- The National Institute for Standards
and Technology (NIST)
- The Mathematical Sciences Research
Institute (MSRI).
- The L-O-O-P Fund.
- The Institute of Scientific Interchange
L L-
- O
O-
- O
O-
- P
P
This work is supported by: This work is supported by: Introducing Alice Introducing Alice & Bob & Bob
Sender Sender Receiver Receiver Eavesdropper Eavesdropper Alice Alice Bob Bob Eve Eve
Bah ! Bah ! Humbug ! Humbug !
Throb Throb !
!
Introducing Alice Introducing Alice & Bob & Bob
Sender Sender Receiver Receiver Eavesdropper Eavesdropper Alice Alice Bob Bob Eve Eve
Bah ! Bah ! Humbug ! Humbug !
Throb Throb !
!
Roberto Roberto Pia Pia
Spia Spia
Quantum cryptography provides a new Quantum cryptography provides a new mechanism enabling the parties mechanism enabling the parties communicating with one another to: communicating with one another to: Consequently, it provides a means of Consequently, it provides a means of determining when an encrypted determining when an encrypted communication has been compromised. communication has been compromised.
Key Idea Key Idea
Automatically detect eavesdropping Automatically detect eavesdropping. .