SLIDE 1 1
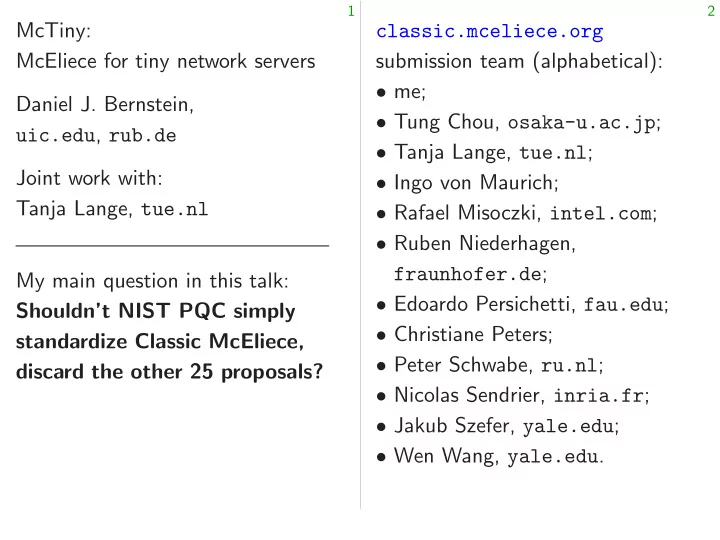
McTiny: McEliece for tiny network servers Daniel J. Bernstein, uic.edu, rub.de Joint work with: Tanja Lange, tue.nl My main question in this talk: Shouldn’t NIST PQC simply standardize Classic McEliece, discard the other 25 proposals?
2
classic.mceliece.org submission team (alphabetical):
- me;
- Tung Chou, osaka-u.ac.jp;
- Tanja Lange, tue.nl;
- Ingo von Maurich;
- Rafael Misoczki, intel.com;
- Ruben Niederhagen,
fraunhofer.de;
- Edoardo Persichetti, fau.edu;
- Christiane Peters;
- Peter Schwabe, ru.nl;
- Nicolas Sendrier, inria.fr;
- Jakub Szefer, yale.edu;
- Wen Wang, yale.edu.

SLIDE 2 1
McTiny: McEliece for tiny network servers
uic.edu, rub.de
Lange, tue.nl main question in this talk: Shouldn’t NIST PQC simply standardize Classic McEliece, rd the other 25 proposals?
2
classic.mceliece.org submission team (alphabetical):
- me;
- Tung Chou, osaka-u.ac.jp;
- Tanja Lange, tue.nl;
- Ingo von Maurich;
- Rafael Misoczki, intel.com;
- Ruben Niederhagen,
fraunhofer.de;
- Edoardo Persichetti, fau.edu;
- Christiane Peters;
- Peter Schwabe, ru.nl;
- Nicolas Sendrier, inria.fr;
- Jakub Szefer, yale.edu;
- Wen Wang, yale.edu.
History Fundamental 1962 Prange + many 1968 Berlek 1970–1971 1978 McEliece 1986 Niederreiter + many 2017: Classic NIST: “the to generate
Classic McEliec

SLIDE 3 1
tiny network servers Bernstein, tue.nl question in this talk: PQC simply Classic McEliece,
2
classic.mceliece.org submission team (alphabetical):
- me;
- Tung Chou, osaka-u.ac.jp;
- Tanja Lange, tue.nl;
- Ingo von Maurich;
- Rafael Misoczki, intel.com;
- Ruben Niederhagen,
fraunhofer.de;
- Edoardo Persichetti, fau.edu;
- Christiane Peters;
- Peter Schwabe, ru.nl;
- Nicolas Sendrier, inria.fr;
- Jakub Szefer, yale.edu;
- Wen Wang, yale.edu.
History Fundamental litera 1962 Prange (attack) + many more attack 1968 Berlekamp (deco 1970–1971 Goppa 1978 McEliece (cryptosystem). 1986 Niederreiter (dual) + many more optimizations. 2017: Classic McEliec NIST: “the submitters to generate parameter
Classic McEliece, round

SLIDE 4 1
servers talk: simply McEliece, roposals?
2
classic.mceliece.org submission team (alphabetical):
- me;
- Tung Chou, osaka-u.ac.jp;
- Tanja Lange, tue.nl;
- Ingo von Maurich;
- Rafael Misoczki, intel.com;
- Ruben Niederhagen,
fraunhofer.de;
- Edoardo Persichetti, fau.edu;
- Christiane Peters;
- Peter Schwabe, ru.nl;
- Nicolas Sendrier, inria.fr;
- Jakub Szefer, yale.edu;
- Wen Wang, yale.edu.
History Fundamental literature: 1962 Prange (attack) + many more attack papers. 1968 Berlekamp (decoder). 1970–1971 Goppa (codes). 1978 McEliece (cryptosystem). 1986 Niederreiter (dual) + many more optimizations. 2017: Classic McEliece, round NIST: “the submitters may wish to generate parameter sets fo
- ther security categories.” ⇒
Classic McEliece, round 2.

SLIDE 5 2
classic.mceliece.org submission team (alphabetical):
- me;
- Tung Chou, osaka-u.ac.jp;
- Tanja Lange, tue.nl;
- Ingo von Maurich;
- Rafael Misoczki, intel.com;
- Ruben Niederhagen,
fraunhofer.de;
- Edoardo Persichetti, fau.edu;
- Christiane Peters;
- Peter Schwabe, ru.nl;
- Nicolas Sendrier, inria.fr;
- Jakub Szefer, yale.edu;
- Wen Wang, yale.edu.
3
History Fundamental literature: 1962 Prange (attack) + many more attack papers. 1968 Berlekamp (decoder). 1970–1971 Goppa (codes). 1978 McEliece (cryptosystem). 1986 Niederreiter (dual) + many more optimizations. 2017: Classic McEliece, round 1. NIST: “the submitters may wish to generate parameter sets for
- ther security categories.” ⇒
Classic McEliece, round 2.

SLIDE 6 2
classic.mceliece.org submission team (alphabetical): ung Chou, osaka-u.ac.jp; anja Lange, tue.nl; von Maurich; Rafael Misoczki, intel.com; en Niederhagen, fraunhofer.de; Edoardo Persichetti, fau.edu; Christiane Peters; eter Schwabe, ru.nl; Nicolas Sendrier, inria.fr; Jakub Szefer, yale.edu; Wang, yale.edu.
3
History Fundamental literature: 1962 Prange (attack) + many more attack papers. 1968 Berlekamp (decoder). 1970–1971 Goppa (codes). 1978 McEliece (cryptosystem). 1986 Niederreiter (dual) + many more optimizations. 2017: Classic McEliece, round 1. NIST: “the submitters may wish to generate parameter sets for
- ther security categories.” ⇒
Classic McEliece, round 2. Encoding 1978 McEliece matrix A Normally

SLIDE 7 2
classic.mceliece.org (alphabetical):
tue.nl; rich; czki, intel.com; Niederhagen, fraunhofer.de; ersichetti, fau.edu; ters; e, ru.nl; Sendrier, inria.fr; yale.edu; yale.edu.
3
History Fundamental literature: 1962 Prange (attack) + many more attack papers. 1968 Berlekamp (decoder). 1970–1971 Goppa (codes). 1978 McEliece (cryptosystem). 1986 Niederreiter (dual) + many more optimizations. 2017: Classic McEliece, round 1. NIST: “the submitters may wish to generate parameter sets for
- ther security categories.” ⇒
Classic McEliece, round 2. Encoding and deco 1978 McEliece public matrix A over F2. Normally s → As is

SLIDE 8 2
etical):
intel.com; fau.edu; inria.fr; ;
3
History Fundamental literature: 1962 Prange (attack) + many more attack papers. 1968 Berlekamp (decoder). 1970–1971 Goppa (codes). 1978 McEliece (cryptosystem). 1986 Niederreiter (dual) + many more optimizations. 2017: Classic McEliece, round 1. NIST: “the submitters may wish to generate parameter sets for
- ther security categories.” ⇒
Classic McEliece, round 2. Encoding and decoding 1978 McEliece public key: matrix A over F2. Normally s → As is injective.

SLIDE 9 3
History Fundamental literature: 1962 Prange (attack) + many more attack papers. 1968 Berlekamp (decoder). 1970–1971 Goppa (codes). 1978 McEliece (cryptosystem). 1986 Niederreiter (dual) + many more optimizations. 2017: Classic McEliece, round 1. NIST: “the submitters may wish to generate parameter sets for
- ther security categories.” ⇒
Classic McEliece, round 2.
4
Encoding and decoding 1978 McEliece public key: matrix A over F2. Normally s → As is injective.

SLIDE 10 3
History Fundamental literature: 1962 Prange (attack) + many more attack papers. 1968 Berlekamp (decoder). 1970–1971 Goppa (codes). 1978 McEliece (cryptosystem). 1986 Niederreiter (dual) + many more optimizations. 2017: Classic McEliece, round 1. NIST: “the submitters may wish to generate parameter sets for
- ther security categories.” ⇒
Classic McEliece, round 2.
4
Encoding and decoding 1978 McEliece public key: matrix A over F2. Normally s → As is injective. Ciphertext: vector C = As + e. Uses secret “codeword” As, weight-w “error vector” e.

SLIDE 11 3
History Fundamental literature: 1962 Prange (attack) + many more attack papers. 1968 Berlekamp (decoder). 1970–1971 Goppa (codes). 1978 McEliece (cryptosystem). 1986 Niederreiter (dual) + many more optimizations. 2017: Classic McEliece, round 1. NIST: “the submitters may wish to generate parameter sets for
- ther security categories.” ⇒
Classic McEliece, round 2.
4
Encoding and decoding 1978 McEliece public key: matrix A over F2. Normally s → As is injective. Ciphertext: vector C = As + e. Uses secret “codeword” As, weight-w “error vector” e. 1978 parameters for 264 security goal: 1024 × 512 matrix, w = 50.

SLIDE 12 3
History Fundamental literature: 1962 Prange (attack) + many more attack papers. 1968 Berlekamp (decoder). 1970–1971 Goppa (codes). 1978 McEliece (cryptosystem). 1986 Niederreiter (dual) + many more optimizations. 2017: Classic McEliece, round 1. NIST: “the submitters may wish to generate parameter sets for
- ther security categories.” ⇒
Classic McEliece, round 2.
4
Encoding and decoding 1978 McEliece public key: matrix A over F2. Normally s → As is injective. Ciphertext: vector C = As + e. Uses secret “codeword” As, weight-w “error vector” e. 1978 parameters for 264 security goal: 1024 × 512 matrix, w = 50. Public key is secretly generated with “binary Goppa code” structure that allows efficient decoding: C → As; e.

SLIDE 13
3
ry undamental literature: Prange (attack) many more attack papers. Berlekamp (decoder). 1970–1971 Goppa (codes). McEliece (cryptosystem). Niederreiter (dual) many more optimizations. Classic McEliece, round 1. “the submitters may wish generate parameter sets for security categories.” ⇒ McEliece, round 2.
4
Encoding and decoding 1978 McEliece public key: matrix A over F2. Normally s → As is injective. Ciphertext: vector C = As + e. Uses secret “codeword” As, weight-w “error vector” e. 1978 parameters for 264 security goal: 1024 × 512 matrix, w = 50. Public key is secretly generated with “binary Goppa code” structure that allows efficient decoding: C → As; e. Binary Goppa Paramete w ∈ {2; 3 n ∈ {w lg

SLIDE 14 3
iterature: (attack) attack papers. (decoder). Goppa (codes). (cryptosystem). Niederreiter (dual)
McEliece, round 1. submitters may wish rameter sets for categories.” ⇒ e, round 2.
4
Encoding and decoding 1978 McEliece public key: matrix A over F2. Normally s → As is injective. Ciphertext: vector C = As + e. Uses secret “codeword” As, weight-w “error vector” e. 1978 parameters for 264 security goal: 1024 × 512 matrix, w = 50. Public key is secretly generated with “binary Goppa code” structure that allows efficient decoding: C → As; e. Binary Goppa codes Parameters: q ∈ { w ∈ {2; 3; : : : ; ⌊(q n ∈ {w lg q + 1; : :

SLIDE 15 3
ers. der). des). (cryptosystem).
round 1. y wish sets for ⇒
4
Encoding and decoding 1978 McEliece public key: matrix A over F2. Normally s → As is injective. Ciphertext: vector C = As + e. Uses secret “codeword” As, weight-w “error vector” e. 1978 parameters for 264 security goal: 1024 × 512 matrix, w = 50. Public key is secretly generated with “binary Goppa code” structure that allows efficient decoding: C → As; e. Binary Goppa codes Parameters: q ∈ {8; 16; 32; : w ∈ {2; 3; : : : ; ⌊(q − 1)= lg q n ∈ {w lg q + 1; : : : ; q − 1; q

SLIDE 16
4
Encoding and decoding 1978 McEliece public key: matrix A over F2. Normally s → As is injective. Ciphertext: vector C = As + e. Uses secret “codeword” As, weight-w “error vector” e. 1978 parameters for 264 security goal: 1024 × 512 matrix, w = 50. Public key is secretly generated with “binary Goppa code” structure that allows efficient decoding: C → As; e.
5
Binary Goppa codes Parameters: q ∈ {8; 16; 32; : : :}; w ∈ {2; 3; : : : ; ⌊(q − 1)= lg q⌋}; n ∈ {w lg q + 1; : : : ; q − 1; q}.

SLIDE 17
4
Encoding and decoding 1978 McEliece public key: matrix A over F2. Normally s → As is injective. Ciphertext: vector C = As + e. Uses secret “codeword” As, weight-w “error vector” e. 1978 parameters for 264 security goal: 1024 × 512 matrix, w = 50. Public key is secretly generated with “binary Goppa code” structure that allows efficient decoding: C → As; e.
5
Binary Goppa codes Parameters: q ∈ {8; 16; 32; : : :}; w ∈ {2; 3; : : : ; ⌊(q − 1)= lg q⌋}; n ∈ {w lg q + 1; : : : ; q − 1; q}. Secrets: distinct ¸1; : : : ; ¸n ∈ Fq; monic irreducible degree-w polynomial g ∈ Fq[x].

SLIDE 18
4
Encoding and decoding 1978 McEliece public key: matrix A over F2. Normally s → As is injective. Ciphertext: vector C = As + e. Uses secret “codeword” As, weight-w “error vector” e. 1978 parameters for 264 security goal: 1024 × 512 matrix, w = 50. Public key is secretly generated with “binary Goppa code” structure that allows efficient decoding: C → As; e.
5
Binary Goppa codes Parameters: q ∈ {8; 16; 32; : : :}; w ∈ {2; 3; : : : ; ⌊(q − 1)= lg q⌋}; n ∈ {w lg q + 1; : : : ; q − 1; q}. Secrets: distinct ¸1; : : : ; ¸n ∈ Fq; monic irreducible degree-w polynomial g ∈ Fq[x]. Goppa code: kernel of the map v → P
i vi=(x − ¸i)
from Fn
2 to Fq[x]=g.
Normal dimension n − w lg q.

SLIDE 19
4
Encoding and decoding 1978 McEliece public key: matrix A over F2. Normally s → As is injective. Ciphertext: vector C = As + e. Uses secret “codeword” As, weight-w “error vector” e. 1978 parameters for 264 security goal: 1024 × 512 matrix, w = 50. Public key is secretly generated with “binary Goppa code” structure that allows efficient decoding: C → As; e.
5
Binary Goppa codes Parameters: q ∈ {8; 16; 32; : : :}; w ∈ {2; 3; : : : ; ⌊(q − 1)= lg q⌋}; n ∈ {w lg q + 1; : : : ; q − 1; q}. Secrets: distinct ¸1; : : : ; ¸n ∈ Fq; monic irreducible degree-w polynomial g ∈ Fq[x]. Goppa code: kernel of the map v → P
i vi=(x − ¸i)
from Fn
2 to Fq[x]=g.
Normal dimension n − w lg q. McEliece uses random matrix A whose image is this code.

SLIDE 20
4
ding and decoding McEliece public key: A over F2. rmally s → As is injective. Ciphertext: vector C = As + e. secret “codeword” As, eight-w “error vector” e. parameters for 264 security 1024 × 512 matrix, w = 50. key is secretly generated “binary Goppa code” structure that allows efficient ding: C → As; e.
5
Binary Goppa codes Parameters: q ∈ {8; 16; 32; : : :}; w ∈ {2; 3; : : : ; ⌊(q − 1)= lg q⌋}; n ∈ {w lg q + 1; : : : ; q − 1; q}. Secrets: distinct ¸1; : : : ; ¸n ∈ Fq; monic irreducible degree-w polynomial g ∈ Fq[x]. Goppa code: kernel of the map v → P
i vi=(x − ¸i)
from Fn
2 to Fq[x]=g.
Normal dimension n − w lg q. McEliece uses random matrix A whose image is this code. One-wayness Fundamental Given random ciphertext can attack

SLIDE 21
4
decoding public key: . As is injective. vector C = As + e. deword” As, vector” e. for 264 security 512 matrix, w = 50. secretly generated Goppa code” allows efficient As; e.
5
Binary Goppa codes Parameters: q ∈ {8; 16; 32; : : :}; w ∈ {2; 3; : : : ; ⌊(q − 1)= lg q⌋}; n ∈ {w lg q + 1; : : : ; q − 1; q}. Secrets: distinct ¸1; : : : ; ¸n ∈ Fq; monic irreducible degree-w polynomial g ∈ Fq[x]. Goppa code: kernel of the map v → P
i vi=(x − ¸i)
from Fn
2 to Fq[x]=g.
Normal dimension n − w lg q. McEliece uses random matrix A whose image is this code. One-wayness (OW-P Fundamental securit Given random public ciphertext As + e can attacker efficiently

SLIDE 22
4
injective. + e. As, . security w = 50. generated efficient
5
Binary Goppa codes Parameters: q ∈ {8; 16; 32; : : :}; w ∈ {2; 3; : : : ; ⌊(q − 1)= lg q⌋}; n ∈ {w lg q + 1; : : : ; q − 1; q}. Secrets: distinct ¸1; : : : ; ¸n ∈ Fq; monic irreducible degree-w polynomial g ∈ Fq[x]. Goppa code: kernel of the map v → P
i vi=(x − ¸i)
from Fn
2 to Fq[x]=g.
Normal dimension n − w lg q. McEliece uses random matrix A whose image is this code. One-wayness (OW-Passive) Fundamental security question: Given random public key A and ciphertext As + e for random can attacker efficiently find s

SLIDE 23
5
Binary Goppa codes Parameters: q ∈ {8; 16; 32; : : :}; w ∈ {2; 3; : : : ; ⌊(q − 1)= lg q⌋}; n ∈ {w lg q + 1; : : : ; q − 1; q}. Secrets: distinct ¸1; : : : ; ¸n ∈ Fq; monic irreducible degree-w polynomial g ∈ Fq[x]. Goppa code: kernel of the map v → P
i vi=(x − ¸i)
from Fn
2 to Fq[x]=g.
Normal dimension n − w lg q. McEliece uses random matrix A whose image is this code.
6
One-wayness (OW-Passive) Fundamental security question: Given random public key A and ciphertext As + e for random s; e, can attacker efficiently find s; e?

SLIDE 24
5
Binary Goppa codes Parameters: q ∈ {8; 16; 32; : : :}; w ∈ {2; 3; : : : ; ⌊(q − 1)= lg q⌋}; n ∈ {w lg q + 1; : : : ; q − 1; q}. Secrets: distinct ¸1; : : : ; ¸n ∈ Fq; monic irreducible degree-w polynomial g ∈ Fq[x]. Goppa code: kernel of the map v → P
i vi=(x − ¸i)
from Fn
2 to Fq[x]=g.
Normal dimension n − w lg q. McEliece uses random matrix A whose image is this code.
6
One-wayness (OW-Passive) Fundamental security question: Given random public key A and ciphertext As + e for random s; e, can attacker efficiently find s; e? 1962 Prange: simple attack idea guiding sizes in 1978 McEliece.

SLIDE 25
5
Binary Goppa codes Parameters: q ∈ {8; 16; 32; : : :}; w ∈ {2; 3; : : : ; ⌊(q − 1)= lg q⌋}; n ∈ {w lg q + 1; : : : ; q − 1; q}. Secrets: distinct ¸1; : : : ; ¸n ∈ Fq; monic irreducible degree-w polynomial g ∈ Fq[x]. Goppa code: kernel of the map v → P
i vi=(x − ¸i)
from Fn
2 to Fq[x]=g.
Normal dimension n − w lg q. McEliece uses random matrix A whose image is this code.
6
One-wayness (OW-Passive) Fundamental security question: Given random public key A and ciphertext As + e for random s; e, can attacker efficiently find s; e? 1962 Prange: simple attack idea guiding sizes in 1978 McEliece. The McEliece system (with later key-size optimizations) uses (c0 + o(1))–2(lg –)2-bit keys as – → ∞ to achieve 2– security against Prange’s attack. Here c0 ≈ 0:7418860694.

SLIDE 26 5
Goppa codes rameters: q ∈ {8; 16; 32; : : :}; 2; 3; : : : ; ⌊(q − 1)= lg q⌋}; lg q + 1; : : : ; q − 1; q}. Secrets: distinct ¸1; : : : ; ¸n ∈ Fq; irreducible degree-w
code: kernel of map v → P
i vi=(x − ¸i) n 2 to Fq[x]=g.
rmal dimension n − w lg q. McEliece uses random matrix A image is this code.
6
One-wayness (OW-Passive) Fundamental security question: Given random public key A and ciphertext As + e for random s; e, can attacker efficiently find s; e? 1962 Prange: simple attack idea guiding sizes in 1978 McEliece. The McEliece system (with later key-size optimizations) uses (c0 + o(1))–2(lg –)2-bit keys as – → ∞ to achieve 2– security against Prange’s attack. Here c0 ≈ 0:7418860694. ≥25 subsequent analyzing 1981 Cla crediting 1988 Lee–Brick 1988 Leon. 1989 Krouk. 1989 Stern. 1989 Dumer. 1990 Coffey–Go 1990 van 1991 Dumer. 1991 Coffey–Go 1993 Chabanne–Courteau.

SLIDE 27
5
des {8; 16; 32; : : :}; (q − 1)= lg q⌋}; : : : ; q − 1; q}. ¸1; : : : ; ¸n ∈ Fq; irreducible degree-w Fq[x]. ernel of
i vi=(x − ¸i)
]=g. dimension n − w lg q. random matrix A this code.
6
One-wayness (OW-Passive) Fundamental security question: Given random public key A and ciphertext As + e for random s; e, can attacker efficiently find s; e? 1962 Prange: simple attack idea guiding sizes in 1978 McEliece. The McEliece system (with later key-size optimizations) uses (c0 + o(1))–2(lg –)2-bit keys as – → ∞ to achieve 2– security against Prange’s attack. Here c0 ≈ 0:7418860694. ≥25 subsequent publication analyzing one-wayness 1981 Clark–Cain, crediting Omura. 1988 Lee–Brickell. 1988 Leon. 1989 Krouk. 1989 Stern. 1989 Dumer. 1990 Coffey–Goodman. 1990 van Tilburg. 1991 Dumer. 1991 Coffey–Goodman–F 1993 Chabanne–Courteau.

SLIDE 28
5
; : : :}; q⌋}; ; q}.
n ∈ Fq;
¸i) lg q. matrix A
6
One-wayness (OW-Passive) Fundamental security question: Given random public key A and ciphertext As + e for random s; e, can attacker efficiently find s; e? 1962 Prange: simple attack idea guiding sizes in 1978 McEliece. The McEliece system (with later key-size optimizations) uses (c0 + o(1))–2(lg –)2-bit keys as – → ∞ to achieve 2– security against Prange’s attack. Here c0 ≈ 0:7418860694. ≥25 subsequent publications analyzing one-wayness of system 1981 Clark–Cain, crediting Omura. 1988 Lee–Brickell. 1988 Leon. 1989 Krouk. 1989 Stern. 1989 Dumer. 1990 Coffey–Goodman. 1990 van Tilburg. 1991 Dumer. 1991 Coffey–Goodman–Farrell. 1993 Chabanne–Courteau.

SLIDE 29
6
One-wayness (OW-Passive) Fundamental security question: Given random public key A and ciphertext As + e for random s; e, can attacker efficiently find s; e? 1962 Prange: simple attack idea guiding sizes in 1978 McEliece. The McEliece system (with later key-size optimizations) uses (c0 + o(1))–2(lg –)2-bit keys as – → ∞ to achieve 2– security against Prange’s attack. Here c0 ≈ 0:7418860694.
7
≥25 subsequent publications analyzing one-wayness of system: 1981 Clark–Cain, crediting Omura. 1988 Lee–Brickell. 1988 Leon. 1989 Krouk. 1989 Stern. 1989 Dumer. 1990 Coffey–Goodman. 1990 van Tilburg. 1991 Dumer. 1991 Coffey–Goodman–Farrell. 1993 Chabanne–Courteau.

SLIDE 30
6
ayness (OW-Passive) undamental security question: random public key A and ciphertext As + e for random s; e, attacker efficiently find s; e? Prange: simple attack idea guiding sizes in 1978 McEliece. McEliece system later key-size optimizations)
0 + o(1))–2(lg –)2-bit keys
∞ to achieve 2– security against Prange’s attack.
0 ≈ 0:7418860694.
7
≥25 subsequent publications analyzing one-wayness of system: 1981 Clark–Cain, crediting Omura. 1988 Lee–Brickell. 1988 Leon. 1989 Krouk. 1989 Stern. 1989 Dumer. 1990 Coffey–Goodman. 1990 van Tilburg. 1991 Dumer. 1991 Coffey–Goodman–Farrell. 1993 Chabanne–Courteau. 1993 Chabaud. 1994 van 1994 Canteaut–Chabanne. 1998 Canteaut–Chabaud. 1998 Canteaut–Sendrier. 2008 Bernstein–Lange–P 2009 Bernstein–Lange–P van 2009 Finiasz–Sendrier. 2011 Bernstein–Lange–P 2011 Ma 2012 Beck 2013 Hamdaoui–Sendrier. 2015 Ma 2016 Canto

SLIDE 31
6
W-Passive) security question: public key A and e for random s; e, efficiently find s; e? simple attack idea 1978 McEliece. system ey-size optimizations) –2(lg –)2-bit keys achieve 2– security attack. 7418860694.
7
≥25 subsequent publications analyzing one-wayness of system: 1981 Clark–Cain, crediting Omura. 1988 Lee–Brickell. 1988 Leon. 1989 Krouk. 1989 Stern. 1989 Dumer. 1990 Coffey–Goodman. 1990 van Tilburg. 1991 Dumer. 1991 Coffey–Goodman–Farrell. 1993 Chabanne–Courteau. 1993 Chabaud. 1994 van Tilburg. 1994 Canteaut–Chabanne. 1998 Canteaut–Chabaud. 1998 Canteaut–Sendrier. 2008 Bernstein–Lange–P 2009 Bernstein–Lange–P van Tilborg. 2009 Finiasz–Sendrier. 2011 Bernstein–Lange–P 2011 May–Meurer–Th 2012 Becker–Joux–Ma 2013 Hamdaoui–Sendrier. 2015 May–Ozerov. 2016 Canto Torres–Sendrier.

SLIDE 32 6
assive) question: and random s; e, find s; e? attack idea McEliece.
security
7
≥25 subsequent publications analyzing one-wayness of system: 1981 Clark–Cain, crediting Omura. 1988 Lee–Brickell. 1988 Leon. 1989 Krouk. 1989 Stern. 1989 Dumer. 1990 Coffey–Goodman. 1990 van Tilburg. 1991 Dumer. 1991 Coffey–Goodman–Farrell. 1993 Chabanne–Courteau. 1993 Chabaud. 1994 van Tilburg. 1994 Canteaut–Chabanne. 1998 Canteaut–Chabaud. 1998 Canteaut–Sendrier. 2008 Bernstein–Lange–Peters. 2009 Bernstein–Lange–Peters– van Tilborg. 2009 Finiasz–Sendrier. 2011 Bernstein–Lange–Peters. 2011 May–Meurer–Thomae. 2012 Becker–Joux–May–Meurer. 2013 Hamdaoui–Sendrier. 2015 May–Ozerov. 2016 Canto Torres–Sendrier.

SLIDE 33
7
≥25 subsequent publications analyzing one-wayness of system: 1981 Clark–Cain, crediting Omura. 1988 Lee–Brickell. 1988 Leon. 1989 Krouk. 1989 Stern. 1989 Dumer. 1990 Coffey–Goodman. 1990 van Tilburg. 1991 Dumer. 1991 Coffey–Goodman–Farrell. 1993 Chabanne–Courteau.
8
1993 Chabaud. 1994 van Tilburg. 1994 Canteaut–Chabanne. 1998 Canteaut–Chabaud. 1998 Canteaut–Sendrier. 2008 Bernstein–Lange–Peters. 2009 Bernstein–Lange–Peters– van Tilborg. 2009 Finiasz–Sendrier. 2011 Bernstein–Lange–Peters. 2011 May–Meurer–Thomae. 2012 Becker–Joux–May–Meurer. 2013 Hamdaoui–Sendrier. 2015 May–Ozerov. 2016 Canto Torres–Sendrier.

SLIDE 34
7
subsequent publications analyzing one-wayness of system: Clark–Cain, crediting Omura. Lee–Brickell. Leon. Krouk. Stern. Dumer. Coffey–Goodman. van Tilburg. Dumer. Coffey–Goodman–Farrell. Chabanne–Courteau.
8
1993 Chabaud. 1994 van Tilburg. 1994 Canteaut–Chabanne. 1998 Canteaut–Chabaud. 1998 Canteaut–Sendrier. 2008 Bernstein–Lange–Peters. 2009 Bernstein–Lange–Peters– van Tilborg. 2009 Finiasz–Sendrier. 2011 Bernstein–Lange–Peters. 2011 May–Meurer–Thomae. 2012 Becker–Joux–May–Meurer. 2013 Hamdaoui–Sendrier. 2015 May–Ozerov. 2016 Canto Torres–Sendrier. The McEliece uses (c0 as – → ∞ against all Same c0

SLIDE 35 7
publications ayness of system: k–Cain, Omura. ell.
urg.
Chabanne–Courteau.
8
1993 Chabaud. 1994 van Tilburg. 1994 Canteaut–Chabanne. 1998 Canteaut–Chabaud. 1998 Canteaut–Sendrier. 2008 Bernstein–Lange–Peters. 2009 Bernstein–Lange–Peters– van Tilborg. 2009 Finiasz–Sendrier. 2011 Bernstein–Lange–Peters. 2011 May–Meurer–Thomae. 2012 Becker–Joux–May–Meurer. 2013 Hamdaoui–Sendrier. 2015 May–Ozerov. 2016 Canto Torres–Sendrier. The McEliece system uses (c0 + o(1))–2 as – → ∞ to achieve against all attacks Same c0 ≈ 0:7418860694.

SLIDE 36
7
publications system: rrell. Chabanne–Courteau.
8
1993 Chabaud. 1994 van Tilburg. 1994 Canteaut–Chabanne. 1998 Canteaut–Chabaud. 1998 Canteaut–Sendrier. 2008 Bernstein–Lange–Peters. 2009 Bernstein–Lange–Peters– van Tilborg. 2009 Finiasz–Sendrier. 2011 Bernstein–Lange–Peters. 2011 May–Meurer–Thomae. 2012 Becker–Joux–May–Meurer. 2013 Hamdaoui–Sendrier. 2015 May–Ozerov. 2016 Canto Torres–Sendrier. The McEliece system uses (c0 + o(1))–2(lg –)2-bit as – → ∞ to achieve 2– securit against all attacks known to Same c0 ≈ 0:7418860694.

SLIDE 37
8
1993 Chabaud. 1994 van Tilburg. 1994 Canteaut–Chabanne. 1998 Canteaut–Chabaud. 1998 Canteaut–Sendrier. 2008 Bernstein–Lange–Peters. 2009 Bernstein–Lange–Peters– van Tilborg. 2009 Finiasz–Sendrier. 2011 Bernstein–Lange–Peters. 2011 May–Meurer–Thomae. 2012 Becker–Joux–May–Meurer. 2013 Hamdaoui–Sendrier. 2015 May–Ozerov. 2016 Canto Torres–Sendrier.
9
The McEliece system uses (c0 + o(1))–2(lg –)2-bit keys as – → ∞ to achieve 2– security against all attacks known today. Same c0 ≈ 0:7418860694.

SLIDE 38
8
1993 Chabaud. 1994 van Tilburg. 1994 Canteaut–Chabanne. 1998 Canteaut–Chabaud. 1998 Canteaut–Sendrier. 2008 Bernstein–Lange–Peters. 2009 Bernstein–Lange–Peters– van Tilborg. 2009 Finiasz–Sendrier. 2011 Bernstein–Lange–Peters. 2011 May–Meurer–Thomae. 2012 Becker–Joux–May–Meurer. 2013 Hamdaoui–Sendrier. 2015 May–Ozerov. 2016 Canto Torres–Sendrier.
9
The McEliece system uses (c0 + o(1))–2(lg –)2-bit keys as – → ∞ to achieve 2– security against all attacks known today. Same c0 ≈ 0:7418860694. Replacing – with 2– stops all known quantum attacks (and is probably massive overkill), as in symmetric crypto.

SLIDE 39
8
1993 Chabaud. 1994 van Tilburg. 1994 Canteaut–Chabanne. 1998 Canteaut–Chabaud. 1998 Canteaut–Sendrier. 2008 Bernstein–Lange–Peters. 2009 Bernstein–Lange–Peters– van Tilborg. 2009 Finiasz–Sendrier. 2011 Bernstein–Lange–Peters. 2011 May–Meurer–Thomae. 2012 Becker–Joux–May–Meurer. 2013 Hamdaoui–Sendrier. 2015 May–Ozerov. 2016 Canto Torres–Sendrier.
9
The McEliece system uses (c0 + o(1))–2(lg –)2-bit keys as – → ∞ to achieve 2– security against all attacks known today. Same c0 ≈ 0:7418860694. Replacing – with 2– stops all known quantum attacks (and is probably massive overkill), as in symmetric crypto. mceliece6960119 parameter set (2008 Bernstein–Lange–Peters): q = 8192, n = 6960, w = 119. Also in submission: 8192128, 6688128, 460896, 348864.

SLIDE 40
8
Chabaud. van Tilburg. Canteaut–Chabanne. Canteaut–Chabaud. Canteaut–Sendrier. Bernstein–Lange–Peters. Bernstein–Lange–Peters– van Tilborg. Finiasz–Sendrier. Bernstein–Lange–Peters. May–Meurer–Thomae. Becker–Joux–May–Meurer. Hamdaoui–Sendrier. May–Ozerov. Canto Torres–Sendrier.
9
The McEliece system uses (c0 + o(1))–2(lg –)2-bit keys as – → ∞ to achieve 2– security against all attacks known today. Same c0 ≈ 0:7418860694. Replacing – with 2– stops all known quantum attacks (and is probably massive overkill), as in symmetric crypto. mceliece6960119 parameter set (2008 Bernstein–Lange–Peters): q = 8192, n = 6960, w = 119. Also in submission: 8192128, 6688128, 460896, 348864. McEliece’s huge amount Some wo while clea e.g., Niederreiter’s e.g., many Classic McEliec

SLIDE 41
8
rg. Canteaut–Chabanne. Canteaut–Chabaud. Canteaut–Sendrier. Bernstein–Lange–Peters. Bernstein–Lange–Peters– rg. Finiasz–Sendrier. Bernstein–Lange–Peters. y–Meurer–Thomae. er–Joux–May–Meurer. Hamdaoui–Sendrier. y–Ozerov. rres–Sendrier.
9
The McEliece system uses (c0 + o(1))–2(lg –)2-bit keys as – → ∞ to achieve 2– security against all attacks known today. Same c0 ≈ 0:7418860694. Replacing – with 2– stops all known quantum attacks (and is probably massive overkill), as in symmetric crypto. mceliece6960119 parameter set (2008 Bernstein–Lange–Peters): q = 8192, n = 6960, w = 119. Also in submission: 8192128, 6688128, 460896, 348864. McEliece’s system huge amount of follo Some work improves while clearly preserving e.g., Niederreiter’s e.g., many decoding Classic McEliece uses

SLIDE 42
8
Canteaut–Chabanne. eters. eters– eters. ae. y–Meurer. rres–Sendrier.
9
The McEliece system uses (c0 + o(1))–2(lg –)2-bit keys as – → ∞ to achieve 2– security against all attacks known today. Same c0 ≈ 0:7418860694. Replacing – with 2– stops all known quantum attacks (and is probably massive overkill), as in symmetric crypto. mceliece6960119 parameter set (2008 Bernstein–Lange–Peters): q = 8192, n = 6960, w = 119. Also in submission: 8192128, 6688128, 460896, 348864. McEliece’s system prompted huge amount of followup wo Some work improves efficiency while clearly preserving secur e.g., Niederreiter’s dual PKE; e.g., many decoding speedups. Classic McEliece uses all this.

SLIDE 43
9
The McEliece system uses (c0 + o(1))–2(lg –)2-bit keys as – → ∞ to achieve 2– security against all attacks known today. Same c0 ≈ 0:7418860694. Replacing – with 2– stops all known quantum attacks (and is probably massive overkill), as in symmetric crypto. mceliece6960119 parameter set (2008 Bernstein–Lange–Peters): q = 8192, n = 6960, w = 119. Also in submission: 8192128, 6688128, 460896, 348864.
10
McEliece’s system prompted a huge amount of followup work. Some work improves efficiency while clearly preserving security: e.g., Niederreiter’s dual PKE; e.g., many decoding speedups. Classic McEliece uses all this.

SLIDE 44
9
The McEliece system uses (c0 + o(1))–2(lg –)2-bit keys as – → ∞ to achieve 2– security against all attacks known today. Same c0 ≈ 0:7418860694. Replacing – with 2– stops all known quantum attacks (and is probably massive overkill), as in symmetric crypto. mceliece6960119 parameter set (2008 Bernstein–Lange–Peters): q = 8192, n = 6960, w = 119. Also in submission: 8192128, 6688128, 460896, 348864.
10
McEliece’s system prompted a huge amount of followup work. Some work improves efficiency while clearly preserving security: e.g., Niederreiter’s dual PKE; e.g., many decoding speedups. Classic McEliece uses all this. Classic McEliece does not use variants whose security has not been studied as thoroughly: e.g., replacing binary Goppa codes with other families of codes; e.g., lattice-based cryptography.

SLIDE 45 9
McEliece system
0 + o(1))–2(lg –)2-bit keys
∞ to achieve 2– security against all attacks known today. c0 ≈ 0:7418860694. Replacing – with 2– all known quantum attacks is probably massive overkill), symmetric crypto. mceliece6960119 parameter set Bernstein–Lange–Peters): 8192, n = 6960, w = 119. submission: 8192128, 6688128, 460896, 348864.
10
McEliece’s system prompted a huge amount of followup work. Some work improves efficiency while clearly preserving security: e.g., Niederreiter’s dual PKE; e.g., many decoding speedups. Classic McEliece uses all this. Classic McEliece does not use variants whose security has not been studied as thoroughly: e.g., replacing binary Goppa codes with other families of codes; e.g., lattice-based cryptography. Niederreiter Generato
n × k matrix McEliece random k

SLIDE 46 9
system –2(lg –)2-bit keys achieve 2– security attacks known today. 7418860694. 2– quantum attacks massive overkill), crypto. mceliece6960119 parameter set Bernstein–Lange–Peters): 6960, w = 119. submission: 8192128, , 348864.
10
McEliece’s system prompted a huge amount of followup work. Some work improves efficiency while clearly preserving security: e.g., Niederreiter’s dual PKE; e.g., many decoding speedups. Classic McEliece uses all this. Classic McEliece does not use variants whose security has not been studied as thoroughly: e.g., replacing binary Goppa codes with other families of codes; e.g., lattice-based cryptography. Niederreiter key comp Generator matrix fo
n × k matrix G with McEliece public key: random k × k invertible

SLIDE 47 9
security today. attacks
rameter set eters): 119. 8192128, .
10
McEliece’s system prompted a huge amount of followup work. Some work improves efficiency while clearly preserving security: e.g., Niederreiter’s dual PKE; e.g., many decoding speedups. Classic McEliece uses all this. Classic McEliece does not use variants whose security has not been studied as thoroughly: e.g., replacing binary Goppa codes with other families of codes; e.g., lattice-based cryptography. Niederreiter key compression Generator matrix for code Γ
- f length n and dimension k
n × k matrix G with Γ = G · McEliece public key: G times random k × k invertible matrix.

SLIDE 48 10
McEliece’s system prompted a huge amount of followup work. Some work improves efficiency while clearly preserving security: e.g., Niederreiter’s dual PKE; e.g., many decoding speedups. Classic McEliece uses all this. Classic McEliece does not use variants whose security has not been studied as thoroughly: e.g., replacing binary Goppa codes with other families of codes; e.g., lattice-based cryptography.
11
Niederreiter key compression Generator matrix for code Γ
- f length n and dimension k:
n × k matrix G with Γ = G · Fk
2.
McEliece public key: G times random k × k invertible matrix.

SLIDE 49 10
McEliece’s system prompted a huge amount of followup work. Some work improves efficiency while clearly preserving security: e.g., Niederreiter’s dual PKE; e.g., many decoding speedups. Classic McEliece uses all this. Classic McEliece does not use variants whose security has not been studied as thoroughly: e.g., replacing binary Goppa codes with other families of codes; e.g., lattice-based cryptography.
11
Niederreiter key compression Generator matrix for code Γ
- f length n and dimension k:
n × k matrix G with Γ = G · Fk
2.
McEliece public key: G times random k × k invertible matrix. Niederreiter instead reduces G to the unique generator matrix in “systematic form”: bottom k rows are k × k identity matrix Ik. Public key T is top n − k rows.

SLIDE 50 10
McEliece’s system prompted a huge amount of followup work. Some work improves efficiency while clearly preserving security: e.g., Niederreiter’s dual PKE; e.g., many decoding speedups. Classic McEliece uses all this. Classic McEliece does not use variants whose security has not been studied as thoroughly: e.g., replacing binary Goppa codes with other families of codes; e.g., lattice-based cryptography.
11
Niederreiter key compression Generator matrix for code Γ
- f length n and dimension k:
n × k matrix G with Γ = G · Fk
2.
McEliece public key: G times random k × k invertible matrix. Niederreiter instead reduces G to the unique generator matrix in “systematic form”: bottom k rows are k × k identity matrix Ik. Public key T is top n − k rows. Pr ≈29% that systematic form
- exists. Security loss: <2 bits.

SLIDE 51 10
McEliece’s system prompted a amount of followup work. work improves efficiency clearly preserving security: Niederreiter’s dual PKE; many decoding speedups. McEliece uses all this. McEliece does not use riants whose security has not studied as thoroughly: replacing binary Goppa codes
lattice-based cryptography.
11
Niederreiter key compression Generator matrix for code Γ
- f length n and dimension k:
n × k matrix G with Γ = G · Fk
2.
McEliece public key: G times random k × k invertible matrix. Niederreiter instead reduces G to the unique generator matrix in “systematic form”: bottom k rows are k × k identity matrix Ik. Public key T is top n − k rows. Pr ≈29% that systematic form
- exists. Security loss: <2 bits.
Niederreiter Use Niede McEliece

SLIDE 52 10
system prompted a followup work. roves efficiency reserving security: Niederreiter’s dual PKE; ding speedups. uses all this. does not use security has not thoroughly: binary Goppa codes families of codes; lattice-based cryptography.
11
Niederreiter key compression Generator matrix for code Γ
- f length n and dimension k:
n × k matrix G with Γ = G · Fk
2.
McEliece public key: G times random k × k invertible matrix. Niederreiter instead reduces G to the unique generator matrix in “systematic form”: bottom k rows are k × k identity matrix Ik. Public key T is top n − k rows. Pr ≈29% that systematic form
- exists. Security loss: <2 bits.
Niederreiter ciphertext Use Niederreiter key McEliece ciphertext:

SLIDE 53 10
rompted a work. efficiency curity: PKE; edups. this. use has not roughly: Goppa codes des; cryptography.
11
Niederreiter key compression Generator matrix for code Γ
- f length n and dimension k:
n × k matrix G with Γ = G · Fk
2.
McEliece public key: G times random k × k invertible matrix. Niederreiter instead reduces G to the unique generator matrix in “systematic form”: bottom k rows are k × k identity matrix Ik. Public key T is top n − k rows. Pr ≈29% that systematic form
- exists. Security loss: <2 bits.
Niederreiter ciphertext comp Use Niederreiter key A = „ T I McEliece ciphertext: As + e

SLIDE 54 11
Niederreiter key compression Generator matrix for code Γ
- f length n and dimension k:
n × k matrix G with Γ = G · Fk
2.
McEliece public key: G times random k × k invertible matrix. Niederreiter instead reduces G to the unique generator matrix in “systematic form”: bottom k rows are k × k identity matrix Ik. Public key T is top n − k rows. Pr ≈29% that systematic form
- exists. Security loss: <2 bits.
12
Niederreiter ciphertext compression Use Niederreiter key A = „ T Ik « . McEliece ciphertext: As + e ∈ Fn
2.

SLIDE 55 11
Niederreiter key compression Generator matrix for code Γ
- f length n and dimension k:
n × k matrix G with Γ = G · Fk
2.
McEliece public key: G times random k × k invertible matrix. Niederreiter instead reduces G to the unique generator matrix in “systematic form”: bottom k rows are k × k identity matrix Ik. Public key T is top n − k rows. Pr ≈29% that systematic form
- exists. Security loss: <2 bits.
12
Niederreiter ciphertext compression Use Niederreiter key A = „ T Ik « . McEliece ciphertext: As + e ∈ Fn
2.
Niederreiter ciphertext, shorter: He ∈ Fn−k
2
where H = (In−k|T).

SLIDE 56 11
Niederreiter key compression Generator matrix for code Γ
- f length n and dimension k:
n × k matrix G with Γ = G · Fk
2.
McEliece public key: G times random k × k invertible matrix. Niederreiter instead reduces G to the unique generator matrix in “systematic form”: bottom k rows are k × k identity matrix Ik. Public key T is top n − k rows. Pr ≈29% that systematic form
- exists. Security loss: <2 bits.
12
Niederreiter ciphertext compression Use Niederreiter key A = „ T Ik « . McEliece ciphertext: As + e ∈ Fn
2.
Niederreiter ciphertext, shorter: He ∈ Fn−k
2
where H = (In−k|T). Given H and Niederreiter’s He, can attacker efficiently find e?

SLIDE 57 11
Niederreiter key compression Generator matrix for code Γ
- f length n and dimension k:
n × k matrix G with Γ = G · Fk
2.
McEliece public key: G times random k × k invertible matrix. Niederreiter instead reduces G to the unique generator matrix in “systematic form”: bottom k rows are k × k identity matrix Ik. Public key T is top n − k rows. Pr ≈29% that systematic form
- exists. Security loss: <2 bits.
12
Niederreiter ciphertext compression Use Niederreiter key A = „ T Ik « . McEliece ciphertext: As + e ∈ Fn
2.
Niederreiter ciphertext, shorter: He ∈ Fn−k
2
where H = (In−k|T). Given H and Niederreiter’s He, can attacker efficiently find e? If so, attacker can efficiently find s; e given A and As + e: compute H(As + e) = He; find e; compute s from As.

SLIDE 58
11
Niederreiter key compression Generator matrix for code Γ length n and dimension k: matrix G with Γ = G · Fk
2.
McEliece public key: G times k × k invertible matrix. Niederreiter instead reduces G unique generator matrix “systematic form”: bottom k re k × k identity matrix Ik. key T is top n − k rows. 29% that systematic form Security loss: <2 bits.
12
Niederreiter ciphertext compression Use Niederreiter key A = „ T Ik « . McEliece ciphertext: As + e ∈ Fn
2.
Niederreiter ciphertext, shorter: He ∈ Fn−k
2
where H = (In−k|T). Given H and Niederreiter’s He, can attacker efficiently find e? If so, attacker can efficiently find s; e given A and As + e: compute H(As + e) = He; find e; compute s from As. The immaturit Case study: the most 2006 Silverman: and CVP studied fo both as intrinsic problems pure and physics and

SLIDE 59
11
compression ix for code Γ dimension k: with Γ = G · Fk
2.
key: G times invertible matrix. instead reduces G generator matrix form”: bottom k identity matrix Ik. top n − k rows. systematic form loss: <2 bits.
12
Niederreiter ciphertext compression Use Niederreiter key A = „ T Ik « . McEliece ciphertext: As + e ∈ Fn
2.
Niederreiter ciphertext, shorter: He ∈ Fn−k
2
where H = (In−k|T). Given H and Niederreiter’s He, can attacker efficiently find e? If so, attacker can efficiently find s; e given A and As + e: compute H(As + e) = He; find e; compute s from As. The immaturity of Case study: SVP, the most famous lattice 2006 Silverman: “Lattices, and CVP, have been studied for more than both as intrinsic mathematical problems and for applications pure and applied mathematics, physics and cryptograph

SLIDE 60 11
ression Γ k: · Fk
2.
times matrix. reduces G matrix
matrix Ik. rows. form bits.
12
Niederreiter ciphertext compression Use Niederreiter key A = „ T Ik « . McEliece ciphertext: As + e ∈ Fn
2.
Niederreiter ciphertext, shorter: He ∈ Fn−k
2
where H = (In−k|T). Given H and Niederreiter’s He, can attacker efficiently find e? If so, attacker can efficiently find s; e given A and As + e: compute H(As + e) = He; find e; compute s from As. The immaturity of lattice attacks Case study: SVP, the most famous lattice problem. 2006 Silverman: “Lattices, SVP and CVP, have been intensively studied for more than 100 yea both as intrinsic mathematical problems and for applications pure and applied mathematics, physics and cryptography.”

SLIDE 61
12
Niederreiter ciphertext compression Use Niederreiter key A = „ T Ik « . McEliece ciphertext: As + e ∈ Fn
2.
Niederreiter ciphertext, shorter: He ∈ Fn−k
2
where H = (In−k|T). Given H and Niederreiter’s He, can attacker efficiently find e? If so, attacker can efficiently find s; e given A and As + e: compute H(As + e) = He; find e; compute s from As.
13
The immaturity of lattice attacks Case study: SVP, the most famous lattice problem. 2006 Silverman: “Lattices, SVP and CVP, have been intensively studied for more than 100 years, both as intrinsic mathematical problems and for applications in pure and applied mathematics, physics and cryptography.”

SLIDE 62
12
Niederreiter ciphertext compression Use Niederreiter key A = „ T Ik « . McEliece ciphertext: As + e ∈ Fn
2.
Niederreiter ciphertext, shorter: He ∈ Fn−k
2
where H = (In−k|T). Given H and Niederreiter’s He, can attacker efficiently find e? If so, attacker can efficiently find s; e given A and As + e: compute H(As + e) = He; find e; compute s from As.
13
The immaturity of lattice attacks Case study: SVP, the most famous lattice problem. 2006 Silverman: “Lattices, SVP and CVP, have been intensively studied for more than 100 years, both as intrinsic mathematical problems and for applications in pure and applied mathematics, physics and cryptography.” Best SVP algorithms known by 2000: time 2Θ(N log N) for almost all dimension-N lattices.

SLIDE 63
12
Niederreiter ciphertext compression Niederreiter key A = „ T Ik « . McEliece ciphertext: As + e ∈ Fn
2.
Niederreiter ciphertext, shorter: Fn−k
2
where H = (In−k|T). H and Niederreiter’s He, attacker efficiently find e? attacker can efficiently e given A and As + e: compute H(As + e) = He; compute s from As.
13
The immaturity of lattice attacks Case study: SVP, the most famous lattice problem. 2006 Silverman: “Lattices, SVP and CVP, have been intensively studied for more than 100 years, both as intrinsic mathematical problems and for applications in pure and applied mathematics, physics and cryptography.” Best SVP algorithms known by 2000: time 2Θ(N log N) for almost all dimension-N lattices. Best SVP today: 2 Approx c believed 0:415: 2008 0:415: 2010

SLIDE 64
12
ciphertext compression key A = „ T Ik « . ciphertext: As + e ∈ Fn
2.
ciphertext, shorter: where H = (In−k|T). Niederreiter’s He, efficiently find e? can efficiently and As + e: e) = He; s from As.
13
The immaturity of lattice attacks Case study: SVP, the most famous lattice problem. 2006 Silverman: “Lattices, SVP and CVP, have been intensively studied for more than 100 years, both as intrinsic mathematical problems and for applications in pure and applied mathematics, physics and cryptography.” Best SVP algorithms known by 2000: time 2Θ(N log N) for almost all dimension-N lattices. Best SVP algorithms today: 2Θ(N). Approx c for some believed to take time 0:415: 2008 Nguyen–Vidi 0:415: 2010 Micciancio–V

SLIDE 65
12
compression „ T Ik « . e ∈ Fn
2.
shorter:
−k|T).
Niederreiter’s He, find e? efficiently e: ; .
13
The immaturity of lattice attacks Case study: SVP, the most famous lattice problem. 2006 Silverman: “Lattices, SVP and CVP, have been intensively studied for more than 100 years, both as intrinsic mathematical problems and for applications in pure and applied mathematics, physics and cryptography.” Best SVP algorithms known by 2000: time 2Θ(N log N) for almost all dimension-N lattices. Best SVP algorithms known today: 2Θ(N). Approx c for some algorithms believed to take time 2(c+o(1)) 0:415: 2008 Nguyen–Vidick. 0:415: 2010 Micciancio–Voulga

SLIDE 66
13
The immaturity of lattice attacks Case study: SVP, the most famous lattice problem. 2006 Silverman: “Lattices, SVP and CVP, have been intensively studied for more than 100 years, both as intrinsic mathematical problems and for applications in pure and applied mathematics, physics and cryptography.” Best SVP algorithms known by 2000: time 2Θ(N log N) for almost all dimension-N lattices.
14
Best SVP algorithms known today: 2Θ(N). Approx c for some algorithms believed to take time 2(c+o(1))N: 0:415: 2008 Nguyen–Vidick. 0:415: 2010 Micciancio–Voulgaris.

SLIDE 67
13
The immaturity of lattice attacks Case study: SVP, the most famous lattice problem. 2006 Silverman: “Lattices, SVP and CVP, have been intensively studied for more than 100 years, both as intrinsic mathematical problems and for applications in pure and applied mathematics, physics and cryptography.” Best SVP algorithms known by 2000: time 2Θ(N log N) for almost all dimension-N lattices.
14
Best SVP algorithms known today: 2Θ(N). Approx c for some algorithms believed to take time 2(c+o(1))N: 0:415: 2008 Nguyen–Vidick. 0:415: 2010 Micciancio–Voulgaris. 0:384: 2011 Wang–Liu–Tian–Bi.

SLIDE 68
13
The immaturity of lattice attacks Case study: SVP, the most famous lattice problem. 2006 Silverman: “Lattices, SVP and CVP, have been intensively studied for more than 100 years, both as intrinsic mathematical problems and for applications in pure and applied mathematics, physics and cryptography.” Best SVP algorithms known by 2000: time 2Θ(N log N) for almost all dimension-N lattices.
14
Best SVP algorithms known today: 2Θ(N). Approx c for some algorithms believed to take time 2(c+o(1))N: 0:415: 2008 Nguyen–Vidick. 0:415: 2010 Micciancio–Voulgaris. 0:384: 2011 Wang–Liu–Tian–Bi. 0:378: 2013 Zhang–Pan–Hu.

SLIDE 69
13
The immaturity of lattice attacks Case study: SVP, the most famous lattice problem. 2006 Silverman: “Lattices, SVP and CVP, have been intensively studied for more than 100 years, both as intrinsic mathematical problems and for applications in pure and applied mathematics, physics and cryptography.” Best SVP algorithms known by 2000: time 2Θ(N log N) for almost all dimension-N lattices.
14
Best SVP algorithms known today: 2Θ(N). Approx c for some algorithms believed to take time 2(c+o(1))N: 0:415: 2008 Nguyen–Vidick. 0:415: 2010 Micciancio–Voulgaris. 0:384: 2011 Wang–Liu–Tian–Bi. 0:378: 2013 Zhang–Pan–Hu. 0:337: 2014 Laarhoven.

SLIDE 70
13
The immaturity of lattice attacks Case study: SVP, the most famous lattice problem. 2006 Silverman: “Lattices, SVP and CVP, have been intensively studied for more than 100 years, both as intrinsic mathematical problems and for applications in pure and applied mathematics, physics and cryptography.” Best SVP algorithms known by 2000: time 2Θ(N log N) for almost all dimension-N lattices.
14
Best SVP algorithms known today: 2Θ(N). Approx c for some algorithms believed to take time 2(c+o(1))N: 0:415: 2008 Nguyen–Vidick. 0:415: 2010 Micciancio–Voulgaris. 0:384: 2011 Wang–Liu–Tian–Bi. 0:378: 2013 Zhang–Pan–Hu. 0:337: 2014 Laarhoven. 0:298: 2015 Laarhoven–de Weger. 0:292: 2015 Becker–Ducas– Gama–Laarhoven.

SLIDE 71
13
The immaturity of lattice attacks Case study: SVP, the most famous lattice problem. 2006 Silverman: “Lattices, SVP and CVP, have been intensively studied for more than 100 years, both as intrinsic mathematical problems and for applications in pure and applied mathematics, physics and cryptography.” Best SVP algorithms known by 2000: time 2Θ(N log N) for almost all dimension-N lattices.
14
Best SVP algorithms known today: 2Θ(N). Approx c for some algorithms believed to take time 2(c+o(1))N: 0:415: 2008 Nguyen–Vidick. 0:415: 2010 Micciancio–Voulgaris. 0:384: 2011 Wang–Liu–Tian–Bi. 0:378: 2013 Zhang–Pan–Hu. 0:337: 2014 Laarhoven. 0:298: 2015 Laarhoven–de Weger. 0:292: 2015 Becker–Ducas– Gama–Laarhoven. Lattice crypto: more attack avenues; even less understanding.

SLIDE 72
13
immaturity of lattice attacks study: SVP, most famous lattice problem. Silverman: “Lattices, SVP CVP, have been intensively studied for more than 100 years, as intrinsic mathematical roblems and for applications in and applied mathematics, physics and cryptography.” SVP algorithms known 2000: time 2Θ(N log N) for all dimension-N lattices.
14
Best SVP algorithms known today: 2Θ(N). Approx c for some algorithms believed to take time 2(c+o(1))N: 0:415: 2008 Nguyen–Vidick. 0:415: 2010 Micciancio–Voulgaris. 0:384: 2011 Wang–Liu–Tian–Bi. 0:378: 2013 Zhang–Pan–Hu. 0:337: 2014 Laarhoven. 0:298: 2015 Laarhoven–de Weger. 0:292: 2015 Becker–Ducas– Gama–Laarhoven. Lattice crypto: more attack avenues; even less understanding. Agility, diversit “You think That’s crazy!

SLIDE 73 13
, famous lattice problem. “Lattices, SVP een intensively than 100 years, mathematical r applications in mathematics, cryptography.” rithms known
Θ(N log N) for
dimension-N lattices.
14
Best SVP algorithms known today: 2Θ(N). Approx c for some algorithms believed to take time 2(c+o(1))N: 0:415: 2008 Nguyen–Vidick. 0:415: 2010 Micciancio–Voulgaris. 0:384: 2011 Wang–Liu–Tian–Bi. 0:378: 2013 Zhang–Pan–Hu. 0:337: 2014 Laarhoven. 0:298: 2015 Laarhoven–de Weger. 0:292: 2015 Becker–Ducas– Gama–Laarhoven. Lattice crypto: more attack avenues; even less understanding. Agility, diversity, etc. “You think there can That’s crazy! We

SLIDE 74
13
attacks roblem. “Lattices, SVP nsively years, mathematical applications in mathematics, .” wn for lattices.
14
Best SVP algorithms known today: 2Θ(N). Approx c for some algorithms believed to take time 2(c+o(1))N: 0:415: 2008 Nguyen–Vidick. 0:415: 2010 Micciancio–Voulgaris. 0:384: 2011 Wang–Liu–Tian–Bi. 0:378: 2013 Zhang–Pan–Hu. 0:337: 2014 Laarhoven. 0:298: 2015 Laarhoven–de Weger. 0:292: 2015 Becker–Ducas– Gama–Laarhoven. Lattice crypto: more attack avenues; even less understanding. Agility, diversity, etc. “You think there can be only That’s crazy! We need backups!”

SLIDE 75
14
Best SVP algorithms known today: 2Θ(N). Approx c for some algorithms believed to take time 2(c+o(1))N: 0:415: 2008 Nguyen–Vidick. 0:415: 2010 Micciancio–Voulgaris. 0:384: 2011 Wang–Liu–Tian–Bi. 0:378: 2013 Zhang–Pan–Hu. 0:337: 2014 Laarhoven. 0:298: 2015 Laarhoven–de Weger. 0:292: 2015 Becker–Ducas– Gama–Laarhoven. Lattice crypto: more attack avenues; even less understanding.
15
Agility, diversity, etc. “You think there can be only one? That’s crazy! We need backups!”

SLIDE 76
14
Best SVP algorithms known today: 2Θ(N). Approx c for some algorithms believed to take time 2(c+o(1))N: 0:415: 2008 Nguyen–Vidick. 0:415: 2010 Micciancio–Voulgaris. 0:384: 2011 Wang–Liu–Tian–Bi. 0:378: 2013 Zhang–Pan–Hu. 0:337: 2014 Laarhoven. 0:298: 2015 Laarhoven–de Weger. 0:292: 2015 Becker–Ducas– Gama–Laarhoven. Lattice crypto: more attack avenues; even less understanding.
15
Agility, diversity, etc. “You think there can be only one? That’s crazy! We need backups!” McEliece has lower risk than lattice-based crypto. This doesn’t mean that McEliece has zero risk.

SLIDE 77
14
Best SVP algorithms known today: 2Θ(N). Approx c for some algorithms believed to take time 2(c+o(1))N: 0:415: 2008 Nguyen–Vidick. 0:415: 2010 Micciancio–Voulgaris. 0:384: 2011 Wang–Liu–Tian–Bi. 0:378: 2013 Zhang–Pan–Hu. 0:337: 2014 Laarhoven. 0:298: 2015 Laarhoven–de Weger. 0:292: 2015 Becker–Ducas– Gama–Laarhoven. Lattice crypto: more attack avenues; even less understanding.
15
Agility, diversity, etc. “You think there can be only one? That’s crazy! We need backups!” McEliece has lower risk than lattice-based crypto. This doesn’t mean that McEliece has zero risk. But there are also risks in standardizing more options: e.g., vulnerabilities are missed because cryptanalysts and implementors are spreading attention too thin.

SLIDE 78
14
Best SVP algorithms known today: 2Θ(N). Approx c for some algorithms believed to take time 2(c+o(1))N: 0:415: 2008 Nguyen–Vidick. 0:415: 2010 Micciancio–Voulgaris. 0:384: 2011 Wang–Liu–Tian–Bi. 0:378: 2013 Zhang–Pan–Hu. 0:337: 2014 Laarhoven. 0:298: 2015 Laarhoven–de Weger. 0:292: 2015 Becker–Ducas– Gama–Laarhoven. Lattice crypto: more attack avenues; even less understanding.
15
Agility, diversity, etc. “You think there can be only one? That’s crazy! We need backups!” McEliece has lower risk than lattice-based crypto. This doesn’t mean that McEliece has zero risk. But there are also risks in standardizing more options: e.g., vulnerabilities are missed because cryptanalysts and implementors are spreading attention too thin. OCB2 was published in 2004; standardized by ISO in 2009; complete break published in 2018.

SLIDE 79
14
SVP algorithms known 2Θ(N). x c for some algorithms elieved to take time 2(c+o(1))N: 2008 Nguyen–Vidick. 2010 Micciancio–Voulgaris. 2011 Wang–Liu–Tian–Bi. 2013 Zhang–Pan–Hu. 2014 Laarhoven. 2015 Laarhoven–de Weger. 2015 Becker–Ducas– Gama–Laarhoven. Lattice crypto: more attack avenues; even less understanding.
15
Agility, diversity, etc. “You think there can be only one? That’s crazy! We need backups!” McEliece has lower risk than lattice-based crypto. This doesn’t mean that McEliece has zero risk. But there are also risks in standardizing more options: e.g., vulnerabilities are missed because cryptanalysts and implementors are spreading attention too thin. OCB2 was published in 2004; standardized by ISO in 2009; complete break published in 2018. Integrity “You want That’s crazy! post-quantum

SLIDE 80
14
rithms known e algorithms time 2(c+o(1))N: Nguyen–Vidick. Micciancio–Voulgaris. ang–Liu–Tian–Bi. Zhang–Pan–Hu. rhoven. rhoven–de Weger. Becker–Ducas– Gama–Laarhoven. more attack less understanding.
15
Agility, diversity, etc. “You think there can be only one? That’s crazy! We need backups!” McEliece has lower risk than lattice-based crypto. This doesn’t mean that McEliece has zero risk. But there are also risks in standardizing more options: e.g., vulnerabilities are missed because cryptanalysts and implementors are spreading attention too thin. OCB2 was published in 2004; standardized by ISO in 2009; complete break published in 2018. Integrity “You want just encryption? That’s crazy! Obviously post-quantum signatures

SLIDE 81 14
wn rithms
k.
ang–Liu–Tian–Bi. an–Hu. Weger. er–Ducas– attack understanding.
15
Agility, diversity, etc. “You think there can be only one? That’s crazy! We need backups!” McEliece has lower risk than lattice-based crypto. This doesn’t mean that McEliece has zero risk. But there are also risks in standardizing more options: e.g., vulnerabilities are missed because cryptanalysts and implementors are spreading attention too thin. OCB2 was published in 2004; standardized by ISO in 2009; complete break published in 2018. Integrity “You want just encryption? That’s crazy! Obviously we post-quantum signatures too!”

SLIDE 82
15
Agility, diversity, etc. “You think there can be only one? That’s crazy! We need backups!” McEliece has lower risk than lattice-based crypto. This doesn’t mean that McEliece has zero risk. But there are also risks in standardizing more options: e.g., vulnerabilities are missed because cryptanalysts and implementors are spreading attention too thin. OCB2 was published in 2004; standardized by ISO in 2009; complete break published in 2018.
16
Integrity “You want just encryption? That’s crazy! Obviously we need post-quantum signatures too!”

SLIDE 83 15
Agility, diversity, etc. “You think there can be only one? That’s crazy! We need backups!” McEliece has lower risk than lattice-based crypto. This doesn’t mean that McEliece has zero risk. But there are also risks in standardizing more options: e.g., vulnerabilities are missed because cryptanalysts and implementors are spreading attention too thin. OCB2 was published in 2004; standardized by ISO in 2009; complete break published in 2018.
16
Integrity “You want just encryption? That’s crazy! Obviously we need post-quantum signatures too!” Example: Google’s NewHope experiment, modification of TLS.
- Server → client: E,
- ne-time NewHope public key.
- Client → server:
AES-GCM key encrypted to E.
- Server signs key exchange
under its long-term RSA key.

SLIDE 84 15
Agility, diversity, etc. “You think there can be only one? That’s crazy! We need backups!” McEliece has lower risk than lattice-based crypto. This doesn’t mean that McEliece has zero risk. But there are also risks in standardizing more options: e.g., vulnerabilities are missed because cryptanalysts and implementors are spreading attention too thin. OCB2 was published in 2004; standardized by ISO in 2009; complete break published in 2018.
16
Integrity “You want just encryption? That’s crazy! Obviously we need post-quantum signatures too!” Example: Google’s NewHope experiment, modification of TLS.
- Server → client: E,
- ne-time NewHope public key.
- Client → server:
AES-GCM key encrypted to E.
- Server signs key exchange
under its long-term RSA key. Must upgrade this protocol before attacker has quantum computer.

SLIDE 85 15
, diversity, etc. think there can be only one? crazy! We need backups!” McEliece has lower risk than lattice-based crypto. This doesn’t that McEliece has zero risk. there are also risks in rdizing more options: e.g., vulnerabilities are missed because cryptanalysts and implementors reading attention too thin. was published in 2004; rdized by ISO in 2009; complete break published in 2018.
16
Integrity “You want just encryption? That’s crazy! Obviously we need post-quantum signatures too!” Example: Google’s NewHope experiment, modification of TLS.
- Server → client: E,
- ne-time NewHope public key.
- Client → server:
AES-GCM key encrypted to E.
- Server signs key exchange
under its long-term RSA key. Must upgrade this protocol before attacker has quantum computer. More general Server signs server’s long-term Client verifies

SLIDE 86 15
etc. can be only one? e need backups!” er risk than
McEliece has zero risk. also risks in more options: e.g., re missed because and implementors attention too thin. published in 2004; ISO in 2009; published in 2018.
16
Integrity “You want just encryption? That’s crazy! Obviously we need post-quantum signatures too!” Example: Google’s NewHope experiment, modification of TLS.
- Server → client: E,
- ne-time NewHope public key.
- Client → server:
AES-GCM key encrypted to E.
- Server signs key exchange
under its long-term RSA key. Must upgrade this protocol before attacker has quantum computer. More general signature Server signs message server’s long-term Client verifies signature.

SLIDE 87 15
backups!” than doesn’t zero risk.
ecause implementors
2004; 2009; in 2018.
16
Integrity “You want just encryption? That’s crazy! Obviously we need post-quantum signatures too!” Example: Google’s NewHope experiment, modification of TLS.
- Server → client: E,
- ne-time NewHope public key.
- Client → server:
AES-GCM key encrypted to E.
- Server signs key exchange
under its long-term RSA key. Must upgrade this protocol before attacker has quantum computer. More general signature situation: Server signs message m under server’s long-term signature Client verifies signature.

SLIDE 88 16
Integrity “You want just encryption? That’s crazy! Obviously we need post-quantum signatures too!” Example: Google’s NewHope experiment, modification of TLS.
- Server → client: E,
- ne-time NewHope public key.
- Client → server:
AES-GCM key encrypted to E.
- Server signs key exchange
under its long-term RSA key. Must upgrade this protocol before attacker has quantum computer.
17
More general signature situation: Server signs message m under server’s long-term signature key. Client verifies signature.

SLIDE 89 16
Integrity “You want just encryption? That’s crazy! Obviously we need post-quantum signatures too!” Example: Google’s NewHope experiment, modification of TLS.
- Server → client: E,
- ne-time NewHope public key.
- Client → server:
AES-GCM key encrypted to E.
- Server signs key exchange
under its long-term RSA key. Must upgrade this protocol before attacker has quantum computer.
17
More general signature situation: Server signs message m under server’s long-term signature key. Client verifies signature. Can protect integrity of m without a signature system:
AES-GCM key k encrypted to server’s long-term encryption key.
message m encrypted under k. AES-GCM includes authentication so client knows m is from server.

SLIDE 90 16
Integrity want just encryption? crazy! Obviously we need
- st-quantum signatures too!”
Example: Google’s NewHope eriment, modification of TLS. Server → client: E,
- ne-time NewHope public key.
Client → server: AES-GCM key encrypted to E. Server signs key exchange under its long-term RSA key. upgrade this protocol before er has quantum computer.
17
More general signature situation: Server signs message m under server’s long-term signature key. Client verifies signature. Can protect integrity of m without a signature system:
AES-GCM key k encrypted to server’s long-term encryption key.
message m encrypted under k. AES-GCM includes authentication so client knows m is from server. Advantages Client kno

SLIDE 91 16
encryption? Obviously we need signatures too!”
dification of TLS. client: E, ewHope public key. server: encrypted to E. ey exchange long-term RSA key. this protocol before quantum computer.
17
More general signature situation: Server signs message m under server’s long-term signature key. Client verifies signature. Can protect integrity of m without a signature system:
AES-GCM key k encrypted to server’s long-term encryption key.
message m encrypted under k. AES-GCM includes authentication so client knows m is from server. Advantages of this Client knows m is

SLIDE 92 16
encryption? e need too!” NewHope
public key. encrypted to E. exchange key. col before computer.
17
More general signature situation: Server signs message m under server’s long-term signature key. Client verifies signature. Can protect integrity of m without a signature system:
AES-GCM key k encrypted to server’s long-term encryption key.
message m encrypted under k. AES-GCM includes authentication so client knows m is from server. Advantages of this approach: Client knows m is fresh.

SLIDE 93 17
More general signature situation: Server signs message m under server’s long-term signature key. Client verifies signature. Can protect integrity of m without a signature system:
AES-GCM key k encrypted to server’s long-term encryption key.
message m encrypted under k. AES-GCM includes authentication so client knows m is from server.
18
Advantages of this approach: Client knows m is fresh.

SLIDE 94 17
More general signature situation: Server signs message m under server’s long-term signature key. Client verifies signature. Can protect integrity of m without a signature system:
AES-GCM key k encrypted to server’s long-term encryption key.
message m encrypted under k. AES-GCM includes authentication so client knows m is from server.
18
Advantages of this approach: Client knows m is fresh. — Already guaranteed for TLS, since m has client randomness.

SLIDE 95 17
More general signature situation: Server signs message m under server’s long-term signature key. Client verifies signature. Can protect integrity of m without a signature system:
AES-GCM key k encrypted to server’s long-term encryption key.
message m encrypted under k. AES-GCM includes authentication so client knows m is from server.
18
Advantages of this approach: Client knows m is fresh. — Already guaranteed for TLS, since m has client randomness. Authenticates and encrypts. Don’t need 2nd encryption layer.

SLIDE 96 17
More general signature situation: Server signs message m under server’s long-term signature key. Client verifies signature. Can protect integrity of m without a signature system:
AES-GCM key k encrypted to server’s long-term encryption key.
message m encrypted under k. AES-GCM includes authentication so client knows m is from server.
18
Advantages of this approach: Client knows m is fresh. — Already guaranteed for TLS, since m has client randomness. Authenticates and encrypts. Don’t need 2nd encryption layer. — But “forward secrecy” needs an ephemeral encryption layer.

SLIDE 97 17
More general signature situation: Server signs message m under server’s long-term signature key. Client verifies signature. Can protect integrity of m without a signature system:
AES-GCM key k encrypted to server’s long-term encryption key.
message m encrypted under k. AES-GCM includes authentication so client knows m is from server.
18
Advantages of this approach: Client knows m is fresh. — Already guaranteed for TLS, since m has client randomness. Authenticates and encrypts. Don’t need 2nd encryption layer. — But “forward secrecy” needs an ephemeral encryption layer. Advantage of signatures: Signer can be offline.

SLIDE 98 17
More general signature situation: Server signs message m under server’s long-term signature key. Client verifies signature. Can protect integrity of m without a signature system:
AES-GCM key k encrypted to server’s long-term encryption key.
message m encrypted under k. AES-GCM includes authentication so client knows m is from server.
18
Advantages of this approach: Client knows m is fresh. — Already guaranteed for TLS, since m has client randomness. Authenticates and encrypts. Don’t need 2nd encryption layer. — But “forward secrecy” needs an ephemeral encryption layer. Advantage of signatures: Signer can be offline. — Designing for a disconnected future? Not relevant to TLS.

SLIDE 99
17
general signature situation: signs message m under server’s long-term signature key. verifies signature. rotect integrity of m without a signature system: Client → server: AES-GCM key k encrypted to server’s long-term encryption key. Server → client: message m encrypted under k. AES-GCM includes authentication client knows m is from server.
18
Advantages of this approach: Client knows m is fresh. — Already guaranteed for TLS, since m has client randomness. Authenticates and encrypts. Don’t need 2nd encryption layer. — But “forward secrecy” needs an ephemeral encryption layer. Advantage of signatures: Signer can be offline. — Designing for a disconnected future? Not relevant to TLS. Time Cycles on params 348864 460896 6688128 6960119 8192128 348864 460896 6688128 6960119 8192128

SLIDE 100 17
signature situation: message m under long-term signature key. signature. integrity of m signature system: server: k encrypted to long-term encryption key. client: encrypted under k. includes authentication m is from server.
18
Advantages of this approach: Client knows m is fresh. — Already guaranteed for TLS, since m has client randomness. Authenticates and encrypts. Don’t need 2nd encryption layer. — But “forward secrecy” needs an ephemeral encryption layer. Advantage of signatures: Signer can be offline. — Designing for a disconnected future? Not relevant to TLS. Time Cycles on Intel Hasw params
cycles 348864 enc 45888 460896 enc 82684 6688128 enc 153372 6960119 enc 154972 8192128 enc 183892 348864 dec 136840 460896 dec 273872 6688128 dec 320428 6960119 dec 302460 8192128 dec 324008

SLIDE 101 17
situation: under signature key. ystem: encrypted to encryption key. under k. authentication server.
18
Advantages of this approach: Client knows m is fresh. — Already guaranteed for TLS, since m has client randomness. Authenticates and encrypts. Don’t need 2nd encryption layer. — But “forward secrecy” needs an ephemeral encryption layer. Advantage of signatures: Signer can be offline. — Designing for a disconnected future? Not relevant to TLS. Time Cycles on Intel Haswell CPU params
cycles 348864 enc 45888 460896 enc 82684 6688128 enc 153372 6960119 enc 154972 8192128 enc 183892 348864 dec 136840 460896 dec 273872 6688128 dec 320428 6960119 dec 302460 8192128 dec 324008

SLIDE 102 18
Advantages of this approach: Client knows m is fresh. — Already guaranteed for TLS, since m has client randomness. Authenticates and encrypts. Don’t need 2nd encryption layer. — But “forward secrecy” needs an ephemeral encryption layer. Advantage of signatures: Signer can be offline. — Designing for a disconnected future? Not relevant to TLS.
19
Time Cycles on Intel Haswell CPU core: params
cycles 348864 enc 45888 460896 enc 82684 6688128 enc 153372 6960119 enc 154972 8192128 enc 183892 348864 dec 136840 460896 dec 273872 6688128 dec 320428 6960119 dec 302460 8192128 dec 324008

SLIDE 103 18
Advantages of this approach: knows m is fresh. Already guaranteed for TLS, has client randomness. Authenticates and encrypts. need 2nd encryption layer. But “forward secrecy” needs ephemeral encryption layer. Advantage of signatures: can be offline. Designing for a disconnected future? Not relevant to TLS.
19
Time Cycles on Intel Haswell CPU core: params
cycles 348864 enc 45888 460896 enc 82684 6688128 enc 153372 6960119 enc 154972 8192128 enc 183892 348864 dec 136840 460896 dec 273872 6688128 dec 320428 6960119 dec 302460 8192128 dec 324008 “Wait, y most imp to have such params 348864 348864f 460896 460896f 6688128 6688128f 6960119 6960119f 8192128 8192128f

SLIDE 104 18
this approach: is fresh. ranteed for TLS, client randomness. and encrypts. encryption layer. secrecy” needs encryption layer. ignatures:
a disconnected relevant to TLS.
19
Time Cycles on Intel Haswell CPU core: params
cycles 348864 enc 45888 460896 enc 82684 6688128 enc 153372 6960119 enc 154972 8192128 enc 183892 348864 dec 136840 460896 dec 273872 6688128 dec 320428 6960119 dec 302460 8192128 dec 324008 “Wait, you’re leaving most important cost! to have such slow params
348864 keygen 348864f keygen 460896 keygen 460896f keygen 6688128 keygen 6688128f keygen 6960119 keygen 6960119f keygen 8192128 keygen 8192128f keygen

SLIDE 105 18
roach: TLS, randomness. encrypts. layer. needs layer. disconnected TLS.
19
Time Cycles on Intel Haswell CPU core: params
cycles 348864 enc 45888 460896 enc 82684 6688128 enc 153372 6960119 enc 154972 8192128 enc 183892 348864 dec 136840 460896 dec 273872 6688128 dec 320428 6960119 dec 302460 8192128 dec 324008 “Wait, you’re leaving out the most important cost! It’s crazy to have such slow keygen!” params
cycles 348864 keygen 140870324 348864f keygen 82232360 460896 keygen 441517292 460896f keygen 282869316 6688128 keygen 1180468912 6688128f keygen 625470504 6960119 keygen 1109340668 6960119f keygen 564570384 8192128 keygen 933422948 8192128f keygen 678860388

SLIDE 106 19
Time Cycles on Intel Haswell CPU core: params
cycles 348864 enc 45888 460896 enc 82684 6688128 enc 153372 6960119 enc 154972 8192128 enc 183892 348864 dec 136840 460896 dec 273872 6688128 dec 320428 6960119 dec 302460 8192128 dec 324008
20
“Wait, you’re leaving out the most important cost! It’s crazy to have such slow keygen!” params
cycles 348864 keygen 140870324 348864f keygen 82232360 460896 keygen 441517292 460896f keygen 282869316 6688128 keygen 1180468912 6688128f keygen 625470504 6960119 keygen 1109340668 6960119f keygen 564570384 8192128 keygen 933422948 8192128f keygen 678860388

SLIDE 107 19
- n Intel Haswell CPU core:
rams
cycles enc 45888 enc 82684 6688128 enc 153372 6960119 enc 154972 8192128 enc 183892 dec 136840 dec 273872 6688128 dec 320428 6960119 dec 302460 8192128 dec 324008
20
“Wait, you’re leaving out the most important cost! It’s crazy to have such slow keygen!” params
cycles 348864 keygen 140870324 348864f keygen 82232360 460896 keygen 441517292 460896f keygen 282869316 6688128 keygen 1180468912 6688128f keygen 625470504 6960119 keygen 1109340668 6960119f keygen 564570384 8192128 keygen 933422948 8192128f keygen 678860388
that this a problem

SLIDE 108 19
Haswell CPU core: cycles 45888 82684 153372 154972 183892 136840 273872 320428 302460 324008
20
“Wait, you’re leaving out the most important cost! It’s crazy to have such slow keygen!” params
cycles 348864 keygen 140870324 348864f keygen 82232360 460896 keygen 441517292 460896f keygen 282869316 6688128 keygen 1180468912 6688128f keygen 625470504 6960119 keygen 1109340668 6960119f keygen 564570384 8192128 keygen 933422948 8192128f keygen 678860388
that this keygen time a problem for applications?

SLIDE 109 19
CPU core:
20
“Wait, you’re leaving out the most important cost! It’s crazy to have such slow keygen!” params
cycles 348864 keygen 140870324 348864f keygen 82232360 460896 keygen 441517292 460896f keygen 282869316 6688128 keygen 1180468912 6688128f keygen 625470504 6960119 keygen 1109340668 6960119f keygen 564570384 8192128 keygen 933422948 8192128f keygen 678860388
- 1. What evidence do we have
that this keygen time is a problem for applications?

SLIDE 110 20
“Wait, you’re leaving out the most important cost! It’s crazy to have such slow keygen!” params
cycles 348864 keygen 140870324 348864f keygen 82232360 460896 keygen 441517292 460896f keygen 282869316 6688128 keygen 1180468912 6688128f keygen 625470504 6960119 keygen 1109340668 6960119f keygen 564570384 8192128 keygen 933422948 8192128f keygen 678860388
21
- 1. What evidence do we have
that this keygen time is a problem for applications?

SLIDE 111 20
“Wait, you’re leaving out the most important cost! It’s crazy to have such slow keygen!” params
cycles 348864 keygen 140870324 348864f keygen 82232360 460896 keygen 441517292 460896f keygen 282869316 6688128 keygen 1180468912 6688128f keygen 625470504 6960119 keygen 1109340668 6960119f keygen 564570384 8192128 keygen 933422948 8192128f keygen 678860388
21
- 1. What evidence do we have
that this keygen time is a problem for applications?
- 2. Classic McEliece is designed
for IND-CCA2 security, so a key can be generated once and used a huge number of times.

SLIDE 112 20
“Wait, you’re leaving out the most important cost! It’s crazy to have such slow keygen!” params
cycles 348864 keygen 140870324 348864f keygen 82232360 460896 keygen 441517292 460896f keygen 282869316 6688128 keygen 1180468912 6688128f keygen 625470504 6960119 keygen 1109340668 6960119f keygen 564570384 8192128 keygen 933422948 8192128f keygen 678860388
21
- 1. What evidence do we have
that this keygen time is a problem for applications?
- 2. Classic McEliece is designed
for IND-CCA2 security, so a key can be generated once and used a huge number of times.
- 3. McEliece’s binary operations
are very well suited for hardware. See 2018 Wang–Szefer–
- Niederhagen. Isn’t this what’s
most important for the future?

SLIDE 113 20
ait, you’re leaving out the important cost! It’s crazy have such slow keygen!” rams
cycles keygen 140870324 348864f keygen 82232360 keygen 441517292 460896f keygen 282869316 6688128 keygen 1180468912 6688128f keygen 625470504 6960119 keygen 1109340668 6960119f keygen 564570384 8192128 keygen 933422948 8192128f keygen 678860388
21
- 1. What evidence do we have
that this keygen time is a problem for applications?
- 2. Classic McEliece is designed
for IND-CCA2 security, so a key can be generated once and used a huge number of times.
- 3. McEliece’s binary operations
are very well suited for hardware. See 2018 Wang–Szefer–
- Niederhagen. Isn’t this what’s
most important for the future? Bytes com params 348864 460896 6688128 6960119 8192128 348864 460896 6688128 6960119 8192128 “It’s crazy

SLIDE 114 20
leaving out the cost! It’s crazy w keygen!” cycles keygen 140870324 keygen 82232360 keygen 441517292 keygen 282869316 keygen 1180468912 keygen 625470504 keygen 1109340668 keygen 564570384 keygen 933422948 keygen 678860388
21
- 1. What evidence do we have
that this keygen time is a problem for applications?
- 2. Classic McEliece is designed
for IND-CCA2 security, so a key can be generated once and used a huge number of times.
- 3. McEliece’s binary operations
are very well suited for hardware. See 2018 Wang–Szefer–
- Niederhagen. Isn’t this what’s
most important for the future? Bytes communicat params
348864 ciphertext 460896 ciphertext 6688128 ciphertext 6960119 ciphertext 8192128 ciphertext 348864 key 460896 key 6688128 key 6960119 key 8192128 key “It’s crazy to have

SLIDE 115 20
the crazy eygen!” cycles 140870324 82232360 441517292 282869316 1180468912 625470504 1109340668 564570384 933422948 678860388
21
- 1. What evidence do we have
that this keygen time is a problem for applications?
- 2. Classic McEliece is designed
for IND-CCA2 security, so a key can be generated once and used a huge number of times.
- 3. McEliece’s binary operations
are very well suited for hardware. See 2018 Wang–Szefer–
- Niederhagen. Isn’t this what’s
most important for the future? Bytes communicated params
bytes 348864 ciphertext 128 460896 ciphertext 188 6688128 ciphertext 240 6960119 ciphertext 226 8192128 ciphertext 240 348864 key 261120 460896 key 524160 6688128 key 1044992 6960119 key 1047319 8192128 key 1357824 “It’s crazy to have big keys!”

SLIDE 116 21
- 1. What evidence do we have
that this keygen time is a problem for applications?
- 2. Classic McEliece is designed
for IND-CCA2 security, so a key can be generated once and used a huge number of times.
- 3. McEliece’s binary operations
are very well suited for hardware. See 2018 Wang–Szefer–
- Niederhagen. Isn’t this what’s
most important for the future?
22
Bytes communicated params
bytes 348864 ciphertext 128 460896 ciphertext 188 6688128 ciphertext 240 6960119 ciphertext 226 8192128 ciphertext 240 348864 key 261120 460896 key 524160 6688128 key 1044992 6960119 key 1047319 8192128 key 1357824 “It’s crazy to have big keys!”

SLIDE 117 21
What evidence do we have this keygen time is roblem for applications? Classic McEliece is designed D-CCA2 security, so can be generated once and huge number of times. McEliece’s binary operations very well suited for hardware. 2018 Wang–Szefer–
- Niederhagen. Isn’t this what’s
important for the future?
22
Bytes communicated params
bytes 348864 ciphertext 128 460896 ciphertext 188 6688128 ciphertext 240 6960119 ciphertext 226 8192128 ciphertext 240 348864 key 261120 460896 key 524160 6688128 key 1044992 6960119 key 1047319 8192128 key 1357824 “It’s crazy to have big keys!” What evidence that these a problem

SLIDE 118 21
evidence do we have time is applications? McEliece is designed security, so generated once and number of times. inary operations suited for hardware. ang–Szefer– Isn’t this what’s for the future?
22
Bytes communicated params
bytes 348864 ciphertext 128 460896 ciphertext 188 6688128 ciphertext 240 6960119 ciphertext 226 8192128 ciphertext 240 348864 key 261120 460896 key 524160 6688128 key 1044992 6960119 key 1047319 8192128 key 1357824 “It’s crazy to have big keys!” What evidence do that these key sizes a problem for applications?

SLIDE 119 21
ave applications? designed
times. erations rdware. what’s future?
22
Bytes communicated params
bytes 348864 ciphertext 128 460896 ciphertext 188 6688128 ciphertext 240 6960119 ciphertext 226 8192128 ciphertext 240 348864 key 261120 460896 key 524160 6688128 key 1044992 6960119 key 1047319 8192128 key 1357824 “It’s crazy to have big keys!” What evidence do we have that these key sizes are a problem for applications?

SLIDE 120 22
Bytes communicated params
bytes 348864 ciphertext 128 460896 ciphertext 188 6688128 ciphertext 240 6960119 ciphertext 226 8192128 ciphertext 240 348864 key 261120 460896 key 524160 6688128 key 1044992 6960119 key 1047319 8192128 key 1357824 “It’s crazy to have big keys!”
23
What evidence do we have that these key sizes are a problem for applications?

SLIDE 121 22
Bytes communicated params
bytes 348864 ciphertext 128 460896 ciphertext 188 6688128 ciphertext 240 6960119 ciphertext 226 8192128 ciphertext 240 348864 key 261120 460896 key 524160 6688128 key 1044992 6960119 key 1047319 8192128 key 1357824 “It’s crazy to have big keys!”
23
What evidence do we have that these key sizes are a problem for applications? Compare to, e.g., web-page size. httparchive.org statistics: 50% of web pages are >1.8MB. 25% of web pages are >3.5MB. 10% of web pages are >6.5MB. The sizes keep growing. Typically browser receives one web page from multiple servers, but reuses servers for more pages. Is key size a big part of this?

SLIDE 122 22
communicated rams
bytes ciphertext 128 ciphertext 188 6688128 ciphertext 240 6960119 ciphertext 226 8192128 ciphertext 240 key 261120 key 524160 6688128 key 1044992 6960119 key 1047319 8192128 key 1357824 crazy to have big keys!”
23
What evidence do we have that these key sizes are a problem for applications? Compare to, e.g., web-page size. httparchive.org statistics: 50% of web pages are >1.8MB. 25% of web pages are >3.5MB. 10% of web pages are >6.5MB. The sizes keep growing. Typically browser receives one web page from multiple servers, but reuses servers for more pages. Is key size a big part of this? 2015 McGrew postquantum Use standa techniques etc.) to reduce communicating Each ciphertext the way the server, can often much faster Again IND-CCA2

SLIDE 123
22
ated bytes ciphertext 128 ciphertext 188 ciphertext 240 ciphertext 226 ciphertext 240 261120 524160 1044992 1047319 1357824 have big keys!”
23
What evidence do we have that these key sizes are a problem for applications? Compare to, e.g., web-page size. httparchive.org statistics: 50% of web pages are >1.8MB. 25% of web pages are >3.5MB. 10% of web pages are >6.5MB. The sizes keep growing. Typically browser receives one web page from multiple servers, but reuses servers for more pages. Is key size a big part of this? 2015 McGrew “Living postquantum cryptography”: Use standard netw techniques (multicasts, etc.) to reduce cost communicating public Each ciphertext has the way between the the server, but public can often be retrieved much faster local net Again IND-CCA2 is

SLIDE 124
22
ytes 128 188 240 226 240 261120 524160 1044992 1047319 1357824 eys!”
23
What evidence do we have that these key sizes are a problem for applications? Compare to, e.g., web-page size. httparchive.org statistics: 50% of web pages are >1.8MB. 25% of web pages are >3.5MB. 10% of web pages are >6.5MB. The sizes keep growing. Typically browser receives one web page from multiple servers, but reuses servers for more pages. Is key size a big part of this? 2015 McGrew “Living with postquantum cryptography”: Use standard networking techniques (multicasts, caching, etc.) to reduce cost of communicating public keys. Each ciphertext has to travel the way between the client and the server, but public keys can often be retrieved through much faster local network. Again IND-CCA2 is critical.

SLIDE 125
23
What evidence do we have that these key sizes are a problem for applications? Compare to, e.g., web-page size. httparchive.org statistics: 50% of web pages are >1.8MB. 25% of web pages are >3.5MB. 10% of web pages are >6.5MB. The sizes keep growing. Typically browser receives one web page from multiple servers, but reuses servers for more pages. Is key size a big part of this?
24
2015 McGrew “Living with postquantum cryptography”: Use standard networking techniques (multicasts, caching, etc.) to reduce cost of communicating public keys. Each ciphertext has to travel all the way between the client and the server, but public keys can often be retrieved through much faster local network. Again IND-CCA2 is critical.

SLIDE 126 23
evidence do we have these key sizes are roblem for applications? Compare to, e.g., web-page size. httparchive.org statistics:
- f web pages are >1.8MB.
- f web pages are >3.5MB.
- f web pages are >6.5MB.
sizes keep growing. ypically browser receives one web from multiple servers, but servers for more pages. size a big part of this?
24
2015 McGrew “Living with postquantum cryptography”: Use standard networking techniques (multicasts, caching, etc.) to reduce cost of communicating public keys. Each ciphertext has to travel all the way between the client and the server, but public keys can often be retrieved through much faster local network. Again IND-CCA2 is critical. Denial of Standard strategy:
up all memo for keeping SYN floo Server is some con connections

SLIDE 127 23
do we have sizes are applications? e.g., web-page size. httparchive.org statistics: pages are >1.8MB. pages are >3.5MB. pages are >6.5MB. growing. wser receives one web multiple servers, but r more pages. part of this?
24
2015 McGrew “Living with postquantum cryptography”: Use standard networking techniques (multicasts, caching, etc.) to reduce cost of communicating public keys. Each ciphertext has to travel all the way between the client and the server, but public keys can often be retrieved through much faster local network. Again IND-CCA2 is critical. Denial of service Standard low-cost strategy: make a huge
up all memory available for keeping track of SYN flood, HTTP Server is forced to some connections, connections from honest

SLIDE 128 23
applications? eb-page size. statistics: 1.8MB. 3.5MB. 6.5MB.
servers, but pages. this?
24
2015 McGrew “Living with postquantum cryptography”: Use standard networking techniques (multicasts, caching, etc.) to reduce cost of communicating public keys. Each ciphertext has to travel all the way between the client and the server, but public keys can often be retrieved through much faster local network. Again IND-CCA2 is critical. Denial of service Standard low-cost attack strategy: make a huge numb
- f connections to a server, filling
up all memory available on server for keeping track of connections. SYN flood, HTTP flood, etc. Server is forced to stop serving some connections, including connections from honest clients.

SLIDE 129 24
2015 McGrew “Living with postquantum cryptography”: Use standard networking techniques (multicasts, caching, etc.) to reduce cost of communicating public keys. Each ciphertext has to travel all the way between the client and the server, but public keys can often be retrieved through much faster local network. Again IND-CCA2 is critical.
25
Denial of service Standard low-cost attack strategy: make a huge number
- f connections to a server, filling
up all memory available on server for keeping track of connections. SYN flood, HTTP flood, etc. Server is forced to stop serving some connections, including connections from honest clients.

SLIDE 130 24
2015 McGrew “Living with postquantum cryptography”: Use standard networking techniques (multicasts, caching, etc.) to reduce cost of communicating public keys. Each ciphertext has to travel all the way between the client and the server, but public keys can often be retrieved through much faster local network. Again IND-CCA2 is critical.
25
Denial of service Standard low-cost attack strategy: make a huge number
- f connections to a server, filling
up all memory available on server for keeping track of connections. SYN flood, HTTP flood, etc. Server is forced to stop serving some connections, including connections from honest clients. But some Internet protocols are not vulnerable to this attack.

SLIDE 131 24
McGrew “Living with
standard networking techniques (multicasts, caching, to reduce cost of communicating public keys. ciphertext has to travel all y between the client and server, but public keys
- ften be retrieved through
faster local network. IND-CCA2 is critical.
25
Denial of service Standard low-cost attack strategy: make a huge number
- f connections to a server, filling
up all memory available on server for keeping track of connections. SYN flood, HTTP flood, etc. Server is forced to stop serving some connections, including connections from honest clients. But some Internet protocols are not vulnerable to this attack. A tiny net handles and each incoming without

SLIDE 132 24
“Living with cryptography”: networking (multicasts, caching, cost of public keys. has to travel all the client and public keys retrieved through cal network. IND-CCA2 is critical.
25
Denial of service Standard low-cost attack strategy: make a huge number
- f connections to a server, filling
up all memory available on server for keeping track of connections. SYN flood, HTTP flood, etc. Server is forced to stop serving some connections, including connections from honest clients. But some Internet protocols are not vulnerable to this attack. A tiny network server handles and immediately each incoming netw without allocating

SLIDE 133 24
with cryptography”: caching, eys. travel all client and through rk. critical.
25
Denial of service Standard low-cost attack strategy: make a huge number
- f connections to a server, filling
up all memory available on server for keeping track of connections. SYN flood, HTTP flood, etc. Server is forced to stop serving some connections, including connections from honest clients. But some Internet protocols are not vulnerable to this attack. A tiny network server handles and immediately forgets each incoming network pack without allocating any memo

SLIDE 134 25
Denial of service Standard low-cost attack strategy: make a huge number
- f connections to a server, filling
up all memory available on server for keeping track of connections. SYN flood, HTTP flood, etc. Server is forced to stop serving some connections, including connections from honest clients. But some Internet protocols are not vulnerable to this attack.
26
A tiny network server handles and immediately forgets each incoming network packet, without allocating any memory.

SLIDE 135 25
Denial of service Standard low-cost attack strategy: make a huge number
- f connections to a server, filling
up all memory available on server for keeping track of connections. SYN flood, HTTP flood, etc. Server is forced to stop serving some connections, including connections from honest clients. But some Internet protocols are not vulnerable to this attack.
26
A tiny network server handles and immediately forgets each incoming network packet, without allocating any memory. Can use tiny network servers to publish information. Unauthenticated example from last century: “anonymous NFS”.

SLIDE 136 25
Denial of service Standard low-cost attack strategy: make a huge number
- f connections to a server, filling
up all memory available on server for keeping track of connections. SYN flood, HTTP flood, etc. Server is forced to stop serving some connections, including connections from honest clients. But some Internet protocols are not vulnerable to this attack.
26
A tiny network server handles and immediately forgets each incoming network packet, without allocating any memory. Can use tiny network servers to publish information. Unauthenticated example from last century: “anonymous NFS”. 1997 Aura–Nikander, 2005 Shieh– Myers–Sirer modify any protocol to use a tiny network server if an “input continuation” fits into a network packet.

SLIDE 137 25
Standard low-cost attack strategy: make a huge number connections to a server, filling memory available on server eeping track of connections. flood, HTTP flood, etc. is forced to stop serving connections, including connections from honest clients. some Internet protocols not vulnerable to this attack.
26
A tiny network server handles and immediately forgets each incoming network packet, without allocating any memory. Can use tiny network servers to publish information. Unauthenticated example from last century: “anonymous NFS”. 1997 Aura–Nikander, 2005 Shieh– Myers–Sirer modify any protocol to use a tiny network server if an “input continuation” fits into a network packet. “Here’s a McEliece

SLIDE 138 25
w-cost attack a huge number to a server, filling available on server
HTTP flood, etc. to stop serving tions, including honest clients. Internet protocols vulnerable to this attack.
26
A tiny network server handles and immediately forgets each incoming network packet, without allocating any memory. Can use tiny network servers to publish information. Unauthenticated example from last century: “anonymous NFS”. 1997 Aura–Nikander, 2005 Shieh– Myers–Sirer modify any protocol to use a tiny network server if an “input continuation” fits into a network packet. “Here’s a natural scena McEliece can’t possibly

SLIDE 139
25
number server, filling server connections. etc. serving including clients. cols attack.
26
A tiny network server handles and immediately forgets each incoming network packet, without allocating any memory. Can use tiny network servers to publish information. Unauthenticated example from last century: “anonymous NFS”. 1997 Aura–Nikander, 2005 Shieh– Myers–Sirer modify any protocol to use a tiny network server if an “input continuation” fits into a network packet. “Here’s a natural scenario that McEliece can’t possibly handle:

SLIDE 140
26
A tiny network server handles and immediately forgets each incoming network packet, without allocating any memory. Can use tiny network servers to publish information. Unauthenticated example from last century: “anonymous NFS”. 1997 Aura–Nikander, 2005 Shieh– Myers–Sirer modify any protocol to use a tiny network server if an “input continuation” fits into a network packet.
27
“Here’s a natural scenario that McEliece can’t possibly handle:

SLIDE 141 26
A tiny network server handles and immediately forgets each incoming network packet, without allocating any memory. Can use tiny network servers to publish information. Unauthenticated example from last century: “anonymous NFS”. 1997 Aura–Nikander, 2005 Shieh– Myers–Sirer modify any protocol to use a tiny network server if an “input continuation” fits into a network packet.
27
“Here’s a natural scenario that McEliece can’t possibly handle:
I want a tiny network server.

SLIDE 142 26
A tiny network server handles and immediately forgets each incoming network packet, without allocating any memory. Can use tiny network servers to publish information. Unauthenticated example from last century: “anonymous NFS”. 1997 Aura–Nikander, 2005 Shieh– Myers–Sirer modify any protocol to use a tiny network server if an “input continuation” fits into a network packet.
27
“Here’s a natural scenario that McEliece can’t possibly handle:
I want a tiny network server.
I want the server to encrypt a session key to an ephemeral public key sent by the client.

SLIDE 143 26
A tiny network server handles and immediately forgets each incoming network packet, without allocating any memory. Can use tiny network servers to publish information. Unauthenticated example from last century: “anonymous NFS”. 1997 Aura–Nikander, 2005 Shieh– Myers–Sirer modify any protocol to use a tiny network server if an “input continuation” fits into a network packet.
27
“Here’s a natural scenario that McEliece can’t possibly handle:
I want a tiny network server.
I want the server to encrypt a session key to an ephemeral public key sent by the client.
- This forces the public key
to fit into a network packet. Is that 1500 bytes? Or 1280? Either way, your key is too big.

SLIDE 144 26
A tiny network server handles and immediately forgets each incoming network packet, without allocating any memory. Can use tiny network servers to publish information. Unauthenticated example from last century: “anonymous NFS”. 1997 Aura–Nikander, 2005 Shieh– Myers–Sirer modify any protocol to use a tiny network server if an “input continuation” fits into a network packet.
27
“Here’s a natural scenario that McEliece can’t possibly handle:
I want a tiny network server.
I want the server to encrypt a session key to an ephemeral public key sent by the client.
- This forces the public key
to fit into a network packet. Is that 1500 bytes? Or 1280? Either way, your key is too big. It’s crazy if post-quantum standards can’t handle this!”

SLIDE 145 26
network server handles and immediately forgets incoming network packet, without allocating any memory. use tiny network servers publish information. Unauthenticated example from century: “anonymous NFS”. Aura–Nikander, 2005 Shieh– ers–Sirer modify any protocol a tiny network server “input continuation” into a network packet.
27
“Here’s a natural scenario that McEliece can’t possibly handle:
I want a tiny network server.
I want the server to encrypt a session key to an ephemeral public key sent by the client.
- This forces the public key
to fit into a network packet. Is that 1500 bytes? Or 1280? Either way, your key is too big. It’s crazy if post-quantum standards can’t handle this!” Bernstein–Lange handles this

SLIDE 146 26
server mediately forgets network packet, cating any memory. work servers rmation. example from “anonymous NFS”. ander, 2005 Shieh– dify any protocol work server tinuation” rk packet.
27
“Here’s a natural scenario that McEliece can’t possibly handle:
I want a tiny network server.
I want the server to encrypt a session key to an ephemeral public key sent by the client.
- This forces the public key
to fit into a network packet. Is that 1500 bytes? Or 1280? Either way, your key is too big. It’s crazy if post-quantum standards can’t handle this!” Bernstein–Lange “McTiny” handles this scenario.

SLIDE 147 26
forgets packet, memory. servers from NFS”. Shieh– rotocol server
27
“Here’s a natural scenario that McEliece can’t possibly handle:
I want a tiny network server.
I want the server to encrypt a session key to an ephemeral public key sent by the client.
- This forces the public key
to fit into a network packet. Is that 1500 bytes? Or 1280? Either way, your key is too big. It’s crazy if post-quantum standards can’t handle this!” Bernstein–Lange “McTiny” handles this scenario.

SLIDE 148 27
“Here’s a natural scenario that McEliece can’t possibly handle:
I want a tiny network server.
I want the server to encrypt a session key to an ephemeral public key sent by the client.
- This forces the public key
to fit into a network packet. Is that 1500 bytes? Or 1280? Either way, your key is too big. It’s crazy if post-quantum standards can’t handle this!”
28
Bernstein–Lange “McTiny” handles this scenario.

SLIDE 149 27
“Here’s a natural scenario that McEliece can’t possibly handle:
I want a tiny network server.
I want the server to encrypt a session key to an ephemeral public key sent by the client.
- This forces the public key
to fit into a network packet. Is that 1500 bytes? Or 1280? Either way, your key is too big. It’s crazy if post-quantum standards can’t handle this!”
28
Bernstein–Lange “McTiny” handles this scenario.
encrypts session key to server’s long-term McEliece public key. This establishes an encrypted authenticated session.

SLIDE 150 27
“Here’s a natural scenario that McEliece can’t possibly handle:
I want a tiny network server.
I want the server to encrypt a session key to an ephemeral public key sent by the client.
- This forces the public key
to fit into a network packet. Is that 1500 bytes? Or 1280? Either way, your key is too big. It’s crazy if post-quantum standards can’t handle this!”
28
Bernstein–Lange “McTiny” handles this scenario.
encrypts session key to server’s long-term McEliece public key. This establishes an encrypted authenticated session. Attacker who records this session and later steals server’s secret key can then decrypt everything. Remaining problem: within this session, encrypt to an ephemeral key for forward secrecy.

SLIDE 151 27
“Here’s a natural scenario that McEliece can’t possibly handle: stop memory floods, ant a tiny network server. forward secrecy, ant the server to encrypt a session key to an ephemeral public key sent by the client. forces the public key fit into a network packet. that 1500 bytes? Or 1280? Either way, your key is too big. crazy if post-quantum rds can’t handle this!”
28
Bernstein–Lange “McTiny” handles this scenario.
encrypts session key to server’s long-term McEliece public key. This establishes an encrypted authenticated session. Attacker who records this session and later steals server’s secret key can then decrypt everything. Remaining problem: within this session, encrypt to an ephemeral key for forward secrecy.
public ke B B @ K1;1 K2;1 . . . Kr;1 Each blo to fit into

SLIDE 152 27
natural scenario that
ry floods, network server. secrecy, server to encrypt a an ephemeral sent by the client. the public key network packet. ytes? Or 1280?
- ur key is too big.
- st-quantum
handle this!”
28
Bernstein–Lange “McTiny” handles this scenario.
encrypts session key to server’s long-term McEliece public key. This establishes an encrypted authenticated session. Attacker who records this session and later steals server’s secret key can then decrypt everything. Remaining problem: within this session, encrypt to an ephemeral key for forward secrecy.
public key K into blo B B @ K1;1 K1;2 K1 K2;1 K2;2 K2 . . . . . . . . . Kr;1 Kr;2 Kr Each block is small to fit into a network

SLIDE 153 27
that handle: server. encrypt a ephemeral client. ey packet. 1280? too big. this!”
28
Bernstein–Lange “McTiny” handles this scenario.
encrypts session key to server’s long-term McEliece public key. This establishes an encrypted authenticated session. Attacker who records this session and later steals server’s secret key can then decrypt everything. Remaining problem: within this session, encrypt to an ephemeral key for forward secrecy.
- 2. Client decomposes ephemeral
public key K into blocks: K B B @ K1;1 K1;2 K1;3 : : : K K2;1 K2;2 K2;3 : : : K . . . . . . . . . ... Kr;1 Kr;2 Kr;3 : : : K Each block is small enough to fit into a network packet.

SLIDE 154 28
Bernstein–Lange “McTiny” handles this scenario.
encrypts session key to server’s long-term McEliece public key. This establishes an encrypted authenticated session. Attacker who records this session and later steals server’s secret key can then decrypt everything. Remaining problem: within this session, encrypt to an ephemeral key for forward secrecy.
29
- 2. Client decomposes ephemeral
public key K into blocks: K = B B @ K1;1 K1;2 K1;3 : : : K1;‘ K2;1 K2;2 K2;3 : : : K2;‘ . . . . . . . . . ... . . . Kr;1 Kr;2 Kr;3 : : : Kr;‘ 1 C C A : Each block is small enough to fit into a network packet.

SLIDE 155 28
Bernstein–Lange “McTiny” handles this scenario.
encrypts session key to server’s long-term McEliece public key. This establishes an encrypted authenticated session. Attacker who records this session and later steals server’s secret key can then decrypt everything. Remaining problem: within this session, encrypt to an ephemeral key for forward secrecy.
29
- 2. Client decomposes ephemeral
public key K into blocks: K = B B @ K1;1 K1;2 K1;3 : : : K1;‘ K2;1 K2;2 K2;3 : : : K2;‘ . . . . . . . . . ... . . . Kr;1 Kr;2 Kr;3 : : : Kr;‘ 1 C C A : Each block is small enough to fit into a network packet.
- 3. Client sends Ki;j to server.
Server sends back Ki;jej encrypted to a server cookie key. Server cookie key is not per-client. Key is erased after a few minutes.

SLIDE 156 28
Bernstein–Lange “McTiny” handles this scenario. The easy part: Client encrypts session key to server’s long-term McEliece public key. establishes an encrypted authenticated session. er who records this session later steals server’s secret key then decrypt everything. Remaining problem: this session, encrypt to an ephemeral key for forward secrecy.
29
- 2. Client decomposes ephemeral
public key K into blocks: K = B B @ K1;1 K1;2 K1;3 : : : K1;‘ K2;1 K2;2 K2;3 : : : K2;‘ . . . . . . . . . ... . . . Kr;1 Kr;2 Kr;3 : : : Kr;‘ 1 C C A : Each block is small enough to fit into a network packet.
- 3. Client sends Ki;j to server.
Server sends back Ki;jej encrypted to a server cookie key. Server cookie key is not per-client. Key is erased after a few minutes.
containing Server sends

SLIDE 157 28
“McTiny” scenario. rt: Client key to server’s McEliece public key. an encrypted session. records this session server’s secret key decrypt everything. lem: session, encrypt to an r forward secrecy.
29
- 2. Client decomposes ephemeral
public key K into blocks: K = B B @ K1;1 K1;2 K1;3 : : : K1;‘ K2;1 K2;2 K2;3 : : : K2;‘ . . . . . . . . . ... . . . Kr;1 Kr;2 Kr;3 : : : Kr;‘ 1 C C A : Each block is small enough to fit into a network packet.
- 3. Client sends Ki;j to server.
Server sends back Ki;jej encrypted to a server cookie key. Server cookie key is not per-client. Key is erased after a few minutes.
containing several Server sends back

SLIDE 158 28
“McTiny” server’s key. encrypted session secret key everything. encrypt to an secrecy.
29
- 2. Client decomposes ephemeral
public key K into blocks: K = B B @ K1;1 K1;2 K1;3 : : : K1;‘ K2;1 K2;2 K2;3 : : : K2;‘ . . . . . . . . . ... . . . Kr;1 Kr;2 Kr;3 : : : Kr;‘ 1 C C A : Each block is small enough to fit into a network packet.
- 3. Client sends Ki;j to server.
Server sends back Ki;jej encrypted to a server cookie key. Server cookie key is not per-client. Key is erased after a few minutes.
- 4. Client sends one packet
containing several Ki;jej. Server sends back combination.

SLIDE 159 29
- 2. Client decomposes ephemeral
public key K into blocks: K = B B @ K1;1 K1;2 K1;3 : : : K1;‘ K2;1 K2;2 K2;3 : : : K2;‘ . . . . . . . . . ... . . . Kr;1 Kr;2 Kr;3 : : : Kr;‘ 1 C C A : Each block is small enough to fit into a network packet.
- 3. Client sends Ki;j to server.
Server sends back Ki;jej encrypted to a server cookie key. Server cookie key is not per-client. Key is erased after a few minutes.
30
- 4. Client sends one packet
containing several Ki;jej. Server sends back combination.

SLIDE 160 29
- 2. Client decomposes ephemeral
public key K into blocks: K = B B @ K1;1 K1;2 K1;3 : : : K1;‘ K2;1 K2;2 K2;3 : : : K2;‘ . . . . . . . . . ... . . . Kr;1 Kr;2 Kr;3 : : : Kr;‘ 1 C C A : Each block is small enough to fit into a network packet.
- 3. Client sends Ki;j to server.
Server sends back Ki;jej encrypted to a server cookie key. Server cookie key is not per-client. Key is erased after a few minutes.
30
- 4. Client sends one packet
containing several Ki;jej. Server sends back combination.
- 5. Repeat to combine everything.

SLIDE 161 29
- 2. Client decomposes ephemeral
public key K into blocks: K = B B @ K1;1 K1;2 K1;3 : : : K1;‘ K2;1 K2;2 K2;3 : : : K2;‘ . . . . . . . . . ... . . . Kr;1 Kr;2 Kr;3 : : : Kr;‘ 1 C C A : Each block is small enough to fit into a network packet.
- 3. Client sends Ki;j to server.
Server sends back Ki;jej encrypted to a server cookie key. Server cookie key is not per-client. Key is erased after a few minutes.
30
- 4. Client sends one packet
containing several Ki;jej. Server sends back combination.
- 5. Repeat to combine everything.
- 6. Server sends final Ke
directly to client, encrypted by session key but not by cookie key.

SLIDE 162 29
- 2. Client decomposes ephemeral
public key K into blocks: K = B B @ K1;1 K1;2 K1;3 : : : K1;‘ K2;1 K2;2 K2;3 : : : K2;‘ . . . . . . . . . ... . . . Kr;1 Kr;2 Kr;3 : : : Kr;‘ 1 C C A : Each block is small enough to fit into a network packet.
- 3. Client sends Ki;j to server.
Server sends back Ki;jej encrypted to a server cookie key. Server cookie key is not per-client. Key is erased after a few minutes.
30
- 4. Client sends one packet
containing several Ki;jej. Server sends back combination.
- 5. Repeat to combine everything.
- 6. Server sends final Ke
directly to client, encrypted by session key but not by cookie key.
Forward secrecy: Once cookie key and secret key for K are erased, client and server cannot decrypt.