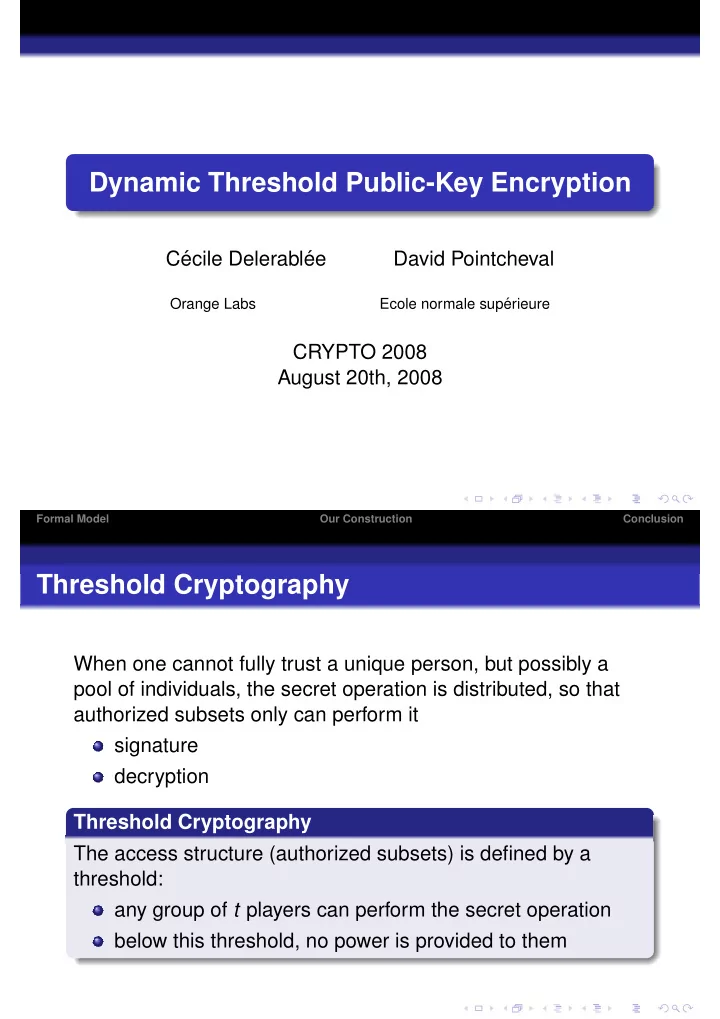
Dynamic Threshold Public-Key Encryption
C´ ecile Delerabl´ ee David Pointcheval
Orange Labs Ecole normale sup´ erieure
CRYPTO 2008 August 20th, 2008
Formal Model Our Construction Conclusion
Dynamic Threshold Public-Key Encryption C ecile Delerabl ee David - - PDF document
Dynamic Threshold Public-Key Encryption C ecile Delerabl ee David Pointcheval Ecole normale sup Orange Labs erieure CRYPTO 2008 August 20th, 2008 Formal Model Our Construction Conclusion Threshold Cryptography When one cannot
Formal Model Our Construction Conclusion
Formal Model Our Construction Conclusion
Formal Model Our Construction Conclusion
1
Formal Model Our Construction Conclusion
Formal Model Our Construction Conclusion
Formal Model Our Construction Conclusion
Formal Model Our Construction Conclusion
Formal Model Our Construction Conclusion
Formal Model Our Construction Conclusion
Formal Model Our Construction Conclusion
Formal Model Our Construction Conclusion
Formal Model Our Construction Conclusion
1 (γ+x1)...(γ+xt ) ∈ GT
1 γ+xj )}t
Formal Model Our Construction Conclusion
Formal Model Our Construction Conclusion
1 γ+x
xi ∈S(γ+xi)· x∈Dm+t−s−1(γ+x)
Formal Model Our Construction Conclusion
1 γ+x
k· xi ∈S∪Dm+t−s−1 (γ+xi ) γ+x
c
Formal Model Our Construction Conclusion
x∈S∪Dm+t−s−1\T (γ+x)
x∈S∪Dm+t−s−1(γ+x)
Our Construction Conclusion
Formal Model Our Construction Conclusion
Formal Model Our Construction Conclusion
xi ∈S(γ+xi)· x∈Dm+t−s−1(γ+x)
1 γ+x , σ = e (usk, C2).
c
Formal Model Our Construction Conclusion
Formal Model Our Construction Conclusion