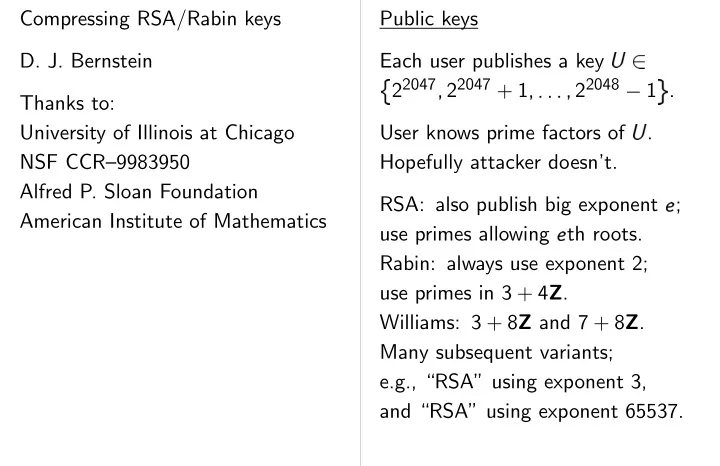
SLIDE 1 Compressing RSA/Rabin keys
Thanks to: University of Illinois at Chicago NSF CCR–9983950 Alfred P. Sloan Foundation American Institute of Mathematics Public keys Each user publishes a key 22047
22047 + 1
✁ ✁ 22048 ✂
1 . User knows prime factors of . Hopefully attacker doesn’t. RSA: also publish big exponent
✄ ;
use primes allowing
✄ th roots.
Rabin: always use exponent 2; use primes in 3 + 4Z. Williams: 3 + 8Z and 7 + 8Z. Many subsequent variants; e.g., “RSA” using exponent 3, and “RSA” using exponent 65537.

SLIDE 2 RSA/Rabin keys Illinois at Chicago CCR–9983950 Foundation Institute of Mathematics Public keys Each user publishes a key 22047
22047 + 1
✁ ✁ 22048 ✂
1 . User knows prime factors of . Hopefully attacker doesn’t. RSA: also publish big exponent
✄ ;
use primes allowing
✄ th roots.
Rabin: always use exponent 2; use primes in 3 + 4Z. Williams: 3 + 8Z and 7 + 8Z. Many subsequent variants; e.g., “RSA” using exponent 3, and “RSA” using exponent 65537. The compression question Can store in 2048 Can store
1
✁ ✁
✁
Can we use fewer bits? Knee-jerk answer: If you can’t afford
✁
switch to 256-bit elliptic http://cr.yp.to/ecdh.html But elliptic-curve signatures have slow verification. Want a better answ

SLIDE 3 Public keys Each user publishes a key 22047
22047 + 1
✁ ✁ 22048 ✂
1 . User knows prime factors of . Hopefully attacker doesn’t. RSA: also publish big exponent
✄ ;
use primes allowing
✄ th roots.
Rabin: always use exponent 2; use primes in 3 + 4Z. Williams: 3 + 8Z and 7 + 8Z. Many subsequent variants; e.g., “RSA” using exponent 3, and “RSA” using exponent 65537. The compression question Can store in 2048 bits. Can store
1
✁ ✁
randomly accessible, in 2048
✁
bits. Can we use fewer bits? Knee-jerk answer: “No! If you can’t afford 2048
✁
bits, switch to 256-bit elliptic curves. http://cr.yp.to/ecdh.html” But elliptic-curve signatures have slow verification. Want a better answer.

SLIDE 4 publishes a key
✁ ✁ 22048 ✂
1 . rime factors of . er doesn’t. publish big exponent
✄ ;
wing
✄ th roots.
use exponent 2; 4Z. Z and 7 + 8Z. subsequent variants; using exponent 3, using exponent 65537. The compression question Can store in 2048 bits. Can store
1
✁ ✁
randomly accessible, in 2048
✁
bits. Can we use fewer bits? Knee-jerk answer: “No! If you can’t afford 2048
✁
bits, switch to 256-bit elliptic curves. http://cr.yp.to/ecdh.html” But elliptic-curve signatures have slow verification. Want a better answer. Recognizing lower 22047
✁ ✁ 22048 ✂
so has top bit 1. Don’t store that bit. With Rabin-Williams: Don’t store bottom Better: Users never divisible by 3
5 7
- so only 480 possibilities
for mod 9240. Replace bottom 13 bits with encoding of mod

SLIDE 5 The compression question Can store in 2048 bits. Can store
1
✁ ✁
randomly accessible, in 2048
✁
bits. Can we use fewer bits? Knee-jerk answer: “No! If you can’t afford 2048
✁
bits, switch to 256-bit elliptic curves. http://cr.yp.to/ecdh.html” But elliptic-curve signatures have slow verification. Want a better answer. Recognizing lower entropy 22047
✁ ✁ 22048 ✂
1 so has top bit 1. Don’t store that bit. With Rabin-Williams: 5 + 8Z. Don’t store bottom 3 bits. Better: Users never generate divisible by 3
5 7 11,
so only 480 possibilities for mod 9240. Replace bottom 13 bits with 9-bit encoding of mod 9240.

SLIDE 6 question 2048 bits.
✁ ✁
accessible, in 2048
✁
bits. er bits? er: “No! rd 2048
✁
bits, 256-bit elliptic curves. http://cr.yp.to/ecdh.html” elliptic-curve signatures verification. answer. Recognizing lower entropy 22047
✁ ✁ 22048 ✂
1 so has top bit 1. Don’t store that bit. With Rabin-Williams: 5 + 8Z. Don’t store bottom 3 bits. Better: Users never generate divisible by 3
5 7 11,
so only 480 possibilities for mod 9240. Replace bottom 13 bits with 9-bit encoding of mod 9240. Have reduced 2048 Can we do much b Knee-jerk answer: C’mon, you know y switch to elliptic curves.” e.g. User generates
21023
✁ ✁ 21024 ✂
✁ ✁ 21025 ✂
1 1025 log 2 chance 1 1026 log 2 chance
✂
1 chance
22023 equally

SLIDE 7 Recognizing lower entropy 22047
✁ ✁ 22048 ✂
1 so has top bit 1. Don’t store that bit. With Rabin-Williams: 5 + 8Z. Don’t store bottom 3 bits. Better: Users never generate divisible by 3
5 7 11,
so only 480 possibilities for mod 9240. Replace bottom 13 bits with 9-bit encoding of mod 9240. Have reduced 2048 to 2043. Can we do much better? Knee-jerk answer: “No! C’mon, you know you want to switch to elliptic curves.” e.g. User generates =
from
independent uniform random 21023
✁ ✁ 21024 ✂
1 ,
✁ ✁ 21025 ✂
1 : 1 1025 log 2 chance of prime, 1 1026 log 2 chance of
prime,
1 8 chance of 3
7 + 8Z,
2 log 2
✂
1 chance of
so 22023 equally likely ’s.

SLIDE 8 er entropy
✁ ✁ 22048 ✂
1 1. bit. Rabin-Williams: 5 + 8Z.
never generate
11,
Replace with 9-bit mod 9240. Have reduced 2048 to 2043. Can we do much better? Knee-jerk answer: “No! C’mon, you know you want to switch to elliptic curves.” e.g. User generates =
from
independent uniform random 21023
✁ ✁ 21024 ✂
1 ,
✁ ✁ 21025 ✂
1 : 1 1025 log 2 chance of prime, 1 1026 log 2 chance of
prime,
1 8 chance of 3
7 + 8Z,
2 log 2
✂
1 chance of
so 22023 equally likely ’s. Reducing entropy Define ( ) = 500th ( ) = with 500th Change key-generation to produce keys Then can encode saving one bit; also top/bottom bits as Brute-force key generation: generate by the if ( ) = 1, try again. Conjecturally this tak almost exactly 2 tries confirmed by experiment.

SLIDE 9 Have reduced 2048 to 2043. Can we do much better? Knee-jerk answer: “No! C’mon, you know you want to switch to elliptic curves.” e.g. User generates =
from
independent uniform random 21023
✁ ✁ 21024 ✂
1 ,
✁ ✁ 21025 ✂
1 : 1 1025 log 2 chance of prime, 1 1026 log 2 chance of
prime,
1 8 chance of 3
7 + 8Z,
2 log 2
✂
1 chance of
so 22023 equally likely ’s. Reducing entropy Define ( ) = 500th bit of , ( ) = with 500th bit omitted. Change key-generation procedure to produce keys with ( ) = 0. Then can encode as ( ), saving one bit; also save top/bottom bits as before. Brute-force key generation: generate by the old method; if ( ) = 1, try again. Conjecturally this takes almost exactly 2 tries on average; confirmed by experiment.

SLIDE 10 2048 to 2043. better? er: “No! you want to curves.” generates =
from
uniform random
✁ ✁ 21024 ✂
1 ,
✁ ✁ 21025 ✂
1 : chance of prime, chance of
prime,
3
7 + 8Z, ✂
chance of
equally likely ’s. Reducing entropy Define ( ) = 500th bit of , ( ) = with 500th bit omitted. Change key-generation procedure to produce keys with ( ) = 0. Then can encode as ( ), saving one bit; also save top/bottom bits as before. Brute-force key generation: generate by the old method; if ( ) = 1, try again. Conjecturally this takes almost exactly 2 tries on average; confirmed by experiment. More generally, select : 2048-bit strings
: 2048-bit strings (2048
✂
with
Change key-generation to produce keys Then can encode saving bits. Is
and easy to invert? for the functions w

SLIDE 11 Reducing entropy Define ( ) = 500th bit of , ( ) = with 500th bit omitted. Change key-generation procedure to produce keys with ( ) = 0. Then can encode as ( ), saving one bit; also save top/bottom bits as before. Brute-force key generation: generate by the old method; if ( ) = 1, try again. Conjecturally this takes almost exactly 2 tries on average; confirmed by experiment. More generally, select functions : 2048-bit strings
and : 2048-bit strings (2048
✂
)-bit strings with
Change key-generation procedure to produce keys with ( ) = 0. Then can encode as ( ), saving bits. Is
and easy to invert? Yes for the functions we’ll consider.

SLIDE 12 y 500th bit of , 500th bit omitted. ey-generation procedure with ( ) = 0. de as ( ), also save as before. generation: the old method; again. this takes tries on average; eriment. More generally, select functions : 2048-bit strings
and : 2048-bit strings (2048
✂
)-bit strings with
Change key-generation procedure to produce keys with ( ) = 0. Then can encode as ( ), saving bits. Is
and easy to invert? Yes for the functions we’ll consider. Do ’s exist with Conjecturally chance
(Provable for chosen from “universal” classes.) Brute force takes
Can we do much b
Are the resulting k Not necessarily!

SLIDE 13 More generally, select functions : 2048-bit strings
and : 2048-bit strings (2048
✂
)-bit strings with
Change key-generation procedure to produce keys with ( ) = 0. Then can encode as ( ), saving bits. Is
and easy to invert? Yes for the functions we’ll consider. Do ’s exist with ( ) = 0? Conjecturally chance 1 2
- for the functions we’ll consider.
(Provable for chosen randomly from “universal” classes.) Brute force takes 2
far too slow for large . Can we do much better?
- Yes. Will come back to this.
Are the resulting keys secure? Not necessarily!

SLIDE 14 select functions strings strings and strings
✂
)-bit strings
ey-generation procedure with ( ) = 0. de as ( ),
invert? Yes we’ll consider. Do ’s exist with ( ) = 0? Conjecturally chance 1 2
- for the functions we’ll consider.
(Provable for chosen randomly from “universal” classes.) Brute force takes 2
far too slow for large . Can we do much better?
- Yes. Will come back to this.
Are the resulting keys secure? Not necessarily! The half-special numb 1998 Lenstra: “Numb form 21024
✁ ✁
1024-bit RSA securit
is not much smaller
Chance of an “unusually NFS polynomial is Not true. Reducing using ( ) = half reduces conjectured Skewed NFS polynomials (1999 Murphy) turn unusually small for

SLIDE 15 Do ’s exist with ( ) = 0? Conjecturally chance 1 2
- for the functions we’ll consider.
(Provable for chosen randomly from “universal” classes.) Brute force takes 2
far too slow for large . Can we do much better?
- Yes. Will come back to this.
Are the resulting keys secure? Not necessarily! The half-special number-field sieve 1998 Lenstra: “Numbers of the form 21024
✁ ✁ offer regular
1024-bit RSA security, as long as
is not much smaller than 2500.”
Chance of an “unusually small” NFS polynomial is “negligible.” Not true. Reducing entropy, using ( ) = half the bits of , reduces conjectured security level. Skewed NFS polynomials (1999 Murphy) turn out to be unusually small for these numbers.

SLIDE 16 with ( ) = 0? chance 1 2
chosen randomly classes.) es 2
large . better? back to this. keys secure? The half-special number-field sieve 1998 Lenstra: “Numbers of the form 21024
✁ ✁ offer regular
1024-bit RSA security, as long as
is not much smaller than 2500.”
Chance of an “unusually small” NFS polynomial is “negligible.” Not true. Reducing entropy, using ( ) = half the bits of , reduces conjectured security level. Skewed NFS polynomials (1999 Murphy) turn out to be unusually small for these numbers. Sharing entropy Generate random from set
Define
1 =
e.g., for = 500th generate random same 500th bit as Similarly generate
✁ ✁
Compress
2 to
( compress
3 to
( Overall (2048
✂
)
✁
to store
1
✁ ✁

SLIDE 17 The half-special number-field sieve 1998 Lenstra: “Numbers of the form 21024
✁ ✁ offer regular
1024-bit RSA security, as long as
is not much smaller than 2500.”
Chance of an “unusually small” NFS polynomial is “negligible.” Not true. Reducing entropy, using ( ) = half the bits of , reduces conjectured security level. Skewed NFS polynomials (1999 Murphy) turn out to be unusually small for these numbers. Sharing entropy Generate random
1
from set
Define
1 =
1( ( 1)).
Generate random
2 1:
e.g., for = 500th bit, generate random
2 having
same 500th bit as
1.
Similarly generate
3
✁ ✁ .
Compress
2 to
( 2); compress
3 to
( 3); etc. Overall (2048
✂
)
✁
+ bits to store
1
✁ ✁

SLIDE 18 number-field sieve “Numbers of the
✁ ✁ offer regular
security, as long as
“unusually small” is “negligible.” Reducing entropy, half the bits of , conjectured security level.
turn out to be for these numbers. Sharing entropy Generate random
1
from set
Define
1 =
1( ( 1)).
Generate random
2 1:
e.g., for = 500th bit, generate random
2 having
same 500th bit as
1.
Similarly generate
3
✁ ✁ .
Compress
2 to
( 2); compress
3 to
( 3); etc. Overall (2048
✂
)
✁
+ bits to store
1
✁ ✁
If distribution of is uniform over , and distribution of is uniform over
1,
then distribution of is uniform over . So attacker’s chance is provably identical attacker’s chance of Same comment with replaced by “forging etc. Sharing entropy is

SLIDE 19 Sharing entropy Generate random
1
from set
Define
1 =
1( ( 1)).
Generate random
2 1:
e.g., for = 500th bit, generate random
2 having
same 500th bit as
1.
Similarly generate
3
✁ ✁ .
Compress
2 to
( 2); compress
3 to
( 3); etc. Overall (2048
✂
)
✁
+ bits to store
1
✁ ✁
If distribution of
1
is uniform over , and distribution of
2 given 1
is uniform over
1,
then distribution of
2
is uniform over . So attacker’s chance of factoring
2
is provably identical to attacker’s chance of factoring
1.
Same comment with “factoring” replaced by “forging signatures” etc. Sharing entropy is provably secure.

SLIDE 20 1
all possible keys.
1( ( 1)).
2 1:
500th bit,
2 having
as
1.
generate
3
✁ ✁ .
( 2); ( 3); etc.
✂
)
✁
+ bits
✁ ✁
If distribution of
1
is uniform over , and distribution of
2 given 1
is uniform over
1,
then distribution of
2
is uniform over . So attacker’s chance of factoring
2
is provably identical to attacker’s chance of factoring
1.
Same comment with “factoring” replaced by “forging signatures” etc. Sharing entropy is provably secure. Time to factor
1
can be less than double the time for a single (e.g., Schnorr, Eratosthenes) Analogy: brute-force versus a secret-key finds
✁
target keys as finding one target Problem arises with shared entropy. (e.g., Coppersmith, For safety, choose so that (conjecturally) can’t even do one

SLIDE 21
If distribution of
1
is uniform over , and distribution of
2 given 1
is uniform over
1,
then distribution of
2
is uniform over . So attacker’s chance of factoring
2
is provably identical to attacker’s chance of factoring
1.
Same comment with “factoring” replaced by “forging signatures” etc. Sharing entropy is provably secure. Time to factor
1 and 2
can be less than double the time for a single factorization. (e.g., Schnorr, Eratosthenes) Analogy: brute-force search versus a secret-key cipher finds
✁
target keys in same time as finding one target key. Problem arises with or without shared entropy. (e.g., Coppersmith, Bernstein) For safety, choose key sizes so that (conjecturally) attacker can’t even do one factorization.

SLIDE 22 1
,
2 given 1 1,
2
. chance of factoring
2
identical to chance of factoring
1.
with “factoring” rging signatures” is provably secure. Time to factor
1 and 2
can be less than double the time for a single factorization. (e.g., Schnorr, Eratosthenes) Analogy: brute-force search versus a secret-key cipher finds
✁
target keys in same time as finding one target key. Problem arises with or without shared entropy. (e.g., Coppersmith, Bernstein) For safety, choose key sizes so that (conjecturally) attacker can’t even do one factorization. Perhaps time to facto is below time to facto Analogy: brute-force finds some target k
✁
after 1
✁
As before, problem with or without sha For safety, multiply factorization success (e.g. ECM success by
✁
before choosing

SLIDE 23 Time to factor
1 and 2
can be less than double the time for a single factorization. (e.g., Schnorr, Eratosthenes) Analogy: brute-force search versus a secret-key cipher finds
✁
target keys in same time as finding one target key. Problem arises with or without shared entropy. (e.g., Coppersmith, Bernstein) For safety, choose key sizes so that (conjecturally) attacker can’t even do one factorization. Perhaps time to factor
1 or 2
is below time to factor
1.
Analogy: brute-force search finds some target key out of
✁
after 1
✁
As before, problem arises with or without shared entropy. For safety, multiply conjectured factorization success chance (e.g. ECM success chance) by
✁
before choosing key sizes.

SLIDE 24 1 and 2
double single factorization. Eratosthenes) rute-force search ey cipher
✁
eys in same time rget key. with or without ersmith, Bernstein)
(conjecturally) attacker
Perhaps time to factor
1 or 2
is below time to factor
1.
Analogy: brute-force search finds some target key out of
✁
after 1
✁
As before, problem arises with or without shared entropy. For safety, multiply conjectured factorization success chance (e.g. ECM success chance) by
✁
before choosing key sizes. Is this overkill? Are there algorithms
1 or 2 or
✁ ✁ ✁ or
For discrete logs, p by randomized self-reduction. For factorization, no without an extra
✁
Factorization literature explicitly address multiple Maybe we’re oversimplifying by considering just

SLIDE 25 Perhaps time to factor
1 or 2
is below time to factor
1.
Analogy: brute-force search finds some target key out of
✁
after 1
✁
As before, problem arises with or without shared entropy. For safety, multiply conjectured factorization success chance (e.g. ECM success chance) by
✁
before choosing key sizes. Is this overkill? Are there algorithms to factor
1 or 2 or
✁ ✁ ✁ or
- more quickly than factoring
1?
For discrete logs, prove “no” by randomized self-reduction. For factorization, no hope of proof without an extra
✁ .
Factorization literature needs to explicitly address multiple inputs. Maybe we’re oversimplifying by considering just one input.

SLIDE 26 factor
1 or 2
factor
1.
rute-force search rget key out of
✁ ✁
the computation. roblem arises shared entropy. multiply conjectured success chance success chance)
✁
Is this overkill? Are there algorithms to factor
1 or 2 or
✁ ✁ ✁ or
- more quickly than factoring
1?
For discrete logs, prove “no” by randomized self-reduction. For factorization, no hope of proof without an extra
✁ .
Factorization literature needs to explicitly address multiple inputs. Maybe we’re oversimplifying by considering just one input. Generating given Define ( ) = mo Reasonably fast generation
(
) =
( 1 Choose 1024-bit .
= 21024 + ( 1
If not both primes, If
Conjecturally 217

SLIDE 27 Is this overkill? Are there algorithms to factor
1 or 2 or
✁ ✁ ✁ or
- more quickly than factoring
1?
For discrete logs, prove “no” by randomized self-reduction. For factorization, no hope of proof without an extra
✁ .
Factorization literature needs to explicitly address multiple inputs. Maybe we’re oversimplifying by considering just one input. Generating given bottom half Define ( ) = mod 21024. Reasonably fast generation of
(
) =
( 1), given ( 1): Choose 1024-bit . Compute
= 21024 + ( 1 ( 1) mod 21024).
If not both primes, try again. If
Conjecturally 217 tries

SLIDE 28 rithms to factor
✁ ✁ ✁ or
1?
logs, prove “no” self-reduction. rization, no hope of proof
✁ .
literature needs to address multiple inputs.
just one input. Generating given bottom half Define ( ) = mod 21024. Reasonably fast generation of
(
) =
( 1), given ( 1): Choose 1024-bit . Compute
= 21024 + ( 1 ( 1) mod 21024).
If not both primes, try again. If
Conjecturally 217 tries
Analogous method ( ) = 21024 Method reinvented Published 1991 Guillou in context of reducing “Some forms of the
✁ ✁ ✁ need less storage. ✁ ✁ ✁
all of the bits of the most significant bytes valued to zero.”

SLIDE 29 Generating given bottom half Define ( ) = mod 21024. Reasonably fast generation of
(
) =
( 1), given ( 1): Choose 1024-bit . Compute
= 21024 + ( 1 ( 1) mod 21024).
If not both primes, try again. If
Conjecturally 217 tries
Analogous method works for ( ) = 21024 . Method reinvented several times. Published 1991 Guillou Quisquater, in context of reducing entropy: “Some forms of the modulus
✁ ✁ ✁ need less storage. ✁ ✁ ✁
all of the bits of the most significant bytes are valued to zero.”

SLIDE 30 given bottom half mod 21024. generation of
( 1): . Compute
rimes, try again.
217 tries Analogous method works for ( ) = 21024 . Method reinvented several times. Published 1991 Guillou Quisquater, in context of reducing entropy: “Some forms of the modulus
✁ ✁ ✁ need less storage. ✁ ✁ ✁
all of the bits of the most significant bytes are valued to zero.” Patent application by Vanstone and Zuccherato: “A method of encrypting
✁ ✁ ✁
selecting said public
✁ ✁ ✁
having a plurality of at least one set being predetermined pattern
✁ ✁ ✁
and applying said public to encrypt the message.” Includes some generation ranging from sensible Granted 2000: US

SLIDE 31
Analogous method works for ( ) = 21024 . Method reinvented several times. Published 1991 Guillou Quisquater, in context of reducing entropy: “Some forms of the modulus
✁ ✁ ✁ need less storage. ✁ ✁ ✁
all of the bits of the most significant bytes are valued to zero.” Patent application filed 1995 by Vanstone and Zuccherato: “A method of encrypting data
✁ ✁ ✁
selecting said public key
✁ ✁ ✁
having a plurality of sets of bits, at least one set being of a predetermined pattern of bits
✁ ✁ ✁
and applying said public key to encrypt the message.” Includes some generation methods, ranging from sensible to silly. Granted 2000: US 6134325.

SLIDE 32 method works for . reinvented several times. Guillou Quisquater, reducing entropy: the modulus
✁ ✁ ✁
rage.
✁ ✁ ✁
the bytes are Patent application filed 1995 by Vanstone and Zuccherato: “A method of encrypting data
✁ ✁ ✁
selecting said public key
✁ ✁ ✁
having a plurality of sets of bits, at least one set being of a predetermined pattern of bits
✁ ✁ ✁
and applying said public key to encrypt the message.” Includes some generation methods, ranging from sensible to silly. Granted 2000: US 6134325. More patents filed responding to silly “Select a number
✁ ✁ ✁
factor
as ✁
the factor
is prime; is prime, compute ✁
as the product of
✁
RSA modulus; and
- is not prime, adjust
- the check of whether
- prime.”
Granted 2002: US US 6496929.

SLIDE 33 Patent application filed 1995 by Vanstone and Zuccherato: “A method of encrypting data
✁ ✁ ✁
selecting said public key
✁ ✁ ✁
having a plurality of sets of bits, at least one set being of a predetermined pattern of bits
✁ ✁ ✁
and applying said public key to encrypt the message.” Includes some generation methods, ranging from sensible to silly. Granted 2000: US 6134325. More patents filed by Lenstra, responding to silly methods. “Select a number ;
✁ ✁ ✁ obtain the
factor
as ✁
the factor
is prime; if the factor is prime, compute the number ✁
as the product of and
and
determine that the number
✁
is the RSA modulus; and if the factor
and repeat
the check of whether the factor
is
prime.” Granted 2002: US 6404890, US 6496929.

SLIDE 34 application filed 1995 Zuccherato: encrypting data
✁ ✁ ✁
public key
✁ ✁ ✁
y of sets of bits, being of a pattern of bits
✁ ✁ ✁
said public key message.” generation methods, sensible to silly. US 6134325. More patents filed by Lenstra, responding to silly methods. “Select a number ;
✁ ✁ ✁ obtain the
factor
as ✁
the factor
is prime; if the factor is prime, compute the number ✁
as the product of and
and
determine that the number
✁
is the RSA modulus; and if the factor
and repeat
the check of whether the factor
is
prime.” Granted 2002: US 6404890, US 6496929. These key-generation allow compression 2048 bits to 1024 Exactly how fast is Can we make it even What if ( ) = What if ( ) = Do we still have fast key-generation metho

SLIDE 35 More patents filed by Lenstra, responding to silly methods. “Select a number ;
✁ ✁ ✁ obtain the
factor
as ✁
the factor
is prime; if the factor is prime, compute the number ✁
as the product of and
and
determine that the number
✁
is the RSA modulus; and if the factor
and repeat
the check of whether the factor
is
prime.” Granted 2002: US 6404890, US 6496929. These key-generation methods allow compression from 2048 bits to 1024 bits. Exactly how fast is this? Can we make it even faster? What if ( ) = mod 21280? What if ( ) = mod 21536? Do we still have fast key-generation methods?

SLIDE 36 filed by Lenstra, silly methods. er ;
✁ ✁ ✁ obtain the
- ✁
- ; check whether
- rime; if the factor
- compute the number
✁
duct of and
and
the number
✁
is the and if the factor
and repeat
whether the factor
is
US 6404890, These key-generation methods allow compression from 2048 bits to 1024 bits. Exactly how fast is this? Can we make it even faster? What if ( ) = mod 21280? What if ( ) = mod 21536? Do we still have fast key-generation methods? Unbalanced primes Take ( ) = mo Choose 768-bit .
= 21280 + ( 1
If not both primes, If
This allows compression 2048 bits to 768 bits, with unbalanced
ECM more dangerous Don’t want so small.

SLIDE 37 These key-generation methods allow compression from 2048 bits to 1024 bits. Exactly how fast is this? Can we make it even faster? What if ( ) = mod 21280? What if ( ) = mod 21536? Do we still have fast key-generation methods? Unbalanced primes Take ( ) = mod 21280. Choose 768-bit . Compute
= 21280 + ( 1 ( 1) mod 21280).
If not both primes, try again. If
This allows compression from 2048 bits to 768 bits, with unbalanced
(1998 Lenstra) ECM more dangerous than NFS! Don’t want so small.

SLIDE 38 ey-generation methods ression from 1024 bits. is this? even faster? mod 21280? mod 21536? fast methods? Unbalanced primes Take ( ) = mod 21280. Choose 768-bit . Compute
= 21280 + ( 1 ( 1) mod 21280).
If not both primes, try again. If
This allows compression from 2048 bits to 768 bits, with unbalanced
(1998 Lenstra) ECM more dangerous than NFS! Don’t want so small. Primes in lattices Take ( ) = mo Choose 683-bit
0.
0 = 1
( 1) mo Idea: will take = and
= 0 + 2683
to try to find
1
with ( ( 1)
✂
1
0 + 1 0
(mo Good chance of success. (2003 Coppersmith)

SLIDE 39 Unbalanced primes Take ( ) = mod 21280. Choose 768-bit . Compute
= 21280 + ( 1 ( 1) mod 21280).
If not both primes, try again. If
This allows compression from 2048 bits to 768 bits, with unbalanced
(1998 Lenstra) ECM more dangerous than NFS! Don’t want so small. Primes in lattices Take ( ) = mod 21366. Choose 683-bit
0 = 1
( 1) mod 2683. Idea: will take =
0 + 2683 1
and
= 0 + 2683 1.
Use lattice reduction to try to find
1
2341 with ( ( 1)
✂ 0) 2683
1
0 + 1 0
(mod 2683). Good chance of success. (2003 Coppersmith)

SLIDE 40 rimes mod 21280. . Compute
rimes, try again.
compression from bits,
dangerous than NFS! small. Primes in lattices Take ( ) = mod 21366. Choose 683-bit
0 = 1
( 1) mod 2683. Idea: will take =
0 + 2683 1
and
= 0 + 2683 1.
Use lattice reduction to try to find
1
2341 with ( ( 1)
✂ 0) 2683
1
0 + 1 0
(mod 2683). Good chance of success. (2003 Coppersmith) This allows compression 2048 bits to 682 bits, with balanced
Minor flaw: uniform does not produce exactly uniform random integer But confirm experimentally that each
0 has go
This implies that each
has probability not far above unifo

SLIDE 41 Primes in lattices Take ( ) = mod 21366. Choose 683-bit
0 = 1
( 1) mod 2683. Idea: will take =
0 + 2683 1
and
= 0 + 2683 1.
Use lattice reduction to try to find
1
2341 with ( ( 1)
✂ 0) 2683
1
0 + 1 0
(mod 2683). Good chance of success. (2003 Coppersmith) This allows compression from 2048 bits to 682 bits, with balanced
Minor flaw: uniform random does not produce exactly uniform random integer . But confirm experimentally that each
0 has good chance
. This implies that each choice
has probability not far above uniform.

SLIDE 42 lattices mod 21366.
=
0 + 2683 1
1.
reduction
2341
✂ 0) 2683
success. ersmith) This allows compression from 2048 bits to 682 bits, with balanced
Minor flaw: uniform random does not produce exactly uniform random integer . But confirm experimentally that each
0 has good chance
. This implies that each choice
has probability not far above uniform. Some open questions: Find random
mod 21500
use higher-dimensional Or 2768,
Doesn’t seem to imp lattice effectiveness. Find three balanced given half the bits Do better with another

SLIDE 43 This allows compression from 2048 bits to 682 bits, with balanced
Minor flaw: uniform random does not produce exactly uniform random integer . But confirm experimentally that each
0 has good chance
. This implies that each choice
has probability not far above uniform. Some open questions: Find random
given
mod 21500? Maybe
use higher-dimensional lattices. Or 2768,
Doesn’t seem to improve lattice effectiveness. Find three balanced integers given half the bits of product? Do better with another shape?

SLIDE 44 compression from bits,
uniform random duce exactly integer . erimentally good chance least one . that each choice robability uniform. Some open questions: Find random
given
mod 21500? Maybe
use higher-dimensional lattices. Or 2768,
Doesn’t seem to improve lattice effectiveness. Find three balanced integers given half the bits of product? Do better with another shape? Key-generation speed Start with many ’s. Use trial division etc. Then try 2
26 exponentiations to find one prime. Traditional key generation chooses
27 exponentiations. Faster, slightly non-unifo build visible primes If determines
:
212 exponentiations.

SLIDE 45 Some open questions: Find random
given
mod 21500? Maybe
use higher-dimensional lattices. Or 2768,
Doesn’t seem to improve lattice effectiveness. Find three balanced integers given half the bits of product? Do better with another shape? Key-generation speed Start with many ’s. Use trial division etc. Then try 2
. 26 exponentiations to find one prime. Traditional key generation chooses
27 exponentiations. Faster, slightly non-uniform: build visible primes (Maurer). If determines
:
212 exponentiations.

SLIDE 46 questions:
higher-dimensional lattices.
improve effectiveness. balanced integers bits of product? another shape? Key-generation speed Start with many ’s. Use trial division etc. Then try 2
. 26 exponentiations to find one prime. Traditional key generation chooses
27 exponentiations. Faster, slightly non-uniform: build visible primes (Maurer). If determines
:
212 exponentiations. For ( ) = mod Each determines pool of 216 possible
until finding a prime. 27 exponentiations. For ( ) = mod Obtain pool of pairs
and all different
’s.
212 exponentiations.

SLIDE 47 Key-generation speed Start with many ’s. Use trial division etc. Then try 2
. 26 exponentiations to find one prime. Traditional key generation chooses
27 exponentiations. Faster, slightly non-uniform: build visible primes (Maurer). If determines
:
212 exponentiations. For ( ) = mod 21008: Each determines pool of 216 possible
’s.
Select randomly from pool until finding a prime. 27 exponentiations. For ( ) = mod 21350: Obtain pool of pairs (
with all different ’s and all different
’s.
212 exponentiations.

SLIDE 48 speed ’s. etc.
.
rime. generation
- independently.
- nentiations.
non-uniform: rimes (Maurer).
:
For ( ) = mod 21008: Each determines pool of 216 possible
’s.
Select randomly from pool until finding a prime. 27 exponentiations. For ( ) = mod 21350: Obtain pool of pairs (
with all different ’s and all different
’s.
212 exponentiations. Can use lattice structure to share trial divisions. Or use batch facto Still many exponentiations. Is there a better metho If not, might as well take opposite approach: compress slightly mo Lattice reduction is so can afford many before each exponentiation.

SLIDE 49 For ( ) = mod 21008: Each determines pool of 216 possible
’s.
Select randomly from pool until finding a prime. 27 exponentiations. For ( ) = mod 21350: Obtain pool of pairs (
with all different ’s and all different
’s.
212 exponentiations. Can use lattice structure to share trial divisions. Or use batch factorization. Still many exponentiations. Is there a better method? If not, might as well take opposite approach: compress slightly more. Lattice reduction is fast, so can afford many
0’s
before each exponentiation.

SLIDE 50 mod 21008: determines
’s.
from pool rime.
mod 21350: pairs (
’s
’s.
Can use lattice structure to share trial divisions. Or use batch factorization. Still many exponentiations. Is there a better method? If not, might as well take opposite approach: compress slightly more. Lattice reduction is fast, so can afford many
0’s
before each exponentiation. Protocol violations One user generates Second user sees and generates
2.
Security of
2 was
assuming uniform random What if first user cheats, and doesn’t generate uniform random
1
Recall half-special can construct rare allowing easier facto

SLIDE 51
Can use lattice structure to share trial divisions. Or use batch factorization. Still many exponentiations. Is there a better method? If not, might as well take opposite approach: compress slightly more. Lattice reduction is fast, so can afford many
0’s
before each exponentiation. Protocol violations One user generates
1.
Second user sees (
1)
and generates
2.
Security of
2 was proven
assuming uniform random
1.
What if first user cheats, and doesn’t generate uniform random
1?
Recall half-special NFS: can construct rare values allowing easier factorization.

SLIDE 52 structure divisions. factorization.
method? well approach: more. is fast, many
0’s
Protocol violations One user generates
1.
Second user sees (
1)
and generates
2.
Security of
2 was proven
assuming uniform random
1.
What if first user cheats, and doesn’t generate uniform random
1?
Recall half-special NFS: can construct rare values allowing easier factorization. One solution is to generate
1
from digits of
:
10th, 20th, 30th, etc. Not random, but conjecturally Variant:
1 without
generate
1
from SHA-256 output. Another solution is generate
1
from 1955 RAND

SLIDE 53 Protocol violations One user generates
1.
Second user sees (
1)
and generates
2.
Security of
2 was proven
assuming uniform random
1.
What if first user cheats, and doesn’t generate uniform random
1?
Recall half-special NFS: can construct rare values allowing easier factorization. One solution is to generate
1
from digits of
:
10th, 20th, 30th, etc. Not random, but conjecturally safe. Variant:
1 without 1
Another solution is to generate
1
from SHA-256 output. Another solution is to generate
1
from 1955 RAND tables.