Lecture 4 Page 1 CS 236 Online
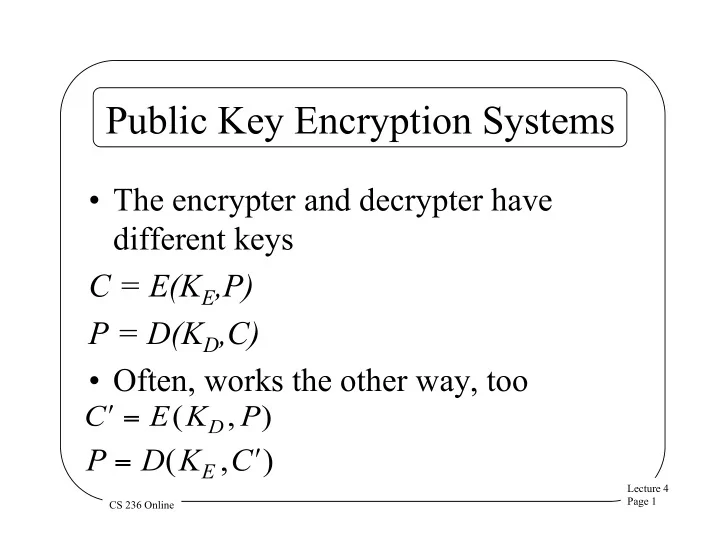
Public Key Encryption Systems
- The encrypter and decrypter have
different keys C = E(KE,P) P = D(KD,C)
- Often, works the other way, too
Public Key Encryption Systems The encrypter and decrypter have - - PowerPoint PPT Presentation
Public Key Encryption Systems The encrypter and decrypter have different keys C = E(K E ,P) P = D(K D ,C) Often, works the other way, too Lecture 4 Page 1 CS 236 Online History of Public Key Cryptography Invented by Diffie and
Lecture 4 Page 1 CS 236 Online
Lecture 4 Page 2 CS 236 Online
Lecture 4 Page 3 CS 236 Online
Lecture 4 Page 4 CS 236 Online
Lecture 4 Page 5 CS 236 Online
Lecture 4 Page 6 CS 236 Online
Lecture 4 Page 7 CS 236 Online
Lecture 4 Page 8 CS 236 Online
Lecture 4 Page 9 CS 236 Online
Lecture 4 Page 10 CS 236 Online
Lecture 4 Page 11 CS 236 Online
Lecture 4 Page 12 CS 236 Online
Lecture 4 Page 13 CS 236 Online
Lecture 4 Page 14 CS 236 Online
Lecture 4 Page 15 CS 236 Online
Lecture 4 Page 16 CS 236 Online
Lecture 4 Page 17 CS 236 Online
Lecture 4 Page 18 CS 236 Online
Lecture 4 Page 19 CS 236 Online
Lecture 4 Page 20 CS 236 Online
Lecture 4 Page 21 CS 236 Online
When in the Course
events it becomes necessary for one
Elas7pa 1o’gw0mega 30’sswp. 1f43’-s 4 32.doas3 Dsp5.a#l ^o,a 02 When in the Course
events it becomes necessary for one
Lecture 4 Page 22 CS 236 Online
Lecture 4 Page 23 CS 236 Online
When in the Course
events it becomes necessary for one
Elas7pa 1o’gw0mega 30’sswp. 1f43’-s 4 32.doas3 Dsp5.a#l ^o,a 02 When in the Course
events it becomes necessary for one
Lecture 4 Page 24 CS 236 Online