10 June, 2002 1
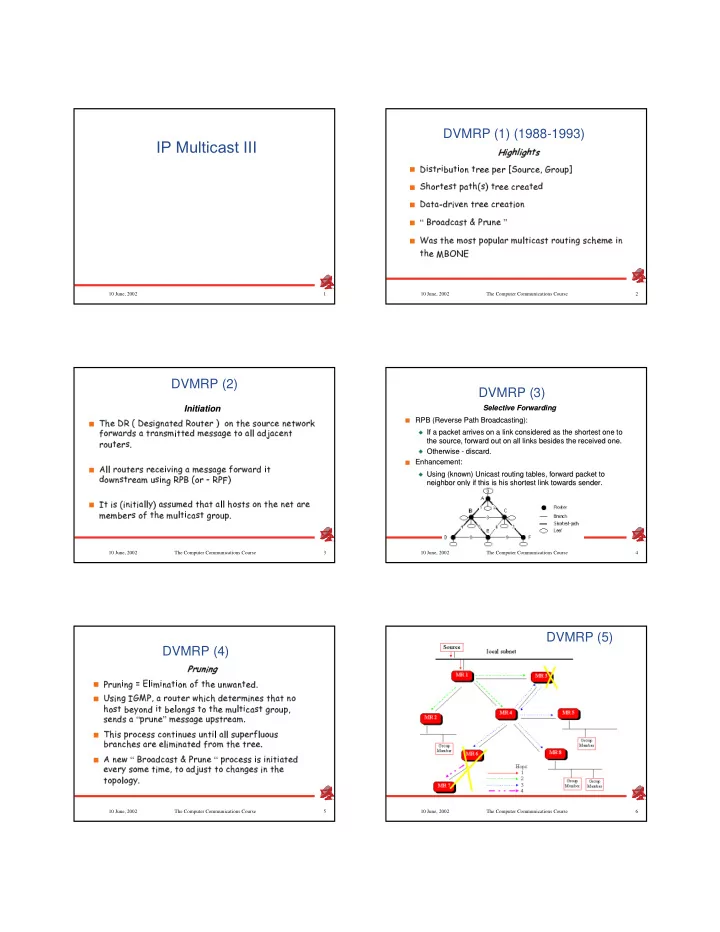
IP Multicast III
2 10 June, 2002 The Computer Communications Course
DVMRP (1) (1988-1993)
✂✁ ✄✆☎✞✝ ✁ ✄✆☎✠✟ ✡ ☛ ☞✍✌ ✎✑✏✓✒✓✌ ✔✖✕✓✏✗✌ ✘✖✙✚✏✓✒✜✛✢✛✤✣✗✛✞✒✦✥ ✧✆✘★✕★✒✪✩✓✛✬✫✗✭✍✒✪✘★✕✗✣✢✮ ☛ ✧✰✯✖✘★✒✪✏✱✛★✎✑✏✲✣✗✳✓✏✓✯✖✴ ✎✓✵✶✏✑✒✪✛✢✛✤✩★✒✪✛★✳✗✏✱✛✢✷ ☛ ☞✠✳✓✏✱✳★✸✹✷✬✒✓✌ ✺✑✛✻✙✚✏✓✒✜✛✢✛✤✩★✒✪✛★✳✗✏✗✌ ✘✖✙ ☛ ✼✲✽✬✒✪✘✗✳✓✷✬✩✓✳✓✎✑✏✂✾❀✿✢✒✪✕✢✙✑✛❂❁ ☛ ❃❄✳✗✎✚✏✓✯✢✛✤❅✚✘✗✎✑✏✚✣★✘★✣★✕✖❆ ✳★✒✂❅✚✕✞❆ ✏✗✌ ✩✓✳✓✎✑✏✦✒✪✘★✕✓✏✗✌ ✙✑❇❈✎✓✩★✯✢✛✢❅✂✛❉✌ ✙ ✏✓✯✢✛✤❊❋✽✬●✲❍✲■3 10 June, 2002 The Computer Communications Course
DVMRP (2)
Initiation Initiation
☛ ❏✰✯✢✛❉☞✰❑❉✴✍☞✠✛✢✎✗✌ ❇✞✙✱✳✗✏✱✛✢✷❉❑✬✘★✕✓✏✱✛✞✒✂✵▲✘✢✙✚✏✓✯✢✛❂✎✓✘★✕★✒✪✩✓✛▼✙✑✛✢✏✱◆✰✘★✒✑❖ P ✘★✒✪◆✆✳★✒✪✷✞✎✲✳✦✏✓✒✜✳✖✙✱✎✓❅✦✌ ✏✱✏✪✛✢✷❉❅✂✛✢✎✑✎✑✳✓❇★✛❂✏✑✘✦✳✞❆ ❆✓✳✗✷✢◗✜✳✗✩✓✛✻✙✑✏ ✒✱✘✗✕✓✏✱✛✞✒✪✎✗❘ ☛ ❙✂❆ ❆✢✒✪✘★✕✓✏✱✛✞✒✜✎❈✒✜✛✖✩✓✛✻✌ ✺★✌ ✙✑❇❈✳❈❅✂✛✢✎✑✎✑✳✓❇★✛ P ✘★✒✪◆✆✳✢✒✜✷❚✌ ✏ ✷✻✘✗◆❯✙✑✎✑✏✑✒✪✛✢✳✗❅❱✕✓✎★✌ ✙✑❇✤❑✬✿✢✽▼✴ ✘✢✒❲✸❲❑✬✿✢❳✖✵ ☛ ❨✢✏✦✌ ✎✲✴❩✌ ✙✗✌ ✏✗✌ ✳✞❆ ❆ ❬✖✵✶✳✓✎✑✎✓✕✗❅✂✛✢✷▼✏✓✯✢✳✓✏✂✳✞❆ ❆★✯✖✘✗✎✑✏✱✎✲✘✢✙✚✏✓✯✢✛▼✙✑✛★✏✚✳★✒✪✛ ❅✂✛✖❅✦✔★✛✞✒✪✎✲✘ P ✏✓✯★✛✤❅✚✕✞❆ ✏✗✌ ✩✓✳✓✎✑✏✚❇✖✒✪✘★✕✗✣✢❘4 10 June, 2002 The Computer Communications Course
DVMRP (3)
Selective Forwarding Selective Forwarding
❭ ❭RPB (Reverse Path Broadcasting): RPB (Reverse Path Broadcasting):
❪ ❪If a packet arrives on a link considered as the shortest one to If a packet arrives on a link considered as the shortest one to the source, forward out on all links besides the received one. the source, forward out on all links besides the received one.
❪ ❪Otherwise - discard. Otherwise - discard.
❭ ❭Enhancement: Enhancement:
❪ ❪Using (known) Unicast routing tables, forward packet to Using (known) Unicast routing tables, forward packet to neighbor only if this is his shortest link towards sender. neighbor only if this is his shortest link towards sender.
5 10 June, 2002 The Computer Communications Course
DVMRP (4)
❫✢❴✑❵✗❛★✁ ❛ ✄ ☛ ✿★✒✱✕✢✙★✌ ✙✱❇✤❜❈■✶❆ ✌ ❅✦✌ ✙✱✳✗✏✗✌ ✘✖✙✲✘ P ✏✓✯✢✛✤✕✢✙✑◆✆✳✢✙✑✏✱✛✢✷✬❘ ☛ ❝✆✎★✌ ✙✱❇❈❨✢✭✰❊▼✿✖✫✗✳❂✒✪✘★✕✓✏✱✛✞✒❲◆✍✯✻✌ ✩★✯❂✷✞✛✢✏✱✛✞✒✱❅✦✌ ✙✱✛✢✎✲✏✑✯✢✳✗✏✦✙✓✘ ✯✖✘✓✎✑✏❈✔★✛✗❬✖✘✖✙✱✷❚✌ ✏❈✔★✛✬❆ ✘✖✙✱❇★✎✚✏✑✘✦✏✓✯✢✛✤❅✚✕✖❆ ✏✗✌ ✩✓✳✓✎✑✏✂❇✖✒✱✘✗✕★✣✞✫ ✎✑✛✻✙✱✷✻✎✚✳✦✼✪✣✢✒✱✕✢✙✑✛★❁✂❅✂✛✢✎✑✎✑✳✓❇★✛✤✕★✣✗✎✑✏✓✒✜✛✢✳★❅✲❘ ☛ ❏✰✯✻✌ ✎✦✣✢✒✪✘★✩✓✛✢✎✱✎✦✩✗✘✢✙✑✏✗✌ ✙✓✕✓✛✢✎✲✕✢✙✑✏✗✌ ❆✓✳✞❆ ❆✓✎✓✕✗✣★✛✖✒ P ❆ ✕✗✘✗✕✗✎ ✔✞✒✜✳✖✙✑✩★✯✢✛✢✎✚✳✢✒✜✛❂✛✬❆ ✌ ❅✦✌ ✙✑✳✓✏✱✛✢✷ P ✒✱✘✗❅❞✏✓✯★✛❂✏✓✒✪✛✢✛✞❘ ☛ ❙❡✙✑✛✢◆❀✼✲✽✬✒✱✘✓✳✗✷✻✩✓✳✓✎✑✏✚✾❀✿★✒✪✕✖✙✱✛❂✼✂✣✢✒✱✘✗✩✓✛✢✎✑✎❈✌ ✎❈✌ ✙★✌ ✏✗✌ ✳✓✏✱✛✢✷ ✛✢✺✑✛✞✒✹❬✤✎✓✘✗❅✂✛❂✏✗✌ ❅✂✛✻✫✗✏✑✘✦✳✓✷✖◗✜✕✗✎✑✏✂✏✑✘❈✩★✯★✳✖✙✱❇★✛✢✎❈✌ ✙✚✏✓✯★✛ ✏✑✘✗✣✢✘✖❆ ✘✗❇✓❬✞❘6 10 June, 2002 The Computer Communications Course