Security Proofs using the Game-based Methodology
David Pointcheval
Ecole normale sup´ erieure, CNRS & INRIAScuola Superiore di Catania Catania – Italy April 21st, 2009
David Pointcheval – 1/47 Cryptography Game-based Proofs Assumptions BLS Signature BF IB-Encryption ConclusionOutline
1Cryptography Introduction Provable Security
2Game-based Methodology Game-based Approach Transition Hops
3Assumptions
4Short Signatures Description of BLS Security Proof
5Identity-Based Encryption Definition Description of BF Security Proof
6Conclusion
David Pointcheval – 2/47 Cryptography Game-based Proofs Assumptions BLS Signature BF IB-Encryption ConclusionOutline
1Cryptography Introduction Provable Security
2Game-based Methodology Game-based Approach Transition Hops
3Assumptions
4Short Signatures Description of BLS Security Proof
5Identity-Based Encryption Definition Description of BF Security Proof
6Conclusion
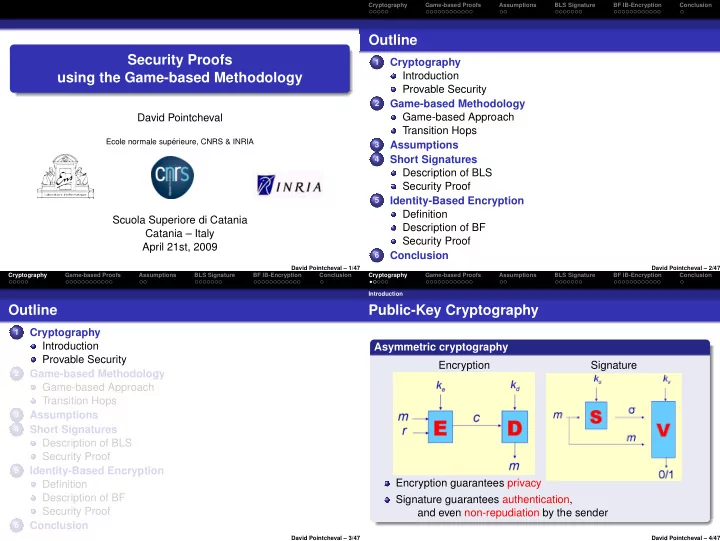
David Pointcheval – 3/47 Cryptography Game-based Proofs Assumptions BLS Signature BF IB-Encryption Conclusion IntroductionPublic-Key Cryptography
Asymmetric cryptography Encryption Signature Encryption guarantees privacy Signature guarantees authentication, and even non-repudiation by the sender
David Pointcheval – 4/47