Cyber security preparedness in water utilities in the UK
Dr Jim Marshall, Senior Policy Advisor, Water UK Cyber Water Workshop 2018 Tuesday 9 October 2018
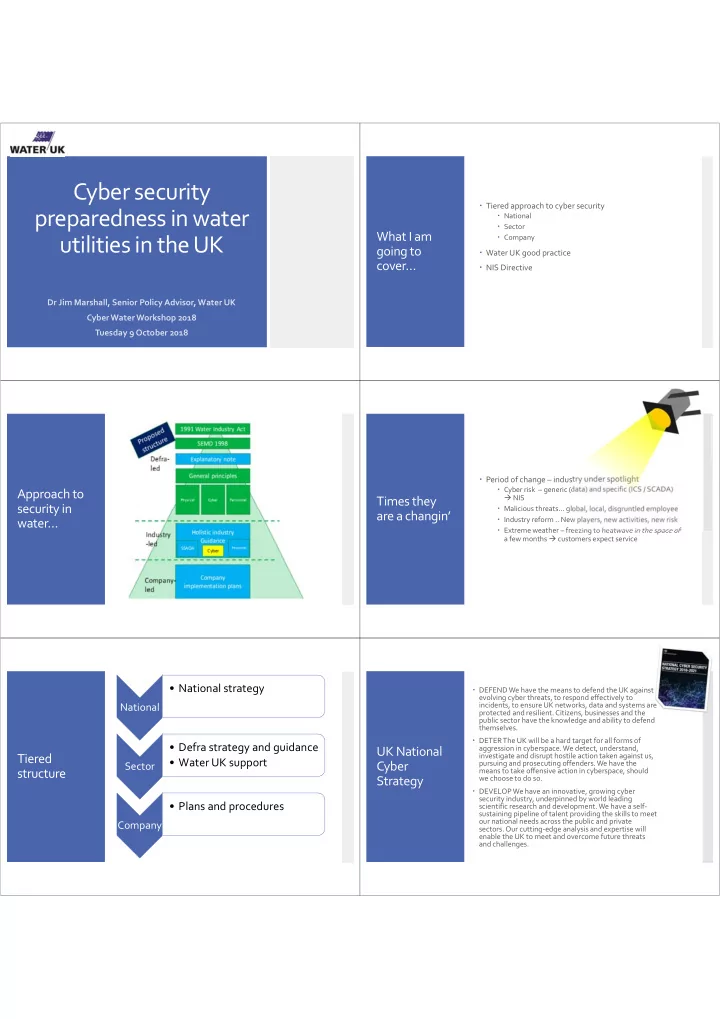
What I am going to cover…
Tiered approach to cyber security
National Sector Company
Water UK good practice NIS Directive
Approach to security in water… Times they are a changin’
Period of change – industry under spotlight
Cyber risk – generic (data) and specific (ICS / SCADA) NIS Malicious threats… global, local, disgruntled employee Industry reform .. New players, new activities, new risk Extreme weather – freezing to heatwave in the space of a few months customers expect service
Tiered structure
National
- National strategy
Sector
- Defra strategy and guidance
- Water UK support
Company
- Plans and procedures
UK National Cyber Strategy
DEFEND We have the means to defend the UK against evolving cyber threats, to respond effectively to incidents, to ensure UK networks, data and systems are protected and resilient. Citizens, businesses and the public sector have the knowledge and ability to defend themselves. DETER The UK will be a hard target for all forms of aggression in cyberspace. We detect, understand, investigate and disrupt hostile action taken against us, pursuing and prosecuting offenders. We have the means to take offensive action in cyberspace, should we choose to do so. DEVELOP We have an innovative, growing cyber security industry, underpinned by world leading scientific research and development. We have a self‐ sustaining pipeline of talent providing the skills to meet
- ur national needs across the public and private
- sectors. Our cutting‐edge analysis and expertise will
enable the UK to meet and overcome future threats and challenges.