Electricite Du Laos (EDL)
- Dr. Kanda Runapongsa Saikaew, Computer Engineering, KKU
1
1
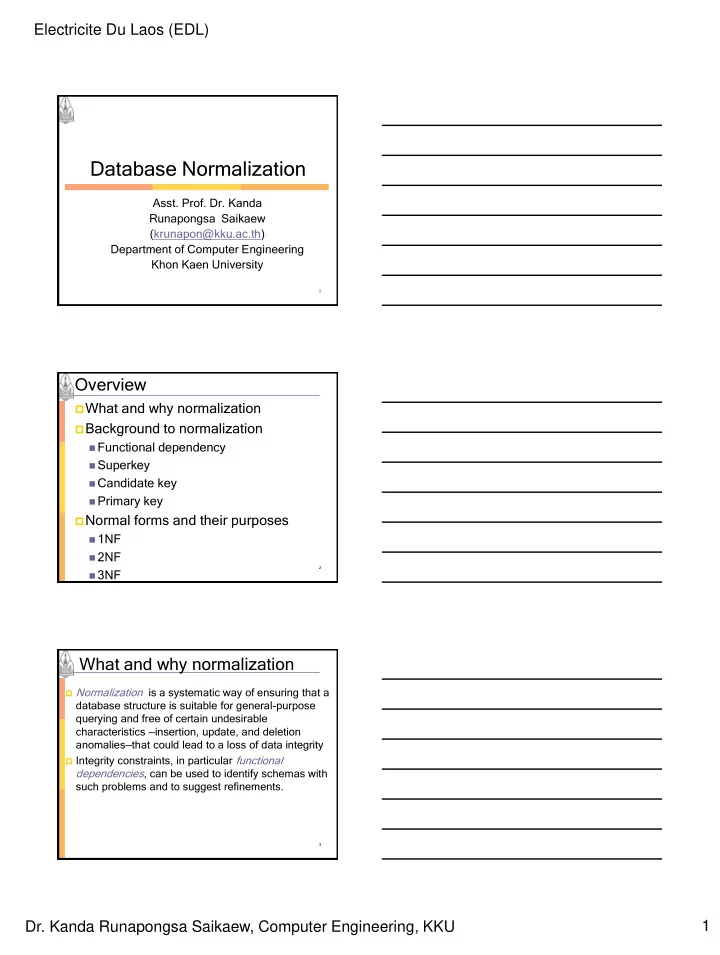
- Asst. Prof. Dr. Kanda
Runapongsa Saikaew (krunapon@kku.ac.th) Department of Computer Engineering Khon Kaen University
Database Normalization
2
Overview
What and why normalization Background to normalization
Functional dependency Superkey Candidate key Primary key
Normal forms and their purposes
1NF 2NF 3NF
3
What and why normalization
Normalization is a systematic way of ensuring that a
database structure is suitable for general-purpose querying and free of certain undesirable characteristics —insertion, update, and deletion anomalies—that could lead to a loss of data integrity
Integrity constraints, in particular functional