Introduction Iterated hash functions Block cipher constructions SHA-3 Outtro
Hash Functions and SHA-3
Lars R. Knudsen February 13, 2008
1 / 59 Introduction Iterated hash functions Block cipher constructions SHA-3 Outtro
1 Introduction 2 Iterated hash functions 3 Block cipher constructions 4 SHA-3 5 Outtro
2 / 59 Introduction Iterated hash functions Block cipher constructions SHA-3 Outtro
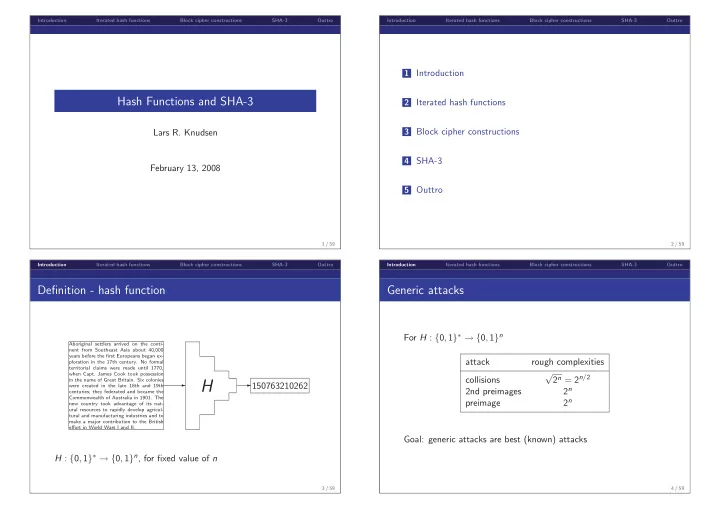
Definition - hash function
✲
Aboriginal settlers arrived on the conti- nent from Southeast Asia about 40,000 years before the first Europeans began ex- ploration in the 17th century. No formal territorial claims were made until 1770, when Capt. James Cook took possession in the name of Great Britain. Six colonies were created in the late 18th and 19th centuries; they federated and became the Commonwealth of Australia in 1901. The new country took advantage of its nat- ural resources to rapidly develop agricul- tural and manufacturing industries and to make a major contribution to the British effort in World Wars I and II.
H
✲150763210262
H : {0, 1}∗ → {0, 1}n, for fixed value of n
3 / 59 Introduction Iterated hash functions Block cipher constructions SHA-3 Outtro
Generic attacks
For H : {0, 1}∗ → {0, 1}n attack rough complexities collisions √ 2n = 2n/2 2nd preimages 2n preimage 2n Goal: generic attacks are best (known) attacks
4 / 59