Finite Fields AES
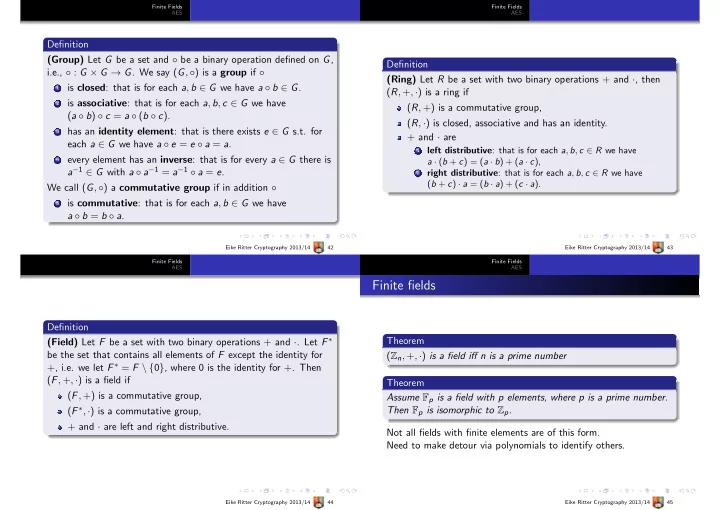
Definition (Group) Let G be a set and ◦ be a binary operation defined on G, i.e., ◦ : G × G → G. We say (G, ◦) is a group if ◦
1 is closed: that is for each a, b ∈ G we have a ◦ b ∈ G. 2 is associative: that is for each a, b, c ∈ G we have
(a ◦ b) ◦ c = a ◦ (b ◦ c).
3 has an identity element: that is there exists e ∈ G s.t. for
each a ∈ G we have a ◦ e = e ◦ a = a.
4 every element has an inverse: that is for every a ∈ G there is
a−1 ∈ G with a ◦ a−1 = a−1 ◦ a = e. We call (G, ◦) a commutative group if in addition ◦
5 is commutative: that is for each a, b ∈ G we have
a ◦ b = b ◦ a.
Eike Ritter Cryptography 2013/14 42 Finite Fields AES
Definition (Ring) Let R be a set with two binary operations + and ·, then (R, +, ·) is a ring if (R, +) is a commutative group, (R, ·) is closed, associative and has an identity. + and · are
1
left distributive: that is for each a, b, c ∈ R we have a · (b + c) = (a · b) + (a · c),
2
right distributive: that is for each a, b, c ∈ R we have (b + c) · a = (b · a) + (c · a).
Eike Ritter Cryptography 2013/14 43 Finite Fields AES
Definition (Field) Let F be a set with two binary operations + and ·. Let F ∗ be the set that contains all elements of F except the identity for +, i.e. we let F ∗ = F \ {0}, where 0 is the identity for +. Then (F, +, ·) is a field if (F, +) is a commutative group, (F ∗, ·) is a commutative group, + and · are left and right distributive.
Eike Ritter Cryptography 2013/14 44 Finite Fields AES
Finite fields
Theorem (Zn, +, ·) is a field iff n is a prime number Theorem Assume Fp is a field with p elements, where p is a prime number. Then Fp is isomorphic to Zp. Not all fields with finite elements are of this form. Need to make detour via polynomials to identify others.
Eike Ritter Cryptography 2013/14 45