Lightweight S Stream C Cipher Scheme f for R Resource- - PowerPoint PPT Presentation
Lightweight S Stream C Cipher Scheme f for R Resource- Constrained I IoT D Devices WIMOB 2019 October 21st 23rd, 2019 Casa Convalescncia, Barcelona, Spain Authors: Hassan Noura, Raphal Couturier, CongDuc Pham and Ali Chehab
Lightweight S Stream C Cipher Scheme f for R Resource- Constrained I IoT D Devices WIMOB 2019 – October 21st – 23rd, 2019 Casa Convalescència, Barcelona, Spain Authors: Hassan Noura, Raphaël Couturier, CongDuc Pham and Ali Chehab Presented on October 22nd, 2019 by Prof. Congduc Pham Prof. Congduc Pham IoT – from idea to reality http://www.univ-pau.fr/~cpham Université de Pau, France
Deploying IoT in Africa [technology does not automatically or inevitably improve people's lives; creative solutions must be contextually grounded and designed in response to on-the-ground needs] From Bill & Melinda Gates foundation, Global Grand Challenges http://www.univ-pau.fr/~cpham Prof. Congduc Pham Needs, constraints, cost, design approach, control mechanism Challenge: Bridging the digital divide 2
IoT security ⊙ Introducing security/encryption can dramatically impact the IoT system performance ⊙ Higher computation ⊙ Additional delays ⊙ Higher energy consumption, thus decreasing lifetime ⊙ Innovative IoT systems can have larger amount of data to send ⊙ Image IoT devices 10-15kms http://www.univ-pau.fr/~cpham Prof. Congduc Pham 3
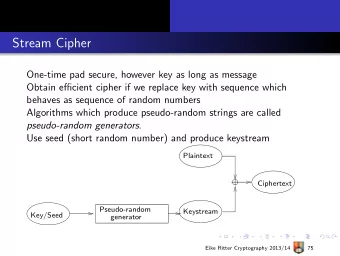
Symmetric cryptographic algorithms http://www.univ-pau.fr/~cpham Prof. Congduc Pham Requires a large number of rounds and operations such as AES (Advanced Encryption Standard) because round functions are usually static 4
Proposed approach ⊙ Lightweight Stream Cipher: dynamic key derivation function http://www.univ-pau.fr/~cpham Prof. Congduc Pham 5
Cipher scheme ⊙ LSC's Cipher scheme is divided into two sub-functions ⊙ RoundFunction ⊙ Update-RM Only once http://www.univ-pau.fr/~cpham Prof. Congduc Pham 6
LSC's main advantages ⊙ LSC is based on the dynamic key dependence approach and therefore can use only one iteration which requires less computation and resources ⊙ LSC also avoids chaining and diffusion operations to further reduce the computational complexity ⊙ LSC updates the cryptographic primitives after each encrypted/decrypted block to provide a higher security level ⊙ Minimum effect of error propagation as LSC encrypts 1 block at a time instead of 2 blocks http://www.univ-pau.fr/~cpham Prof. Congduc Pham ⊙ Overall, it can result in simpler implementation 7
Analysis ⊙ Security analysis ⊙ Randomness analysis ⊙ Key sensitivity ⊙ Message sensitivity ⊙ Performance analysis ⊙ Using low-end microcontroller: 8- 56° lens ucamII bit ATmega328P, 2K RAM, 8MHz CS Pin 1 Pin 1 ⊙ Using high-end micro-controller: SCK 3.3v TX CS RX MOSI MISO 32-bit Cortex-M4, 96K RAM, UART1 76° lens 48MHz http://www.univ-pau.fr/~cpham Prof. Congduc Pham ⊙ Comparison between SCK 3.3v GND RAW + ⊙ AES (multi-round) 116° lens ⊙ Speck (multi-round, light) ⊙ LSC (single-round, light) 8
Randomness analysis The encrypted message should reach a high level of randomness Two different tests can be applied to quantify the randomness level, which are : the correlation between the difference between the adjacent elements original and encrypted TestU01 practrand http://www.univ-pau.fr/~cpham Prof. Congduc Pham cipher scheme reaches the independence if and only if it satisfies Diff ≈ 50% 9
Key sensitivity ⊙ Difference in percentages between the encrypted messages, if one bit differs in the secret key (i.e. our dynamic key) ⊙ The desired value is 50% difference at the bit level. http://www.univ-pau.fr/~cpham Prof. Congduc Pham Counts of bit occurrence s in Y Nonce = ´ Key KS 100 % Length of Y in bit level 10
Message sensitivity ⊙ LSC uses a dynamic key approach which changes M C cipher primitives for each Cipher K input message Y ⊙ Identical messages will then M ' be encrypted under Cipher K different dynamic keys and C ' consequently different encrypted messages will be Counts of bit occurrence s in Y = ´ PS 100 % http://www.univ-pau.fr/~cpham Prof. Congduc Pham obtained (difference close Length of Y in bit level to 50%) 11
Performance LSC vs AES vs Speck on Arduino ProMini LSC vs AES & SPECK on Arduino Encryption time Encryption time ratio LSC AES SPECK AES-LSC ratio SPECK-LSC ratio 2496 4968 7464 9944 1214614912173921987222352248322730429784322803476037256 40000 Encryption time in us 1984 3944 5784 7616 9472 11312131761499216832186802054422384242162607227888 20 30000 9.45 10.53 10.60 10.72 10.47 10.84 10.82 10.85 10.96 10.97 10.94 10.89 10.93 10.97 10.98 20000 10 10000 8.36 8.25 8.25 8.23 8.23 8.22 8.21 8.17 8.22 8.19 8.18 8.18 8.20 8.22 7.52 0 928 1160 1376 1608 1832 2040 2264 2496 2736 2952 3168 3392 472 704 264 0 112 128 144 160 176 192 208 224 240 16 32 48 64 80 96 16 32 48 64 80 96 112 128 144 160 176 192 208 224 240 Message size in bytes Message size in bytes LSC vs AES vs Speck on Teensy32 LSC vs AES & SPECK on Teensy32 Encryption time Encryption time ratio LSC - 48MHz AES - 48MHz SPECK - 48MHz http://www.univ-pau.fr/~cpham AES-LSC ratio SPECK-LSC ratio 5000 Prof. Congduc Pham 857 1143 1427 1715 1998 2283 2568 2855 3139 3426 3709 3995 4282 Encryption time in us 4000 28.70 31.89 32.96 35.72 34.80 35.73 36.33 36.24 36.17 36.60 36.50 36.84 36.72 36.99 37.23 40 3000 20 2000 0.80 0.83 0.85 0.94 0.90 0.92 0.91 0.97 0.93 0.94 0.93 0.94 0.94 0.94 0.95 1000 574 287 0 86 93 101 108 115 26 32 41 48 55 63 71 78 10 18 0 66 73 80 87 95 101 109 8 15 22 30 37 44 50 61 16 32 48 64 80 96 112 128 144 160 176 192 208 224 240 16 32 48 64 80 96 112 128 144 160 176 192 208 224 240 Message size in bytes Message size in bytes 12
Conclusions ⊙ an efficient lightweight stream cipher scheme (LSC) was proposed for tiny IoT devices ⊙ existing standard ciphers are not adapted for these devices since a higher number of round iterations is required to reach the desired security level (because of static round function) ⊙ LSC is based on the dynamic key dependence approach to reach a good balance between security level and device’s performance ⊙ statistical tests and experimentations on real IoT hardware show http://www.univ-pau.fr/~cpham Prof. Congduc Pham that LSC is a promising candidate for resource-constrained IoT ⊙ outperforming traditional AES in terms of encryption/decryption time as well as the more recent Speck algorithm on low-end microcontrollers 13
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.