SLIDE 1
06-20008 Cryptography The University of Birmingham Autumn Semester 2012 School of Computer Science Eike Ritter 24 September, 2012
Handout 1
Summary of this handout: Overview of historical cryptographic techniques — Definition of some im- portant cryptographic concepts — Math: Permutations and Residue Classes
I. Historical Overview
- 1. Secret Writing
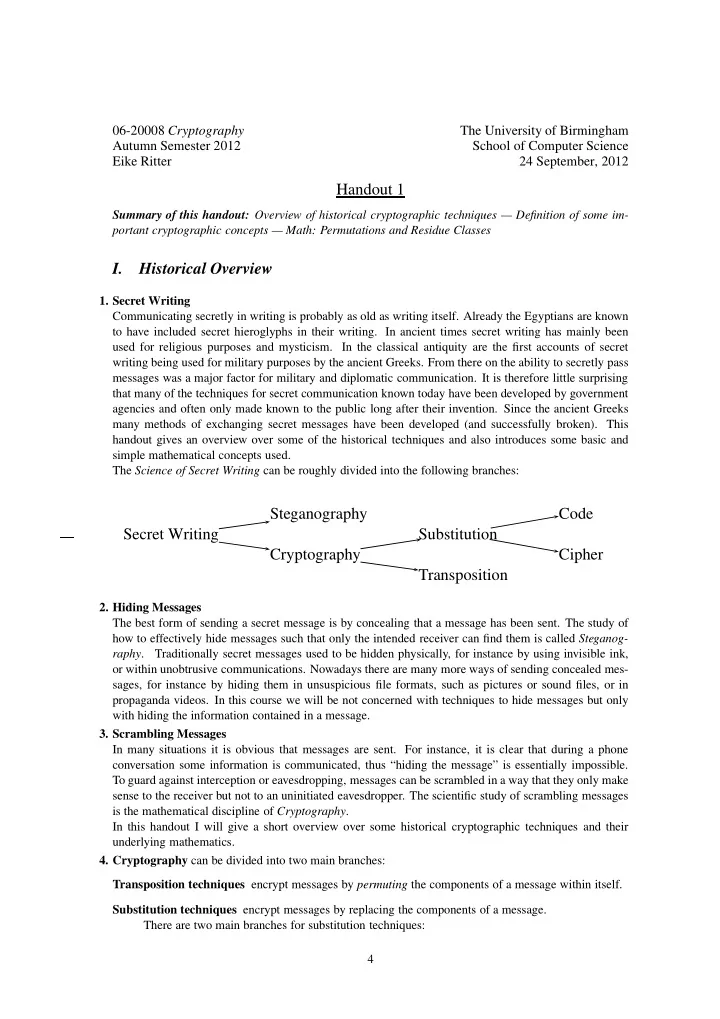
Communicating secretly in writing is probably as old as writing itself. Already the Egyptians are known to have included secret hieroglyphs in their writing. In ancient times secret writing has mainly been used for religious purposes and mysticism. In the classical antiquity are the first accounts of secret writing being used for military purposes by the ancient Greeks. From there on the ability to secretly pass messages was a major factor for military and diplomatic communication. It is therefore little surprising that many of the techniques for secret communication known today have been developed by government agencies and often only made known to the public long after their invention. Since the ancient Greeks many methods of exchanging secret messages have been developed (and successfully broken). This handout gives an overview over some of the historical techniques and also introduces some basic and simple mathematical concepts used. The Science of Secret Writing can be roughly divided into the following branches:
Steganography Code Secret Writing Substitution Cryptography Cipher Transposition
- 2. Hiding Messages
The best form of sending a secret message is by concealing that a message has been sent. The study of how to effectively hide messages such that only the intended receiver can find them is called Steganog- raphy. Traditionally secret messages used to be hidden physically, for instance by using invisible ink,
- r within unobtrusive communications. Nowadays there are many more ways of sending concealed mes-
sages, for instance by hiding them in unsuspicious file formats, such as pictures or sound files, or in propaganda videos. In this course we will be not concerned with techniques to hide messages but only with hiding the information contained in a message.
- 3. Scrambling Messages
In many situations it is obvious that messages are sent. For instance, it is clear that during a phone conversation some information is communicated, thus “hiding the message” is essentially impossible. To guard against interception or eavesdropping, messages can be scrambled in a way that they only make sense to the receiver but not to an uninitiated eavesdropper. The scientific study of scrambling messages is the mathematical discipline of Cryptography. In this handout I will give a short overview over some historical cryptographic techniques and their underlying mathematics.
- 4. Cryptography can be divided into two main branches: