10/25/19 1
Cognitive Radio Network Security
Yao Zheng
1
Outline
- A taxonomy of CR security threats
- Primary user emulation attacks
- Byzantine failures in distributed spectrum
sensing
- Security vulnerabilities in IEEE 802.22
2
Introduction
- Successful deployment of CR networks and the
realization of their benefits will depend on the placement of essential security mechanisms
- Emergence of the opportunistic spectrum sharing
(OSS) paradigm and cognitive radio technology raises new security implications that have not been studied previously
- Researchers have only recently started to examine
the security issues specific to CR devices and networks
3
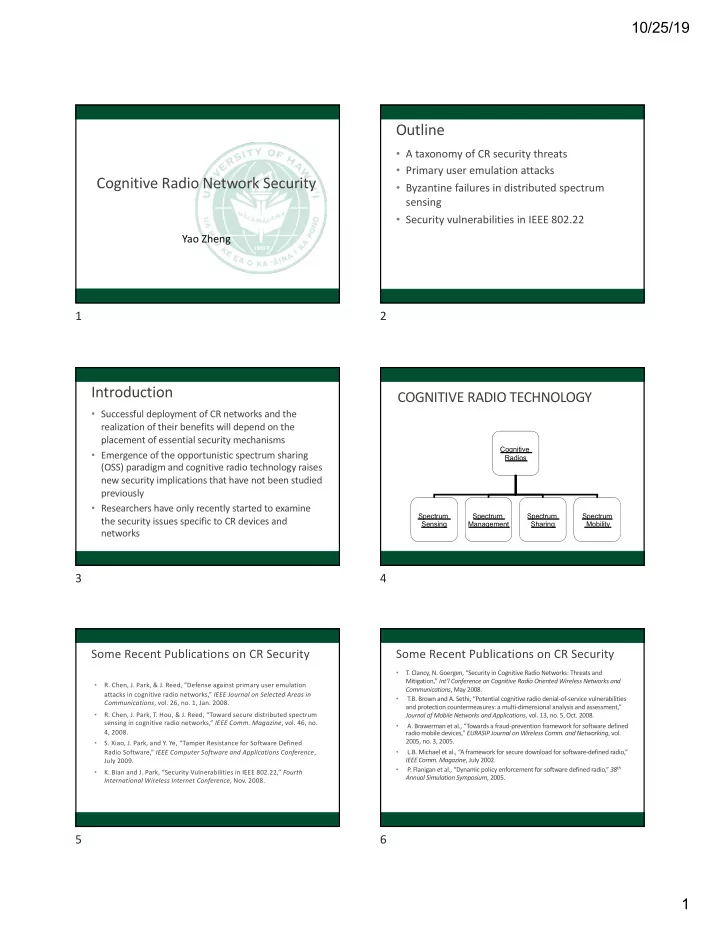
COGNITIVE RADIO TECHNOLOGY
Cognitive Radios Spectrum Sensing Spectrum Sharing Spectrum Mobility Spectrum Management
4 Some Recent Publications on CR Security
- R. Chen, J. Park, & J. Reed, “Defense against primary user emulation
attacks in cognitive radio networks,” IEEE Journal on Selected Areas in Communications, vol. 26, no. 1, Jan. 2008.
- R. Chen, J. Park, T. Hou, & J. Reed, “Toward secure distributed spectrum
sensing in cognitive radio networks,” IEEE Comm. Magazine, vol. 46, no. 4, 2008.
- S. Xiao, J. Park, and Y. Ye, “Tamper Resistance for Software Defined
Radio Software,” IEEE Computer Software and Applications Conference, July 2009.
- K. Bian and J. Park, “Security Vulnerabilities in IEEE 802.22,” Fourth
International Wireless Internet Conference, Nov. 2008.
5 Some Recent Publications on CR Security
- T. Clancy, N. Goergen, “Security in Cognitive Radio Networks: Threats and
Mitigation,” Int’l Conference on Cognitive Radio Oriented Wireless Networks and Communications, May 2008.
- T.B. Brown and A. Sethi, “Potential cognitive radio denial-of-service vulnerabilities
and protection countermeasures: a multi-dimensional analysis and assessment,” Journal of Mobile Networks and Applications, vol. 13, no. 5, Oct. 2008.
- A. Brawerman et al., “Towards a fraud-prevention framework for software defined
radio mobile devices,” EURASIP Journal on Wireless Comm. and Networking, vol. 2005, no. 3, 2005.
- L.B. Michael et al., “A framework for secure download for software-defined radio,”
IEEE Comm. Magazine, July 2002.
- P
. Flanigan et al., “Dynamic policy enforcement for software defined radio,” 38th Annual Simulation Symposium, 2005.