SLIDE 1
CSci 5271 Introduction to Computer Security Web security, part 2
Stephen McCamant
University of Minnesota, Computer Science & Engineering
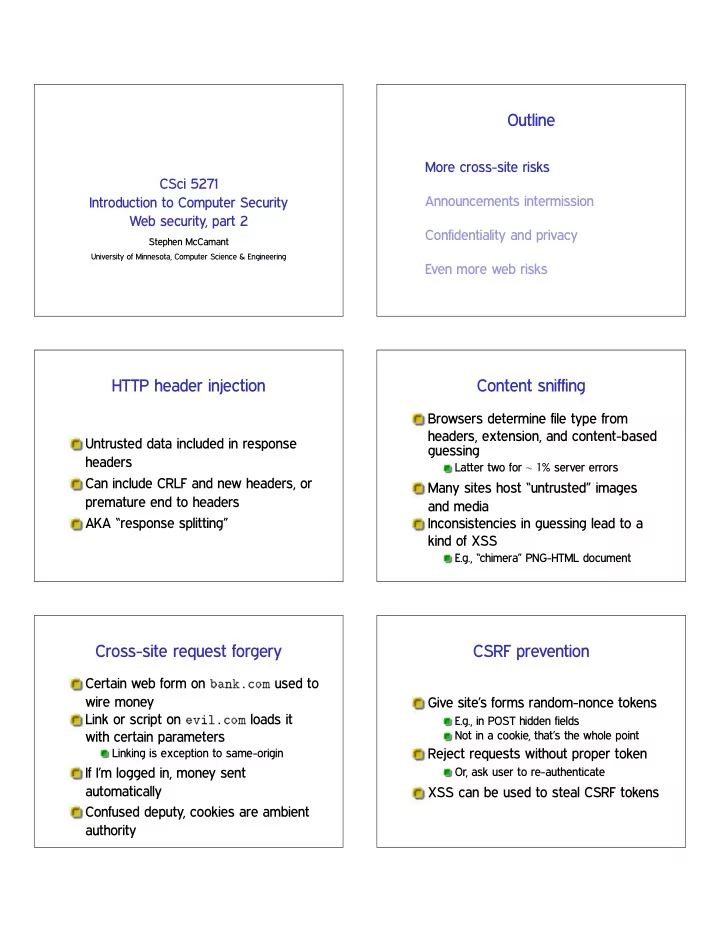
Outline More cross-site risks CSci 5271 Announcements intermission - - PDF document
Outline More cross-site risks CSci 5271 Announcements intermission Introduction to Computer Security Web security, part 2 Confidentiality and privacy Stephen McCamant University of Minnesota, Computer Science & Engineering Even more web
University of Minnesota, Computer Science & Engineering