Lecture 5 - Tuesday, Sept 27 2010. Material and some slide content from:
- Software Architecture: Foundations, Theory, and Practice
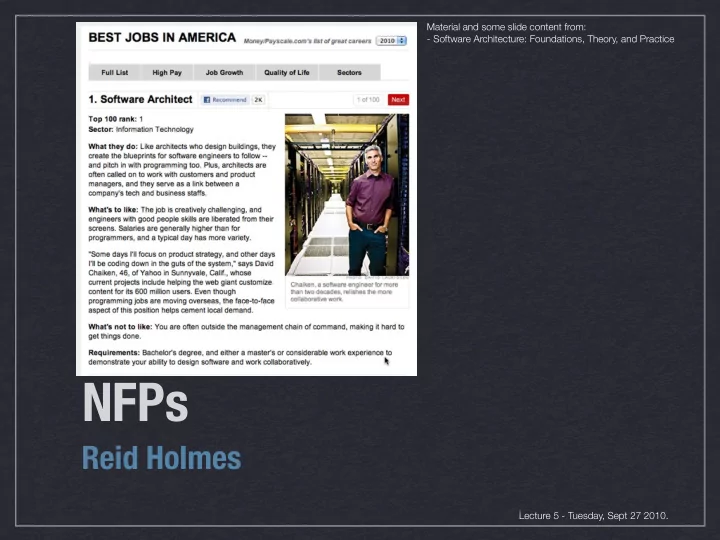
NFPs Reid Holmes Lecture 5 - Tuesday, Sept 27 2010. [TAILOR ET - - PowerPoint PPT Presentation
Material and some slide content from: - Software Architecture: Foundations, Theory, and Practice NFPs Reid Holmes Lecture 5 - Tuesday, Sept 27 2010. [TAILOR ET AL.] NFPs NFPs are constraints on the manner in which the system implements
Lecture 5 - Tuesday, Sept 27 2010. Material and some slide content from:
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
system implements and delivers its functionality.
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
ability to meet its performance requirements.
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
size of a system, its volume of constituent elements, their internal structure, and their interdependencies.
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
!"#$%&'()$* +$*,-'% +./.0$- 1$)2,-3% 4/)$-5.6$ 4/)$-78-,6$((% 9,**:/"6.)",/( 8-,6$((% &6;$<:#$- 4/")".#"=.)",/ >"?-.-'
+$*,-'% +./.0$- 1$)2,-3% 4/)$-5.6$ 4/)$-78-,6$((% 9,**:/"6.)",/( 8-,6$((% &6;$<:#$- 4/")".#"=.)",/ >"?-.-'
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
adapted to meet new size / scope requirements.
and environments (e.g., portability).
multiple platforms while retaining their functional and non-functional properties.
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
requirements and environments.
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
within its design limits without failure over time.
a particular instant in time.
adequately to unanticipated runtime conditions.
gracefully to failures at runtime.
component-connector mismatches.
to threats.
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
preserve its integrity, availability, and confidentiality if its resources.”
unauthorized parties from accessing the information or perhaps even being aware of the existence of the information. I.e., secrecy.
parties can manipulate the information and do so only in authorized ways.
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
[TAILOR ET AL.]
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
resources, and whether the accessor has permissions.
investigated at an architectural level.
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
DB Component Interface Alice Read-write; always Bend Y Bob Read-write; Between 9-5 Fold N Charles No access Spindle N Dave No access Mutilate Y Eve Read-only; Always Non N
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
REID HOLMES - SE2: SOFTWARE DESIGN & ARCHITECTURE
agent assesses another agents will perform some specific action within a specific context.
behaviour based on their past behaviours.
about trust-related issues.