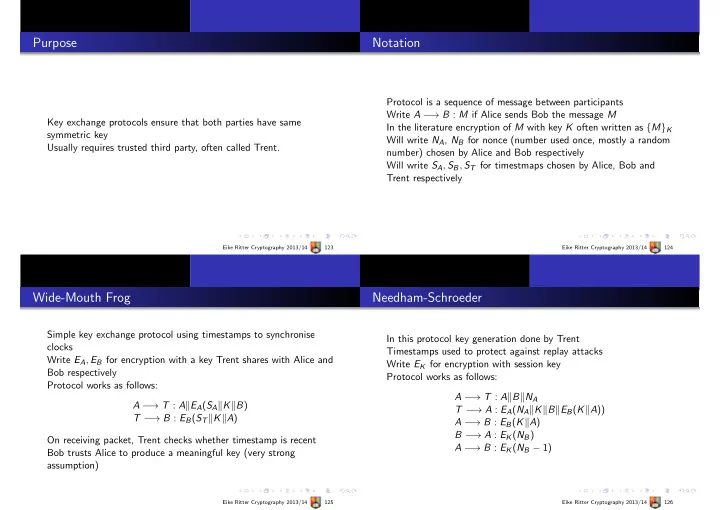
Purpose
Key exchange protocols ensure that both parties have same symmetric key Usually requires trusted third party, often called Trent.
Eike Ritter Cryptography 2013/14 123
Notation
Protocol is a sequence of message between participants Write A − → B : M if Alice sends Bob the message M In the literature encryption of M with key K often written as {M}K Will write NA, NB for nonce (number used once, mostly a random number) chosen by Alice and Bob respectively Will write SA, SB, ST for timestmaps chosen by Alice, Bob and Trent respectively
Eike Ritter Cryptography 2013/14 124
Wide-Mouth Frog
Simple key exchange protocol using timestamps to synchronise clocks Write EA, EB for encryption with a key Trent shares with Alice and Bob respectively Protocol works as follows: A − → T : AEA(SAKB) T − → B : EB(STKA) On receiving packet, Trent checks whether timestamp is recent Bob trusts Alice to produce a meaningful key (very strong assumption)
Eike Ritter Cryptography 2013/14 125
Needham-Schroeder
In this protocol key generation done by Trent Timestamps used to protect against replay attacks Write EK for encryption with session key Protocol works as follows: A − → T : ABNA T − → A : EA(NAKBEB(KA)) A − → B : EB(KA) B − → A : EK(NB) A − → B : EK(NB − 1)
Eike Ritter Cryptography 2013/14 126