1
Memory forensics
(well, that’s what the title says)
Wietse Venema wietse@porcupine.org IBM T.J.Watson Research, USA
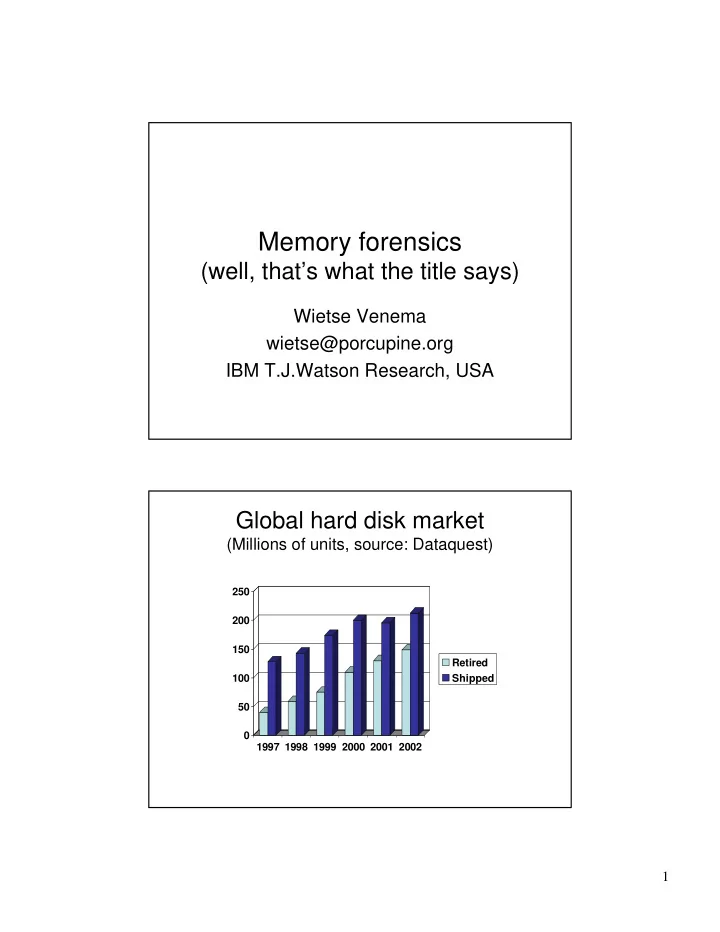
Global hard disk market
(Millions of units, source: Dataquest)
50 100 150 200 250 1997 1998 1999 2000 2001 2002 Retired Shipped
Memory forensics (well, thats what the title says) Wietse Venema - - PDF document
Memory forensics (well, thats what the title says) Wietse Venema wietse@porcupine.org IBM T.J.Watson Research, USA Global hard disk market (Millions of units, source: Dataquest) 250 200 150 Retired 100 Shipped 50 0 1997 1998 1999
50 100 150 200 250 1997 1998 1999 2000 2001 2002 Retired Shipped
IEEE Privacy & Security January/February 2003, http://www.computer.org/security/garfinkel.hmtl
Application File System Block Cache Disk Blocks Application Virtual Cache File System Disk Blocks
DOS, Win95/98/ME, BSD BSD, Linux, Solaris,WinNT/2K/XP
att.ps fish-audit.ps fish.ps fw-audit.ps handouts.html how2.ps index.html intro.ps nancy-cook.ps network-examples.ps networks.ps
5 10 15 20 5 time of day (hours) hit buffered absent