1
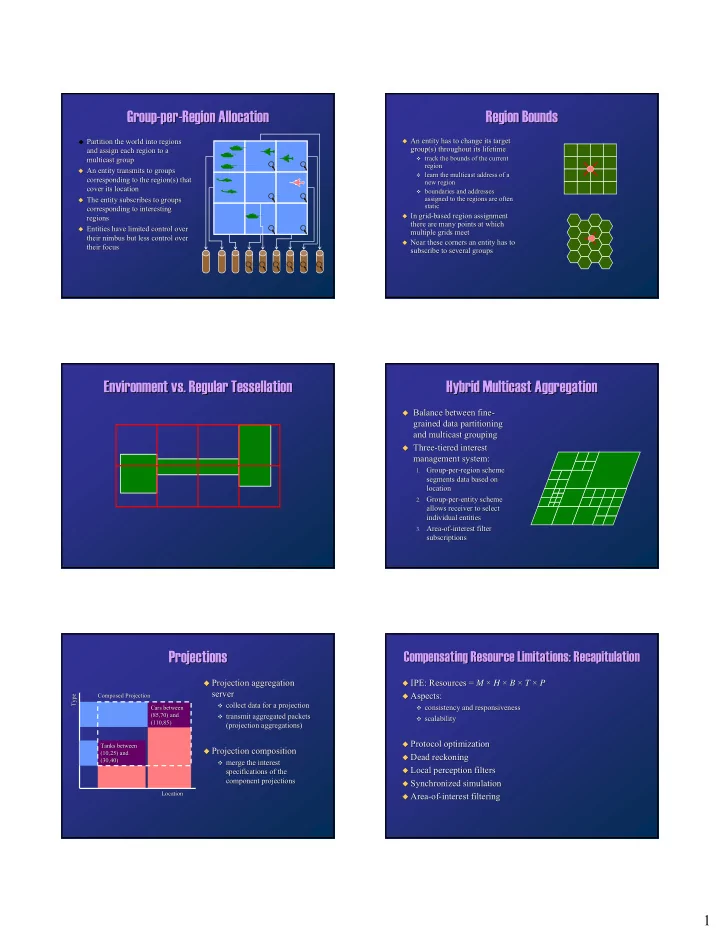
Group Group-
- per
per-
- Region Allocation
Region Allocation
Partition the world into regions
Partition the world into regions and assign each region to a and assign each region to a multicast group multicast group
- An entity transmits to groups
An entity transmits to groups corresponding to the region(s) that corresponding to the region(s) that cover its location cover its location
- The entity subscribes to groups
The entity subscribes to groups corresponding to interesting corresponding to interesting regions regions
- Entities have limited
Entities have limited control over control over their nimbus but less their nimbus but less control over control over their focus their focus
Region Bounds Region Bounds
- An entity has to change its target
An entity has to change its target group(s) throughout its lifetime group(s) throughout its lifetime
- track the bounds of the current
track the bounds of the current region region
- learn the multicast address of a
learn the multicast address of a new region new region
- boundaries and addresses
boundaries and addresses assigned to the regions are often assigned to the regions are often static static
- In grid
In grid-
- based region assignment
based region assignment there are many points at which there are many points at which multiple grids meet multiple grids meet
- Near these corners an entity has to
Near these corners an entity has to subscribe to several groups subscribe to several groups
Environment vs. Regular Environment vs. Regular Tessellation Tessellation Hybrid Multicast Aggregation Hybrid Multicast Aggregation
- Balance between
Balance between fine fine-
- grained
grained data partitioning data partitioning and multicast grouping and multicast grouping
- Three
Three-
- tiered
tiered interest interest management system: management system:
1.
- 1. Group
Group-
- per
per-
- region
region scheme scheme segments data based on segments data based on location location
2.
- 2. Group
Group-
- per
per-
- entity
entity scheme scheme allows receiver to select allows receiver to select individual entities individual entities
3.
- 3. Area
Area-
- of
- f-
- interest
interest filter filter subscriptions subscriptions
Projections Projections
Location Location Type Type Cars between Cars between (85,70) and (85,70) and (110,85) (110,85) Tanks between Tanks between (10,25) and (10,25) and (30,40) (30,40) Composed Projection Composed Projection
- Projection aggregation
Projection aggregation server server
- collect data for a projection
collect data for a projection
- transmit aggregated packets
transmit aggregated packets (projection aggregations) (projection aggregations)
- Projection composition
Projection composition
- merge the interest
merge the interest specifications of the specifications of the component projections component projections
Compensating Resource Limitations: Recapitulation Compensating Resource Limitations: Recapitulation
- IPE: Resources =
IPE: Resources = M M × × H H × × B B × × T T × × P P
- Aspects:
Aspects:
- consistency and responsiveness
consistency and responsiveness
- scalability
scalability
- Protocol optimization
Protocol optimization
- Dead reckoning
Dead reckoning
- Local perception filters
Local perception filters
- Synchronized simulation
Synchronized simulation
- Area
Area-
- of
- f-
- interest filtering