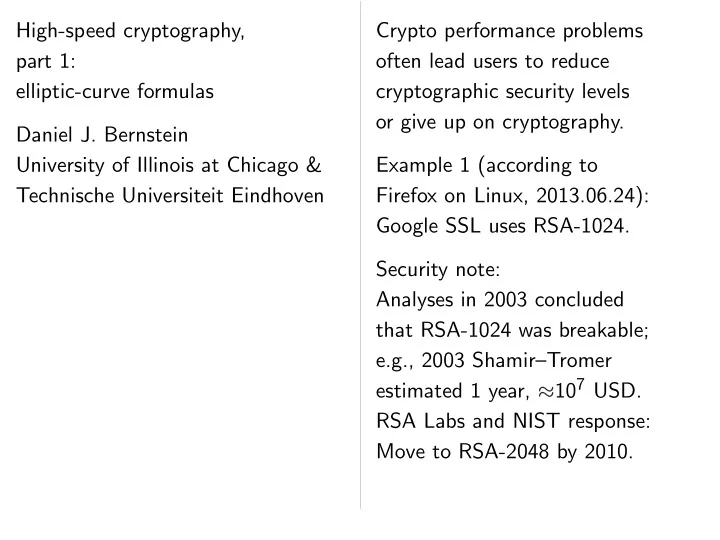
SLIDE 1 High-speed cryptography, part 1: elliptic-curve formulas Daniel J. Bernstein University of Illinois at Chicago & Technische Universiteit Eindhoven Crypto performance problems
- ften lead users to reduce
cryptographic security levels
- r give up on cryptography.
Example 1 (according to Firefox on Linux, 2013.06.24): Google SSL uses RSA-1024. Security note: Analyses in 2003 concluded that RSA-1024 was breakable; e.g., 2003 Shamir–Tromer estimated 1 year, ✙107 USD. RSA Labs and NIST response: Move to RSA-2048 by 2010.

SLIDE 2 High-speed cryptography, 1: elliptic-curve formulas
University of Illinois at Chicago & echnische Universiteit Eindhoven Crypto performance problems
- ften lead users to reduce
cryptographic security levels
- r give up on cryptography.
Example 1 (according to Firefox on Linux, 2013.06.24): Google SSL uses RSA-1024. Security note: Analyses in 2003 concluded that RSA-1024 was breakable; e.g., 2003 Shamir–Tromer estimated 1 year, ✙107 USD. RSA Labs and NIST response: Move to RSA-2048 by 2010. Example Example 1024: “tradeoff risk of key performance✿ ✿ ✿ Example AES load Example
https://sourceforge.net/account
is protected
https://sourceforge.net/develop
redirects
http://sourceforge.net/develop
turning off

SLIDE 3 cryptography, rmulas Bernstein Illinois at Chicago & Universiteit Eindhoven Crypto performance problems
- ften lead users to reduce
cryptographic security levels
- r give up on cryptography.
Example 1 (according to Firefox on Linux, 2013.06.24): Google SSL uses RSA-1024. Security note: Analyses in 2003 concluded that RSA-1024 was breakable; e.g., 2003 Shamir–Tromer estimated 1 year, ✙107 USD. RSA Labs and NIST response: Move to RSA-2048 by 2010. Example 2: Tor use Example 3: DNSSEC 1024: “tradeoff bet risk of key compromise performance✿ ✿ ✿ ” Example 4: OpenSSL AES load addresse Example 5:
https://sourceforge.net/account
is protected by SSL
https://sourceforge.net/develop
redirects browser to
http://sourceforge.net/develop
turning off the cryptography

SLIDE 4 Chicago & Eindhoven Crypto performance problems
- ften lead users to reduce
cryptographic security levels
- r give up on cryptography.
Example 1 (according to Firefox on Linux, 2013.06.24): Google SSL uses RSA-1024. Security note: Analyses in 2003 concluded that RSA-1024 was breakable; e.g., 2003 Shamir–Tromer estimated 1 year, ✙107 USD. RSA Labs and NIST response: Move to RSA-2048 by 2010. Example 2: Tor uses RSA-1024. Example 3: DNSSEC uses RSA- 1024: “tradeoff between the risk of key compromise and performance✿ ✿ ✿ ” Example 4: OpenSSL uses secret AES load addresses; dangerous! Example 5:
https://sourceforge.net/account
is protected by SSL but
https://sourceforge.net/develop
redirects browser to
http://sourceforge.net/develop
turning off the cryptography.

SLIDE 5 Crypto performance problems
- ften lead users to reduce
cryptographic security levels
- r give up on cryptography.
Example 1 (according to Firefox on Linux, 2013.06.24): Google SSL uses RSA-1024. Security note: Analyses in 2003 concluded that RSA-1024 was breakable; e.g., 2003 Shamir–Tromer estimated 1 year, ✙107 USD. RSA Labs and NIST response: Move to RSA-2048 by 2010. Example 2: Tor uses RSA-1024. Example 3: DNSSEC uses RSA- 1024: “tradeoff between the risk of key compromise and performance✿ ✿ ✿ ” Example 4: OpenSSL uses secret AES load addresses; dangerous! Example 5:
https://sourceforge.net/account
is protected by SSL but
https://sourceforge.net/develop
redirects browser to
http://sourceforge.net/develop,
turning off the cryptography.

SLIDE 6 performance problems lead users to reduce cryptographic security levels up on cryptography. Example 1 (according to
- n Linux, 2013.06.24):
- gle SSL uses RSA-1024.
Security note: Analyses in 2003 concluded RSA-1024 was breakable; 2003 Shamir–Tromer estimated 1 year, ✙107 USD. Labs and NIST response: to RSA-2048 by 2010. Example 2: Tor uses RSA-1024. Example 3: DNSSEC uses RSA- 1024: “tradeoff between the risk of key compromise and performance✿ ✿ ✿ ” Example 4: OpenSSL uses secret AES load addresses; dangerous! Example 5:
https://sourceforge.net/account
is protected by SSL but
https://sourceforge.net/develop
redirects browser to
http://sourceforge.net/develop,
turning off the cryptography. Extensive ✮ fast high-securit Example: 460200 Co 332304 Snap 182632 Ivy Requires and optimization Not just not just My topic decomposing

SLIDE 7 rmance problems to reduce security levels cryptography. rding to Linux, 2013.06.24): RSA-1024. concluded was breakable; Shamir–Tromer r, ✙107 USD. NIST response: RSA-2048 by 2010. Example 2: Tor uses RSA-1024. Example 3: DNSSEC uses RSA- 1024: “tradeoff between the risk of key compromise and performance✿ ✿ ✿ ” Example 4: OpenSSL uses secret AES load addresses; dangerous! Example 5:
https://sourceforge.net/account
is protected by SSL but
https://sourceforge.net/develop
redirects browser to
http://sourceforge.net/develop,
turning off the cryptography. Extensive work on ✮ fast high-securit Example: Curve25519 460200 Cortex A8 332304 Snapdragon 182632 Ivy Bridge Requires serious analysis and optimization of Not just “polynomial not just “quadratic My topic today: decomposing elliptic-curve

SLIDE 8 roblems levels cryptography. 2013.06.24): RSA-1024. concluded ble; ✙ USD.
2010. Example 2: Tor uses RSA-1024. Example 3: DNSSEC uses RSA- 1024: “tradeoff between the risk of key compromise and performance✿ ✿ ✿ ” Example 4: OpenSSL uses secret AES load addresses; dangerous! Example 5:
https://sourceforge.net/account
is protected by SSL but
https://sourceforge.net/develop
redirects browser to
http://sourceforge.net/develop,
turning off the cryptography. Extensive work on ECC speed ✮ fast high-security ECC. Example: Curve25519 ECDH 460200 Cortex A8 cycles; 332304 Snapdragon S4 cycles; 182632 Ivy Bridge cycles. Requires serious analysis and optimization of algorithms. Not just “polynomial time”; not just “quadratic time”. My topic today: decomposing elliptic-curve
- perations into field operations.

SLIDE 9 Example 2: Tor uses RSA-1024. Example 3: DNSSEC uses RSA- 1024: “tradeoff between the risk of key compromise and performance✿ ✿ ✿ ” Example 4: OpenSSL uses secret AES load addresses; dangerous! Example 5:
https://sourceforge.net/account
is protected by SSL but
https://sourceforge.net/develop
redirects browser to
http://sourceforge.net/develop,
turning off the cryptography. Extensive work on ECC speed ✮ fast high-security ECC. Example: Curve25519 ECDH in 460200 Cortex A8 cycles; 332304 Snapdragon S4 cycles; 182632 Ivy Bridge cycles. Requires serious analysis and optimization of algorithms. Not just “polynomial time”; not just “quadratic time”. My topic today: decomposing elliptic-curve
- perations into field operations.

SLIDE 10 Example 2: Tor uses RSA-1024. Example 3: DNSSEC uses RSA- “tradeoff between the key compromise and rmance✿ ✿ ✿ ” Example 4: OpenSSL uses secret load addresses; dangerous! Example 5:
https://sourceforge.net/account
rotected by SSL but
https://sourceforge.net/develop
redirects browser to
http://sourceforge.net/develop,
turning off the cryptography. Extensive work on ECC speed ✮ fast high-security ECC. Example: Curve25519 ECDH in 460200 Cortex A8 cycles; 332304 Snapdragon S4 cycles; 182632 Ivy Bridge cycles. Requires serious analysis and optimization of algorithms. Not just “polynomial time”; not just “quadratic time”. My topic today: decomposing elliptic-curve
- perations into field operations.
Eliminating Typical computation: P ✼✦ ♥P Decompose P❀ ◗ ✼✦ P ◗ Addition ① ❀ ② ① ❀ ② ((①1②2 + ② ① ❂ ❞① ① ② ② (②1②2 ① ① ❂ ❞① ① ② ② uses exp Better: p and work Represent ①❀ ② (❳ : ❨ : ❩ ① ❳❂❩ ② = ❨❂❩ ❩ ✻

SLIDE 11 uses RSA-1024. DNSSEC uses RSA- between the romise and ✿ ✿ ✿ enSSL uses secret ddresses; dangerous!
https://sourceforge.net/account
SSL but
https://sourceforge.net/develop
wser to
http://sourceforge.net/develop,
cryptography. Extensive work on ECC speed ✮ fast high-security ECC. Example: Curve25519 ECDH in 460200 Cortex A8 cycles; 332304 Snapdragon S4 cycles; 182632 Ivy Bridge cycles. Requires serious analysis and optimization of algorithms. Not just “polynomial time”; not just “quadratic time”. My topic today: decomposing elliptic-curve
- perations into field operations.
Eliminating divisions Typical computation: P ✼✦ ♥P. Decompose into addi P❀ ◗ ✼✦ P + ◗. Addition (①1❀ ②1) + ① ❀ ② ((①1②2 + ②1①2)❂(1 ❞① ① ② ② (②1②2 ①1①2)❂(1 ❞① ① ② ② uses expensive divisions. Better: postpone divisions and work with fractions. Represent (①❀ ②) as (❳ : ❨ : ❩) with ① ❳❂❩ ② = ❨❂❩ for ❩ ✻= 0.

SLIDE 12 RSA-1024. RSA- the and ✿ ✿ ✿ secret dangerous!
https://sourceforge.net/account https://sourceforge.net/develop http://sourceforge.net/develop,
cryptography. Extensive work on ECC speed ✮ fast high-security ECC. Example: Curve25519 ECDH in 460200 Cortex A8 cycles; 332304 Snapdragon S4 cycles; 182632 Ivy Bridge cycles. Requires serious analysis and optimization of algorithms. Not just “polynomial time”; not just “quadratic time”. My topic today: decomposing elliptic-curve
- perations into field operations.
Eliminating divisions Typical computation: P ✼✦ ♥P. Decompose into additions: P❀ ◗ ✼✦ P + ◗. Addition (①1❀ ②1) + (①2❀ ②2) ((①1②2 + ②1①2)❂(1 + ❞①1①2② ② (②1②2 ①1①2)❂(1 ❞①1①2② ② uses expensive divisions. Better: postpone divisions and work with fractions. Represent (①❀ ②) as (❳ : ❨ : ❩) with ① = ❳❂❩ ② = ❨❂❩ for ❩ ✻= 0.

SLIDE 13 Extensive work on ECC speed ✮ fast high-security ECC. Example: Curve25519 ECDH in 460200 Cortex A8 cycles; 332304 Snapdragon S4 cycles; 182632 Ivy Bridge cycles. Requires serious analysis and optimization of algorithms. Not just “polynomial time”; not just “quadratic time”. My topic today: decomposing elliptic-curve
- perations into field operations.
Eliminating divisions Typical computation: P ✼✦ ♥P. Decompose into additions: P❀ ◗ ✼✦ P + ◗. Addition (①1❀ ②1) + (①2❀ ②2) = ((①1②2 + ②1①2)❂(1 + ❞①1①2②1②2), (②1②2 ①1①2)❂(1 ❞①1①2②1②2)) uses expensive divisions. Better: postpone divisions and work with fractions. Represent (①❀ ②) as (❳ : ❨ : ❩) with ① = ❳❂❩ and ② = ❨❂❩ for ❩ ✻= 0.

SLIDE 14 Extensive work on ECC speed ✮ fast high-security ECC. Example: Curve25519 ECDH in 460200 Cortex A8 cycles; 332304 Snapdragon S4 cycles; 182632 Ivy Bridge cycles. Requires serious analysis
- ptimization of algorithms.
just “polynomial time”; just “quadratic time”. topic today: decomposing elliptic-curve erations into field operations. Eliminating divisions Typical computation: P ✼✦ ♥P. Decompose into additions: P❀ ◗ ✼✦ P + ◗. Addition (①1❀ ②1) + (①2❀ ②2) = ((①1②2 + ②1①2)❂(1 + ❞①1①2②1②2), (②1②2 ①1①2)❂(1 ❞①1①2②1②2)) uses expensive divisions. Better: postpone divisions and work with fractions. Represent (①❀ ②) as (❳ : ❨ : ❩) with ① = ❳❂❩ and ② = ❨❂❩ for ❩ ✻= 0. Addition handle fractions ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ ✒❳ ❩ ❀ ❨ ❩ ✓ ✥
❳1 ❩1 ❨2 ❩2 ❨ ❩ ❳ ❩
1 + ❞❳
❩ ❳ ❩ ❨ ❩ ❨ ❩ ❨1 ❩1 ❨2 ❩2 ❳ ❩ ❳ ❩
1 ❞❳
❩ ❳ ❩ ❨ ❩ ❨ ❩
✦ ✥ ❩1❩2(❳ ❨ ❨ ❳ ❩2
1❩2 2
❞❳ ❳ ❨ ❨ ❩1❩2(❨ ❨ ❳ ❳ ❩2
1❩2 2 ❞❳ ❳ ❨ ❨
✦

SLIDE 15
✮ high-security ECC. Curve25519 ECDH in A8 cycles; dragon S4 cycles; Bridge cycles. analysis
- f algorithms.
- lynomial time”;
ratic time”. elliptic-curve field operations. Eliminating divisions Typical computation: P ✼✦ ♥P. Decompose into additions: P❀ ◗ ✼✦ P + ◗. Addition (①1❀ ②1) + (①2❀ ②2) = ((①1②2 + ②1①2)❂(1 + ❞①1①2②1②2), (②1②2 ①1①2)❂(1 ❞①1①2②1②2)) uses expensive divisions. Better: postpone divisions and work with fractions. Represent (①❀ ②) as (❳ : ❨ : ❩) with ① = ❳❂❩ and ② = ❨❂❩ for ❩ ✻= 0. Addition now has to handle fractions as ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨ ❩ ✓ ✥
❳1 ❩1 ❨2 ❩2 + ❨1 ❩1 ❳2 ❩2
1 + ❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2 ❨1 ❩1 ❨2 ❩2 ❳1 ❩1 ❳2 ❩2
1 ❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
✦ ✥ ❩1❩2(❳1❨2 + ❨1❳ ❩2
1❩2 2 + ❞❳1❳2❨ ❨
❩1❩2(❨1❨2 ❳1❳ ❩2
1❩2 2 ❞❳1❳2❨ ❨
✦

SLIDE 16
eed ✮ ECDH in cycles; rithms. time”; erations. Eliminating divisions Typical computation: P ✼✦ ♥P. Decompose into additions: P❀ ◗ ✼✦ P + ◗. Addition (①1❀ ②1) + (①2❀ ②2) = ((①1②2 + ②1①2)❂(1 + ❞①1①2②1②2), (②1②2 ①1①2)❂(1 ❞①1①2②1②2)) uses expensive divisions. Better: postpone divisions and work with fractions. Represent (①❀ ②) as (❳ : ❨ : ❩) with ① = ❳❂❩ and ② = ❨❂❩ for ❩ ✻= 0. Addition now has to handle fractions as input: ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ = ✥
❳1 ❩1 ❨2 ❩2 + ❨1 ❩1 ❳2 ❩2
1 + ❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
,
❨1 ❩1 ❨2 ❩2 ❳1 ❩1 ❳2 ❩2
1 ❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
✦ = ✥ ❩1❩2(❳1❨2 + ❨1❳2) ❩2
1❩2 2 + ❞❳1❳2❨1❨2
, ❩1❩2(❨1❨2 ❳1❳2) ❩2
1❩2 2 ❞❳1❳2❨1❨2
✦

SLIDE 17
Eliminating divisions Typical computation: P ✼✦ ♥P. Decompose into additions: P❀ ◗ ✼✦ P + ◗. Addition (①1❀ ②1) + (①2❀ ②2) = ((①1②2 + ②1①2)❂(1 + ❞①1①2②1②2), (②1②2 ①1①2)❂(1 ❞①1①2②1②2)) uses expensive divisions. Better: postpone divisions and work with fractions. Represent (①❀ ②) as (❳ : ❨ : ❩) with ① = ❳❂❩ and ② = ❨❂❩ for ❩ ✻= 0. Addition now has to handle fractions as input: ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ = ✥
❳1 ❩1 ❨2 ❩2 + ❨1 ❩1 ❳2 ❩2
1 + ❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
,
❨1 ❩1 ❨2 ❩2 ❳1 ❩1 ❳2 ❩2
1 ❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
✦ = ✥ ❩1❩2(❳1❨2 + ❨1❳2) ❩2
1❩2 2 + ❞❳1❳2❨1❨2
, ❩1❩2(❨1❨2 ❳1❳2) ❩2
1❩2 2 ❞❳1❳2❨1❨2
✦

SLIDE 18 Eliminating divisions ypical computation: P ✼✦ ♥P. Decompose into additions: P❀ ◗ ✼✦ P + ◗. Addition (①1❀ ②1) + (①2❀ ②2) = ① ② + ②1①2)❂(1 + ❞①1①2②1②2), ② ② ①1①2)❂(1 ❞①1①2②1②2)) expensive divisions. Better: postpone divisions
resent (①❀ ②) as ❳ ❨ : ❩) with ① = ❳❂❩ and ② ❨❂❩ for ❩ ✻= 0. Addition now has to handle fractions as input: ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ = ✥
❳1 ❩1 ❨2 ❩2 + ❨1 ❩1 ❳2 ❩2
1 + ❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
,
❨1 ❩1 ❨2 ❩2 ❳1 ❩1 ❳2 ❩2
1 ❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
✦ = ✥ ❩1❩2(❳1❨2 + ❨1❳2) ❩2
1❩2 2 + ❞❳1❳2❨1❨2
, ❩1❩2(❨1❨2 ❳1❳2) ❩2
1❩2 2 ❞❳1❳2❨1❨2
✦ i.e. ✒❳1 ❩1 ❀ ❨ ❩ ✓ ✒❳ ❩ ❀ ❨ ❩ ✓ = ✒❳3 ❩3 ❀ ❨ ❩ ✓ where ❋ = ❩2
1❩ ❞❳ ❳ ❨ ❨
1❩
❞❳ ❳ ❨ ❨ ❳3 = ❩1❩ ❳ ❨ ❨ ❳ ❋ ❨3 = ❩1❩ ❨ ❨ ❳ ❳
Input to ❳1❀ ❨1❀ ❩ ❀ ❳ ❀ ❨ ❀ ❩ Output from ❳3❀ ❨3❀ ❩

SLIDE 19 divisions computation: P ✼✦ ♥P additions: P❀ ◗ ✼✦ P ◗ ① ❀ ② ) + (①2❀ ②2) = ① ② ② ① ❂(1 + ❞①1①2②1②2), ② ② ① ① ❂(1 ❞①1①2②1②2)) divisions.
fractions. ①❀ ② as ❳ ❨ ❩ with ① = ❳❂❩ and ② ❨❂❩ ❩ ✻ 0. Addition now has to handle fractions as input: ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ = ✥
❳1 ❩1 ❨2 ❩2 + ❨1 ❩1 ❳2 ❩2
1 + ❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
,
❨1 ❩1 ❨2 ❩2 ❳1 ❩1 ❳2 ❩2
1 ❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
✦ = ✥ ❩1❩2(❳1❨2 + ❨1❳2) ❩2
1❩2 2 + ❞❳1❳2❨1❨2
, ❩1❩2(❨1❨2 ❳1❳2) ❩2
1❩2 2 ❞❳1❳2❨1❨2
✦ i.e. ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳ ❩ ❀ ❨ ❩ ✓ = ✒❳3 ❩3 ❀ ❨3 ❩3 ✓ where ❋ = ❩2
1❩2 2 ❞❳1❳ ❨ ❨
1❩2 2 + ❞❳1❳ ❨ ❨
❳3 = ❩1❩2(❳1❨2 + ❨ ❳ ❋ ❨3 = ❩1❩2(❨1❨2 ❳ ❳
Input to addition algo ❳1❀ ❨1❀ ❩1❀ ❳2❀ ❨2❀ ❩ Output from addition ❳3❀ ❨3❀ ❩3. No divisions

SLIDE 20 P ✼✦ ♥P : P❀ ◗ ✼✦ P ◗ ① ❀ ② ① ❀ ② ) = ① ② ② ① ❂ ❞① ①2②1②2), ② ② ① ① ❂ ❞① ①2②1②2)) ①❀ ② ❳ ❨ ❩ ① ❳❂❩ and ② ❨❂❩ ❩ ✻ Addition now has to handle fractions as input: ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ = ✥
❳1 ❩1 ❨2 ❩2 + ❨1 ❩1 ❳2 ❩2
1 + ❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
,
❨1 ❩1 ❨2 ❩2 ❳1 ❩1 ❳2 ❩2
1 ❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
✦ = ✥ ❩1❩2(❳1❨2 + ❨1❳2) ❩2
1❩2 2 + ❞❳1❳2❨1❨2
, ❩1❩2(❨1❨2 ❳1❳2) ❩2
1❩2 2 ❞❳1❳2❨1❨2
✦ i.e. ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ = ✒❳3 ❩3 ❀ ❨3 ❩3 ✓ where ❋ = ❩2
1❩2 2 ❞❳1❳2❨1❨2,
1❩2 2 + ❞❳1❳2❨1❨2,
❳3 = ❩1❩2(❳1❨2 + ❨1❳2)❋ ❨3 = ❩1❩2(❨1❨2 ❳1❳2)●, ❩3 = ❋●. Input to addition algorithm: ❳1❀ ❨1❀ ❩1❀ ❳2❀ ❨2❀ ❩2. Output from addition algorithm: ❳3❀ ❨3❀ ❩3. No divisions needed!

SLIDE 21 Addition now has to handle fractions as input: ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ = ✥
❳1 ❩1 ❨2 ❩2 + ❨1 ❩1 ❳2 ❩2
1 + ❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
,
❨1 ❩1 ❨2 ❩2 ❳1 ❩1 ❳2 ❩2
1 ❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
✦ = ✥ ❩1❩2(❳1❨2 + ❨1❳2) ❩2
1❩2 2 + ❞❳1❳2❨1❨2
, ❩1❩2(❨1❨2 ❳1❳2) ❩2
1❩2 2 ❞❳1❳2❨1❨2
✦ i.e. ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ = ✒❳3 ❩3 ❀ ❨3 ❩3 ✓ where ❋ = ❩2
1❩2 2 ❞❳1❳2❨1❨2,
1❩2 2 + ❞❳1❳2❨1❨2,
❳3 = ❩1❩2(❳1❨2 + ❨1❳2)❋, ❨3 = ❩1❩2(❨1❨2 ❳1❳2)●, ❩3 = ❋●. Input to addition algorithm: ❳1❀ ❨1❀ ❩1❀ ❳2❀ ❨2❀ ❩2. Output from addition algorithm: ❳3❀ ❨3❀ ❩3. No divisions needed!

SLIDE 22 Addition now has to fractions as input: ✒❳ ❩ ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ = ✥
❳ ❩ ❨2 ❩2 + ❨1 ❩1 ❳2 ❩2
❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
,
❨ ❩ ❨2 ❩2 ❳1 ❩1 ❳2 ❩2
❞❳1
❩1 ❳2 ❩2 ❨1 ❩1 ❨2 ❩2
✦ = ✥ ❩ ❩2(❳1❨2 + ❨1❳2) ❩ ❩2
2 + ❞❳1❳2❨1❨2
, ❩ ❩2(❨1❨2 ❳1❳2) ❩ ❩2
2 ❞❳1❳2❨1❨2
✦ i.e. ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ = ✒❳3 ❩3 ❀ ❨3 ❩3 ✓ where ❋ = ❩2
1❩2 2 ❞❳1❳2❨1❨2,
1❩2 2 + ❞❳1❳2❨1❨2,
❳3 = ❩1❩2(❳1❨2 + ❨1❳2)❋, ❨3 = ❩1❩2(❨1❨2 ❳1❳2)●, ❩3 = ❋●. Input to addition algorithm: ❳1❀ ❨1❀ ❩1❀ ❳2❀ ❨2❀ ❩2. Output from addition algorithm: ❳3❀ ❨3❀ ❩3. No divisions needed! Save multiplications eliminating subexpressions: ❆ = ❩1 ✁ ❩ ❇ ❆ ❈ = ❳1 ✁ ❳ ❉ = ❨1 ✁ ❨ ❊ = ❞ ✁ ❈ ✁ ❉ ❋ = ❇ ❊ ● ❇ ❊ ❳3 = ❆ ✁ ❋ ✁ ❳ ✁ ❨ ❨ ✁ ❳ ❨3 = ❆ ✁ ● ✁ ❉ ❈ ❩3 = ❋ ✁ ● Cost: 11 Can do b

SLIDE 23 has to as input: ✒❳ ❩ ❀ ❨ ❩ ✓ ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ = ✥
❳ ❩ ❨ ❩ ❨ ❩ ❳2 ❩2
❞❳
❩ ❳ ❩ ❨ ❩ ❨2 ❩2
,
❨ ❩ ❨ ❩ ❳ ❩ ❳2 ❩2
❞❳
❩ ❳ ❩ ❨ ❩ ❨2 ❩2
✦ = ✥ ❩ ❩ ❳ ❨ ❨1❳2) ❩ ❩ ❞❳ ❳2❨1❨2 , ❩ ❩ ❨ ❨ ❳1❳2) ❩ ❩ ❞❳ ❳2❨1❨2 ✦ i.e. ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ = ✒❳3 ❩3 ❀ ❨3 ❩3 ✓ where ❋ = ❩2
1❩2 2 ❞❳1❳2❨1❨2,
1❩2 2 + ❞❳1❳2❨1❨2,
❳3 = ❩1❩2(❳1❨2 + ❨1❳2)❋, ❨3 = ❩1❩2(❨1❨2 ❳1❳2)●, ❩3 = ❋●. Input to addition algorithm: ❳1❀ ❨1❀ ❩1❀ ❳2❀ ❨2❀ ❩2. Output from addition algorithm: ❳3❀ ❨3❀ ❩3. No divisions needed! Save multiplications eliminating common subexpressions: ❆ = ❩1 ✁ ❩2; ❇ = ❆ ❈ = ❳1 ✁ ❳2; ❉ = ❨1 ✁ ❨2; ❊ = ❞ ✁ ❈ ✁ ❉; ❋ = ❇ ❊; ● = ❇ ❊ ❳3 = ❆ ✁ ❋ ✁ (❳1 ✁ ❨ ❨ ✁ ❳ ❨3 = ❆ ✁ ● ✁ (❉ ❈ ❩3 = ❋ ✁ ●. Cost: 11M + 1S + Can do better: 10M

SLIDE 24 ✒❳ ❩ ❀ ❨ ❩ ✓ ✒❳ ❩ ❀ ❨ ❩ ✓ = ✥
❳ ❩ ❨ ❩ ❨ ❩ ❳ ❩
❞❳
❩ ❳ ❩ ❨ ❩ ❨ ❩ ❨ ❩ ❨ ❩ ❳ ❩ ❳ ❩
❞❳
❩ ❳ ❩ ❨ ❩ ❨ ❩
✦ ✥ ❩ ❩ ❳ ❨ ❨ ❳ ❩ ❩ ❞❳ ❳ ❨ ❨ ❩ ❩ ❨ ❨ ❳ ❳ ❩ ❩ ❞❳ ❳ ❨ ❨ ✦ i.e. ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ = ✒❳3 ❩3 ❀ ❨3 ❩3 ✓ where ❋ = ❩2
1❩2 2 ❞❳1❳2❨1❨2,
1❩2 2 + ❞❳1❳2❨1❨2,
❳3 = ❩1❩2(❳1❨2 + ❨1❳2)❋, ❨3 = ❩1❩2(❨1❨2 ❳1❳2)●, ❩3 = ❋●. Input to addition algorithm: ❳1❀ ❨1❀ ❩1❀ ❳2❀ ❨2❀ ❩2. Output from addition algorithm: ❳3❀ ❨3❀ ❩3. No divisions needed! Save multiplications by eliminating common subexpressions: ❆ = ❩1 ✁ ❩2; ❇ = ❆2; ❈ = ❳1 ✁ ❳2; ❉ = ❨1 ✁ ❨2; ❊ = ❞ ✁ ❈ ✁ ❉; ❋ = ❇ ❊; ● = ❇ + ❊; ❳3 = ❆ ✁ ❋ ✁ (❳1 ✁ ❨2 + ❨1 ✁ ❳ ❨3 = ❆ ✁ ● ✁ (❉ ❈); ❩3 = ❋ ✁ ●. Cost: 11M + 1S + 1D. Can do better: 10M + 1S +

SLIDE 25 i.e. ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ = ✒❳3 ❩3 ❀ ❨3 ❩3 ✓ where ❋ = ❩2
1❩2 2 ❞❳1❳2❨1❨2,
1❩2 2 + ❞❳1❳2❨1❨2,
❳3 = ❩1❩2(❳1❨2 + ❨1❳2)❋, ❨3 = ❩1❩2(❨1❨2 ❳1❳2)●, ❩3 = ❋●. Input to addition algorithm: ❳1❀ ❨1❀ ❩1❀ ❳2❀ ❨2❀ ❩2. Output from addition algorithm: ❳3❀ ❨3❀ ❩3. No divisions needed! Save multiplications by eliminating common subexpressions: ❆ = ❩1 ✁ ❩2; ❇ = ❆2; ❈ = ❳1 ✁ ❳2; ❉ = ❨1 ✁ ❨2; ❊ = ❞ ✁ ❈ ✁ ❉; ❋ = ❇ ❊; ● = ❇ + ❊; ❳3 = ❆ ✁ ❋ ✁ (❳1 ✁ ❨2 + ❨1 ✁ ❳2); ❨3 = ❆ ✁ ● ✁ (❉ ❈); ❩3 = ❋ ✁ ●. Cost: 11M + 1S + 1D. Can do better: 10M + 1S + 1D.

SLIDE 26 ✒❳1 ❩1 ❀ ❨1 ❩1 ✓ + ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ ✒❳3 ❩ ❀ ❨3 ❩3 ✓ ❋ ❩2
1❩2 2 ❞❳1❳2❨1❨2,
1❩2 2 + ❞❳1❳2❨1❨2,
❳ ❩1❩2(❳1❨2 + ❨1❳2)❋, ❨ ❩1❩2(❨1❨2 ❳1❳2)●, ❩ ❋●. to addition algorithm: ❳ ❀ ❨ ❀ ❩1❀ ❳2❀ ❨2❀ ❩2. Output from addition algorithm: ❳ ❀ ❨ ❀ ❩3. No divisions needed! Save multiplications by eliminating common subexpressions: ❆ = ❩1 ✁ ❩2; ❇ = ❆2; ❈ = ❳1 ✁ ❳2; ❉ = ❨1 ✁ ❨2; ❊ = ❞ ✁ ❈ ✁ ❉; ❋ = ❇ ❊; ● = ❇ + ❊; ❳3 = ❆ ✁ ❋ ✁ (❳1 ✁ ❨2 + ❨1 ✁ ❳2); ❨3 = ❆ ✁ ● ✁ (❉ ❈); ❩3 = ❋ ✁ ●. Cost: 11M + 1S + 1D. Can do better: 10M + 1S + 1D. Faster doublin (①1❀ ②1) + ① ❀ ② ((①1②1+② ① ❂ ❞① ① ② ② (②1②1① ① ❂ ❞① ① ② ② ((2①1②1)❂ ❞① ② (②2
1①2 1 ❂
❞① ② ①2
1 + ②2 1
❞① ② (①1❀ ②1) + ① ❀ ② ((2①1②1)❂ ① ② (②2
1①2 1 ❂
① ② Again eliminate using P2 Much faster Useful: many

SLIDE 27 ✒❳ ❩ ❀ ❨ ❩ ✓ ✒❳2 ❩2 ❀ ❨2 ❩2 ✓ ✒❳ ❩ ❀ ❨ ❩ ✓ ❋ ❩ ❩ ❞❳1❳2❨1❨2,
❞❳1❳2❨1❨2, ❳ ❩ ❩ ❳ ❨2 + ❨1❳2)❋, ❨ ❩ ❩ ❨ ❨ ❳1❳2)●, ❩ ❋● algorithm: ❳ ❀ ❨ ❀ ❩ ❀ ❳ ❀ ❨ ❀ ❩2. addition algorithm: ❳ ❀ ❨ ❀ ❩ divisions needed! Save multiplications by eliminating common subexpressions: ❆ = ❩1 ✁ ❩2; ❇ = ❆2; ❈ = ❳1 ✁ ❳2; ❉ = ❨1 ✁ ❨2; ❊ = ❞ ✁ ❈ ✁ ❉; ❋ = ❇ ❊; ● = ❇ + ❊; ❳3 = ❆ ✁ ❋ ✁ (❳1 ✁ ❨2 + ❨1 ✁ ❳2); ❨3 = ❆ ✁ ● ✁ (❉ ❈); ❩3 = ❋ ✁ ●. Cost: 11M + 1S + 1D. Can do better: 10M + 1S + 1D. Faster doubling (①1❀ ②1) + (①1❀ ②1) ((①1②1+②1①1)❂(1+❞① ① ② ② (②1②1①1①1)❂(1❞① ① ② ② ((2①1②1)❂(1 + ❞①2
1②
(②2
1①2 1)❂(1 ❞① ②
①2
1 + ②2 1 = 1 + ❞①2 1②
(①1❀ ②1) + (①1❀ ②1) ((2①1②1)❂(①2
1 + ②2 1
(②2
1①2 1)❂(2 ①2 1 ②
Again eliminate divisions using P2: only 3M Much faster than addition. Useful: many doublings

SLIDE 28 ✒❳ ❩ ❀ ❨ ❩ ✓ ✒❳ ❩ ❀ ❨ ❩2 ✓ ✒❳ ❩ ❀ ❨ ❩ ✓ ❋ ❩ ❩ ❞❳ ❳ ❨ ❨
❞❳ ❳ ❨ ❨ ❳ ❩ ❩ ❳ ❨ ❨ ❳ ❋, ❨ ❩ ❩ ❨ ❨ ❳ ❳
❩ ❋● rithm: ❳ ❀ ❨ ❀ ❩ ❀ ❳ ❀ ❨ ❀ ❩ rithm: ❳ ❀ ❨ ❀ ❩ needed! Save multiplications by eliminating common subexpressions: ❆ = ❩1 ✁ ❩2; ❇ = ❆2; ❈ = ❳1 ✁ ❳2; ❉ = ❨1 ✁ ❨2; ❊ = ❞ ✁ ❈ ✁ ❉; ❋ = ❇ ❊; ● = ❇ + ❊; ❳3 = ❆ ✁ ❋ ✁ (❳1 ✁ ❨2 + ❨1 ✁ ❳2); ❨3 = ❆ ✁ ● ✁ (❉ ❈); ❩3 = ❋ ✁ ●. Cost: 11M + 1S + 1D. Can do better: 10M + 1S + 1D. Faster doubling (①1❀ ②1) + (①1❀ ②1) = ((①1②1+②1①1)❂(1+❞①1①1②1② (②1②1①1①1)❂(1❞①1①1②1② ((2①1②1)❂(1 + ❞①2
1②2 1),
(②2
1①2 1)❂(1 ❞①2 1②2 1)).
①2
1 + ②2 1 = 1 + ❞①2 1②2 1 so
(①1❀ ②1) + (①1❀ ②1) = ((2①1②1)❂(①2
1 + ②2 1),
(②2
1①2 1)❂(2 ①2 1 ②2 1)).
Again eliminate divisions using P2: only 3M + 4S. Much faster than addition. Useful: many doublings in ECC.

SLIDE 29
Save multiplications by eliminating common subexpressions: ❆ = ❩1 ✁ ❩2; ❇ = ❆2; ❈ = ❳1 ✁ ❳2; ❉ = ❨1 ✁ ❨2; ❊ = ❞ ✁ ❈ ✁ ❉; ❋ = ❇ ❊; ● = ❇ + ❊; ❳3 = ❆ ✁ ❋ ✁ (❳1 ✁ ❨2 + ❨1 ✁ ❳2); ❨3 = ❆ ✁ ● ✁ (❉ ❈); ❩3 = ❋ ✁ ●. Cost: 11M + 1S + 1D. Can do better: 10M + 1S + 1D. Faster doubling (①1❀ ②1) + (①1❀ ②1) = ((①1②1+②1①1)❂(1+❞①1①1②1②1), (②1②1①1①1)❂(1❞①1①1②1②1)) = ((2①1②1)❂(1 + ❞①2
1②2 1),
(②2
1①2 1)❂(1 ❞①2 1②2 1)).
①2
1 + ②2 1 = 1 + ❞①2 1②2 1 so
(①1❀ ②1) + (①1❀ ②1) = ((2①1②1)❂(①2
1 + ②2 1),
(②2
1①2 1)❂(2 ①2 1 ②2 1)).
Again eliminate divisions using P2: only 3M + 4S. Much faster than addition. Useful: many doublings in ECC.

SLIDE 30
multiplications by eliminating common ressions: ❆ ❩1 ✁ ❩2; ❇ = ❆2; ❈ ❳1 ✁ ❳2; ❉ ❨1 ✁ ❨2; ❊ ❞ ✁ ❈ ✁ ❉; ❋ ❇ ❊; ● = ❇ + ❊; ❳ ❆ ✁ ❋ ✁ (❳1 ✁ ❨2 + ❨1 ✁ ❳2); ❨ ❆ ✁ ● ✁ (❉ ❈); ❩ ❋ ✁ ●. 11M + 1S + 1D. do better: 10M + 1S + 1D. Faster doubling (①1❀ ②1) + (①1❀ ②1) = ((①1②1+②1①1)❂(1+❞①1①1②1②1), (②1②1①1①1)❂(1❞①1①1②1②1)) = ((2①1②1)❂(1 + ❞①2
1②2 1),
(②2
1①2 1)❂(1 ❞①2 1②2 1)).
①2
1 + ②2 1 = 1 + ❞①2 1②2 1 so
(①1❀ ②1) + (①1❀ ②1) = ((2①1②1)❂(①2
1 + ②2 1),
(②2
1①2 1)❂(2 ①2 1 ②2 1)).
Again eliminate divisions using P2: only 3M + 4S. Much faster than addition. Useful: many doublings in ECC. More add Dual addition (①1❀ ②1) + ① ❀ ② ((①1②1 + ① ② ❂ ① ① ② ② ❀ (①1②1 ① ② ❂ ① ② ① ② Low degree, ❞ Warning: Is this really Most EC

SLIDE 31
multiplications by common ❆ ❩ ✁ ❩ ❇ = ❆2; ❈ ❳ ✁ ❳ ❉ ❨ ✁ ❨ ❊ ❞ ✁ ❈ ✁ ❉ ❋ ❇ ❊ ● ❇ + ❊; ❳ ❆ ✁ ❋ ✁ ❳ ✁ ❨2 + ❨1 ✁ ❳2); ❨ ❆ ✁ ● ✁ ❉ ❈); ❩ ❋ ✁ ● + 1D. 10M + 1S + 1D. Faster doubling (①1❀ ②1) + (①1❀ ②1) = ((①1②1+②1①1)❂(1+❞①1①1②1②1), (②1②1①1①1)❂(1❞①1①1②1②1)) = ((2①1②1)❂(1 + ❞①2
1②2 1),
(②2
1①2 1)❂(1 ❞①2 1②2 1)).
①2
1 + ②2 1 = 1 + ❞①2 1②2 1 so
(①1❀ ②1) + (①1❀ ②1) = ((2①1②1)❂(①2
1 + ②2 1),
(②2
1①2 1)❂(2 ①2 1 ②2 1)).
Again eliminate divisions using P2: only 3M + 4S. Much faster than addition. Useful: many doublings in ECC. More addition strategies Dual addition formula: (①1❀ ②1) + (①2❀ ②2) ((①1②1 + ①2②2)❂(① ① ② ② ❀ (①1②1 ①2②2)❂(① ② ① ② Low degree, no need ❞ Warning: fails for Is this really “addition”? Most EC formulas

SLIDE 32
❆ ❩ ✁ ❩ ❇ ❆ ❈ ❳ ✁ ❳ ❉ ❨ ✁ ❨ ❊ ❞ ✁ ❈ ✁ ❉ ❋ ❇ ❊ ● ❇ ❊ ❳ ❆ ✁ ❋ ✁ ❳ ✁ ❨ ❨ ✁ ❳2); ❨ ❆ ✁ ● ✁ ❉ ❈ ❩ ❋ ✁ ● + 1D. Faster doubling (①1❀ ②1) + (①1❀ ②1) = ((①1②1+②1①1)❂(1+❞①1①1②1②1), (②1②1①1①1)❂(1❞①1①1②1②1)) = ((2①1②1)❂(1 + ❞①2
1②2 1),
(②2
1①2 1)❂(1 ❞①2 1②2 1)).
①2
1 + ②2 1 = 1 + ❞①2 1②2 1 so
(①1❀ ②1) + (①1❀ ②1) = ((2①1②1)❂(①2
1 + ②2 1),
(②2
1①2 1)❂(2 ①2 1 ②2 1)).
Again eliminate divisions using P2: only 3M + 4S. Much faster than addition. Useful: many doublings in ECC. More addition strategies Dual addition formula: (①1❀ ②1) + (①2❀ ②2) = ((①1②1 + ①2②2)❂(①1①2 + ②1② ❀ (①1②1 ①2②2)❂(①1②2 ①2② Low degree, no need for ❞. Warning: fails for doubling! Is this really “addition”? Most EC formulas have failures.

SLIDE 33
Faster doubling (①1❀ ②1) + (①1❀ ②1) = ((①1②1+②1①1)❂(1+❞①1①1②1②1), (②1②1①1①1)❂(1❞①1①1②1②1)) = ((2①1②1)❂(1 + ❞①2
1②2 1),
(②2
1①2 1)❂(1 ❞①2 1②2 1)).
①2
1 + ②2 1 = 1 + ❞①2 1②2 1 so
(①1❀ ②1) + (①1❀ ②1) = ((2①1②1)❂(①2
1 + ②2 1),
(②2
1①2 1)❂(2 ①2 1 ②2 1)).
Again eliminate divisions using P2: only 3M + 4S. Much faster than addition. Useful: many doublings in ECC. More addition strategies Dual addition formula: (①1❀ ②1) + (①2❀ ②2) = ((①1②1 + ①2②2)❂(①1①2 + ②1②2)❀ (①1②1 ①2②2)❂(①1②2 ①2②1)). Low degree, no need for ❞. Warning: fails for doubling! Is this really “addition”? Most EC formulas have failures.

SLIDE 34
Faster doubling (①1❀ ②1) + (①1❀ ②1) = ((①1②1+②1①1)❂(1+❞①1①1②1②1), (②1②1①1①1)❂(1❞①1①1②1②1)) = ((2①1②1)❂(1 + ❞①2
1②2 1),
(②2
1①2 1)❂(1 ❞①2 1②2 1)).
①2
1 + ②2 1 = 1 + ❞①2 1②2 1 so
(①1❀ ②1) + (①1❀ ②1) = ((2①1②1)❂(①2
1 + ②2 1),
(②2
1①2 1)❂(2 ①2 1 ②2 1)).
Again eliminate divisions using P2: only 3M + 4S. Much faster than addition. Useful: many doublings in ECC. More addition strategies Dual addition formula: (①1❀ ②1) + (①2❀ ②2) = ((①1②1 + ①2②2)❂(①1①2 + ②1②2)❀ (①1②1 ①2②2)❂(①1②2 ①2②1)). Low degree, no need for ❞. Warning: fails for doubling! Is this really “addition”? Most EC formulas have failures. More coordinate systems: Inverted: ① = ❩❂❳, ② = ❩❂❨ . Extended: ① = ❳❂❩, ② = ❨❂❚. Completed: ① = ❳❂❩, ② = ❨❂❩, ①② = ❚❂❩.

SLIDE 35
doubling ① ❀ ② ) + (①1❀ ②1) = ① ② +②1①1)❂(1+❞①1①1②1②1), ② ② ①1①1)❂(1❞①1①1②1②1)) = ① ②1)❂(1 + ❞①2
1②2 1),
② ①2
1)❂(1 ❞①2 1②2 1)).
① ②2
1 = 1 + ❞①2 1②2 1 so
① ❀ ② ) + (①1❀ ②1) = ① ②1)❂(①2
1 + ②2 1),
② ①2
1)❂(2 ①2 1 ②2 1)).
eliminate divisions P2: only 3M + 4S. faster than addition. Useful: many doublings in ECC. More addition strategies Dual addition formula: (①1❀ ②1) + (①2❀ ②2) = ((①1②1 + ①2②2)❂(①1①2 + ②1②2)❀ (①1②1 ①2②2)❂(①1②2 ①2②1)). Low degree, no need for ❞. Warning: fails for doubling! Is this really “addition”? Most EC formulas have failures. More coordinate systems: Inverted: ① = ❩❂❳, ② = ❩❂❨ . Extended: ① = ❳❂❩, ② = ❨❂❚. Completed: ① = ❳❂❩, ② = ❨❂❩, ①② = ❚❂❩. More elliptic Edwards Easiest w elliptic curves Geometrically are Edwa Algebraically more elliptic Every odd-cha expressed ✈2 = ✉3 ❛ ✉ ❛ ✉ ❛ Warning: different

SLIDE 36
① ❀ ② ① ❀ ②1) = ① ② ② ① ❂(1+❞①1①1②1②1), ② ② ① ① ❂(1❞①1①1②1②1)) = ① ② ❂ ❞①2
1②2 1),
② ① ❂ ❞①2
1②2 1)).
① ② ❞①2
1②2 1 so
① ❀ ② ① ❀ ②1) = ① ② ❂ ① ②2
1),
② ① ❂ ①2
1 ②2 1)).
divisions M + 4S. than addition. doublings in ECC. More addition strategies Dual addition formula: (①1❀ ②1) + (①2❀ ②2) = ((①1②1 + ①2②2)❂(①1①2 + ②1②2)❀ (①1②1 ①2②2)❂(①1②2 ①2②1)). Low degree, no need for ❞. Warning: fails for doubling! Is this really “addition”? Most EC formulas have failures. More coordinate systems: Inverted: ① = ❩❂❳, ② = ❩❂❨ . Extended: ① = ❳❂❩, ② = ❨❂❚. Completed: ① = ❳❂❩, ② = ❨❂❩, ①② = ❚❂❩. More elliptic curves Edwards curves are Easiest way to understand elliptic curves is Edw Geometrically, all elliptic are Edwards curves. Algebraically, more elliptic curves Every odd-char curve expressed as Weierstrass ✈2 = ✉3 + ❛2✉2 + ❛ ✉ ❛ Warning: “Weierstra different meaning in

SLIDE 37
① ❀ ② ① ❀ ② ① ② ② ① ❂ ❞① ① ②1②1), ② ② ① ① ❂ ❞① ① ②1②1)) = ① ② ❂ ❞① ② ② ① ❂ ❞① ② ① ② ❞① ② ① ❀ ② ① ❀ ② ① ② ❂ ① ② ② ① ❂ ① ② addition. ECC. More addition strategies Dual addition formula: (①1❀ ②1) + (①2❀ ②2) = ((①1②1 + ①2②2)❂(①1①2 + ②1②2)❀ (①1②1 ①2②2)❂(①1②2 ①2②1)). Low degree, no need for ❞. Warning: fails for doubling! Is this really “addition”? Most EC formulas have failures. More coordinate systems: Inverted: ① = ❩❂❳, ② = ❩❂❨ . Extended: ① = ❳❂❩, ② = ❨❂❚. Completed: ① = ❳❂❩, ② = ❨❂❩, ①② = ❚❂❩. More elliptic curves Edwards curves are elliptic. Easiest way to understand elliptic curves is Edwards. Geometrically, all elliptic curves are Edwards curves. Algebraically, more elliptic curves exist. Every odd-char curve can be expressed as Weierstrass curve ✈2 = ✉3 + ❛2✉2 + ❛4✉ + ❛6. Warning: “Weierstrass” has different meaning in char 2.

SLIDE 38
More addition strategies Dual addition formula: (①1❀ ②1) + (①2❀ ②2) = ((①1②1 + ①2②2)❂(①1①2 + ②1②2)❀ (①1②1 ①2②2)❂(①1②2 ①2②1)). Low degree, no need for ❞. Warning: fails for doubling! Is this really “addition”? Most EC formulas have failures. More coordinate systems: Inverted: ① = ❩❂❳, ② = ❩❂❨ . Extended: ① = ❳❂❩, ② = ❨❂❚. Completed: ① = ❳❂❩, ② = ❨❂❩, ①② = ❚❂❩. More elliptic curves Edwards curves are elliptic. Easiest way to understand elliptic curves is Edwards. Geometrically, all elliptic curves are Edwards curves. Algebraically, more elliptic curves exist. Every odd-char curve can be expressed as Weierstrass curve ✈2 = ✉3 + ❛2✉2 + ❛4✉ + ❛6. Warning: “Weierstrass” has different meaning in char 2.

SLIDE 39
addition strategies addition formula: ① ❀ ② ) + (①2❀ ②2) = ① ② + ①2②2)❂(①1①2 + ②1②2)❀ ① ② ①2②2)❂(①1②2 ①2②1)). degree, no need for ❞. rning: fails for doubling! really “addition”? EC formulas have failures. coordinate systems: Inverted: ① = ❩❂❳, ② = ❩❂❨ . Extended: ① = ❳❂❩, ② = ❨❂❚. Completed: ① = ❳❂❩, ② = ❨❂❩, ①② ❚❂❩. More elliptic curves Edwards curves are elliptic. Easiest way to understand elliptic curves is Edwards. Geometrically, all elliptic curves are Edwards curves. Algebraically, more elliptic curves exist. Every odd-char curve can be expressed as Weierstrass curve ✈2 = ✉3 + ❛2✉2 + ❛4✉ + ❛6. Warning: “Weierstrass” has different meaning in char 2. Addition ✈2 = ✉3 ✉ ✉ ✎ P ✎P ✎ P P ✾ ✎P P ✉ ✈ Slope ✕ = ✈ ✈ ❂ ✉ ✉ Note that ✉ ✻ ✉

SLIDE 40 strategies rmula: ① ❀ ② ① ❀ ②2) = ① ② ① ② ❂(①1①2 + ②1②2)❀ ① ② ① ② ❂(①1②2 ①2②1)). need for ❞. r doubling! “addition”? rmulas have failures. systems: ① ❩❂❳, ② = ❩❂❨ . ① ❳❂❩, ② = ❨❂❚. ① ❳❂❩, ② = ❨❂❩, ①② ❚❂❩ More elliptic curves Edwards curves are elliptic. Easiest way to understand elliptic curves is Edwards. Geometrically, all elliptic curves are Edwards curves. Algebraically, more elliptic curves exist. Every odd-char curve can be expressed as Weierstrass curve ✈2 = ✉3 + ❛2✉2 + ❛4✉ + ❛6. Warning: “Weierstrass” has different meaning in char 2. Addition on Weierstrass ✈2 = ✉3 + ✉2 + ✉ ✎ P1 ✎P2 ✎ P P ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✎P P ✉ ✈
Note that ✉1 ✻= ✉2

SLIDE 41 ① ❀ ② ① ❀ ② ① ② ① ② ❂ ① ① ②1②2)❀ ① ② ① ② ❂ ① ② ①2②1)). ❞. doubling! failures. ① ❩❂❳ ② ❩❂❨ . ① ❳❂❩ ② ❨❂❚. ① ❳❂❩ ② = ❨❂❩, ①② ❚❂❩ More elliptic curves Edwards curves are elliptic. Easiest way to understand elliptic curves is Edwards. Geometrically, all elliptic curves are Edwards curves. Algebraically, more elliptic curves exist. Every odd-char curve can be expressed as Weierstrass curve ✈2 = ✉3 + ❛2✉2 + ❛4✉ + ❛6. Warning: “Weierstrass” has different meaning in char 2. Addition on Weierstrass curve ✈2 = ✉3 + ✉2 + ✉ + 1 ✎ P1 ✎P2 ✎(P1 + P ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✎P1 + P2 ✉
- ✈
- Slope ✕ = (✈2 ✈1)❂(✉2 ✉
Note that ✉1 ✻= ✉2.

SLIDE 42 More elliptic curves Edwards curves are elliptic. Easiest way to understand elliptic curves is Edwards. Geometrically, all elliptic curves are Edwards curves. Algebraically, more elliptic curves exist. Every odd-char curve can be expressed as Weierstrass curve ✈2 = ✉3 + ❛2✉2 + ❛4✉ + ❛6. Warning: “Weierstrass” has different meaning in char 2. Addition on Weierstrass curve ✈2 = ✉3 + ✉2 + ✉ + 1 ✎ P1 ✎P2 ✎(P1 + P2) ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✎P1 + P2 ✉
- ✈
- Slope ✕ = (✈2 ✈1)❂(✉2 ✉1).
Note that ✉1 ✻= ✉2.

SLIDE 43 elliptic curves rds curves are elliptic. Easiest way to understand curves is Edwards. Geometrically, all elliptic curves Edwards curves. raically, elliptic curves exist.
ressed as Weierstrass curve ✈ ✉3 + ❛2✉2 + ❛4✉ + ❛6. rning: “Weierstrass” has different meaning in char 2. Addition on Weierstrass curve ✈2 = ✉3 + ✉2 + ✉ + 1 ✎ P1 ✎P2 ✎(P1 + P2) ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✎P1 + P2 ✉
- ✈
- Slope ✕ = (✈2 ✈1)❂(✉2 ✉1).
Note that ✉1 ✻= ✉2. Doubling ✈2 = ✉3 ✉ ✎ P ✎ P ❧ ❧ ❧ ✎ P ✉ ✈ Slope ✕ = ✉ ❂ ✈

SLIDE 44 curves are elliptic. nderstand Edwards. all elliptic curves curves. curves exist. curve can be eierstrass curve ✈ ✉ ❛ ✉ + ❛4✉ + ❛6. rstrass” has meaning in char 2. Addition on Weierstrass curve ✈2 = ✉3 + ✉2 + ✉ + 1 ✎ P1 ✎P2 ✎(P1 + P2) ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✎P1 + P2 ✉
- ✈
- Slope ✕ = (✈2 ✈1)❂(✉2 ✉1).
Note that ✉1 ✻= ✉2. Doubling on Weierstrass ✈2 = ✉3 ✉ ✎ P1 ✎ P ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ✎ P ✉ ✈
1
❂ ✈

SLIDE 45 elliptic. curves be curve ✈ ✉ ❛ ✉ ❛ ✉ ❛6. has 2. Addition on Weierstrass curve ✈2 = ✉3 + ✉2 + ✉ + 1 ✎ P1 ✎P2 ✎(P1 + P2) ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✎P1 + P2 ✉
- ✈
- Slope ✕ = (✈2 ✈1)❂(✉2 ✉1).
Note that ✉1 ✻= ✉2. Doubling on Weierstrass curve ✈2 = ✉3 ✉ ✎ P1 ✎ 2P1 ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ✎ 2P1 ✉
1 1)❂(2✈1).

SLIDE 46 Addition on Weierstrass curve ✈2 = ✉3 + ✉2 + ✉ + 1 ✎ P1 ✎P2 ✎(P1 + P2) ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✎P1 + P2 ✉
- ✈
- Slope ✕ = (✈2 ✈1)❂(✉2 ✉1).
Note that ✉1 ✻= ✉2. Doubling on Weierstrass curve ✈2 = ✉3 ✉ ✎ P1 ✎ 2P1 ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ✎ 2P1 ✉
1 1)❂(2✈1).

SLIDE 47 Addition on Weierstrass curve ✈ ✉3 + ✉2 + ✉ + 1 ✎ P1 ✎P2 ✎(P1 + P2) ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✎P1 + P2 ✉
that ✉1 ✻= ✉2. Doubling on Weierstrass curve ✈2 = ✉3 ✉ ✎ P1 ✎ 2P1 ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ✎ 2P1 ✉
1 1)❂(2✈1).
In most (✉1❀ ✈1) + ✉ ❀ ✈ (✉3❀ ✈3) ✉ ❀ ✈ (✕2✉1✉ ❀ ✕ ✉ ✉ ✈ ✿ ✉1 ✻= ✉2, ✕ = (✈2 ✈ ❂ ✉ ✉ Total cost (✉1❀ ✈1) ✉ ❀ ✈ ✈ ✻ “doubling” ✕ = (3✉2
1
❛ ✉ ❛ ❂ ✈ Total cost Also handle (✉1❀ ✈1) ✉ ❀ ✈ inputs at ✶

SLIDE 48 eierstrass curve ✈ ✉ ✉ ✉ + 1 ✎ P ✎P2 ✎(P1 + P2) ✾ ✾ ✾ ✾ ✾ ✾ ✾ ✎P1 + P2 ✉
✕ ✈ ✈1)❂(✉2 ✉1). ✉ ✻ ✉2. Doubling on Weierstrass curve ✈2 = ✉3 ✉ ✎ P1 ✎ 2P1 ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ✎ 2P1 ✉
1 1)❂(2✈1).
In most cases (✉1❀ ✈1) + (✉2❀ ✈2) (✉3❀ ✈3) where (✉3❀ ✈ (✕2✉1✉2❀ ✕(✉1✉ ✈ ✿ ✉1 ✻= ✉2, “addition” ✕ = (✈2 ✈1)❂(✉2 ✉ Total cost 1I + 2M (✉1❀ ✈1) = (✉2❀ ✈2) ✈ ✻ “doubling” (alert!): ✕ = (3✉2
1 + 2❛2✉1
❛ ❂ ✈ Total cost 1I + 2M Also handle some exceptions: (✉1❀ ✈1) = (✉2❀ ✈ inputs at ✶.

SLIDE 49 curve ✈ ✉ ✉ ✉ ✎ P ✎P ✎ P + P2) ✎P P2 ✉
✕ ✈ ✈ ❂ ✉ ✉1). ✉ ✻ ✉ Doubling on Weierstrass curve ✈2 = ✉3 ✉ ✎ P1 ✎ 2P1 ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ✎ 2P1 ✉
1 1)❂(2✈1).
In most cases (✉1❀ ✈1) + (✉2❀ ✈2) = (✉3❀ ✈3) where (✉3❀ ✈3) = (✕2✉1✉2❀ ✕(✉1✉3)✈1)✿ ✉1 ✻= ✉2, “addition” (alert!): ✕ = (✈2 ✈1)❂(✉2 ✉1). Total cost 1I + 2M + 1S. (✉1❀ ✈1) = (✉2❀ ✈2) and ✈1 ✻= “doubling” (alert!): ✕ = (3✉2
1 + 2❛2✉1 + ❛4)❂(2✈
Total cost 1I + 2M + 2S. Also handle some exceptions: (✉1❀ ✈1) = (✉2❀ ✈2); inputs at ✶.

SLIDE 50 Doubling on Weierstrass curve ✈2 = ✉3 ✉ ✎ P1 ✎ 2P1 ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ✎ 2P1 ✉
1 1)❂(2✈1).
In most cases (✉1❀ ✈1) + (✉2❀ ✈2) = (✉3❀ ✈3) where (✉3❀ ✈3) = (✕2✉1✉2❀ ✕(✉1✉3)✈1)✿ ✉1 ✻= ✉2, “addition” (alert!): ✕ = (✈2 ✈1)❂(✉2 ✉1). Total cost 1I + 2M + 1S. (✉1❀ ✈1) = (✉2❀ ✈2) and ✈1 ✻= 0, “doubling” (alert!): ✕ = (3✉2
1 + 2❛2✉1 + ❛4)❂(2✈1).
Total cost 1I + 2M + 2S. Also handle some exceptions: (✉1❀ ✈1) = (✉2❀ ✈2); inputs at ✶.

SLIDE 51 Doubling on Weierstrass curve ✈ ✉3 ✉ ✎ P1 ✎ 2P1 ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ✎ 2P1 ✉
1 1)❂(2✈1).
In most cases (✉1❀ ✈1) + (✉2❀ ✈2) = (✉3❀ ✈3) where (✉3❀ ✈3) = (✕2✉1✉2❀ ✕(✉1✉3)✈1)✿ ✉1 ✻= ✉2, “addition” (alert!): ✕ = (✈2 ✈1)❂(✉2 ✉1). Total cost 1I + 2M + 1S. (✉1❀ ✈1) = (✉2❀ ✈2) and ✈1 ✻= 0, “doubling” (alert!): ✕ = (3✉2
1 + 2❛2✉1 + ❛4)❂(2✈1).
Total cost 1I + 2M + 2S. Also handle some exceptions: (✉1❀ ✈1) = (✉2❀ ✈2); inputs at ✶. Birational Starting ①❀ ②
❞① ② Define ❆ ❞ ❂ ❞ ❇ = 4❂(1 ❞ ✉ = (1 + ② ❂ ❇ ② ✈ = ✉❂① ② ❂ ❇① ② (Skip a fe ✈2 = ✉3 ❆❂❇ ✉ ❂❇ ✉ Maps Edw Compatible Easily invert ① = ✉❂✈ ② ❇✉ ❂ ❇✉

SLIDE 52 eierstrass curve ✈ ✉ ✉ ✎ P ✎ 2P1 ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ❧ ✎ 2P1 ✉
✕ ✉ 1)❂(2✈1). In most cases (✉1❀ ✈1) + (✉2❀ ✈2) = (✉3❀ ✈3) where (✉3❀ ✈3) = (✕2✉1✉2❀ ✕(✉1✉3)✈1)✿ ✉1 ✻= ✉2, “addition” (alert!): ✕ = (✈2 ✈1)❂(✉2 ✉1). Total cost 1I + 2M + 1S. (✉1❀ ✈1) = (✉2❀ ✈2) and ✈1 ✻= 0, “doubling” (alert!): ✕ = (3✉2
1 + 2❛2✉1 + ❛4)❂(2✈1).
Total cost 1I + 2M + 2S. Also handle some exceptions: (✉1❀ ✈1) = (✉2❀ ✈2); inputs at ✶. Birational equivalence Starting from point ①❀ ②
Define ❆ = 2(1 + ❞ ❂ ❞ ❇ = 4❂(1 ❞); ✉ = (1 + ②)❂(❇(1 ② ✈ = ✉❂① = (1 + ②)❂ ❇① ② (Skip a few exceptional ✈2 = ✉3 + (❆❂❇)✉ ❂❇ ✉ Maps Edwards to W Compatible with p Easily invert this map: ① = ✉❂✈, ② = (❇✉ ❂ ❇✉

SLIDE 53 curve ✈ ✉ ✉ ✎ P ✎ P1 ❧ ✎ P ✉
✕ ✉ ❂ ✈ ). In most cases (✉1❀ ✈1) + (✉2❀ ✈2) = (✉3❀ ✈3) where (✉3❀ ✈3) = (✕2✉1✉2❀ ✕(✉1✉3)✈1)✿ ✉1 ✻= ✉2, “addition” (alert!): ✕ = (✈2 ✈1)❂(✉2 ✉1). Total cost 1I + 2M + 1S. (✉1❀ ✈1) = (✉2❀ ✈2) and ✈1 ✻= 0, “doubling” (alert!): ✕ = (3✉2
1 + 2❛2✉1 + ❛4)❂(2✈1).
Total cost 1I + 2M + 2S. Also handle some exceptions: (✉1❀ ✈1) = (✉2❀ ✈2); inputs at ✶. Birational equivalence Starting from point (①❀ ②)
Define ❆ = 2(1 + ❞)❂(1 ❞), ❇ = 4❂(1 ❞); ✉ = (1 + ②)❂(❇(1 ②)), ✈ = ✉❂① = (1 + ②)❂(❇①(1 ② (Skip a few exceptional points.) ✈2 = ✉3 + (❆❂❇)✉2 + (1❂❇ ✉ Maps Edwards to Weierstrass. Compatible with point addition! Easily invert this map: ① = ✉❂✈, ② = (❇✉ 1)❂(❇✉

SLIDE 54 In most cases (✉1❀ ✈1) + (✉2❀ ✈2) = (✉3❀ ✈3) where (✉3❀ ✈3) = (✕2✉1✉2❀ ✕(✉1✉3)✈1)✿ ✉1 ✻= ✉2, “addition” (alert!): ✕ = (✈2 ✈1)❂(✉2 ✉1). Total cost 1I + 2M + 1S. (✉1❀ ✈1) = (✉2❀ ✈2) and ✈1 ✻= 0, “doubling” (alert!): ✕ = (3✉2
1 + 2❛2✉1 + ❛4)❂(2✈1).
Total cost 1I + 2M + 2S. Also handle some exceptions: (✉1❀ ✈1) = (✉2❀ ✈2); inputs at ✶. Birational equivalence Starting from point (①❀ ②)
Define ❆ = 2(1 + ❞)❂(1 ❞), ❇ = 4❂(1 ❞); ✉ = (1 + ②)❂(❇(1 ②)), ✈ = ✉❂① = (1 + ②)❂(❇①(1 ②)). (Skip a few exceptional points.) ✈2 = ✉3 + (❆❂❇)✉2 + (1❂❇2)✉. Maps Edwards to Weierstrass. Compatible with point addition! Easily invert this map: ① = ✉❂✈, ② = (❇✉ 1)❂(❇✉ + 1).

SLIDE 55 most cases ✉ ❀ ✈ ) + (✉2❀ ✈2) = ✉ ❀ ✈ ) where (✉3❀ ✈3) = ✕ ✉1✉2❀ ✕(✉1✉3)✈1)✿ ✉ ✻ ✉2, “addition” (alert!): ✕ ✈2 ✈1)❂(✉2 ✉1). cost 1I + 2M + 1S. ✉ ❀ ✈ ) = (✉2❀ ✈2) and ✈1 ✻= 0, “doubling” (alert!): ✕ ✉2
1 + 2❛2✉1 + ❛4)❂(2✈1).
cost 1I + 2M + 2S. handle some exceptions: ✉ ❀ ✈ ) = (✉2❀ ✈2); at ✶. Birational equivalence Starting from point (①❀ ②)
Define ❆ = 2(1 + ❞)❂(1 ❞), ❇ = 4❂(1 ❞); ✉ = (1 + ②)❂(❇(1 ②)), ✈ = ✉❂① = (1 + ②)❂(❇①(1 ②)). (Skip a few exceptional points.) ✈2 = ✉3 + (❆❂❇)✉2 + (1❂❇2)✉. Maps Edwards to Weierstrass. Compatible with point addition! Easily invert this map: ① = ✉❂✈, ② = (❇✉ 1)❂(❇✉ + 1). Some histo There ar elliptic-curve 1984 (published ECM, the
1984 (published and indep 1984 (published Elliptic-curve Bosma, Goldw Chudnovsky–Chudnovsky elliptic-curve

SLIDE 56 ✉ ❀ ✈ ✉ ❀ ✈2) = ✉ ❀ ✈ ✉3❀ ✈3) = ✕ ✉ ✉ ❀ ✕ ✉1✉3)✈1)✿ ✉ ✻ ✉ “addition” (alert!): ✕ ✈ ✈ ❂ ✉2 ✉1). 2M + 1S. ✉ ❀ ✈ ✉ ❀ ✈2) and ✈1 ✻= 0, (alert!): ✕ ✉ ❛ ✉1 + ❛4)❂(2✈1). 2M + 2S. some exceptions: ✉ ❀ ✈ ✉ ❀ ✈2); ✶ Birational equivalence Starting from point (①❀ ②)
Define ❆ = 2(1 + ❞)❂(1 ❞), ❇ = 4❂(1 ❞); ✉ = (1 + ②)❂(❇(1 ②)), ✈ = ✉❂① = (1 + ②)❂(❇①(1 ②)). (Skip a few exceptional points.) ✈2 = ✉3 + (❆❂❇)✉2 + (1❂❇2)✉. Maps Edwards to Weierstrass. Compatible with point addition! Easily invert this map: ① = ✉❂✈, ② = (❇✉ 1)❂(❇✉ + 1). Some history There are many persp elliptic-curve compu 1984 (published 1987) ECM, the elliptic-curve
1984 (published 1985) and independently 1984 (published 1987) Elliptic-curve cryptography Bosma, Goldwasser–Kilian, Chudnovsky–Chudnovsky elliptic-curve primalit

SLIDE 57 ✉ ❀ ✈ ✉ ❀ ✈ ✉ ❀ ✈ ✉ ❀ ✈ ✕ ✉ ✉ ❀ ✕ ✉ ✉ ✈1)✿ ✉ ✻ ✉ (alert!): ✕ ✈ ✈ ❂ ✉ ✉ ✉ ❀ ✈ ✉ ❀ ✈ ✈ ✻= 0, ✕ ✉ ❛ ✉ ❛ ❂(2✈1). exceptions: ✉ ❀ ✈ ✉ ❀ ✈ ✶ Birational equivalence Starting from point (①❀ ②)
Define ❆ = 2(1 + ❞)❂(1 ❞), ❇ = 4❂(1 ❞); ✉ = (1 + ②)❂(❇(1 ②)), ✈ = ✉❂① = (1 + ②)❂(❇①(1 ②)). (Skip a few exceptional points.) ✈2 = ✉3 + (❆❂❇)✉2 + (1❂❇2)✉. Maps Edwards to Weierstrass. Compatible with point addition! Easily invert this map: ① = ✉❂✈, ② = (❇✉ 1)❂(❇✉ + 1). Some history There are many perspectives elliptic-curve computations. 1984 (published 1987) Lenstra: ECM, the elliptic-curve metho
1984 (published 1985) Miller, and independently 1984 (published 1987) Koblitz: Elliptic-curve cryptography. Bosma, Goldwasser–Kilian, Chudnovsky–Chudnovsky, Atkin: elliptic-curve primality proving.

SLIDE 58 Birational equivalence Starting from point (①❀ ②)
Define ❆ = 2(1 + ❞)❂(1 ❞), ❇ = 4❂(1 ❞); ✉ = (1 + ②)❂(❇(1 ②)), ✈ = ✉❂① = (1 + ②)❂(❇①(1 ②)). (Skip a few exceptional points.) ✈2 = ✉3 + (❆❂❇)✉2 + (1❂❇2)✉. Maps Edwards to Weierstrass. Compatible with point addition! Easily invert this map: ① = ✉❂✈, ② = (❇✉ 1)❂(❇✉ + 1). Some history There are many perspectives on elliptic-curve computations. 1984 (published 1987) Lenstra: ECM, the elliptic-curve method
1984 (published 1985) Miller, and independently 1984 (published 1987) Koblitz: Elliptic-curve cryptography. Bosma, Goldwasser–Kilian, Chudnovsky–Chudnovsky, Atkin: elliptic-curve primality proving.

SLIDE 59 Birational equivalence rting from point (①❀ ②) ① + ②2 = 1 + ❞①2②2: ❆ = 2(1 + ❞)❂(1 ❞), ❇ ❂(1 ❞); ✉ + ②)❂(❇(1 ②)), ✈ ✉❂① = (1 + ②)❂(❇①(1 ②)). a few exceptional points.) ✈ ✉3 + (❆❂❇)✉2 + (1❂❇2)✉. Edwards to Weierstrass. Compatible with point addition! invert this map: ① ✉❂✈, ② = (❇✉ 1)❂(❇✉ + 1). Some history There are many perspectives on elliptic-curve computations. 1984 (published 1987) Lenstra: ECM, the elliptic-curve method
1984 (published 1985) Miller, and independently 1984 (published 1987) Koblitz: Elliptic-curve cryptography. Bosma, Goldwasser–Kilian, Chudnovsky–Chudnovsky, Atkin: elliptic-curve primality proving. The Edw 1761 Euler, introduced for ①2 + ② ① ② the “lemniscatic 2007 Edw many curves ① ② ❝ ① ② Theorem: all elliptic 2007 Bernstein–Lange: Edwards for ①2 + ② ❞① ② ❞ ✻ and gives

SLIDE 60 equivalence
① ② + ❞①2②2: ❆ + ❞)❂(1 ❞), ❇ ❂ ❞ ✉ ② ❂ ❇(1 ②)), ✈ ✉❂① ②)❂(❇①(1 ②)). exceptional points.) ✈ ✉ ❆❂❇)✉2 + (1❂❇2)✉. to Weierstrass. point addition! map: ① ✉❂✈ ② ❇✉ 1)❂(❇✉ + 1). Some history There are many perspectives on elliptic-curve computations. 1984 (published 1987) Lenstra: ECM, the elliptic-curve method
1984 (published 1985) Miller, and independently 1984 (published 1987) Koblitz: Elliptic-curve cryptography. Bosma, Goldwasser–Kilian, Chudnovsky–Chudnovsky, Atkin: elliptic-curve primality proving. The Edwards persp 1761 Euler, 1866 Gauss introduced an addition for ①2 + ②2 = 1 ① ② the “lemniscatic elliptic 2007 Edwards generalized many curves ①2+② ❝ ① ② Theorem: have no all elliptic curves over 2007 Bernstein–Lange: Edwards addition la for ①2 + ②2 = 1 + ❞① ② ❞ ✻ and gives new ECC

SLIDE 61 ①❀ ② ① ② ❞① ② ❆ ❞ ❂ ❞), ❇ ❂ ❞ ✉ ② ❂ ❇ ② ✈ ✉❂① ② ❂ ❇① ②)).
✈ ✉ ❆❂❇ ✉ ❂❇2)✉. ierstrass. addition! ① ✉❂✈ ② ❇✉ ❂ ❇✉ + 1). Some history There are many perspectives on elliptic-curve computations. 1984 (published 1987) Lenstra: ECM, the elliptic-curve method
1984 (published 1985) Miller, and independently 1984 (published 1987) Koblitz: Elliptic-curve cryptography. Bosma, Goldwasser–Kilian, Chudnovsky–Chudnovsky, Atkin: elliptic-curve primality proving. The Edwards perspective is new! 1761 Euler, 1866 Gauss introduced an addition law for ①2 + ②2 = 1 ①2②2, the “lemniscatic elliptic curve.” 2007 Edwards generalized to many curves ①2+②2 = 1+❝4① ② Theorem: have now obtained all elliptic curves over Q. 2007 Bernstein–Lange: Edwards addition law is complete for ①2 + ②2 = 1 + ❞①2②2 if ❞ ✻ and gives new ECC speed reco

SLIDE 62 Some history There are many perspectives on elliptic-curve computations. 1984 (published 1987) Lenstra: ECM, the elliptic-curve method
1984 (published 1985) Miller, and independently 1984 (published 1987) Koblitz: Elliptic-curve cryptography. Bosma, Goldwasser–Kilian, Chudnovsky–Chudnovsky, Atkin: elliptic-curve primality proving. The Edwards perspective is new! 1761 Euler, 1866 Gauss introduced an addition law for ①2 + ②2 = 1 ①2②2, the “lemniscatic elliptic curve.” 2007 Edwards generalized to many curves ①2+②2 = 1+❝4①2②2. Theorem: have now obtained all elliptic curves over Q. 2007 Bernstein–Lange: Edwards addition law is complete for ①2 + ②2 = 1 + ❞①2②2 if ❞ ✻= ; and gives new ECC speed records.

SLIDE 63
history are many perspectives on elliptic-curve computations. (published 1987) Lenstra: the elliptic-curve method factoring integers. (published 1985) Miller, independently (published 1987) Koblitz: Elliptic-curve cryptography. Bosma, Goldwasser–Kilian, Chudnovsky–Chudnovsky, Atkin: elliptic-curve primality proving. The Edwards perspective is new! 1761 Euler, 1866 Gauss introduced an addition law for ①2 + ②2 = 1 ①2②2, the “lemniscatic elliptic curve.” 2007 Edwards generalized to many curves ①2+②2 = 1+❝4①2②2. Theorem: have now obtained all elliptic curves over Q. 2007 Bernstein–Lange: Edwards addition law is complete for ①2 + ②2 = 1 + ❞①2②2 if ❞ ✻= ; and gives new ECC speed records. Representing Crypto 1985, elliptic curves Given ♥ ✷ P ✷ ❊
q
division-p computes ♥P ✷ ❊
q
“in 26 log ♥ but can “It appea represent in the follo Each point triple (①❀ ②❀ ③ to the point ①❂③ ❀ ②❂③

SLIDE 64
perspectives on putations. 1987) Lenstra: elliptic-curve method integers. 1985) Miller, endently 1987) Koblitz: cryptography. ser–Kilian, Chudnovsky–Chudnovsky, Atkin: rimality proving. The Edwards perspective is new! 1761 Euler, 1866 Gauss introduced an addition law for ①2 + ②2 = 1 ①2②2, the “lemniscatic elliptic curve.” 2007 Edwards generalized to many curves ①2+②2 = 1+❝4①2②2. Theorem: have now obtained all elliptic curves over Q. 2007 Bernstein–Lange: Edwards addition law is complete for ①2 + ②2 = 1 + ❞①2②2 if ❞ ✻= ; and gives new ECC speed records. Representing curve Crypto 1985, Miller, elliptic curves in cryptography”: Given ♥ ✷ Z, P ✷ ❊
q
division-polynomial computes ♥P ✷ ❊
q
“in 26 log2 ♥ multiplications”; but can do better! “It appears to be b represent the points in the following form: Each point is represented triple (①❀ ②❀ ③) which to the point (①❂③2❀ ②❂③

SLIDE 65
ectives on tations. Lenstra: method Miller, Koblitz: cryptography. ser–Kilian, Atkin: roving. The Edwards perspective is new! 1761 Euler, 1866 Gauss introduced an addition law for ①2 + ②2 = 1 ①2②2, the “lemniscatic elliptic curve.” 2007 Edwards generalized to many curves ①2+②2 = 1+❝4①2②2. Theorem: have now obtained all elliptic curves over Q. 2007 Bernstein–Lange: Edwards addition law is complete for ①2 + ②2 = 1 + ❞①2②2 if ❞ ✻= ; and gives new ECC speed records. Representing curve points Crypto 1985, Miller, “Use of elliptic curves in cryptography”: Given ♥ ✷ Z, P ✷ ❊(Fq), division-polynomial recurrence computes ♥P ✷ ❊(Fq) “in 26 log2 ♥ multiplications”; but can do better! “It appears to be best to represent the points on the curve in the following form: Each point is represented by triple (①❀ ②❀ ③) which corresp to the point (①❂③2❀ ②❂③3).”

SLIDE 66
The Edwards perspective is new! 1761 Euler, 1866 Gauss introduced an addition law for ①2 + ②2 = 1 ①2②2, the “lemniscatic elliptic curve.” 2007 Edwards generalized to many curves ①2+②2 = 1+❝4①2②2. Theorem: have now obtained all elliptic curves over Q. 2007 Bernstein–Lange: Edwards addition law is complete for ①2 + ②2 = 1 + ❞①2②2 if ❞ ✻= ; and gives new ECC speed records. Representing curve points Crypto 1985, Miller, “Use of elliptic curves in cryptography”: Given ♥ ✷ Z, P ✷ ❊(Fq), division-polynomial recurrence computes ♥P ✷ ❊(Fq) “in 26 log2 ♥ multiplications”; but can do better! “It appears to be best to represent the points on the curve in the following form: Each point is represented by the triple (①❀ ②❀ ③) which corresponds to the point (①❂③2❀ ②❂③3).”

SLIDE 67 Edwards perspective is new! Euler, 1866 Gauss duced an addition law ① + ②2 = 1 ①2②2, “lemniscatic elliptic curve.” Edwards generalized to curves ①2+②2 = 1+❝4①2②2. rem: have now obtained elliptic curves over Q. Bernstein–Lange: rds addition law is complete ① + ②2 = 1 + ❞①2②2 if ❞ ✻= ; gives new ECC speed records. Representing curve points Crypto 1985, Miller, “Use of elliptic curves in cryptography”: Given ♥ ✷ Z, P ✷ ❊(Fq), division-polynomial recurrence computes ♥P ✷ ❊(Fq) “in 26 log2 ♥ multiplications”; but can do better! “It appears to be best to represent the points on the curve in the following form: Each point is represented by the triple (①❀ ②❀ ③) which corresponds to the point (①❂③2❀ ②❂③3).” 1986 Chudnovsky–Chudnovsky “Sequences generated in formal and new and facto “The crucial the choice
where com ♣ are the least Most imp ADD is P❀ ◗ ✼✦ P ◗ DBL is P ✼✦ P

SLIDE 68 erspective is new! 1866 Gauss addition law ① ② ①2②2, elliptic curve.” generalized to ① +②2 = 1+❝4①2②2. now obtained
Bernstein–Lange: addition law is complete ① ② + ❞①2②2 if ❞ ✻= ; ECC speed records. Representing curve points Crypto 1985, Miller, “Use of elliptic curves in cryptography”: Given ♥ ✷ Z, P ✷ ❊(Fq), division-polynomial recurrence computes ♥P ✷ ❊(Fq) “in 26 log2 ♥ multiplications”; but can do better! “It appears to be best to represent the points on the curve in the following form: Each point is represented by the triple (①❀ ②❀ ③) which corresponds to the point (①❂③2❀ ②❂③3).” 1986 Chudnovsky–Chudnovsky “Sequences of numb generated by addition in formal groups and new primality and factorization tests”: “The crucial problem the choice of the mo
where computations ♣ are the least time Most important computations: ADD is P❀ ◗ ✼✦ P ◗ DBL is P ✼✦ 2P.

SLIDE 69 is new! ① ② ① ② curve.” to ① ② ❝4①2②2.
complete ① ② ❞① ② if ❞ ✻= ; records. Representing curve points Crypto 1985, Miller, “Use of elliptic curves in cryptography”: Given ♥ ✷ Z, P ✷ ❊(Fq), division-polynomial recurrence computes ♥P ✷ ❊(Fq) “in 26 log2 ♥ multiplications”; but can do better! “It appears to be best to represent the points on the curve in the following form: Each point is represented by the triple (①❀ ②❀ ③) which corresponds to the point (①❂③2❀ ②❂③3).” 1986 Chudnovsky–Chudnovsky “Sequences of numbers generated by addition in formal groups and new primality and factorization tests”: “The crucial problem becomes the choice of the model
- f an algebraic group variety
where computations mod ♣ are the least time consuming.” Most important computations: ADD is P❀ ◗ ✼✦ P + ◗. DBL is P ✼✦ 2P.

SLIDE 70 Representing curve points Crypto 1985, Miller, “Use of elliptic curves in cryptography”: Given ♥ ✷ Z, P ✷ ❊(Fq), division-polynomial recurrence computes ♥P ✷ ❊(Fq) “in 26 log2 ♥ multiplications”; but can do better! “It appears to be best to represent the points on the curve in the following form: Each point is represented by the triple (①❀ ②❀ ③) which corresponds to the point (①❂③2❀ ②❂③3).” 1986 Chudnovsky–Chudnovsky, “Sequences of numbers generated by addition in formal groups and new primality and factorization tests”: “The crucial problem becomes the choice of the model
- f an algebraic group variety,
where computations mod ♣ are the least time consuming.” Most important computations: ADD is P❀ ◗ ✼✦ P + ◗. DBL is P ✼✦ 2P.

SLIDE 71 resenting curve points 1985, Miller, “Use of curves in cryptography”: ♥ ✷ Z, P ✷ ❊(Fq), division-polynomial recurrence computes ♥P ✷ ❊(Fq) log2 ♥ multiplications”; can do better! appears to be best to resent the points on the curve following form:
- int is represented by the
(①❀ ②❀ ③) which corresponds point (①❂③2❀ ②❂③3).” 1986 Chudnovsky–Chudnovsky, “Sequences of numbers generated by addition in formal groups and new primality and factorization tests”: “The crucial problem becomes the choice of the model
- f an algebraic group variety,
where computations mod ♣ are the least time consuming.” Most important computations: ADD is P❀ ◗ ✼✦ P + ◗. DBL is P ✼✦ 2P. “It is preferable models of lying in lo for other coordinates increasing. ✿ ✿ ✿ 4 basic mo Short W ②2 = ①3 ❛① ❜ Jacobi intersection: s2 + ❝2 = ❛s ❞ Jacobi qua ② ① ❛① Hessian: ① ② ❞①②

SLIDE 72 curve points Miller, “Use of cryptography”: ♥ ✷ P ✷ ❊(Fq),
♥P ✷ ❊(Fq) ♥ multiplications”; etter! e best to
form: represented by the ①❀ ②❀ ③ which corresponds ①❂③2❀ ②❂③3).” 1986 Chudnovsky–Chudnovsky, “Sequences of numbers generated by addition in formal groups and new primality and factorization tests”: “The crucial problem becomes the choice of the model
- f an algebraic group variety,
where computations mod ♣ are the least time consuming.” Most important computations: ADD is P❀ ◗ ✼✦ P + ◗. DBL is P ✼✦ 2P. “It is preferable to models of elliptic curves lying in low-dimensional for otherwise the numb coordinates and op
✿ ✿ ✿ 4 basic models of elliptic Short Weierstrass: ②2 = ①3 + ❛① + ❜. Jacobi intersection: s2 + ❝2 = 1, ❛s2 + ❞ Jacobi quartic: ②2 ① ❛① Hessian: ①3 + ②3 + ❞①②

SLIDE 73
cryptography”: ♥ ✷ P ✷ ❊
q
recurrence ♥P ✷ ❊
q
♥ multiplications”; the curve by the ①❀ ②❀ ③ rresponds ①❂③ ❀ ②❂③ ).” 1986 Chudnovsky–Chudnovsky, “Sequences of numbers generated by addition in formal groups and new primality and factorization tests”: “The crucial problem becomes the choice of the model
- f an algebraic group variety,
where computations mod ♣ are the least time consuming.” Most important computations: ADD is P❀ ◗ ✼✦ P + ◗. DBL is P ✼✦ 2P. “It is preferable to use models of elliptic curves lying in low-dimensional spaces, for otherwise the number of coordinates and operations is
- increasing. This limits us ✿ ✿ ✿
4 basic models of elliptic curves.” Short Weierstrass: ②2 = ①3 + ❛① + ❜. Jacobi intersection: s2 + ❝2 = 1, ❛s2 + ❞2 = 1. Jacobi quartic: ②2 = ①4+2❛① Hessian: ①3 + ②3 + 1 = 3❞①②

SLIDE 74 1986 Chudnovsky–Chudnovsky, “Sequences of numbers generated by addition in formal groups and new primality and factorization tests”: “The crucial problem becomes the choice of the model
- f an algebraic group variety,
where computations mod ♣ are the least time consuming.” Most important computations: ADD is P❀ ◗ ✼✦ P + ◗. DBL is P ✼✦ 2P. “It is preferable to use models of elliptic curves lying in low-dimensional spaces, for otherwise the number of coordinates and operations is
- increasing. This limits us ✿ ✿ ✿ to
4 basic models of elliptic curves.” Short Weierstrass: ②2 = ①3 + ❛① + ❜. Jacobi intersection: s2 + ❝2 = 1, ❛s2 + ❞2 = 1. Jacobi quartic: ②2 = ①4+2❛①2+1. Hessian: ①3 + ②3 + 1 = 3❞①②.

SLIDE 75 Chudnovsky–Chudnovsky, “Sequences of numbers generated by addition al groups new primality factorization tests”: crucial problem becomes choice of the model algebraic group variety, computations mod ♣ the least time consuming.” important computations: is P❀ ◗ ✼✦ P + ◗. is P ✼✦ 2P. “It is preferable to use models of elliptic curves lying in low-dimensional spaces, for otherwise the number of coordinates and operations is
- increasing. This limits us ✿ ✿ ✿ to
4 basic models of elliptic curves.” Short Weierstrass: ②2 = ①3 + ❛① + ❜. Jacobi intersection: s2 + ❝2 = 1, ❛s2 + ❞2 = 1. Jacobi quartic: ②2 = ①4+2❛①2+1. Hessian: ①3 + ②3 + 1 = 3❞①②. Optimizing For “traditional” ❳❂❩ ❀ ❨❂❩
❛① ❜ 1986 Chudnovsky–Chudnovsky state explicit 10M for Consequence: ✙ ✒ 10 lg ♥ ♥ ♥ ✓ to compute ♥❀ P ✼✦ ♥P using sliding-windo
Notation:

SLIDE 76 Chudnovsky–Chudnovsky, numbers addition rimality tests”: roblem becomes the model group variety, utations mod ♣ time consuming.” computations: P❀ ◗ ✼✦ P + ◗. P ✼✦ P. “It is preferable to use models of elliptic curves lying in low-dimensional spaces, for otherwise the number of coordinates and operations is
- increasing. This limits us ✿ ✿ ✿ to
4 basic models of elliptic curves.” Short Weierstrass: ②2 = ①3 + ❛① + ❜. Jacobi intersection: s2 + ❝2 = 1, ❛s2 + ❞2 = 1. Jacobi quartic: ②2 = ①4+2❛①2+1. Hessian: ①3 + ②3 + 1 = 3❞①②. Optimizing Jacobian For “traditional” (❳❂❩ ❀ ❨❂❩
1986 Chudnovsky–Chudnovsky state explicit formulas 10M for DBL; 16M Consequence: ✙ ✒ 10 lg ♥ + 16 lg ♥ lg ♥ ✓ to compute ♥❀ P ✼✦ ♥P using sliding-windo
Notation: lg = log

SLIDE 77 Chudnovsky–Chudnovsky, ecomes riety, ♣ consuming.” computations: P❀ ◗ ✼✦ P ◗ P ✼✦ P “It is preferable to use models of elliptic curves lying in low-dimensional spaces, for otherwise the number of coordinates and operations is
- increasing. This limits us ✿ ✿ ✿ to
4 basic models of elliptic curves.” Short Weierstrass: ②2 = ①3 + ❛① + ❜. Jacobi intersection: s2 + ❝2 = 1, ❛s2 + ❞2 = 1. Jacobi quartic: ②2 = ①4+2❛①2+1. Hessian: ①3 + ②3 + 1 = 3❞①②. Optimizing Jacobian coordina For “traditional” (❳❂❩2❀ ❨❂❩
1986 Chudnovsky–Chudnovsky state explicit formulas using 10M for DBL; 16M for ADD. Consequence: ✙ ✒ 10 lg ♥ + 16 lg ♥ lg lg ♥ ✓ M to compute ♥❀ P ✼✦ ♥P using sliding-windows metho
Notation: lg = log2.

SLIDE 78 “It is preferable to use models of elliptic curves lying in low-dimensional spaces, for otherwise the number of coordinates and operations is
- increasing. This limits us ✿ ✿ ✿ to
4 basic models of elliptic curves.” Short Weierstrass: ②2 = ①3 + ❛① + ❜. Jacobi intersection: s2 + ❝2 = 1, ❛s2 + ❞2 = 1. Jacobi quartic: ②2 = ①4+2❛①2+1. Hessian: ①3 + ②3 + 1 = 3❞①②. Optimizing Jacobian coordinates For “traditional” (❳❂❩2❀ ❨❂❩3)
1986 Chudnovsky–Chudnovsky state explicit formulas using 10M for DBL; 16M for ADD. Consequence: ✙ ✒ 10 lg ♥ + 16 lg ♥ lg lg ♥ ✓ M to compute ♥❀ P ✼✦ ♥P using sliding-windows method
Notation: lg = log2.

SLIDE 79 preferable to use dels of elliptic curves in low-dimensional spaces, erwise the number of rdinates and operations is
- increasing. This limits us ✿ ✿ ✿ to
basic models of elliptic curves.” Weierstrass: ② ①3 + ❛① + ❜. intersection: s ❝ = 1, ❛s2 + ❞2 = 1. quartic: ②2 = ①4+2❛①2+1. Hessian: ①3 + ②3 + 1 = 3❞①②. Optimizing Jacobian coordinates For “traditional” (❳❂❩2❀ ❨❂❩3)
1986 Chudnovsky–Chudnovsky state explicit formulas using 10M for DBL; 16M for ADD. Consequence: ✙ ✒ 10 lg ♥ + 16 lg ♥ lg lg ♥ ✓ M to compute ♥❀ P ✼✦ ♥P using sliding-windows method
Notation: lg = log2. Squaring Here are ❙ = 4❳ ✁ ❨ ▼ = 3❳ ❛❩ ❚ = ▼ ❙ ❳3 = ❚ ❨3 = ▼ ✁ ❙ ❚ ❨ ❩3 = 2❨ ✁ ❩ Total cost S is the
q
D is the ❛ The squa ❳2
1❀ ❨ 2 1 ❀ ❨ ❀ ❩ ❀ ❩ ❀ ▼

SLIDE 80 to use liptic curves w-dimensional spaces, the number of
limits us ✿ ✿ ✿ to
eierstrass: ② ① ❛① ❜. intersection: s ❝ ❛s + ❞2 = 1. ②2 = ①4+2❛①2+1. ① ② + 1 = 3❞①②. Optimizing Jacobian coordinates For “traditional” (❳❂❩2❀ ❨❂❩3)
1986 Chudnovsky–Chudnovsky state explicit formulas using 10M for DBL; 16M for ADD. Consequence: ✙ ✒ 10 lg ♥ + 16 lg ♥ lg lg ♥ ✓ M to compute ♥❀ P ✼✦ ♥P using sliding-windows method
Notation: lg = log2. Squaring is faster than Here are the DBL ❙ = 4❳1 ✁ ❨ 2
1 ;
▼ = 3❳2
1 + ❛❩4 1
❚ = ▼2 2❙; ❳3 = ❚; ❨3 = ▼ ✁ (❙ ❚ ❨ ❩3 = 2❨1 ✁ ❩1. Total cost 3M + 6 S is the cost of squa
q
D is the cost of multiplying ❛ The squarings produce ❳2
1❀ ❨ 2 1 ❀ ❨ 4 1 ❀ ❩2 1❀ ❩4 1❀ ▼

SLIDE 81 spaces,
erations is ✿ ✿ ✿ to curves.” ② ① ❛① ❜ s ❝ ❛s ❞ 1. ② ① 2❛①2+1. ① ② ❞①②. Optimizing Jacobian coordinates For “traditional” (❳❂❩2❀ ❨❂❩3)
1986 Chudnovsky–Chudnovsky state explicit formulas using 10M for DBL; 16M for ADD. Consequence: ✙ ✒ 10 lg ♥ + 16 lg ♥ lg lg ♥ ✓ M to compute ♥❀ P ✼✦ ♥P using sliding-windows method
Notation: lg = log2. Squaring is faster than M. Here are the DBL formulas: ❙ = 4❳1 ✁ ❨ 2
1 ;
▼ = 3❳2
1 + ❛❩4 1;
❚ = ▼2 2❙; ❳3 = ❚; ❨3 = ▼ ✁ (❙ ❚) 8❨ 4
1 ;
❩3 = 2❨1 ✁ ❩1. Total cost 3M + 6S + 1D where S is the cost of squaring in Fq D is the cost of multiplying ❛ The squarings produce ❳2
1❀ ❨ 2 1 ❀ ❨ 4 1 ❀ ❩2 1❀ ❩4 1❀ ▼2.

SLIDE 82 Optimizing Jacobian coordinates For “traditional” (❳❂❩2❀ ❨❂❩3)
1986 Chudnovsky–Chudnovsky state explicit formulas using 10M for DBL; 16M for ADD. Consequence: ✙ ✒ 10 lg ♥ + 16 lg ♥ lg lg ♥ ✓ M to compute ♥❀ P ✼✦ ♥P using sliding-windows method
Notation: lg = log2. Squaring is faster than M. Here are the DBL formulas: ❙ = 4❳1 ✁ ❨ 2
1 ;
▼ = 3❳2
1 + ❛❩4 1;
❚ = ▼2 2❙; ❳3 = ❚; ❨3 = ▼ ✁ (❙ ❚) 8❨ 4
1 ;
❩3 = 2❨1 ✁ ❩1. Total cost 3M + 6S + 1D where S is the cost of squaring in Fq, D is the cost of multiplying by ❛. The squarings produce ❳2
1❀ ❨ 2 1 ❀ ❨ 4 1 ❀ ❩2 1❀ ❩4 1❀ ▼2.

SLIDE 83 Optimizing Jacobian coordinates “traditional” (❳❂❩2❀ ❨❂❩3) ② = ①3 + ❛① + ❜: Chudnovsky–Chudnovsky explicit formulas using for DBL; 16M for ADD. Consequence: ✙ ✒ lg ♥ + 16 lg ♥ lg lg ♥ ✓ M compute ♥❀ P ✼✦ ♥P sliding-windows method scalar multiplication. Notation: lg = log2. Squaring is faster than M. Here are the DBL formulas: ❙ = 4❳1 ✁ ❨ 2
1 ;
▼ = 3❳2
1 + ❛❩4 1;
❚ = ▼2 2❙; ❳3 = ❚; ❨3 = ▼ ✁ (❙ ❚) 8❨ 4
1 ;
❩3 = 2❨1 ✁ ❩1. Total cost 3M + 6S + 1D where S is the cost of squaring in Fq, D is the cost of multiplying by ❛. The squarings produce ❳2
1❀ ❨ 2 1 ❀ ❨ 4 1 ❀ ❩2 1❀ ❩4 1❀ ▼2.
Most ECC curves that Curve-choice 1986 Chudnovsky–Chudnovsky: Can eliminate by choosing ❛ But “it is to choose ❛
▼ ❳ ❩ = 3(❳1 ❩ ✁ ❳ ❩ Replace Now DBL

SLIDE 84 Jacobian coordinates (❳❂❩2❀ ❨❂❩3) ② ① ❛① + ❜: Chudnovsky–Chudnovsky rmulas using 16M for ADD. ✙ ✒ ♥ lg ♥ lg lg ♥ ✓ M ♥❀ P ✼✦ ♥P sliding-windows method multiplication. log2. Squaring is faster than M. Here are the DBL formulas: ❙ = 4❳1 ✁ ❨ 2
1 ;
▼ = 3❳2
1 + ❛❩4 1;
❚ = ▼2 2❙; ❳3 = ❚; ❨3 = ▼ ✁ (❙ ❚) 8❨ 4
1 ;
❩3 = 2❨1 ✁ ❩1. Total cost 3M + 6S + 1D where S is the cost of squaring in Fq, D is the cost of multiplying by ❛. The squarings produce ❳2
1❀ ❨ 2 1 ❀ ❨ 4 1 ❀ ❩2 1❀ ❩4 1❀ ▼2.
Most ECC standards curves that make fo Curve-choice advice 1986 Chudnovsky–Chudnovsky: Can eliminate the by choosing curve ❛ But “it is even sma to choose curve with ❛
❳ ❩ = 3(❳1 ❩2
1) ✁ (❳
❩ Replace 2S with 1M Now DBL costs 4M

SLIDE 85
rdinates ❳❂❩ ❀ ❨❂❩3) ② ① ❛① ❜ Chudnovsky–Chudnovsky using ADD. ✙ ✒ ♥ ♥ ♥ ✓ ♥❀ P ✼✦ ♥P method Squaring is faster than M. Here are the DBL formulas: ❙ = 4❳1 ✁ ❨ 2
1 ;
▼ = 3❳2
1 + ❛❩4 1;
❚ = ▼2 2❙; ❳3 = ❚; ❨3 = ▼ ✁ (❙ ❚) 8❨ 4
1 ;
❩3 = 2❨1 ✁ ❩1. Total cost 3M + 6S + 1D where S is the cost of squaring in Fq, D is the cost of multiplying by ❛. The squarings produce ❳2
1❀ ❨ 2 1 ❀ ❨ 4 1 ❀ ❩2 1❀ ❩4 1❀ ▼2.
Most ECC standards choose curves that make formulas faster. Curve-choice advice from 1986 Chudnovsky–Chudnovsky: Can eliminate the 1D by choosing curve with ❛ = But “it is even smarter” to choose curve with ❛ = 3. If ❛ = 3 then ▼ = 3(❳2
1 ❩
= 3(❳1 ❩2
1) ✁ (❳1 + ❩2 1).
Replace 2S with 1M. Now DBL costs 4M + 4S.

SLIDE 86
Squaring is faster than M. Here are the DBL formulas: ❙ = 4❳1 ✁ ❨ 2
1 ;
▼ = 3❳2
1 + ❛❩4 1;
❚ = ▼2 2❙; ❳3 = ❚; ❨3 = ▼ ✁ (❙ ❚) 8❨ 4
1 ;
❩3 = 2❨1 ✁ ❩1. Total cost 3M + 6S + 1D where S is the cost of squaring in Fq, D is the cost of multiplying by ❛. The squarings produce ❳2
1❀ ❨ 2 1 ❀ ❨ 4 1 ❀ ❩2 1❀ ❩4 1❀ ▼2.
Most ECC standards choose curves that make formulas faster. Curve-choice advice from 1986 Chudnovsky–Chudnovsky: Can eliminate the 1D by choosing curve with ❛ = 1. But “it is even smarter” to choose curve with ❛ = 3. If ❛ = 3 then ▼ = 3(❳2
1 ❩4 1)
= 3(❳1 ❩2
1) ✁ (❳1 + ❩2 1).
Replace 2S with 1M. Now DBL costs 4M + 4S.

SLIDE 87 ring is faster than M. re the DBL formulas: ❙ 4❳1 ✁ ❨ 2
1 ;
▼ 3❳2
1 + ❛❩4 1;
❚ ▼2 2❙; ❳ = ❚; ❨ ▼ ✁ (❙ ❚) 8❨ 4
1 ;
❩ 2❨1 ✁ ❩1. cost 3M + 6S + 1D where the cost of squaring in Fq, the cost of multiplying by ❛. squarings produce ❳ ❀ ❨ ❀ ❨ 4
1 ❀ ❩2 1❀ ❩4 1❀ ▼2.
Most ECC standards choose curves that make formulas faster. Curve-choice advice from 1986 Chudnovsky–Chudnovsky: Can eliminate the 1D by choosing curve with ❛ = 1. But “it is even smarter” to choose curve with ❛ = 3. If ❛ = 3 then ▼ = 3(❳2
1 ❩4 1)
= 3(❳1 ❩2
1) ✁ (❳1 + ❩2 1).
Replace 2S with 1M. Now DBL costs 4M + 4S. 2001 Bernstein: 3M + 5S 11M + 5 How? Easy
❨ ✁ ❩ compute ❨ ❩ ❨ ❩ DBL form computing ❨ ❩ Same idea but have ❳❀ ❨❀ ❩ to eliminate

SLIDE 88
faster than M. DBL formulas: ❙ ❳ ✁ ❨ ; ▼ ❳ ❛❩4
1;
❚ ▼ ❙; ❳ ❚ ❨ ▼ ✁ ❙ ❚) 8❨ 4
1 ;
❩ ❨ ✁ ❩ . 6S + 1D where squaring in Fq, multiplying by ❛. roduce ❳ ❀ ❨ ❀ ❨ ❀ ❩ ❀ ❩4
1❀ ▼2.
Most ECC standards choose curves that make formulas faster. Curve-choice advice from 1986 Chudnovsky–Chudnovsky: Can eliminate the 1D by choosing curve with ❛ = 1. But “it is even smarter” to choose curve with ❛ = 3. If ❛ = 3 then ▼ = 3(❳2
1 ❩4 1)
= 3(❳1 ❩2
1) ✁ (❳1 + ❩2 1).
Replace 2S with 1M. Now DBL costs 4M + 4S. 2001 Bernstein: 3M + 5S for DBL. 11M + 5S for ADD. How? Easy S M instead of computing ❨ ✁ ❩ compute (❨1 + ❩1) ❨ ❩ DBL formulas were computing ❨ 2
1 and ❩
Same idea for the but have to scale ❳❀ ❨❀ ❩ to eliminate divisions

SLIDE 89
. rmulas: ❙ ❳ ✁ ❨ ▼ ❳ ❛❩ ❚ ▼ ❙ ❳ ❚ ❨ ▼ ✁ ❙ ❚ ❨ ; ❩ ❨ ✁ ❩ where in Fq, multiplying by ❛. ❳ ❀ ❨ ❀ ❨ ❀ ❩ ❀ ❩ ❀ ▼ Most ECC standards choose curves that make formulas faster. Curve-choice advice from 1986 Chudnovsky–Chudnovsky: Can eliminate the 1D by choosing curve with ❛ = 1. But “it is even smarter” to choose curve with ❛ = 3. If ❛ = 3 then ▼ = 3(❳2
1 ❩4 1)
= 3(❳1 ❩2
1) ✁ (❳1 + ❩2 1).
Replace 2S with 1M. Now DBL costs 4M + 4S. 2001 Bernstein: 3M + 5S for DBL. 11M + 5S for ADD. How? Easy S M tradeoff: instead of computing 2❨1 ✁ ❩ compute (❨1 + ❩1)2 ❨ 2
1 ❩
DBL formulas were already computing ❨ 2
1 and ❩2 1.
Same idea for the ADD formulas, but have to scale ❳❀ ❨❀ ❩ to eliminate divisions by 2.

SLIDE 90
Most ECC standards choose curves that make formulas faster. Curve-choice advice from 1986 Chudnovsky–Chudnovsky: Can eliminate the 1D by choosing curve with ❛ = 1. But “it is even smarter” to choose curve with ❛ = 3. If ❛ = 3 then ▼ = 3(❳2
1 ❩4 1)
= 3(❳1 ❩2
1) ✁ (❳1 + ❩2 1).
Replace 2S with 1M. Now DBL costs 4M + 4S. 2001 Bernstein: 3M + 5S for DBL. 11M + 5S for ADD. How? Easy S M tradeoff: instead of computing 2❨1 ✁ ❩1, compute (❨1 + ❩1)2 ❨ 2
1 ❩2 1.
DBL formulas were already computing ❨ 2
1 and ❩2 1.
Same idea for the ADD formulas, but have to scale ❳❀ ❨❀ ❩ to eliminate divisions by 2.

SLIDE 91 ECC standards choose that make formulas faster. Curve-choice advice from Chudnovsky–Chudnovsky: eliminate the 1D
“it is even smarter”
❛ 3 then ▼ = 3(❳2
1 ❩4 1)
❳1 ❩2
1) ✁ (❳1 + ❩2 1).
Replace 2S with 1M. DBL costs 4M + 4S. 2001 Bernstein: 3M + 5S for DBL. 11M + 5S for ADD. How? Easy S M tradeoff: instead of computing 2❨1 ✁ ❩1, compute (❨1 + ❩1)2 ❨ 2
1 ❩2 1.
DBL formulas were already computing ❨ 2
1 and ❩2 1.
Same idea for the ADD formulas, but have to scale ❳❀ ❨❀ ❩ to eliminate divisions by 2. ADD for ② ① ❛① ❜ ❯1 = ❳1❩ ❯ ❳ ❩ ❙1 = ❨1❩ ❙ ❨ ❩ many mo 1986 Chudnovsky–Chudnovsky: “We suggest addition (❳❀ ❨❀ ❩❀ ❩ ❀ ❩ Disadvantages: Allocate ❩ ❀ ❩ Pay 1S+ Advantages: Save 2S Save 1S

SLIDE 92 standards choose e formulas faster. advice from Chudnovsky–Chudnovsky: the 1D curve with ❛ = 1. smarter” with ❛ = 3. ❛
1 ❩4 1)
❳ ❩ ✁ (❳1 + ❩2
1).
1M. 4M + 4S. 2001 Bernstein: 3M + 5S for DBL. 11M + 5S for ADD. How? Easy S M tradeoff: instead of computing 2❨1 ✁ ❩1, compute (❨1 + ❩1)2 ❨ 2
1 ❩2 1.
DBL formulas were already computing ❨ 2
1 and ❩2 1.
Same idea for the ADD formulas, but have to scale ❳❀ ❨❀ ❩ to eliminate divisions by 2. ADD for ②2 = ①3 + ❛① ❜ ❯1 = ❳1❩2
2, ❯2 = ❳ ❩
❙1 = ❨1❩3
2, ❙2 = ❨ ❩
many more computations. 1986 Chudnovsky–Chudnovsky: “We suggest to write addition formulas involving (❳❀ ❨❀ ❩❀ ❩2❀ ❩3).” Disadvantages: Allocate space for ❩ ❀ ❩ Pay 1S+1M in ADD Advantages: Save 2S + 2M at sta Save 1S at start of

SLIDE 93
faster. Chudnovsky–Chudnovsky: ❛ = 1. ❛ 3. ❛
❳ ❩4
1)
❳ ❩ ✁ ❳ ❩ ). 2001 Bernstein: 3M + 5S for DBL. 11M + 5S for ADD. How? Easy S M tradeoff: instead of computing 2❨1 ✁ ❩1, compute (❨1 + ❩1)2 ❨ 2
1 ❩2 1.
DBL formulas were already computing ❨ 2
1 and ❩2 1.
Same idea for the ADD formulas, but have to scale ❳❀ ❨❀ ❩ to eliminate divisions by 2. ADD for ②2 = ①3 + ❛① + ❜: ❯1 = ❳1❩2
2, ❯2 = ❳2❩2 1,
❙1 = ❨1❩3
2, ❙2 = ❨2❩3 1,
many more computations. 1986 Chudnovsky–Chudnovsky: “We suggest to write addition formulas involving (❳❀ ❨❀ ❩❀ ❩2❀ ❩3).” Disadvantages: Allocate space for ❩2❀ ❩3. Pay 1S+1M in ADD and in Advantages: Save 2S + 2M at start of ADD. Save 1S at start of DBL.

SLIDE 94
2001 Bernstein: 3M + 5S for DBL. 11M + 5S for ADD. How? Easy S M tradeoff: instead of computing 2❨1 ✁ ❩1, compute (❨1 + ❩1)2 ❨ 2
1 ❩2 1.
DBL formulas were already computing ❨ 2
1 and ❩2 1.
Same idea for the ADD formulas, but have to scale ❳❀ ❨❀ ❩ to eliminate divisions by 2. ADD for ②2 = ①3 + ❛① + ❜: ❯1 = ❳1❩2
2, ❯2 = ❳2❩2 1,
❙1 = ❨1❩3
2, ❙2 = ❨2❩3 1,
many more computations. 1986 Chudnovsky–Chudnovsky: “We suggest to write addition formulas involving (❳❀ ❨❀ ❩❀ ❩2❀ ❩3).” Disadvantages: Allocate space for ❩2❀ ❩3. Pay 1S+1M in ADD and in DBL. Advantages: Save 2S + 2M at start of ADD. Save 1S at start of DBL.

SLIDE 95 Bernstein: 5S for DBL. 5S for ADD. Easy S M tradeoff:
compute (❨1 + ❩1)2 ❨ 2
1 ❩2 1.
formulas were already computing ❨ 2
1 and ❩2 1.
idea for the ADD formulas, have to scale ❳❀ ❨❀ ❩ eliminate divisions by 2. ADD for ②2 = ①3 + ❛① + ❜: ❯1 = ❳1❩2
2, ❯2 = ❳2❩2 1,
❙1 = ❨1❩3
2, ❙2 = ❨2❩3 1,
many more computations. 1986 Chudnovsky–Chudnovsky: “We suggest to write addition formulas involving (❳❀ ❨❀ ❩❀ ❩2❀ ❩3).” Disadvantages: Allocate space for ❩2❀ ❩3. Pay 1S+1M in ADD and in DBL. Advantages: Save 2S + 2M at start of ADD. Save 1S at start of DBL. 1998 Cohen–Miy Store point ❳ ❨ ❩ If point is also cache ❩ ❩ No cost, If point is reuse ❩2❀ ❩ Best Jacobian including
❛
10M + 4 7M + 4S ❩

SLIDE 96 DBL. ADD. M tradeoff: computing 2❨1 ✁ ❩1, ❨ ❩1)2 ❨ 2
1 ❩2 1.
ere already ❨ and ❩2
1.
the ADD formulas, scale ❳❀ ❨❀ ❩ divisions by 2. ADD for ②2 = ①3 + ❛① + ❜: ❯1 = ❳1❩2
2, ❯2 = ❳2❩2 1,
❙1 = ❨1❩3
2, ❙2 = ❨2❩3 1,
many more computations. 1986 Chudnovsky–Chudnovsky: “We suggest to write addition formulas involving (❳❀ ❨❀ ❩❀ ❩2❀ ❩3).” Disadvantages: Allocate space for ❩2❀ ❩3. Pay 1S+1M in ADD and in DBL. Advantages: Save 2S + 2M at start of ADD. Save 1S at start of DBL. 1998 Cohen–Miyaj Store point as (❳ ❨ ❩ If point is input to also cache ❩2 and ❩ No cost, aside from If point is input to reuse ❩2❀ ❩3. Save Best Jacobian speeds including S M tradeoffs: 3M + 5S for DBL ❛
10M + 4S for reADD. 7M + 4S for mADD ❩

SLIDE 97
❨ ✁ ❩1, ❨ ❩ ❨ ❩2
1.
already ❨ ❩ rmulas, ❳❀ ❨❀ ❩ 2. ADD for ②2 = ①3 + ❛① + ❜: ❯1 = ❳1❩2
2, ❯2 = ❳2❩2 1,
❙1 = ❨1❩3
2, ❙2 = ❨2❩3 1,
many more computations. 1986 Chudnovsky–Chudnovsky: “We suggest to write addition formulas involving (❳❀ ❨❀ ❩❀ ❩2❀ ❩3).” Disadvantages: Allocate space for ❩2❀ ❩3. Pay 1S+1M in ADD and in DBL. Advantages: Save 2S + 2M at start of ADD. Save 1S at start of DBL. 1998 Cohen–Miyaji–Ono: Store point as (❳ : ❨ : ❩). If point is input to ADD, also cache ❩2 and ❩3. No cost, aside from space. If point is input to another ADD, reuse ❩2❀ ❩3. Save 1S + 1M Best Jacobian speeds today, including S M tradeoffs: 3M + 5S for DBL if ❛ = 3. 11M + 5S for ADD. 10M + 4S for reADD. 7M + 4S for mADD (i.e. ❩2

SLIDE 98
ADD for ②2 = ①3 + ❛① + ❜: ❯1 = ❳1❩2
2, ❯2 = ❳2❩2 1,
❙1 = ❨1❩3
2, ❙2 = ❨2❩3 1,
many more computations. 1986 Chudnovsky–Chudnovsky: “We suggest to write addition formulas involving (❳❀ ❨❀ ❩❀ ❩2❀ ❩3).” Disadvantages: Allocate space for ❩2❀ ❩3. Pay 1S+1M in ADD and in DBL. Advantages: Save 2S + 2M at start of ADD. Save 1S at start of DBL. 1998 Cohen–Miyaji–Ono: Store point as (❳ : ❨ : ❩). If point is input to ADD, also cache ❩2 and ❩3. No cost, aside from space. If point is input to another ADD, reuse ❩2❀ ❩3. Save 1S + 1M! Best Jacobian speeds today, including S M tradeoffs: 3M + 5S for DBL if ❛ = 3. 11M + 5S for ADD. 10M + 4S for reADD. 7M + 4S for mADD (i.e. ❩2 = 1).

SLIDE 99
for ②2 = ①3 + ❛① + ❜: ❯ ❳1❩2
2, ❯2 = ❳2❩2 1,
❙ ❨1❩3
2, ❙2 = ❨2❩3 1,
more computations. Chudnovsky–Chudnovsky: suggest to write addition formulas involving ❳❀ ❨❀ ❩❀ ❩2❀ ❩3).” Disadvantages: cate space for ❩2❀ ❩3. S+1M in ADD and in DBL. Advantages: S + 2M at start of ADD. S at start of DBL. 1998 Cohen–Miyaji–Ono: Store point as (❳ : ❨ : ❩). If point is input to ADD, also cache ❩2 and ❩3. No cost, aside from space. If point is input to another ADD, reuse ❩2❀ ❩3. Save 1S + 1M! Best Jacobian speeds today, including S M tradeoffs: 3M + 5S for DBL if ❛ = 3. 11M + 5S for ADD. 10M + 4S for reADD. 7M + 4S for mADD (i.e. ❩2 = 1). Compare curves ① ② ❞① ② in projec (2007 Bernstein–Lange): 3M + 4S 10M + 1 9M + 1S Inverted (2007 Bernstein–Lange): 3M + 4S 9M + 1S 8M + 1S Even better extended/completed (2008 Hisil–W

SLIDE 100 ② ①3 + ❛① + ❜: ❯ ❳ ❩ ❯ = ❳2❩2
1,
❙ ❨ ❩ ❙ ❨2❩3
1,
computations. Chudnovsky–Chudnovsky: write rmulas involving ❳❀ ❨❀ ❩❀ ❩ ❀ ❩ ).” for ❩2❀ ❩3. ADD and in DBL. at start of ADD.
1998 Cohen–Miyaji–Ono: Store point as (❳ : ❨ : ❩). If point is input to ADD, also cache ❩2 and ❩3. No cost, aside from space. If point is input to another ADD, reuse ❩2❀ ❩3. Save 1S + 1M! Best Jacobian speeds today, including S M tradeoffs: 3M + 5S for DBL if ❛ = 3. 11M + 5S for ADD. 10M + 4S for reADD. 7M + 4S for mADD (i.e. ❩2 = 1). Compare to speeds curves ①2 + ②2 = 1 ❞① ② in projective coordinates (2007 Bernstein–Lange): 3M + 4S for DBL. 10M + 1S + 1D fo 9M + 1S + 1D for Inverted Edwards co (2007 Bernstein–Lange): 3M + 4S + 1D for 9M + 1S + 1D for 8M + 1S + 1D for Even better speeds extended/completed (2008 Hisil–Wong–Ca

SLIDE 101
② ① ❛① ❜: ❯ ❳ ❩ ❯ ❳ ❩ ❙ ❨ ❩ ❙ ❨ ❩ Chudnovsky–Chudnovsky: involving ❳❀ ❨❀ ❩❀ ❩ ❀ ❩ ❩ ❀ ❩ in DBL. ADD. 1998 Cohen–Miyaji–Ono: Store point as (❳ : ❨ : ❩). If point is input to ADD, also cache ❩2 and ❩3. No cost, aside from space. If point is input to another ADD, reuse ❩2❀ ❩3. Save 1S + 1M! Best Jacobian speeds today, including S M tradeoffs: 3M + 5S for DBL if ❛ = 3. 11M + 5S for ADD. 10M + 4S for reADD. 7M + 4S for mADD (i.e. ❩2 = 1). Compare to speeds for Edwa curves ①2 + ②2 = 1 + ❞①2②2 in projective coordinates (2007 Bernstein–Lange): 3M + 4S for DBL. 10M + 1S + 1D for ADD. 9M + 1S + 1D for mADD. Inverted Edwards coordinates (2007 Bernstein–Lange): 3M + 4S + 1D for DBL. 9M + 1S + 1D for ADD. 8M + 1S + 1D for mADD. Even better speeds from extended/completed coordin (2008 Hisil–Wong–Carter–Da

SLIDE 102
1998 Cohen–Miyaji–Ono: Store point as (❳ : ❨ : ❩). If point is input to ADD, also cache ❩2 and ❩3. No cost, aside from space. If point is input to another ADD, reuse ❩2❀ ❩3. Save 1S + 1M! Best Jacobian speeds today, including S M tradeoffs: 3M + 5S for DBL if ❛ = 3. 11M + 5S for ADD. 10M + 4S for reADD. 7M + 4S for mADD (i.e. ❩2 = 1). Compare to speeds for Edwards curves ①2 + ②2 = 1 + ❞①2②2 in projective coordinates (2007 Bernstein–Lange): 3M + 4S for DBL. 10M + 1S + 1D for ADD. 9M + 1S + 1D for mADD. Inverted Edwards coordinates (2007 Bernstein–Lange): 3M + 4S + 1D for DBL. 9M + 1S + 1D for ADD. 8M + 1S + 1D for mADD. Even better speeds from extended/completed coordinates (2008 Hisil–Wong–Carter–Dawson).

SLIDE 103 Cohen–Miyaji–Ono: point as (❳ : ❨ : ❩).
cache ❩2 and ❩3. cost, aside from space.
- int is input to another ADD,
❩2❀ ❩3. Save 1S + 1M! Jacobian speeds today, including S M tradeoffs: 5S for DBL if ❛ = 3. 5S for ADD. 4S for reADD. 4S for mADD (i.e. ❩2 = 1). Compare to speeds for Edwards curves ①2 + ②2 = 1 + ❞①2②2 in projective coordinates (2007 Bernstein–Lange): 3M + 4S for DBL. 10M + 1S + 1D for ADD. 9M + 1S + 1D for mADD. Inverted Edwards coordinates (2007 Bernstein–Lange): 3M + 4S + 1D for DBL. 9M + 1S + 1D for ADD. 8M + 1S + 1D for mADD. Even better speeds from extended/completed coordinates (2008 Hisil–Wong–Carter–Dawson). ②2 = ①3 ✿ ① ✿

SLIDE 104 aji–Ono: ❳ : ❨ : ❩). to ADD, ❩ and ❩3. from space. to another ADD, ❩ ❀ ❩ Save 1S + 1M! eeds today,
DBL if ❛ = 3. ADD. reADD. mADD (i.e. ❩2 = 1). Compare to speeds for Edwards curves ①2 + ②2 = 1 + ❞①2②2 in projective coordinates (2007 Bernstein–Lange): 3M + 4S for DBL. 10M + 1S + 1D for ADD. 9M + 1S + 1D for mADD. Inverted Edwards coordinates (2007 Bernstein–Lange): 3M + 4S + 1D for DBL. 9M + 1S + 1D for ADD. 8M + 1S + 1D for mADD. Even better speeds from extended/completed coordinates (2008 Hisil–Wong–Carter–Dawson). ②2 = ①3 0✿4① + ✿

SLIDE 105 ❳ ❨ ❩). ❩ ❩ space. another ADD, ❩ ❀ ❩ M! y,
❛ 3. ❩2 = 1). Compare to speeds for Edwards curves ①2 + ②2 = 1 + ❞①2②2 in projective coordinates (2007 Bernstein–Lange): 3M + 4S for DBL. 10M + 1S + 1D for ADD. 9M + 1S + 1D for mADD. Inverted Edwards coordinates (2007 Bernstein–Lange): 3M + 4S + 1D for DBL. 9M + 1S + 1D for ADD. 8M + 1S + 1D for mADD. Even better speeds from extended/completed coordinates (2008 Hisil–Wong–Carter–Dawson). ②2 = ①3 0✿4① + 0✿7

SLIDE 106
Compare to speeds for Edwards curves ①2 + ②2 = 1 + ❞①2②2 in projective coordinates (2007 Bernstein–Lange): 3M + 4S for DBL. 10M + 1S + 1D for ADD. 9M + 1S + 1D for mADD. Inverted Edwards coordinates (2007 Bernstein–Lange): 3M + 4S + 1D for DBL. 9M + 1S + 1D for ADD. 8M + 1S + 1D for mADD. Even better speeds from extended/completed coordinates (2008 Hisil–Wong–Carter–Dawson). ②2 = ①3 0✿4① + 0✿7

SLIDE 107
Compare to speeds for Edwards ①2 + ②2 = 1 + ❞①2②2 rojective coordinates Bernstein–Lange): 4S for DBL. 1S + 1D for ADD. 1S + 1D for mADD. Inverted Edwards coordinates Bernstein–Lange): 4S + 1D for DBL. 1S + 1D for ADD. 1S + 1D for mADD. etter speeds from extended/completed coordinates Hisil–Wong–Carter–Dawson). ②2 = ①3 0✿4① + 0✿7

SLIDE 108 eeds for Edwards ① ② 1 + ❞①2②2 rdinates Bernstein–Lange): DBL. for ADD. for mADD. rds coordinates Bernstein–Lange): for DBL. for ADD. for mADD. eeds from extended/completed coordinates
②2 = ①3 0✿4① + 0✿7

SLIDE 109
wards ① ② ❞① ②2 ADD. rdinates ADD. rdinates rter–Dawson). ②2 = ①3 0✿4① + 0✿7

SLIDE 110
②2 = ①3 0✿4① + 0✿7

SLIDE 111 ② ①3 0✿4① + 0✿7 ①2 + ②2

SLIDE 112
② ① ✿ ① + 0✿7 ①2 + ②2 = 1 300① ②

SLIDE 113
② ① ✿ ① ✿ ①2 + ②2 = 1 300①2②2

SLIDE 114
①2 + ②2 = 1 300①2②2

SLIDE 115
①2 + ②2 = 1 300①2②2

SLIDE 116
①2 + ②2 = 1 300①2②2

SLIDE 117
①2 + ②2 = 1 300①2②2

SLIDE 118
①2 + ②2 = 1 300①2②2

SLIDE 119
① ②2 = 1 300①2②2

SLIDE 120
① ② 300①2②2


SLIDE 122

SLIDE 123

SLIDE 124

SLIDE 125

SLIDE 126

SLIDE 127

SLIDE 128

SLIDE 129

SLIDE 130

SLIDE 131

SLIDE 132

SLIDE 133

SLIDE 134

SLIDE 135

SLIDE 136

SLIDE 137

SLIDE 138