1
7: Net wor k Secur it y 1
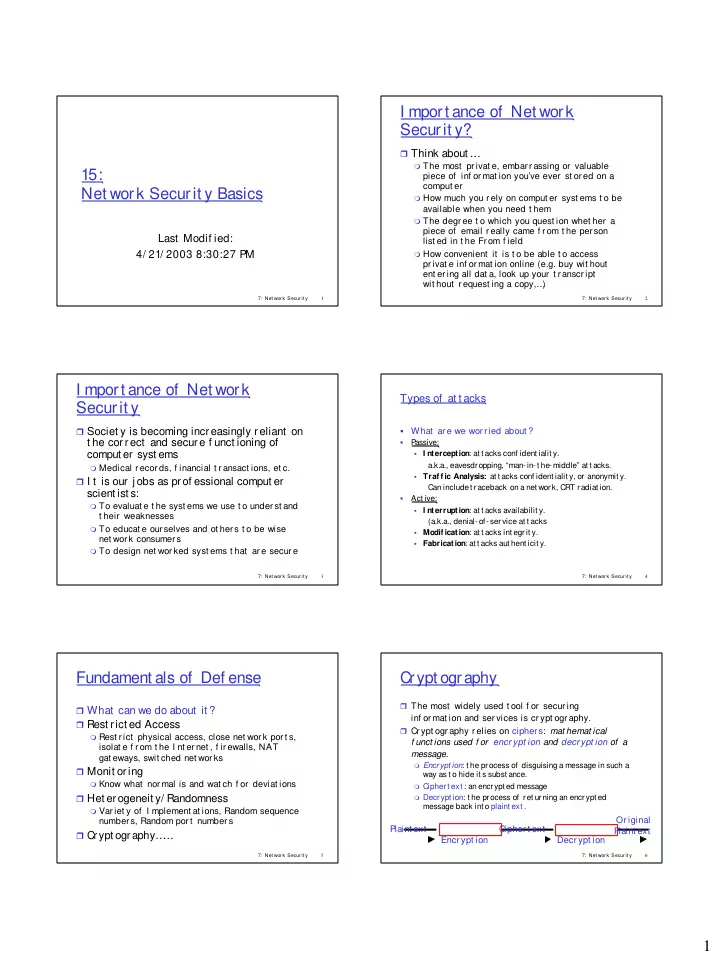
15: Net work Securit y Basics
Last Modif ied: 4/ 21/ 2003 8:30:27 PM
7: Net wor k Secur it y 2
I mport ance of Net work Securit y?
Think about …
The most pr ivat e, embar r assing or valuable
piece of inf or mat ion you’ve ever st or ed on a comput er
How much you r ely on comput er syst ems t o be
available when you need t hem
The degr ee t o which you quest ion whet her a
piece of email r eally came f r om t he per son list ed in t he Fr om f ield
How convenient it is t o be able t o access
pr ivat e inf or mat ion online (e.g. buy wit hout ent er ing all dat a, look up your t r anscr ipt wit hout r equest ing a copy,… )
7: Net wor k Secur it y 3
I mport ance of Net work Securit y
Societ y is becoming increasingly reliant on
t he correct and secure f unct ioning of comput er syst ems
Medical r ecor ds, f inancial t r ansact ions, et c.
I t is our j obs as prof essional comput er
scient ist s:
To evaluat e t he syst ems we use t o under st and
t heir weaknesses
To educat e our selves and ot her s t o be wise
net wor k consumer s
To design net wor ked syst ems t hat ar e secur e
7: Net wor k Secur it y 4
Types of at t acks
- What ar e we wor r ied about ?
- P
assive:
I nterception: at t acks conf ident ialit y.
a.k.a., eavesdropping, “man- in- t he- middle” at t acks.
Traf f ic Analysis: at t acks conf ident ialit y, or anonymit y.
Can includet raceback on a net work, CRT radiat ion.
- Act ive:
I nterruption: at t acks availabilit y.
(a.k.a., denial- of- service at t acks
Modif ication: at t acks int egrit y. Fabrication: at t acks aut hent icit y.
7: Net wor k Secur it y 5
Fundament als of Def ense
What can we do about it ? Rest rict ed Access
Rest r ict physical access, close net wor k por t s,
isolat e f r om t he I nt er net , f ir ewalls, NAT gat eways, swit ched net wor ks Monit or ing
Know what nor mal is and wat ch f or deviat ions
Het erogeneit y/ Randomness
Var iet y of I mplement at ions, Random sequence
number s, Random por t number s Crypt ography…
…
7: Net wor k Secur it y 6
The most widely used t ool f or secur ing
inf or mat ion and ser vices is cr ypt ogr aphy.
Cr ypt ogr aphy r elies on cipher s: mat hemat ical
f unct ions used f or encr ypt ion and decr ypt ion of a message.
Encrypt ion: t he process of disguising a message in such a
way as t o hide it s subst ance.
Ciphert ext : an encrypt ed message Decrypt ion: t he process of ret urning an encrypt ed